当前位置:网站首页>6-6 vulnerability exploitation SSH security defense
6-6 vulnerability exploitation SSH security defense
2022-07-07 02:33:00 【Mountain Rabbit 1】

SSH Modify the default port
By default ,SSH Use 22 port . For the sake of safety , Generally, the default port will be modified .
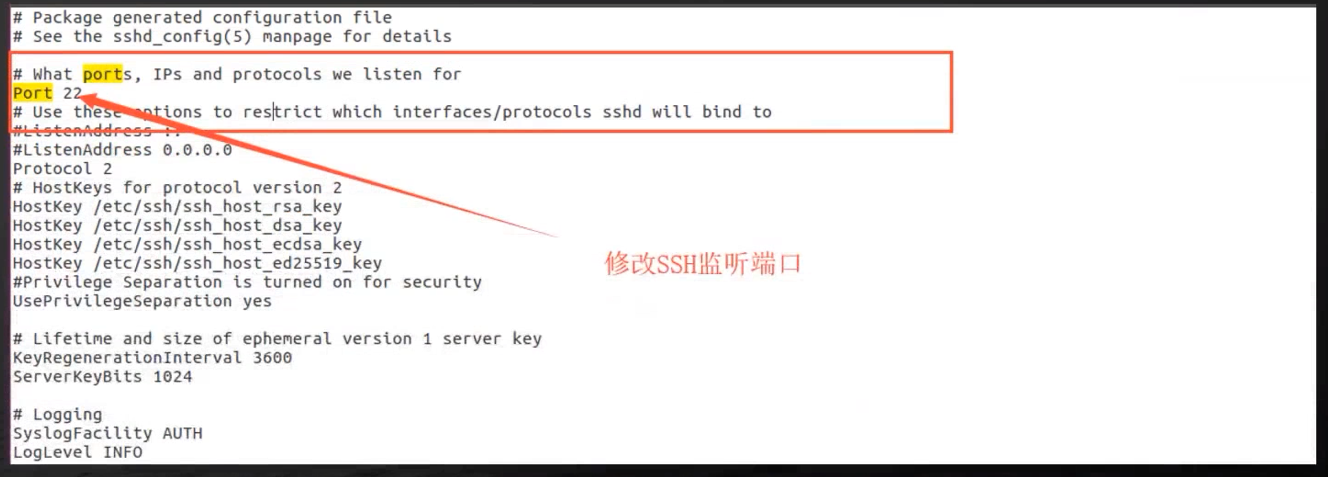
modify 22 For other port numbers , Thus, our listening port is modified
Be careful : You must restart after modification SSH service , Only in this way can our configuration file , In the process of restarting , Reload , Thus effective .
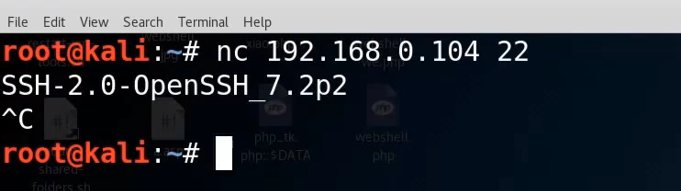
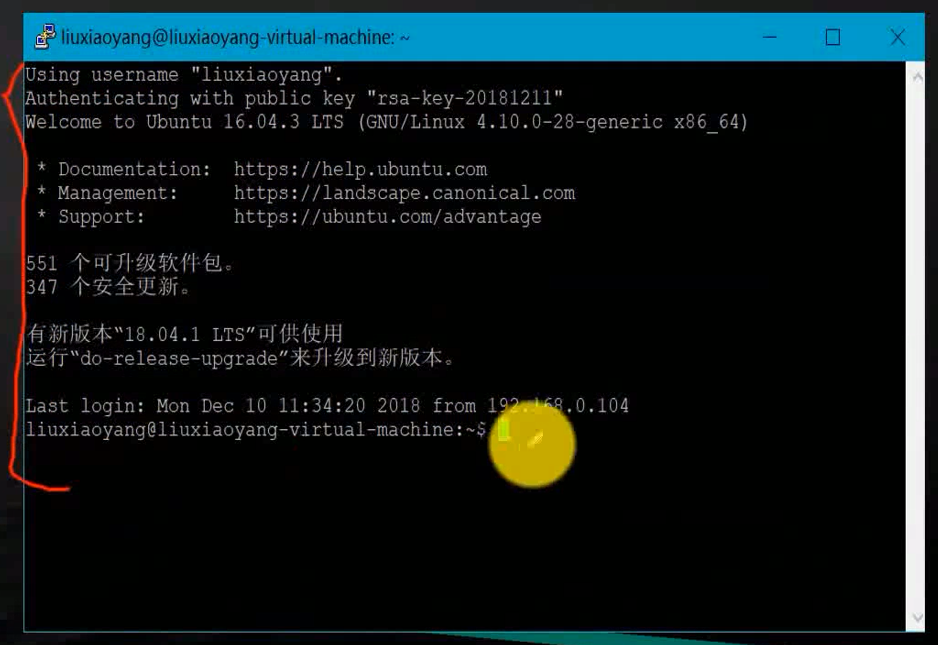
Turn on ubuntu Of ssh service function , stay kali Detect in the middle
nc 192.168.0.104 22
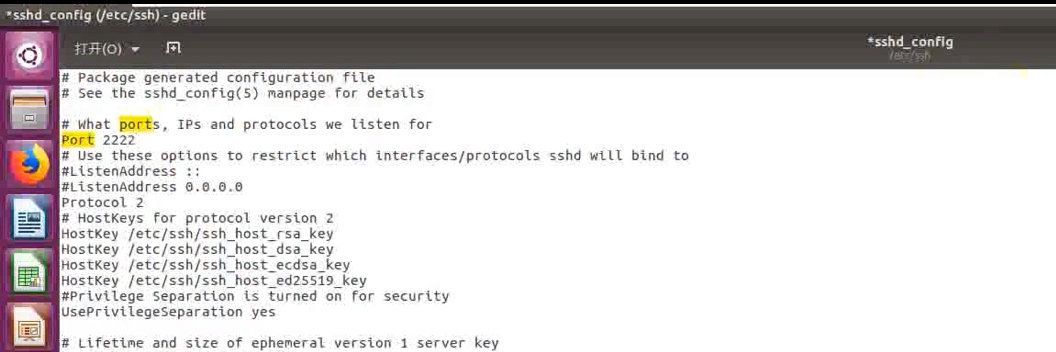
stay ubuntu among , Modify port number
cd /etc/ssh/
ls
sudo gedit sshd_config
