当前位置:网站首页>Hash table
Hash table
2022-07-04 21:38:00 【Wu_ Candy】
This is the first step of infinite testing 163 Original article
During the interview , Have been asked : Do you know what the underlying data structure of the dictionary is ?
What we are mainly talking about today is what the data structure of hash table looks like ; How hash collision is caused and how to solve hash collision .
1. Definition
Hashtable (Hash table, Also called a hash table ), According to the key code value (Key value) Data structures that are accessed directly . in other words , It accesses records by mapping key values to a location in a table , To speed up the search . This mapping function is called the hash function , The array of records is called a hash table .
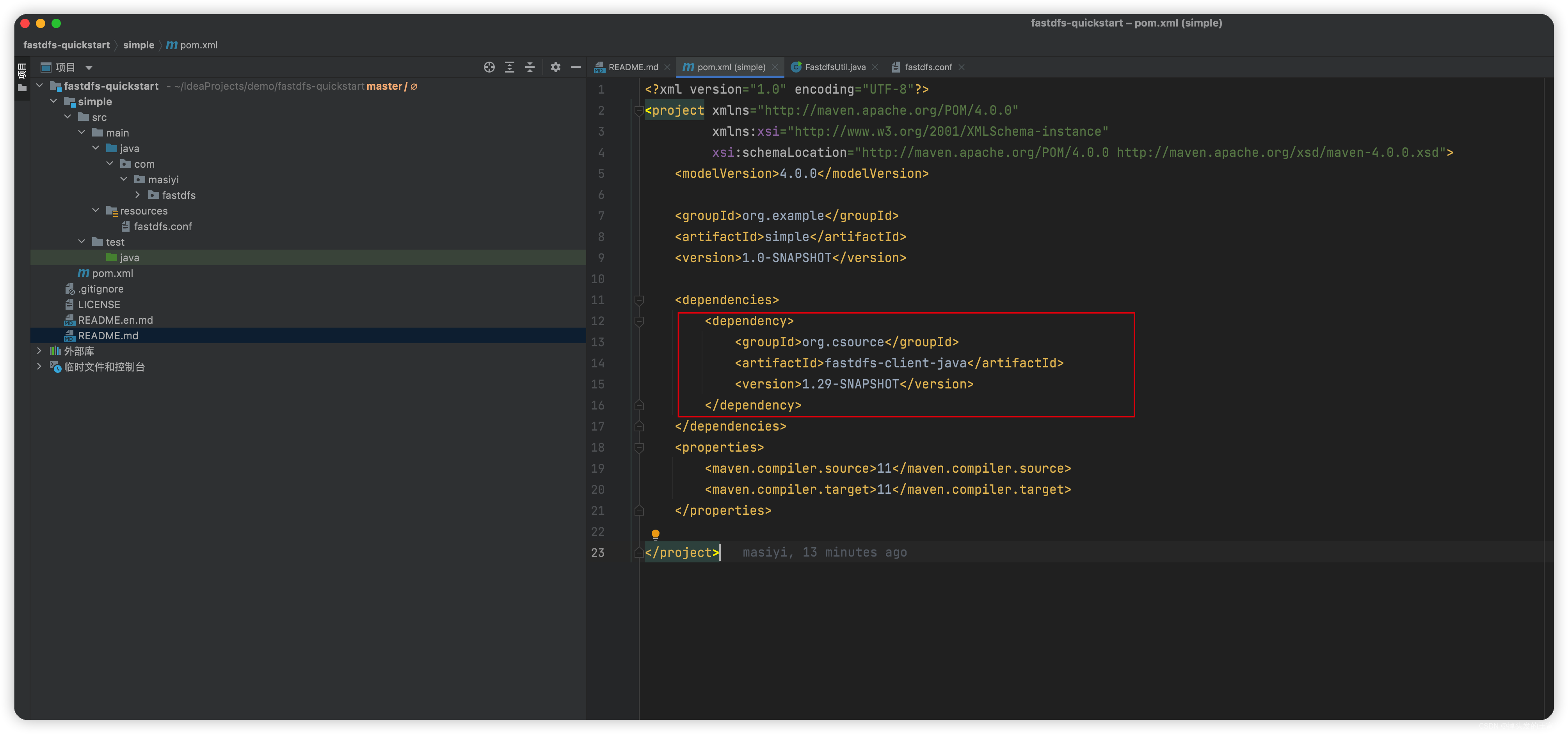
The example of dictionary stored value is as follows . In order to understand the data structure of hash table more popularly , Let's look at the picture below :
put("jack","666")
put("Rose","777")
put("Evan","888")
Hash Table Mainly by 2 Part of it is made up of :
- hash function
- Table 「 The bottom layer is an array , The general array size is 2n 」 As for why , For the convenience of bit operation
Hash Functions and Table The role of
hash The main function is to convert key To operate , Generate an index value of an integer index. Corresponding to our case :
hash("Jack") --> index = 14hash("Rose") --> index = 01hash("Evan") --> index = 03
And then according to index The corresponding value Store in Table Array . To complete the key and value Mapping .
