当前位置:网站首页>Roguelike game into crack the hardest hit areas, how to break the bureau?
Roguelike game into crack the hardest hit areas, how to break the bureau?
2022-07-06 08:34:00 【Fairguard mobile game reinforcement】
If there is a game , It will let players experience it again and again , What would that be ?
In the 1980s , One is called 《Rogue》 The game was born , Its unique random playing method has led many games to follow , By authoritative magazines “PC WORLD” named “ One of the ten greatest games in history ”.

The ancestor of meat pigeon game 《Rogue》
Now ,Roguelike It has developed into the most commonly used theme of independent games , The randomness and surprise in the game are amazing , Every start is a new experience , The rich playability makes the majority of players willing to play again and again .
Roguelike With its unique game charm , It has countless fans all over the world . so to speak ,Roguelike The tag is the traffic password of the game party , Just stick it , Attention is guaranteed .
from TapTap We can see on the popular list of games , Many of the top 100 games have Roguelike Elements , Such as 《 From the knight 》、《 Regenerating cell 》、《 Gunfire rebirth 》、《 The full moon night 》 etc. .
Roguelike Games are also popular because of their high popularity , It's easier to be targeted by hackers . Some cracking websites even set up corresponding cracking game zones .
We search on Baidu “ Vitality Knight cracked version ”, You can search for 2180 Ten thousand pieces of relevant information , A cracking website even updated its 84 A version , Including internal purchase cracking 、 Unlimited resources 、 Full role 、 Infinite Blue infinite skill CD Wait for the player to crack 、 Modify the content .

Published by a website 《 From the knight 》 Cracked versions
except 《 From the knight 》 This old popular game , New games are also hard to escape .2022 year 3 month , Owned by a big game factory Roguelike Game online test , With novel game role setting and pigeon playing , stay TapTap Got it. 40 More than 10000 attention , stay Roguelike The game is among the best under the track .
The game was targeted by hackers soon after it was launched , Posted a detailed strategy and steps on a cracking Forum , The cracker uses the simulator to install and export the game package for decompression , Then use dnspy decompile , Extract relevant functions and modify them , Attack the game 、 After the blood volume and other values are tampered , Realize the second monster function .

Some of the modification ideas posted by the cracker

After the game is cracked , Achieved second kill BOSS
For a game , The impact of cracking and modification is undoubtedly devastating . Cracking the game will lead to a sharp decline in the charging capacity of the game , And modify the provided “ metamorphosis ” The function will lead to the loss of genuine and paid players , If you don't take precautions , It has a great impact on the life cycle of the game .
In view of the proliferation of cracking and modification ,FairGuard The team concentrates on the underlying technology , We have developed a number of protection functions that are unique in the industry , The product has been FunPlus、 Notoginseng and entertainment 、BillBill And many other head companies adopt , And verified FairGuard Outstanding security 、 stability 、 Ease of use .

FairGuard Introduction to some functions of the product
边栏推荐
猜你喜欢
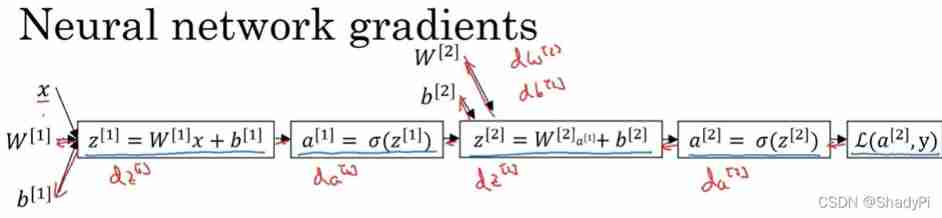
Deep learning: derivation of shallow neural networks and deep neural networks

Roguelike游戏成破解重灾区,如何破局?
![[cloud native] teach you how to build ferry open source work order system](/img/fb/507f763791235bd00bc8201e5d7741.png)
[cloud native] teach you how to build ferry open source work order system