2222
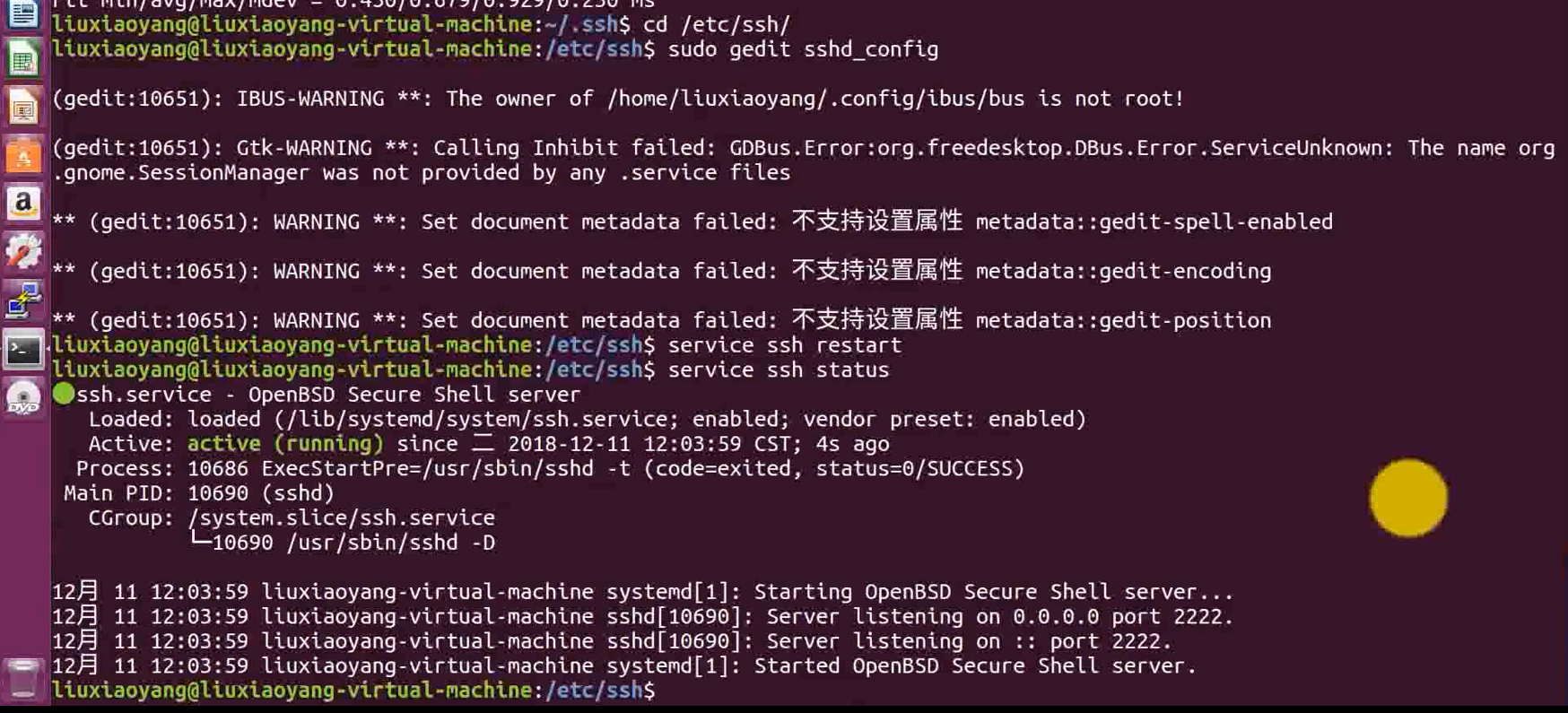
service ssh restart
service ssh status

netstat -pantu

nc 192.168.0.104 22
nc 192,168.0.104 2222
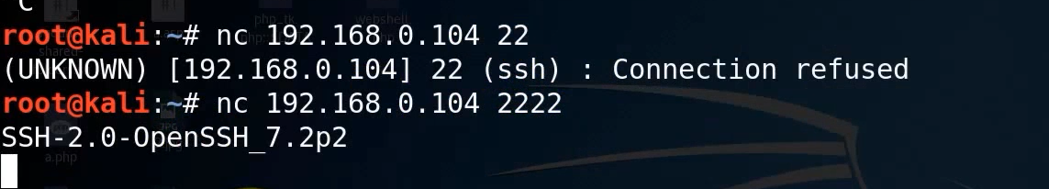
Modify the function of the default port , So we can't use it directly 22 Port number connection , Further detection is needed , Detection ssh Listening port , To make the corresponding connection
SSH Set up PGP Sign in
By default ,SSH Use user name and password for remote login , Will cause violent cracking , Keep trying user names and passwords , So as to log in to the system , In order to prevent this process , adopt putty This software , To generate the corresponding private key , Configure the private key , Authentication , So that we can log in without user password , More secure , Prevent violent cracking
Generate SSH Key pair , Use puttygen.