2.Hash Collision
Let's add another set of data to the dictionary (Jeffery,999), hypothesis hash("Jeffery") --> index = 03, At this point, you will find that ,Jeffery and Rose Of index All for 3, The conflict , This is it. Hash Collision .
3. solve Hash Collision
solve Hash Common methods of conflict :
- 1. Open addressing (Open Addressing): According to certain rules, probe other addresses , Until you meet an empty place
- 2. Then the hash method (Rr-Hashing)“ Design multiple hash function
- 3. Chain address (Separate Chaining) For example, through a linked list, the same index The elements of
Today we mainly want to introduce the chain address method , If I found hash At the time of the collision , You can use a single linked list to list the same index The elements of , As shown in the figure below :
4. How to survive key Hash value of ?
key Common types may be : Integers 、 Floating point numbers 、 character string 、 Define the object . Different kinds of key, Hash values are generated differently , But the goal is the same :
- 1. Try to make every key The hash value of is unique
- 2. Try to make key All of the information in the calculation
In this paper, the key All are strings , With jack For example :jack The hash value of can be expressed as :j * n^3 + a * n^2 + c * n^1 + k * n^0jack Of ASCII It's all traceable , Therefore, an integer can be obtained through the above calculation T, And then through Table The size of the array & An operation perhaps % Decouple operation , You can get inedx Subscript value .
About integers 、 Floating point numbers 、 Define how the hash value of an object is calculated , If you are interested, you can search , There is a systematic explanation .
summary
Today, I mainly introduce how the hash table data structure stores values , Then it explains how hash collision is generated and how to solve it , Finally, the string key How to calculate the hash value of . I believe you will read this article carefully , I have a clear understanding of what a hash table is .
