当前位置:网站首页>What is web application security testing technology?
What is web application security testing technology?
2022-07-01 17:58:00 【Yisixun College】
In order to find software vulnerabilities and defects , Make sure Web The application is secure before and after delivery , We need to make use of Web Apply security testing techniques to identify Web Weaknesses and vulnerabilities of the architecture in the application , And before hackers can find and use them .
Web After years of development, applied security testing technology , At present, the commonly used technologies in the industry are mainly divided into 3 Major categories .
DAST:
Dynamic application security testing (Dynamic Application Security Testing) Technology analyzes the dynamic running state of an application in the test or run phase . It simulates hackers to attack applications dynamically , Analyze the response of the application , To determine the Web Whether the application is vulnerable .
DAST It is a black box testing technology , Is currently the most widely used 、 Use the simplest one Web Apply security testing methods , Tools commonly used by safety engineers, such as AWVS、AppScan Waiting is based on DAST Principle products .
SAST:
Static application security testing (Static Application Security Testing) Technology usually analyzes the syntax of the application's source code or binary files in the coding phase 、 structure 、 The process 、 Interface to find the security vulnerabilities in the program code .
exceed 50% The security vulnerability of is caused by wrong coding , Developers generally lack safety development awareness and skills , Pay more attention to the realization of business functions . If you want to control vulnerabilities from the source, you need to develop a code detection mechanism ,SAST It is a kind of test plan to test the source code and find security vulnerabilities in the development stage .
IAST:
Interactive application security testing (Interactive Application Security Testing) yes 2012 year Gartner A new application security testing solution proposed by the company , Through agency 、VPN Or deploy on the server side Agent Program , collect 、 monitor Web Application runtime function execution 、 The data transfer , And interact with the scanner in real time , Efficient 、 Accurately identify security defects and vulnerabilities , At the same time, it can accurately determine the code file where the vulnerability lies 、 Row number 、 Functions and parameters .IAST Equivalent to DAST and SAST An interrelated runtime security detection technology combined with .
IAST Interactive application security testing technology is a hot new application security testing technology in recent years , Ever been Gartner The consulting company is listed as a leader in the field of network security Top 10 One of the technologies .IAST Integrated DAST and SAST The advantages of , The vulnerability detection rate is very high 、 False positives are extremely low , At the same time, you can locate API Interfaces and code snippets .
边栏推荐
- Length of learning and changing
- To improve the efficiency of office collaboration, trackup may be the best choice
- 2022 Heilongjiang latest fire protection facility operator simulation test question bank and answers
- MFC obtains local IP (used more in network communication)
- Is it safe to open an ETF account online? What are the steps?
- Penetration practice vulnhub range Nemesis
- Depth first traversal and breadth first traversal [easy to understand]
- What are the legal risks of NFT brought by stars such as curry and O'Neill?
- SLO is increasingly used to achieve observability | Devops
- js如何将带有分割符的字符串转化成一个n维数组
猜你喜欢
What are the legal risks of NFT brought by stars such as curry and O'Neill?