Download link :https://www.chiark.greenend.org/~sgtatham/putty/latest.html
Click on Generate Generate the private key
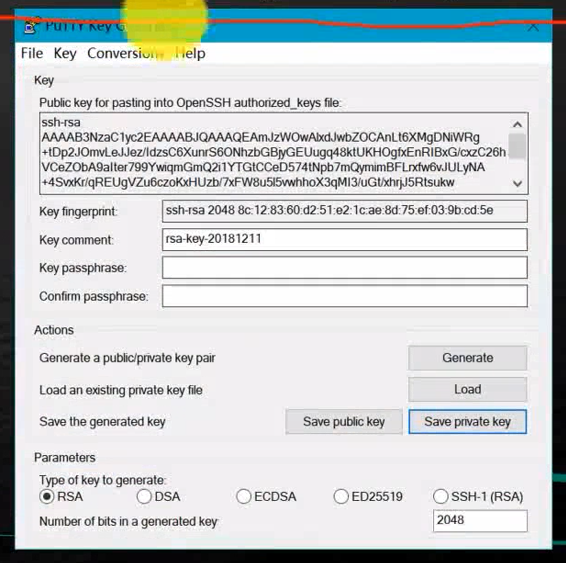
Click on save private key, It will be generated on the desktop .ppk, This name can also be named by yourself
SSH Set up PGP Sign in
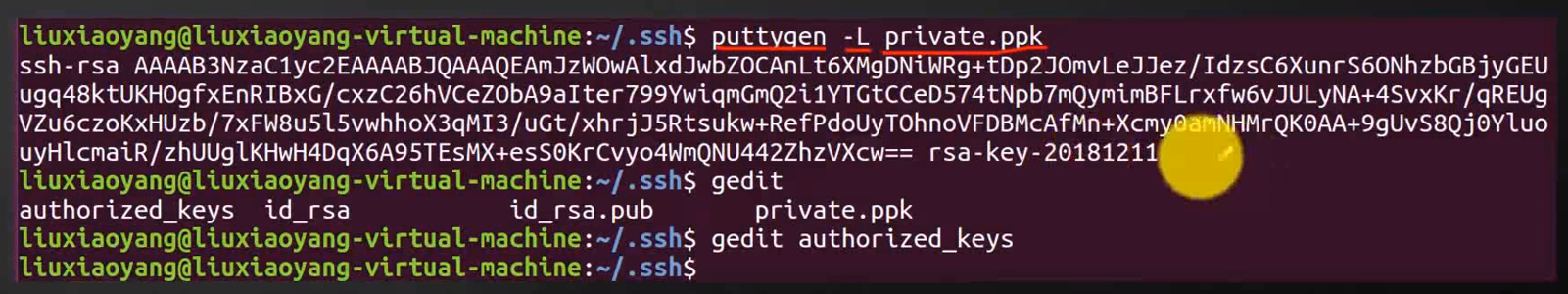
Use ssh-keygen Command in Linux Generate .ssh Catalog , stay .ssh Create a new key storage file authorized_keys, And copy the private key file to .ssh Under the table of contents . Use command puttygen -L “ Copy the private key file ”, Copy content to authorized_keys In file .
ssh-keygen
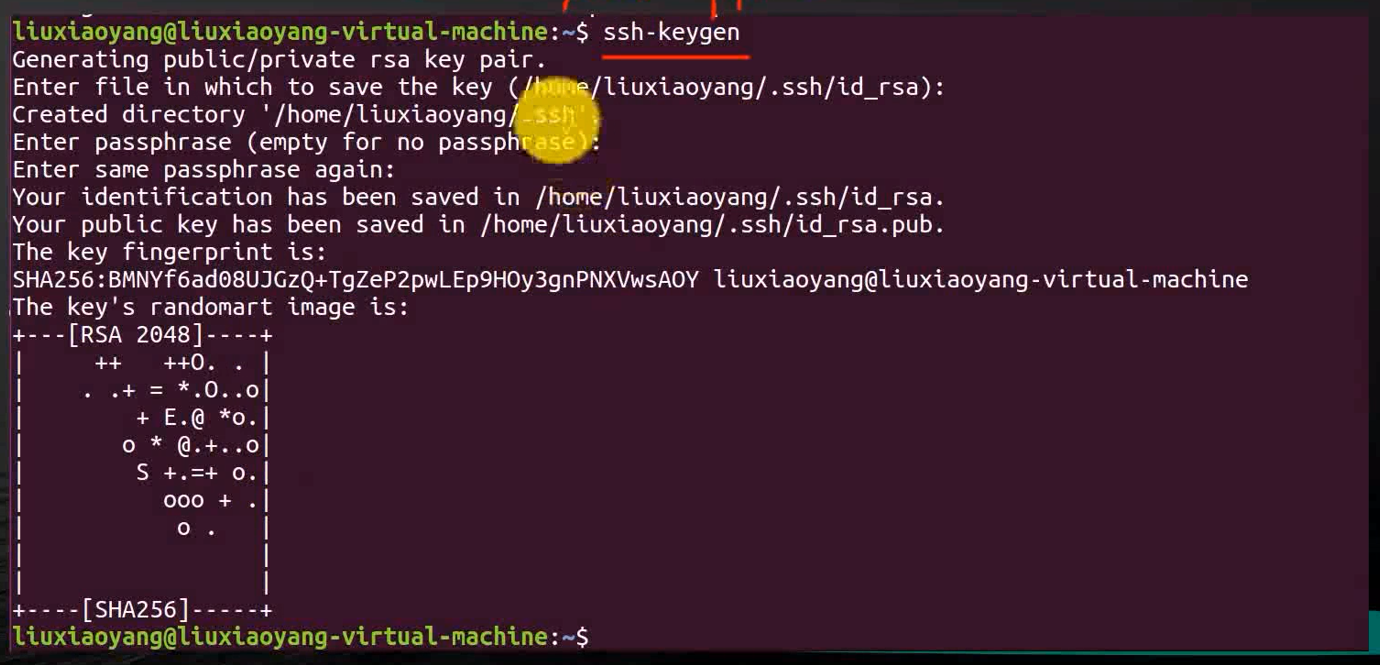
This time will be in /home/liuxiaoyang/ Generate hidden directory under .ssh, Switch to .ssh, new directory authorized_keys
SSH Set up PGP Sign in
Use Putty The client loads the private key file to connect .