边栏推荐
- redis事务
- Can be displayed in CAD but not displayed in print
- 奋斗正当时,城链科技战略峰会广州站圆满召开
- Daily question -leetcode1200- minimum absolute difference - array - sort
- Delphi SOAP WebService 服务器端多个 SoapDataModule 实现相同的接口方法,接口继承
- Huawei ENSP simulator layer 3 switch
- Huawei ENSP simulator configures DHCP for router
- Flutter TextField示例
- 每日一题-LeetCode556-下一个更大元素III-字符串-双指针-next_permutation
- Introduction to pressure measurement of JMeter
猜你喜欢
FastDfs的快速入门,三分钟带你上传下载文件到云服务器
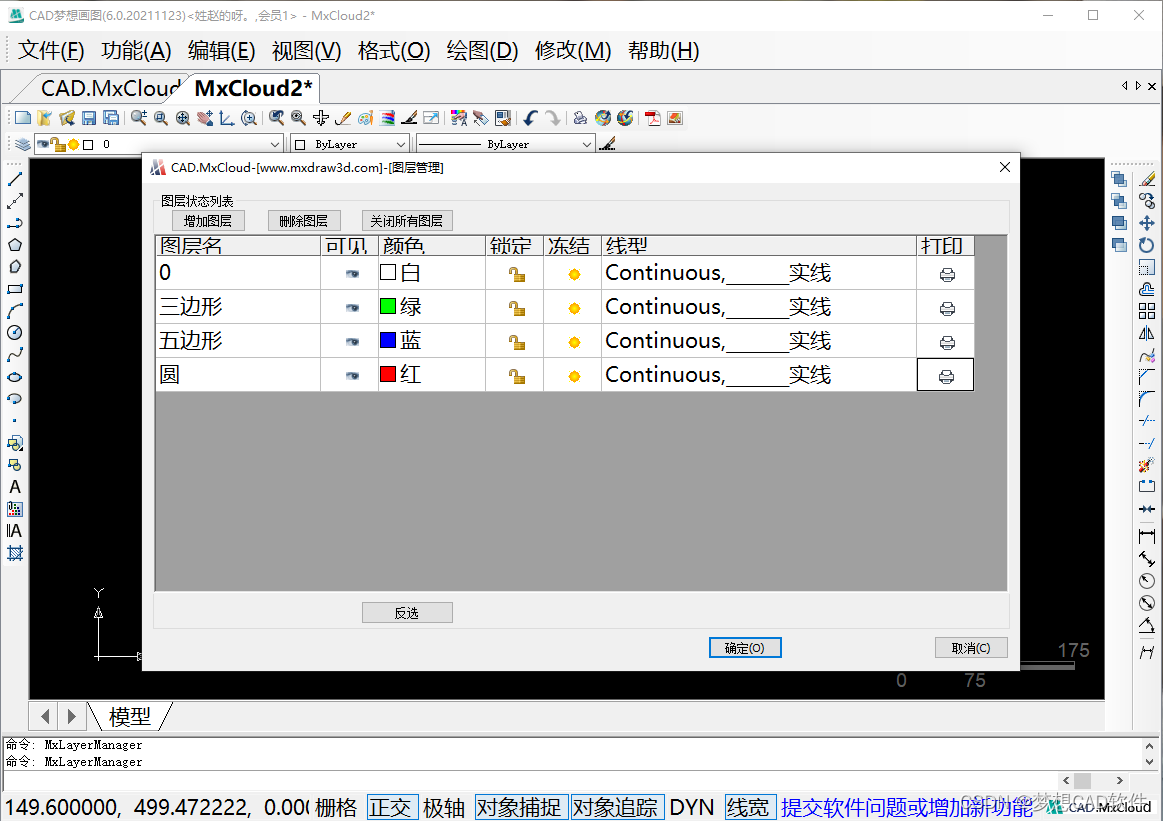
CAD中能显示打印不显示
![Jerry added the process of turning off the touch module before turning it off [chapter]](/img/28/5e4eb39243a0c973d0b90f76571f9b.png)
Jerry added the process of turning off the touch module before turning it off [chapter]
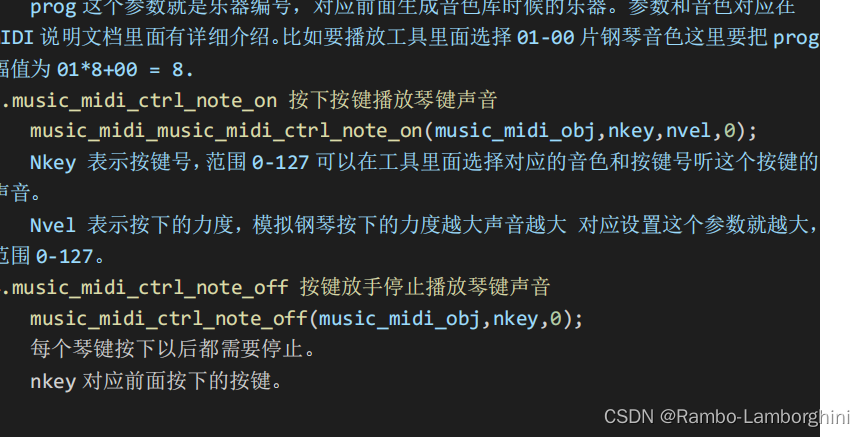
杰理之AD 系列 MIDI 功能说明【篇】
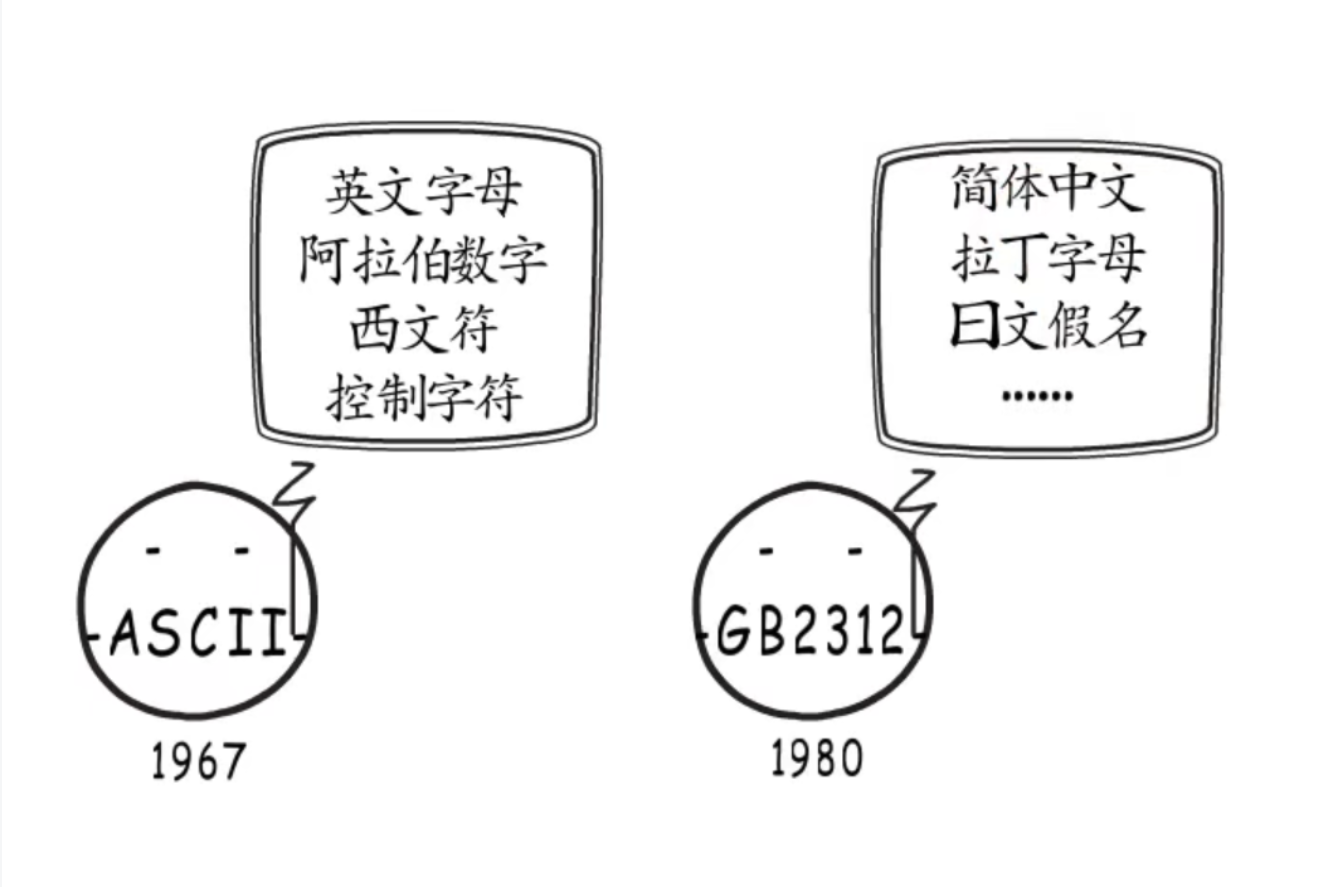
UTF encoding and character set in golang

