当前位置:网站首页>Summary of common algorithms of binary tree
Summary of common algorithms of binary tree
2020-11-06 01:18:00 【Clamhub's blog】
Node definition
1 |
public static class BinaryNode<T> { |
Binary tree nodes include element values and left and right child node references .
Create nodes
1 |
BinaryNode g = new BinaryNode(7); |
Form like :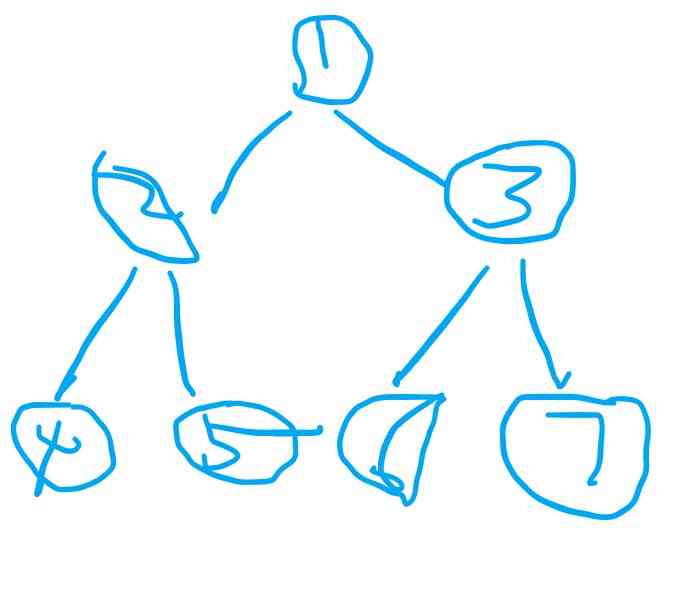
1、 front 、 in 、 After the sequence traversal
In front of the binary tree 、 in 、 Before in postorder traversal 、 in 、 The root node ;
Before the order : Output the root node first , And then the left and right nodes .
Middle preface : First left , Then output the root node , To the right .
In the following order : First left and right , Then output the root node .
1 |
public static void visit(BinaryNode p) { |
1.1、 The former sequence traversal
1 |
root -> Left -> Right |
1.1.1、 Recursive implementation
1 |
public static void recursivePreOrder(BinaryNode p) { |
If the node is null, Go straight back to ;
Print out the root node first , Then recursion left subtree , Then recurs the right subtree .
Just meet : First root , And then around .
1.1.2、 Non recursive implementation
1 |
public static void iterativePreOrder(BinaryNode p) { |
Make full use of the idea of stack , First in, then out .
When the node is not empty , Putting nodes on the stack , Iterate the elements in the stack , Pop up top element , Currently the root element , After that, press the right and left child nodes on the stack respectively . In this way, the order of the child nodes is left first and then right .
1.2、 In the sequence traversal
1 |
Left -> root -> Right |
1.2.1、 Recursive implementation
1 |
public static void recursiveInOrder(BinaryNode p) { |
1.2.2、 Non recursive implementation
1 |
public static void iterativeInOrder(BinaryNode p) { |
1.3、 After the sequence traversal
1 |
Left -> Right -> root |
1.3.1、 Recursive implementation
1 |
public static void recursivePostOrder(BinaryNode p) { |
1.3.2、 Non recursive implementation
1 |
public static void iterativePostOrder(BinaryNode p) { |
2、BFS And DFS
2.1、BFS Breadth first search
1 |
1234567 |
Breadth first traversal is to read node elements by layer , We need to use the data structure of the queue .
1 |
public static void levelOrderTraversal(BinaryNode node) { |
2.2、DFS Depth-first search
1 |
1245367 |
Starting from the root node , Select a branch to read all the elements , We need to use the data structure of the stack .
1 |
public static void depthTraversal(BinaryNode node) { |
3、 The depth of the binary tree
104. The maximum depth of a binary tree
3.1、 recursive
1 |
private static int calcDepth(BinaryNode node) { |
3.2、 Depth first
maxDepth Compare the length of each branch to update , Finally get the deepest branch length .
1 |
public static int maxDepthDFS(BinaryNode node) { |
3.3、 breadth-first
Search by layer , Every step into the floor , depth +1.
1 |
public static int maxDepthBFS(BinaryNode node) { |
4、 Binary tree image
Traverse by depth or breadth , Swap the left and right subtrees of nodes .
1 |
public static void mirror(BinaryNode root) { |
5、 Symmetric binary tree
101. Symmetric binary tree
This problem is a variation of binary tree mirror image , If two binary trees are symmetric , be :
- Two root nodes have the same value
- The left subtree of each tree , Are the same as the right subtree of another tree
Recursive implementation :Iterative implementation :1
2
3
4
5
6
7
8
9
10
11public boolean isSymmetric(BinaryNode root) {
return isMirror(root, root);
}
public boolean isMirror(BinaryNode t1, BinaryNode t2) {
if (t1 == null && t2 == null) return true;
if (t1 == null || t2 == null) return false;
return (t1.val == t2.val)
&& isMirror(t1.right, t2.left)
&& isMirror(t1.left, t2.right);
}1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17public boolean isSymmetric(BinaryNode root) {
LinkedList<BinaryNode> q = new LinkedList<>();
q.add(root);
q.add(root);
while (!q.isEmpty()) {
BinaryNode t1 = q.poll();
BinaryNode t2 = q.poll();
if (t1 == null && t2 == null) continue;
if (t1 == null || t2 == null) return false;
if (t1.val != t2.val) return false;
q.add(t1.left);
q.add(t2.right);
q.add(t1.right);
q.add(t2.left);
}
return true;
}
summary
The algorithm of various topics of binary tree will think of recursion in the first consciousness , But when the recursion depth is too large, there will be stack overflow , So iterations will be used to implement accordingly , Accordingly, the data structure of queue or stack is introduced .
It feels like the most important algorithm is DFS And BFS, among DFS Depth first search uses the FIFO feature of the stack , and BFS Breadth first search uses the first in first out feature of the queue .
版权声明
本文为[Clamhub's blog]所创,转载请带上原文链接,感谢
边栏推荐
- The difference between Es5 class and ES6 class
- 遞迴思想的巧妙理解
- H5 makes its own video player (JS Part 2)
- Installing the consult cluster
- 连肝三个通宵,JVM77道高频面试题详细分析,就这?
- PHPSHE 短信插件说明
- 一时技痒,撸了个动态线程池,源码放Github了
- Leetcode's ransom letter
- Can't be asked again! Reentrantlock source code, drawing a look together!
- Why do private enterprises do party building? ——Special subject study of geek state holding Party branch
猜你喜欢