Click on auth
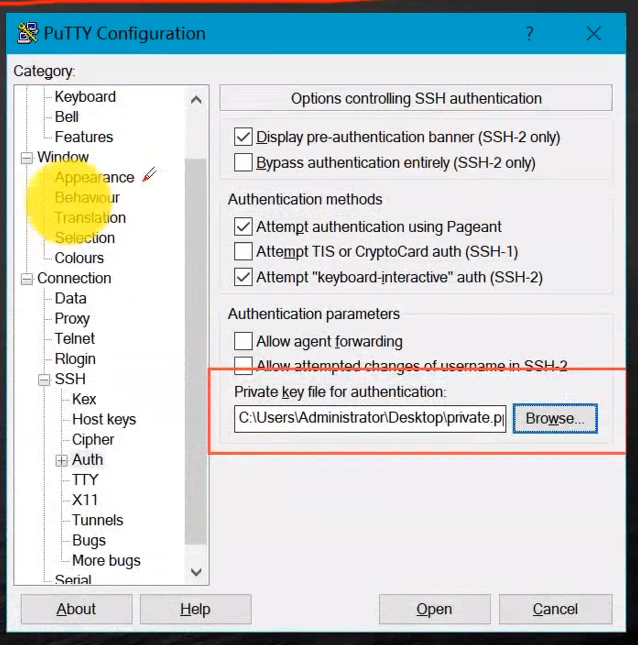
After loading , We are connecting , You don't need to enter the corresponding connection password , Only need Data Enter the user name in
cd ~
pwd
ls -alh
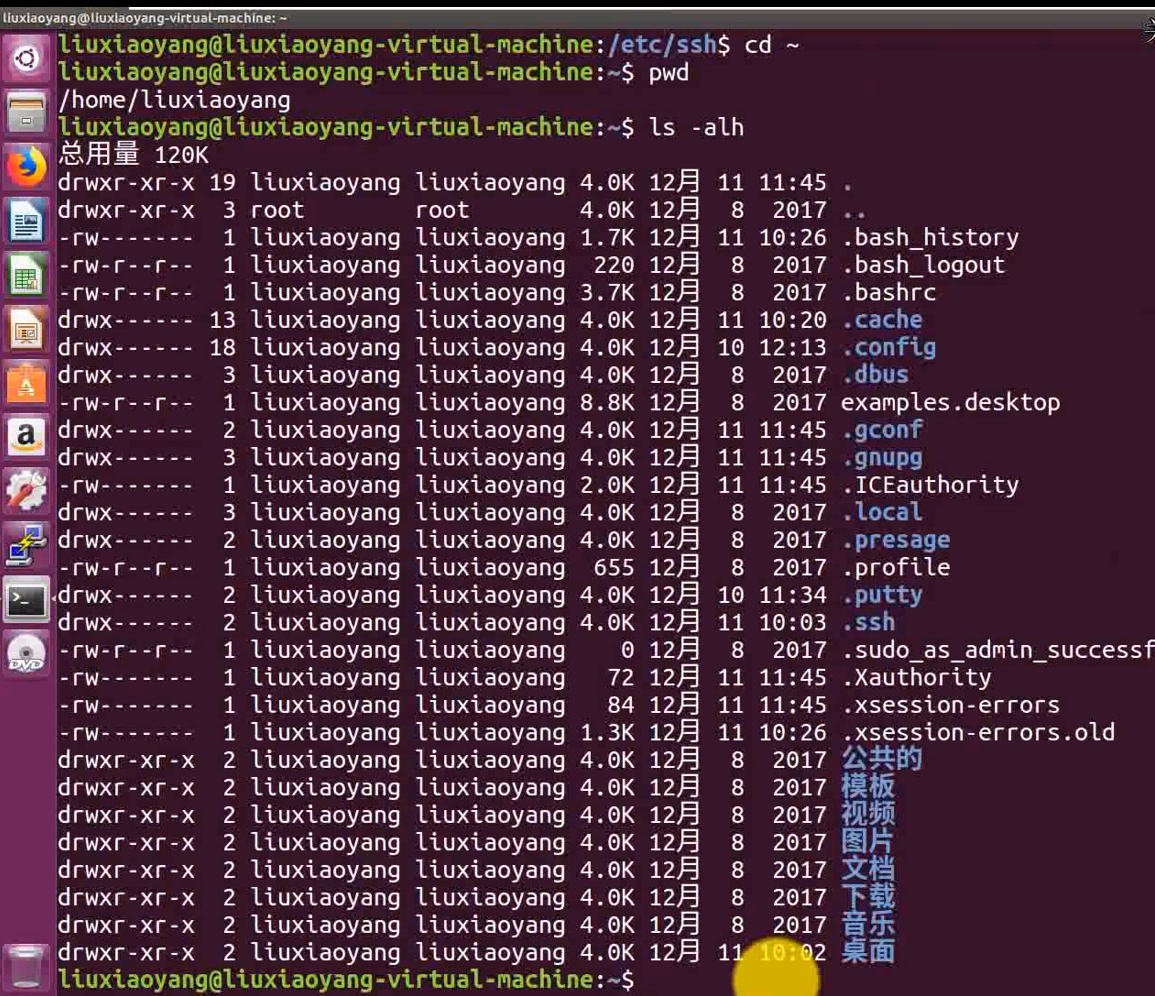
cd .ssh/
ls
puttygen -L private.ppk
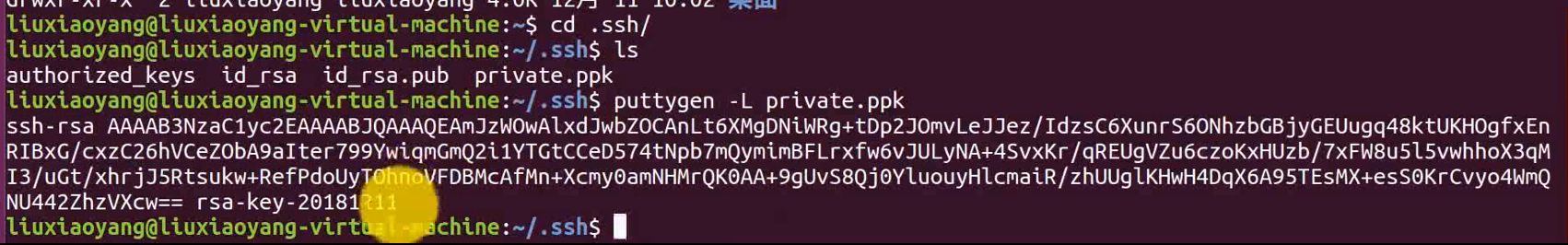
gedit authorized_keys
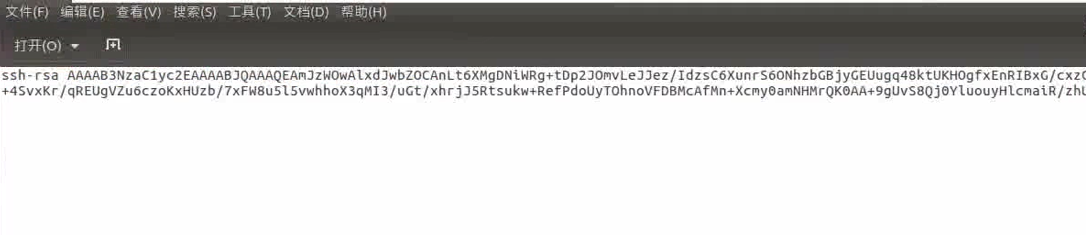
Paste the content here , Preservation , After saving , We have one aythorized_keys file