杰理之增加进关机前把触摸模块关闭流程【篇】

【C語言】符號的深度理解
改善机器视觉系统的方法
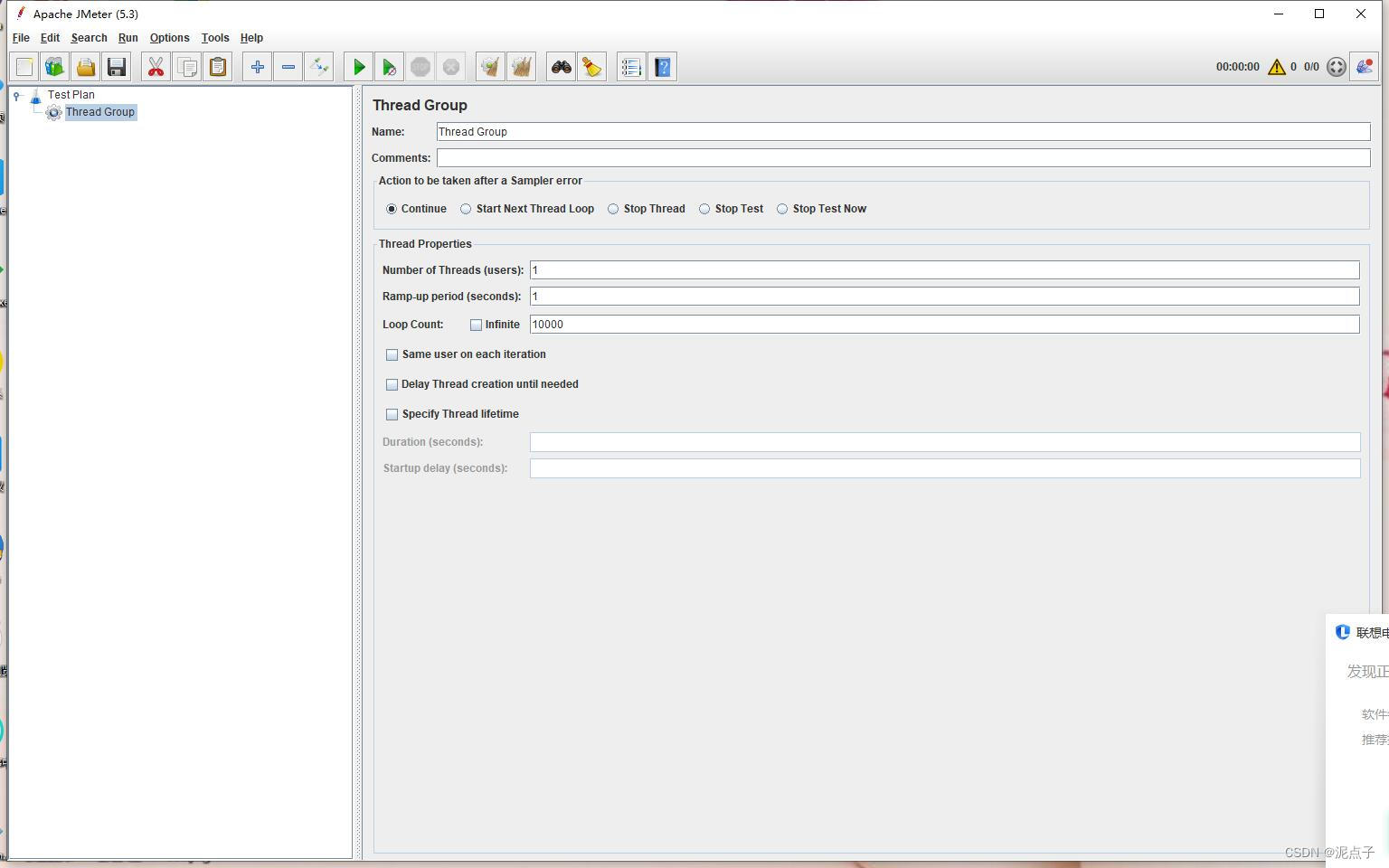
Introduction to pressure measurement of JMeter
![[ 每周译Go ] 《How to Code in Go》系列文章上线了!!](/img/bf/77253c87bfa1512f4b8d3d8f7ebe80.png)
[ 每周译Go ] 《How to Code in Go》系列文章上线了!!
随机推荐
杰理之AD 系列 MIDI 功能说明【篇】
杰理之AD 系列 MIDI 功能说明【篇】
Operation of adding material schedule in SolidWorks drawing
OMS系统实战的三两事
数十亿公民信息遭泄漏!公有云上的数据安全还有“救”吗?
Use of class methods and class variables
Delphi SOAP WebService 服务器端多个 SoapDataModule 实现相同的接口方法,接口继承
Render function and virtual DOM
Jerry's ad series MIDI function description [chapter]
Kubedm initialization error: [error cri]: container runtime is not running
学习突围3 - 关于精力
redis RDB AOF
每日一题-LeetCode1200-最小绝对差-数组-排序
Enlightenment of maker thinking in Higher Education
Introduction to pressure measurement of JMeter
MP3是如何诞生的?
ArcGIS 10.2.2 | solution to the failure of ArcGIS license server to start
股票开户佣金最低多少,炒股开户佣金最低网上开户安全吗
解析互联网时代的创客教育技术
Redis transaction