如何将数据变成资产?吸引数据科学家

容联完成1.25亿美元F轮融资
Didi elasticsearch cluster cross version upgrade and platform reconfiguration

全球疫情加速互联网企业转型,区块链会是解药吗?
Face to face Manual Chapter 16: explanation and implementation of fair lock of code peasant association lock and reentrantlock

Filecoin主网上线以来Filecoin矿机扇区密封到底是什么意思
Subordination judgment in structured data
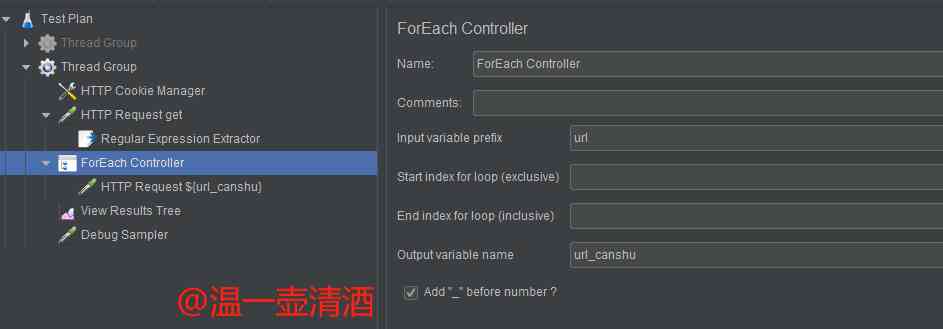
Jmeter——ForEach Controller&Loop Controller

IPFS/Filecoin合法性:保护个人隐私不被泄露

华为云“四个可靠”的方法论
随机推荐
(1) ASP.NET Introduction to core3.1 Ocelot
至联云解析:IPFS/Filecoin挖矿为什么这么难?
使用 Iceberg on Kubernetes 打造新一代云原生数据湖
Swagger 3.0 天天刷屏,真的香嗎?
PHPSHE 短信插件说明
Chainlink将美国选举结果带入区块链 - Everipedia
嘘!异步事件这样用真的好么?
Wiremock: a powerful tool for API testing
Analysis of ThreadLocal principle
Analysis of react high order components
人工智能学什么课程?它将替代人类工作?
Listening to silent words: hand in hand teaching you sign language recognition with modelarts
DRF JWT authentication module and self customization
Subordination judgment in structured data
“颜值经济”的野望:华熙生物净利率六连降,收购案遭上交所问询
Programmer introspection checklist
Character string and memory operation function in C language
速看!互联网、电商离线大数据分析最佳实践!(附网盘链接)
【效能優化】納尼?記憶體又溢位了?!是時候總結一波了!!
The practice of the architecture of Internet public opinion system