This is the time , We can do that windows Next , Or installed under other systems ppy, Under the client software , Connect ssh, It uses PGP Connect
SSH Defend against brute force cracking user accounts
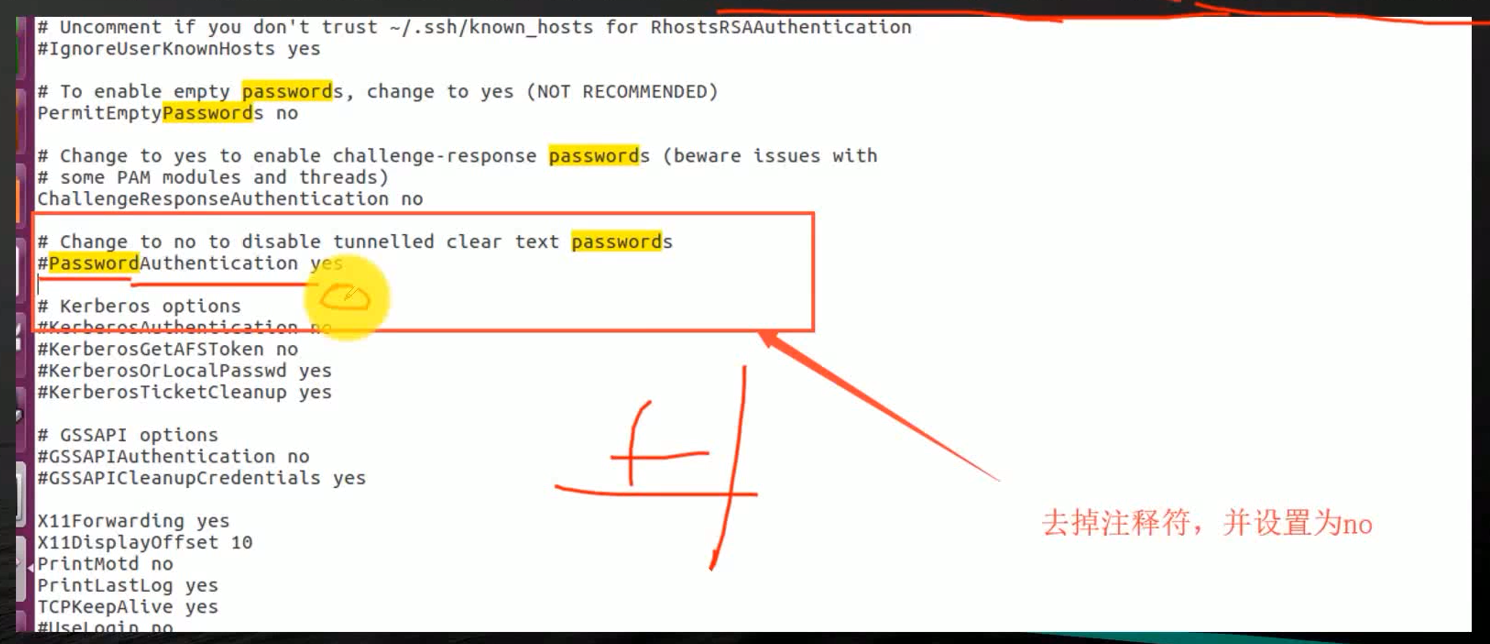
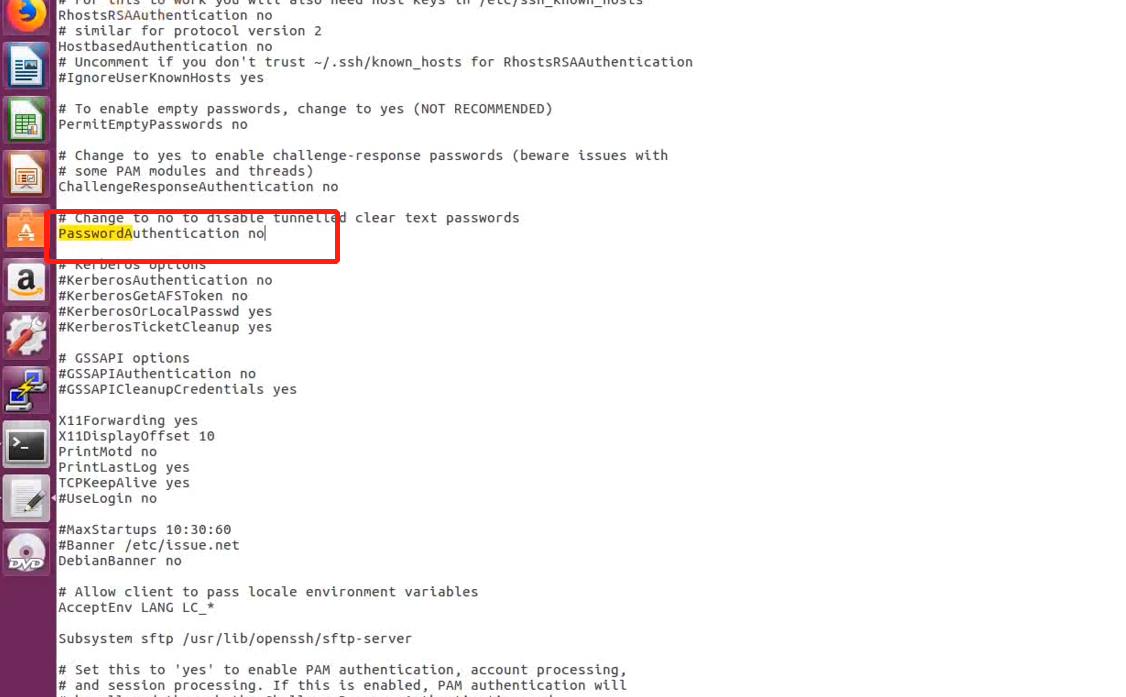
Set up pgp To prevent violent cracking , But we can still log in with account and password
stay linux You can configure that you cannot log in with user name and password , Use only SSH PGP How to verify login . Evaded SSH Brute force .
