当前位置:网站首页>C final review
C final review
2022-07-05 18:32:00 【mxrone】
1. Direct access is to access directly by using the address of the variable .(T)
analysis :
(1) Direct access :
Access the variable value according to the address of the variable .
(2) Indirect access to :
Access variables through variables that store variable addresses .
2. Let the variable be defined as int a[2]={1,3}, *p=&a[0]+1; be *p The value of is ( 3 ).
analysis : Notice the address plus one , instead of It's worth adding 1;
3. For the following structure definitions ,++p->str Medium ++ Add to (A).
struct {
int len;
char *str;
} *p;
A. The pointer str On B. The pointer p On C.str Point to the content D. Grammar mistakes
4.C Structure type variables in the language during program execution ( All members always reside in memory ).
5. What linked lists don't have is ( Any element can be accessed at random ).
6. When using linked list instead of array for data operation , Query is more convenient .(F)
analysis :
Array : Support random access , Easy to use , Query efficiency is higher than linked list , Memory It is a continuous area .
Linked list : No data access , Can be dynamically added or deleted Variable size , Memory may be discontinuous , Chain store , Query efficiency is low .
7. stay C In the program , Functions can be either nested or defined , You can also nest calls .(F)
analysis :
C The definitions of functions in language are parallel to each other 、 Mutually independent , That is to say, when defining a function , A function body cannot contain the definition of another function , That is, functions cannot be nested , But you can nest calls .
8. The file pointer points to the access location of the file data in the file buffer .(F)
analysis :
The file pointer points to A memory area , This area stores information about the open file , Including the current position of the file reading pointer 、 File read buffer size and other information , Not pointing to a file .
9. Using a structure pointer as a function parameter only needs to pass an address value , therefore , It can improve the efficiency of parameter transmission .(T)
10. Known and defined ,FILE fp; char str[] = "Good!"; fp = fopen("filename.dat", "wb");
Will array str The string stored in is written to the name filename.dat In the binary file of . The required statement is ( D).
A.fwrite(str[0], sizeof(char), 1, fp) B.fread(str, sizeof(char), 5, fp)
C.fwrite(fp, sizeof(char), 5, str) D.fwrite(str, sizeof(char), 5, fp)
analysis :
fread And fwrite function
The function prototype :
size_t fread(void *buffer, size_t size, size_t, count, FILE *pf)
size_t fwrite(void *buffer, size_t size, size_t count, FILE *pf)
fread and fwrite Function is generally used for input and output of binary files .
fscanf And fprintf function
for example :
fscanf(fp, "%s %d %d %f\n", pb->name, &pb->num, &pb->age, &pb->score)
fprintf(fp,"%s %d %d %f\n", pa->name, pa->num, pa->age, pa->score)
fscanf The function :
Press “ Format string ” Specified format , from “ File type pointer ” Read data from the current location of the file pointed to , Then press “ Entry address table column ” The order of , Store the read data into the specified memory unit .
fprintf The function :
Press “ Format string ” Specified format , take “ Output item table column ” Write the values of the items specified in “ File type pointer ” The current location of the file pointed to . If the write is successful ,fprintf The return value of the function is the number of characters written to the file ( Or number of bytes ), Otherwise return to EOF(-1).
11. Open a text file for student.txt, The correct way to add data is ( B ).
A.fp=fopen("my.txt","r") B.fp=fopen("my.txt","a")
C.fp=fopen("my.txt","w") D.fp=fopen("my.txt","w+")
r With read-only Way to open a file . The pointer to the file will be placed at the beginning of the file . This is the default mode .
a Open a file for Additional . If the file already exists , The file pointer will be placed at the end of the file . in other words , The new content will be written after the existing content . If the file does not exist , Create a new file to write to .
a+ Open a file For reading and writing only . If the file already exists , The file pointer will be placed at the end of the file . Append mode when the file opens . If the file does not exist , Create a new file for reading and writing .
w Open a file Write only . Open the file if it already exists , And edit from the beginning , The original content will be deleted . If the file does not exist , Create a new file .
w+ Open a file for Reading and writing . Open the file if it already exists , And edit from the beginning , The original content will be deleted . If the file does not exist , Create a new file .
wb With Binary format Open a file Write only . Open the file if it already exists , And edit from the beginning , The original content will be deleted . If the file does not exist , Create a new file . Generally used for non - text files such as pictures .
wb+ With Binary format Open a file For reading and writing . Open the file if it already exists , And edit from the beginning , The original content will be deleted . If the file does not exist , Create a new file . Generally used for non - text files such as pictures .