深度剖析C语言指针
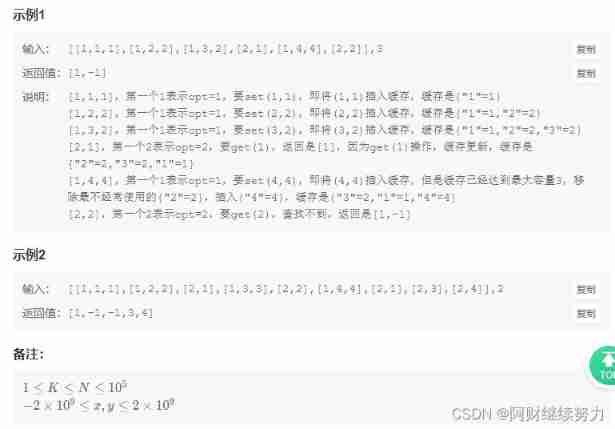
2022.02.13 - NC003. Design LRU cache structure
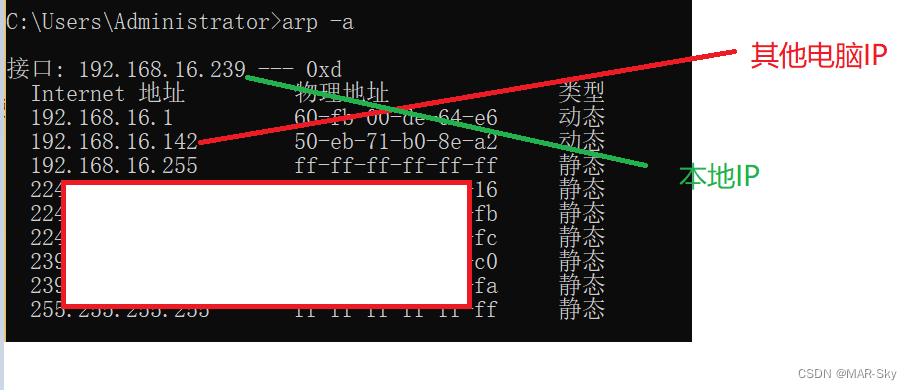
查看局域网中电脑设备
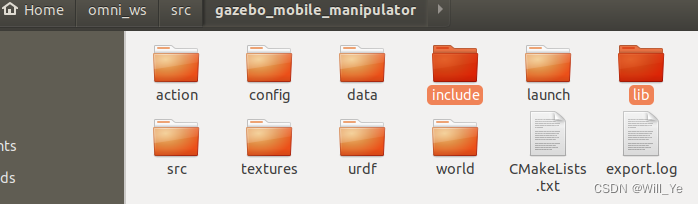
ROS编译 调用第三方动态库(xxx.so)
【刷题】牛客网面试必刷TOP101
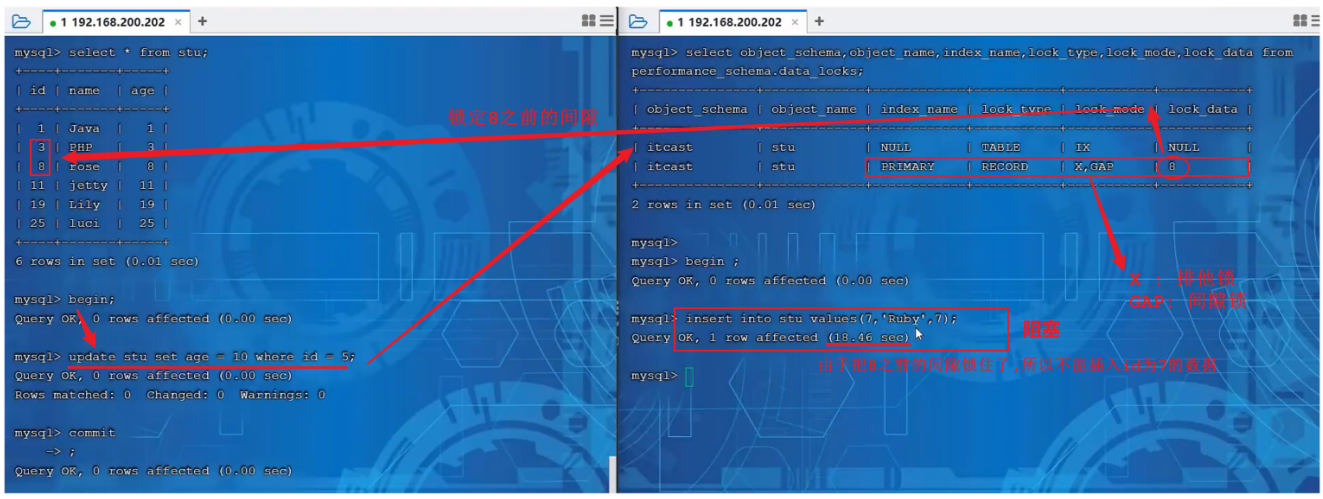
【MySQL】鎖

FairGuard游戏加固:游戏出海热潮下,游戏安全面临新挑战
随机推荐
On the day of resignation, jd.com deleted the database and ran away, and the programmer was sentenced
LDAP應用篇(4)Jenkins接入
Online yaml to CSV tool
leetcode刷题 (5.28) 哈希表
Summary of phased use of sonic one-stop open source distributed cluster cloud real machine test platform
The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower
【MySQL】锁
704 二分查找
PC easy to use essential software (used)
Deep analysis of C language pointer
根据csv文件某一列字符串中某个数字排序
egg. JS getting started navigation: installation, use and learning
Cisp-pte practice explanation
查看局域网中电脑设备
企微服务商平台收费接口对接教程
深度剖析C语言指针
On the inverse order problem of 01 knapsack problem in one-dimensional state
堆排序详解
Screenshot in win10 system, win+prtsc save location
Visual implementation and inspection of visdom