Problems arise : Cannot log in with user password , There are complex operations to a large extent .
for instance , There are many administrators in our current system , Cannot log in with user name and password , Everyone needs PPT file , To log in , It will be a lot of work and operation
cd /etc/ssh/
sudo gedit sshd_config
service ssh restart
service ssh status
below , We are kali Login with user name and password , To verify that
ssh [email protected]
ssh [email protected] -p 2222
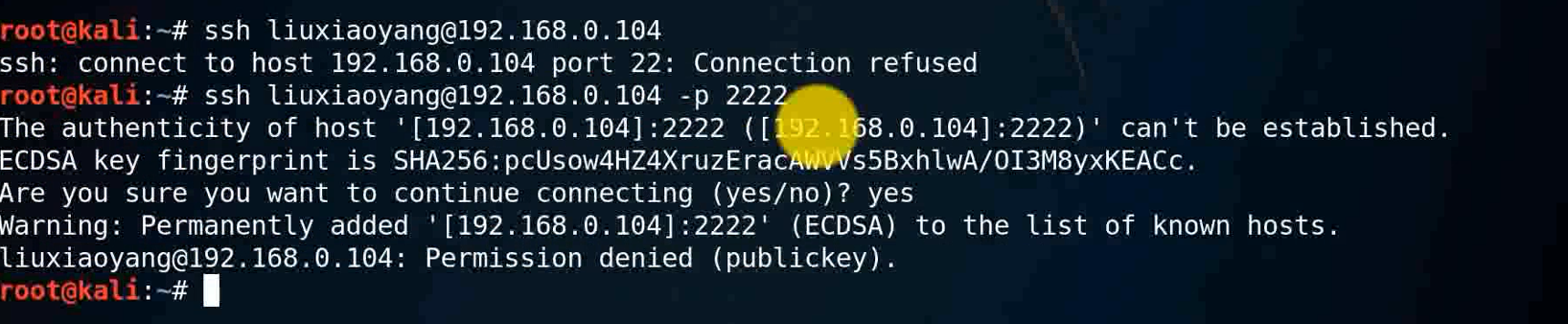
Because we can't log in , So brute force software , Is failure
iptables Set threshold to prevent brute force cracking
use iptables Firewall to prevent brute force cracking , We can set the corresponding threshold , After we try to login three times , Just lock the login , Makes it impossible for him to log in
utilize Iptables Error validating multiple connections , Lock the account 120 second .
sudo iptables -l INPUT -p tcp --dport 22 -i eth0 -m state --state NEW -m recent --set
sudo iptables -l INPUT -p tcp --dport 22 -i eth0 -m state --state NEW -m recent --update --seconds 120 --hitcount 3 -j DROP
After setting , Reboot required SSH service .
service ssh restart
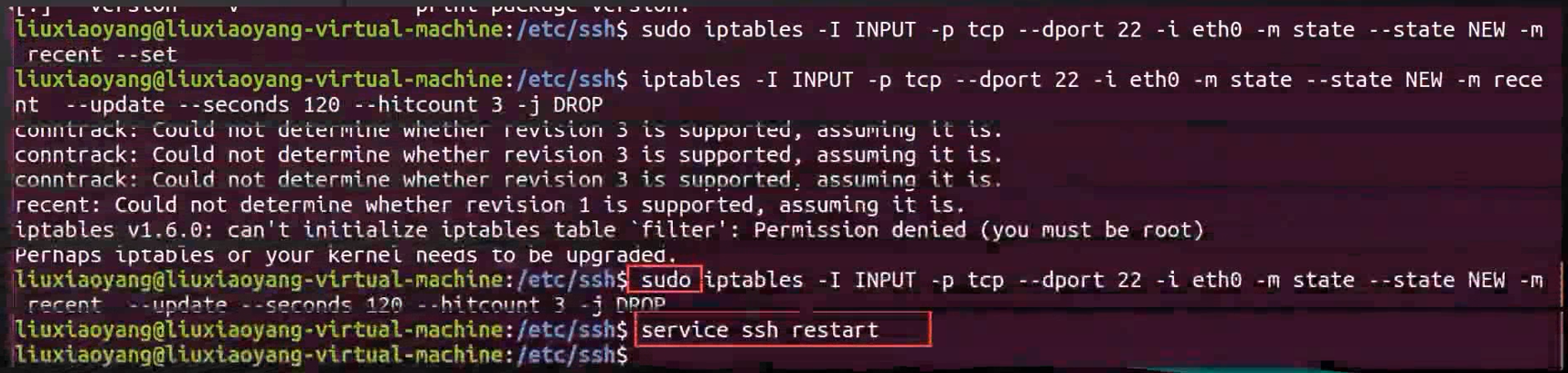
We can set a longer time , You can only try three combinations in a day , You can only try 1000 combinations a year , When our password setting is complex , Brute force cracking is also a very slow situation , Brute force cracking cannot take effect , Or say , It takes a lot of energy , several tens of years , It may be tens of thousands of years , Can the current dictionary , Guess and solve
边栏推荐
- Chang'an chain learning notes - certificate model of certificate research
- 1--新唐nuc980 NUC980移植 UBOOT,从外部mx25l启动
- 1500万员工轻松管理,云原生数据库GaussDB让HR办公更高效
- 如何设计好接口测试用例?教你几个小技巧,轻松稿定
- Lidar: introduction and usage of ouster OS
- 测试优惠券要怎么写测试用例?