12.
The following description is wrong ( D ).
A. Function calls can appear in an expression B. Function calls can appear in the execution statement
C. Function calls can be used as arguments to a function D. Function calls can be used as formal parameters of a function
analysis :
The return value is stored in the register , No address , It cannot be a formal parameter , But it can be used as an argument .
边栏推荐
- 音视频包的pts,dts,duration的由来.
- Various pits of vs2017 QT
- 文章中的逻辑词
- Is it safe to open an account and register stocks for stock speculation? Is there any risk? Is it reliable?
- Is it safe to make fund fixed investment on access letter?
- Fix vulnerability - mysql, ES
- Exemple Quelle est la relation entre le taux d'échantillonnage, l'échantillon et la durée?
- sample_ What is the relationship between rate, sample and duration
- 解决 contents have differences only in line separators
- LeetCode 6109. Number of people who know the secret
猜你喜欢
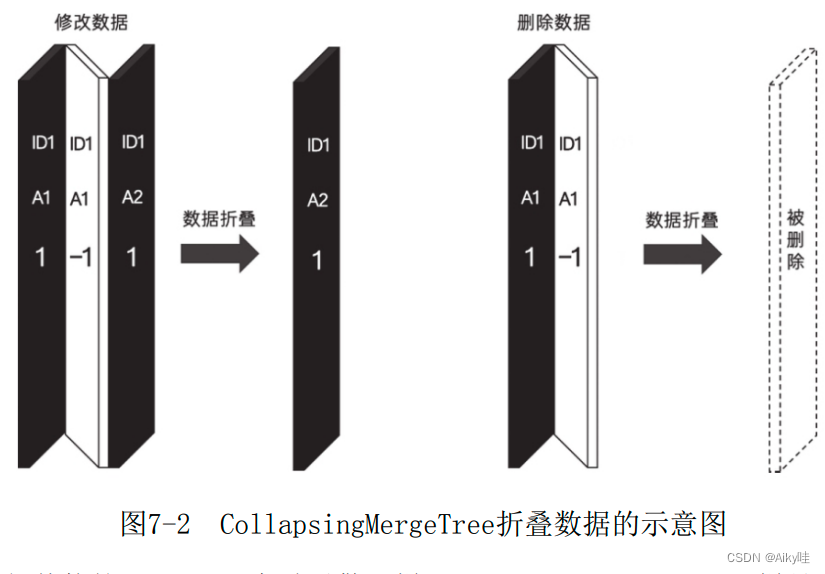
《ClickHouse原理解析与应用实践》读书笔记(5)
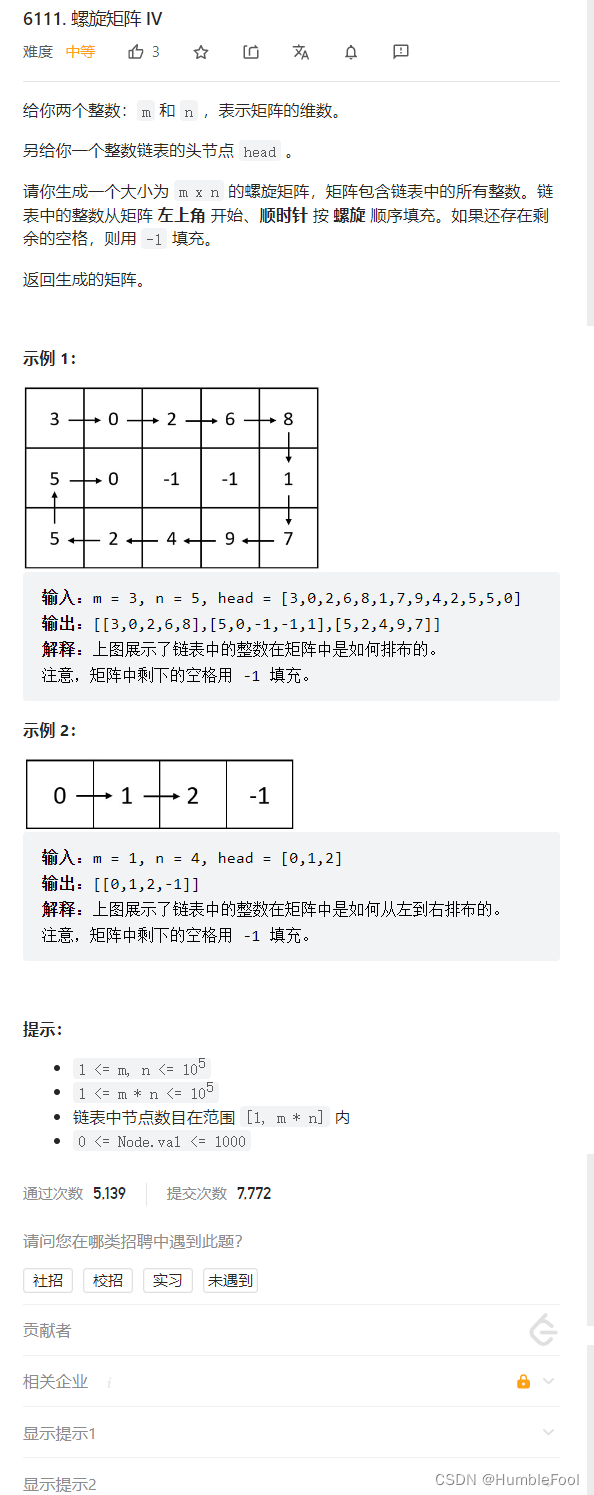
LeetCode 6111. 螺旋矩阵 IV

Nanjing University: Discussion on the training program of digital talents in the new era
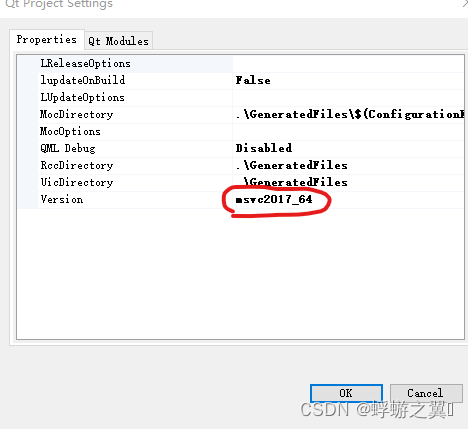
vs2017 qt的各种坑
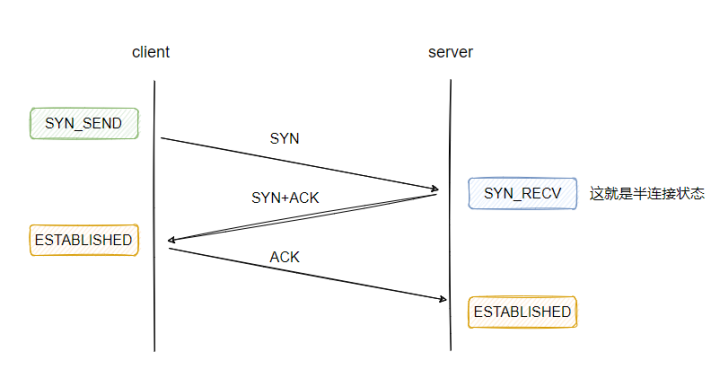
Thoroughly understand why network i/o is blocked?