- Detailed explanation of line segment tree (including tested code implementation)
- MFC Windows 程序设计[147]之ODBC数据库连接(附源码)
- 本周 火火火火 的开源项目!
- 建議收藏!!Flutter狀態管理插件哪家强?請看島上碼農的排行榜!
猜你喜欢
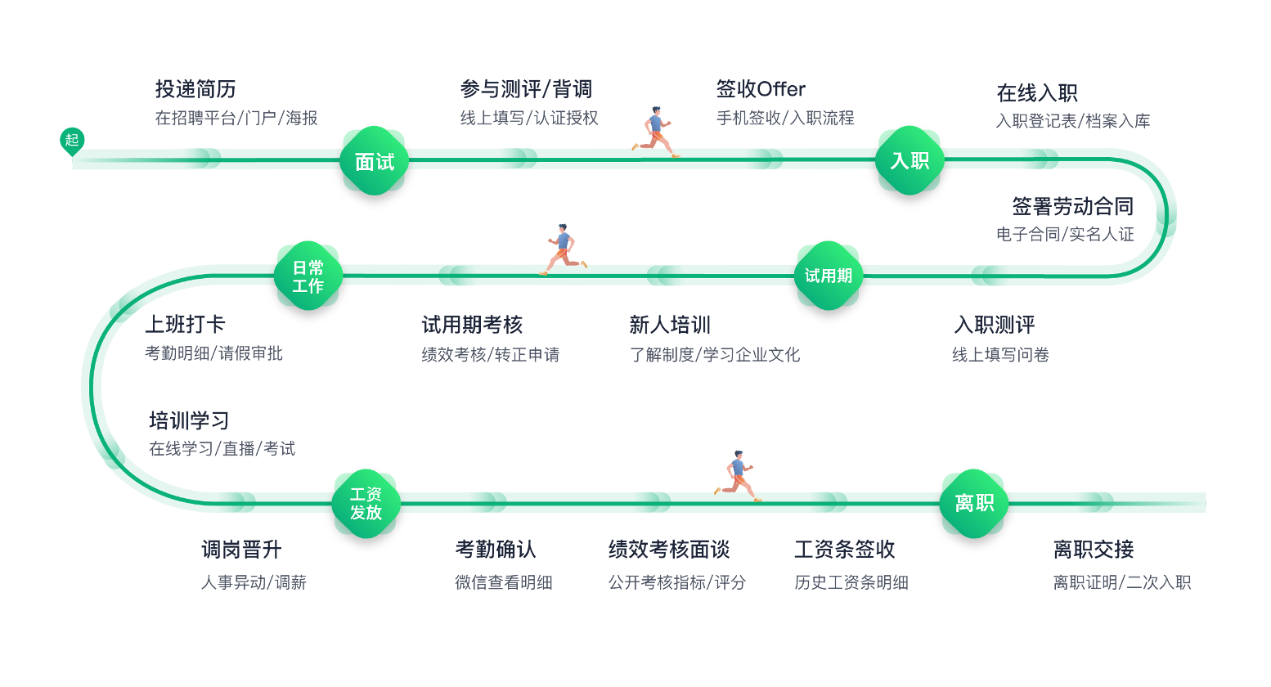
1500万员工轻松管理,云原生数据库GaussDB让HR办公更高效

1 -- Xintang nuc980 nuc980 porting uboot, starting from external mx25l
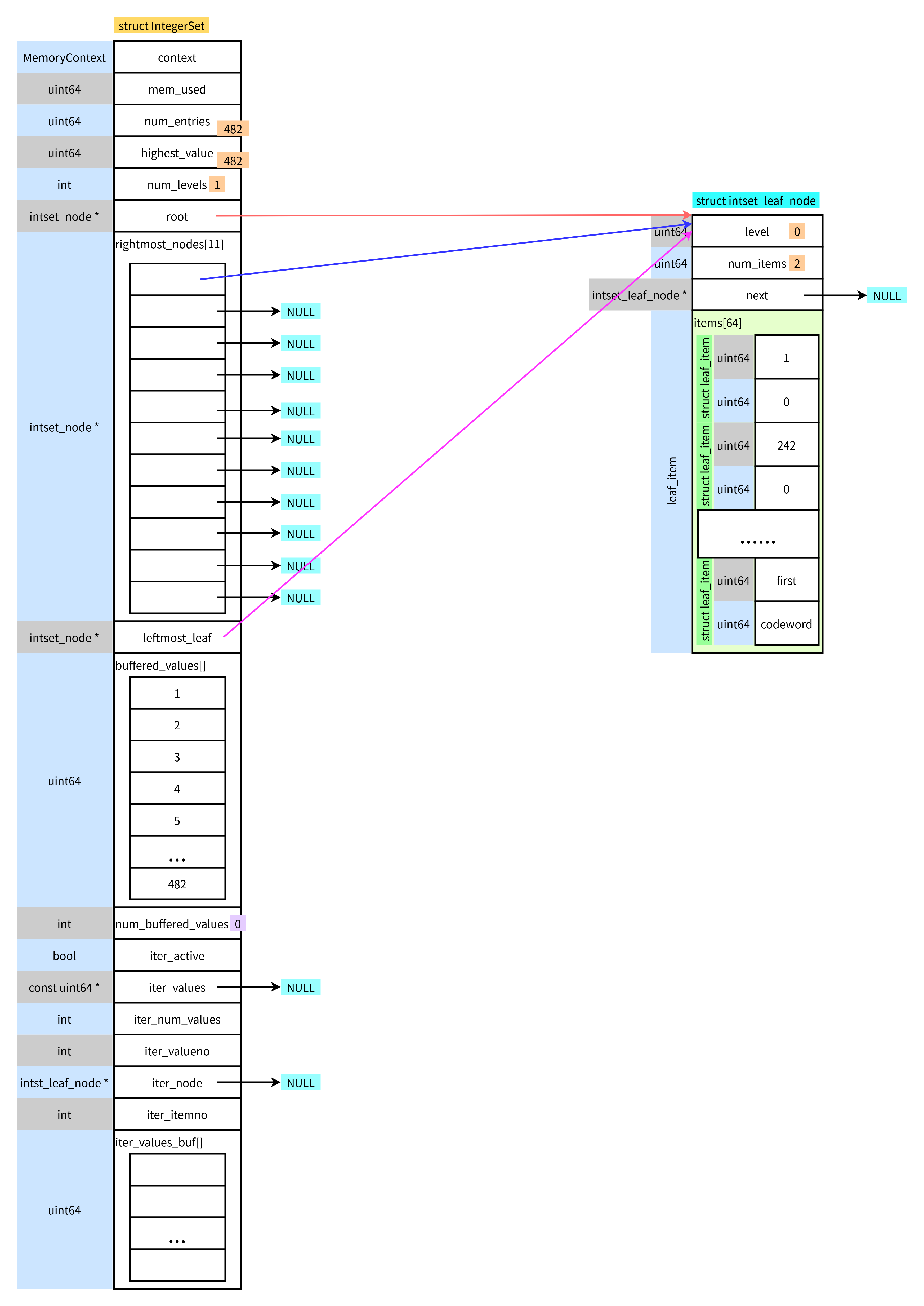
postgresql之integerset

FLIR blackfly s usb3 industrial camera: how to use counters and timers
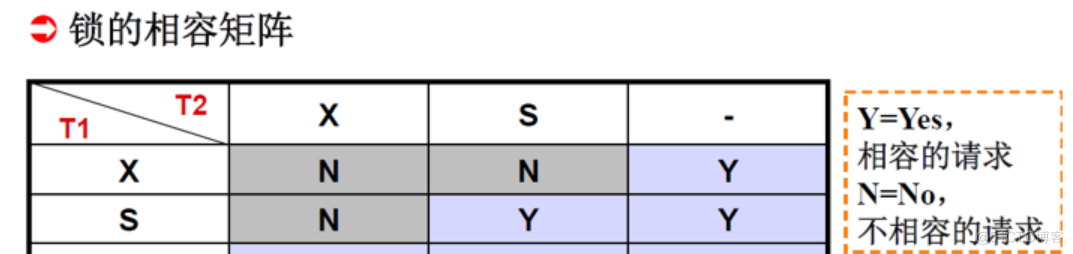
#夏日挑战赛#数据库学霸笔记(下)~

Draco - glTF模型压缩利器
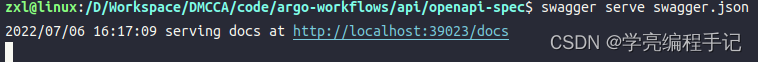
go swagger使用

Argo workflows source code analysis
![[unity notes] screen coordinates to ugui coordinates](/img/e4/fc18dd9b4b0e36ec3e278e5fb3fd23.jpg)
[unity notes] screen coordinates to ugui coordinates
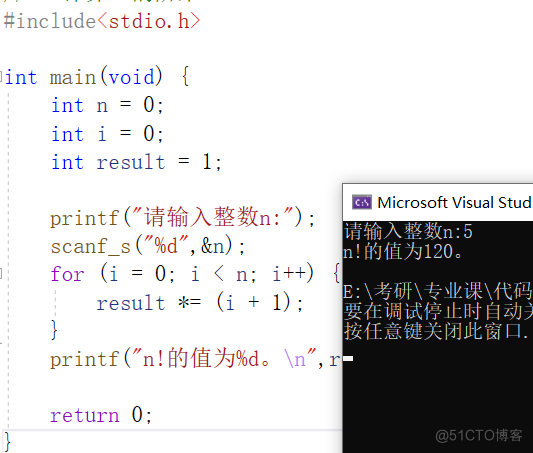
C语言练习题_1
随机推荐
阿里云易立:云原生如何破解企业降本提效难题?
Halcon实例转OpenCvSharp(C# OpenCV)实现--瓶口缺陷检测(附源码)
STM32项目 -- 选题分享(部分)
4 -- Xintang nuc980 mount initramfs NFS file system
Lumion 11.0 software installation package download and installation tutorial
The mega version model of dall-e MINI has been released and is open for download
The boss is quarantined
所谓的消费互联网仅仅只是做行业信息的撮合和对接,并不改变产业本身
Lombok makes the pit of ⽤ @data and @builder at the same time
4--新唐nuc980 挂载initramfs nfs文件系统
CSDN 夏令营课程 项目分析
Decryption function calculates "task state and lifecycle management" of asynchronous task capability
3--新唐nuc980 kernel支持jffs2, Jffs2文件系统制作, 内核挂载jffs2, uboot网口设置,uboot支持tftp
Stm32f4 --- PWM output
人脸识别应用解析
go swagger使用
低代码平台中的数据连接方式(上)
Sensor: DS1302 clock chip and driver code
unity webgl自适应网页尺寸
Use of pgpool II and pgpooladmin