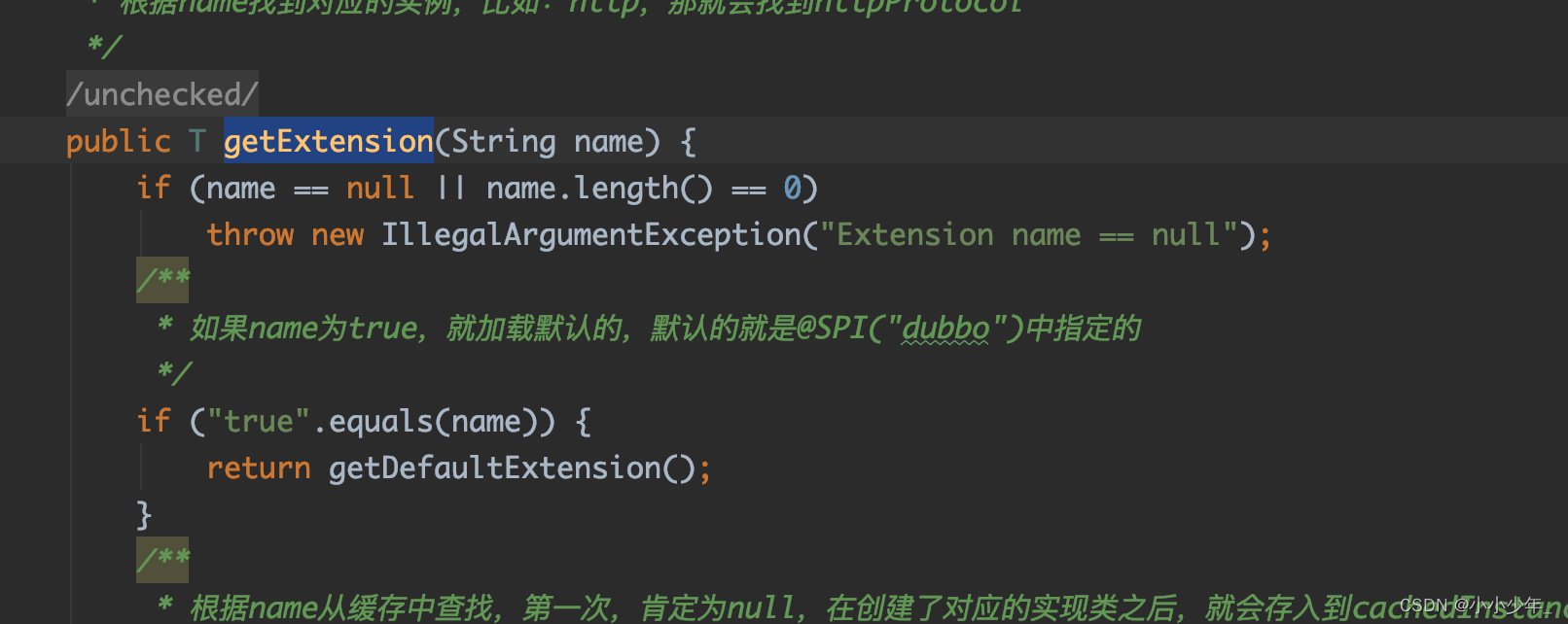
@Extension、@SPI注解原理
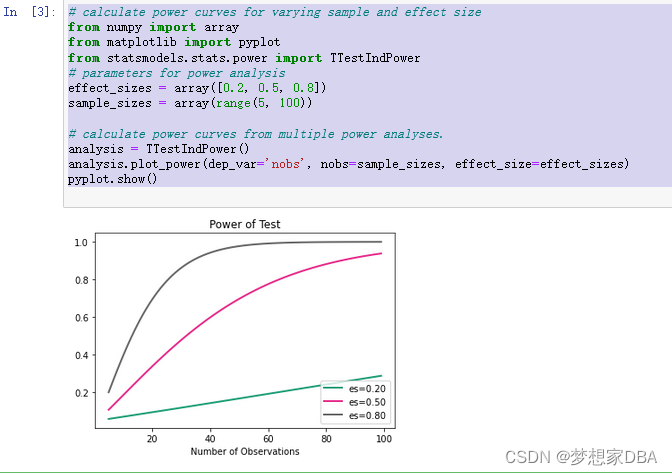
About statistical power
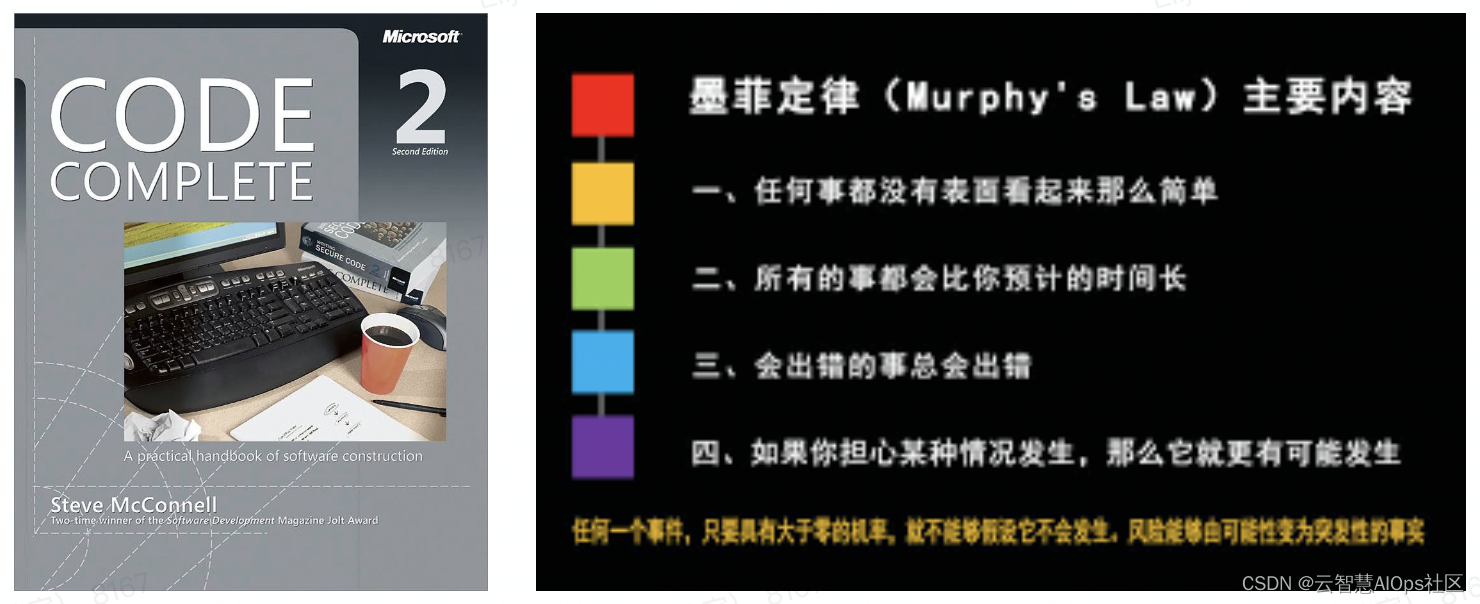
如何写出好代码 - 防御式编程

图片数据不够?我做了一个免费的图像增强软件
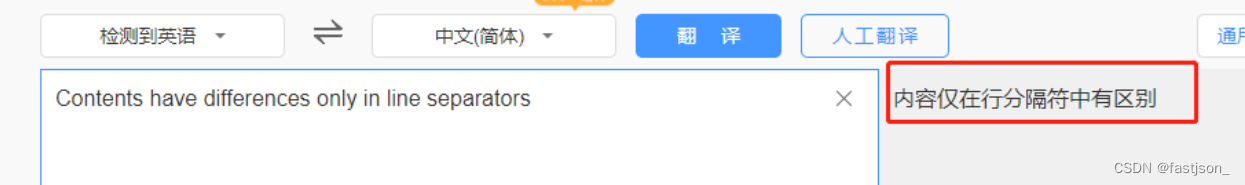
解决 contents have differences only in line separators
随机推荐
Gimp 2.10 tutorial "suggestions collection"
Copy the linked list with random pointer in the "Li Kou brush question plan"
[utiliser Electron pour développer le Bureau sur youkirin devrait]
快速生成ipa包
爬虫01-爬虫基本原理讲解
FCN: Fully Convolutional Networks for Semantic Segmentation
The 11th China cloud computing standards and Applications Conference | China cloud data has become the deputy leader unit of the cloud migration special group of the cloud computing standards working
[paddlepaddle] paddedetection face recognition custom data set
Generate XML schema from class
图像分类,看我就够啦!
Electron installation problems
Multithreading (I) processes and threads
Introduction to Resampling
New words new words new words new words [2]
sample_rate(采樣率),sample(采樣),duration(時長)是什麼關系
A2L file parsing based on CAN bus (3)
Pytorch yolov5 training custom data
Thoroughly understand why network i/o is blocked?
How to improve the thermal management in PCB design with the effective placement of thermal through holes?
node_ Exporter memory usage is not displayed