Rotation order and universal lock of unity panel
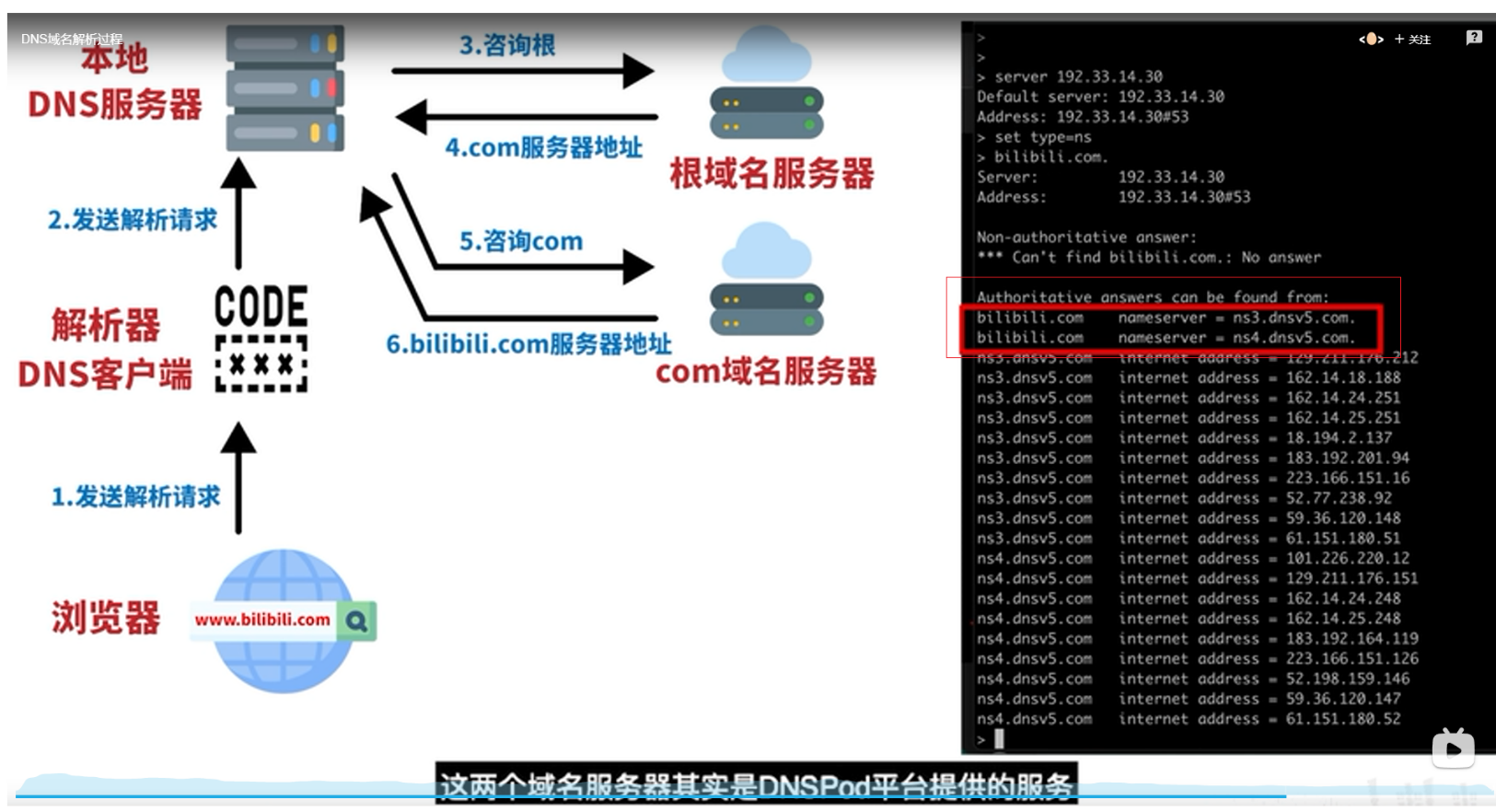
DNS
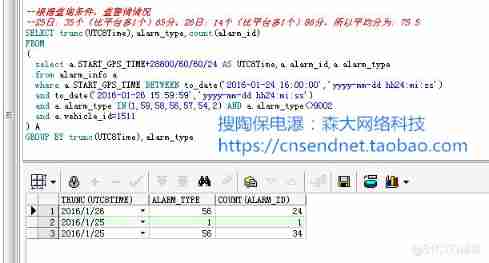
Oracle TRUNC function processing date format
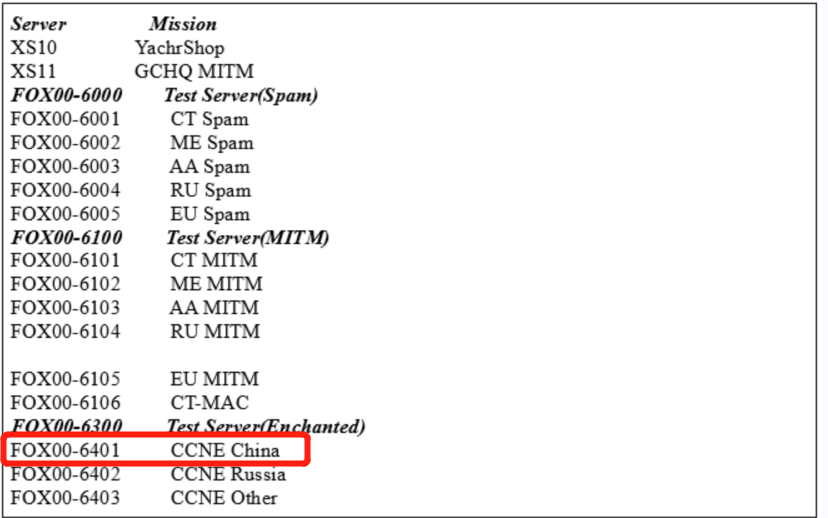
Heavy disclosure! Hundreds of important information systems have been invaded, and the host has become a key attack target

Gameframework eating guide

The new server is packaged with the source code of H5 mall with an operation level value of several thousand

Yuancosmos game farmersworld farmers world - core content of the second conference in China!
![[C supplement] [string] display the schedule of a month by date](/img/9c/5fcc6bfc8fe0f433c0d1eba92b5c3e.jpg)
[C supplement] [string] display the schedule of a month by date
![[Verilog quick start of Niuke network question brushing series] ~ priority encoder circuit ①](/img/24/23f6534e2c74724f9512c5b18661b6.png)
[Verilog quick start of Niuke network question brushing series] ~ priority encoder circuit ①
随机推荐
PHP实现敏感词过滤系统「建议收藏」
股票万1免5证券开户是合理安全的吗,怎么讲
Thinkphp6 - CMS multi wechat management system source code
China PBAT resin Market Forecast and Strategic Research Report (2022 Edition)
The new server is packaged with the source code of H5 mall with an operation level value of several thousand
麦趣尔:媒体报道所涉两批次产品已下架封存,受理消费者诉求
Nearly 60% of the employees strongly support Ctrip's "3+2" working mode, and work at home for two days a week
Cloud picture says | distributed transaction management DTM: the little helper behind "buy buy buy"
Radhat builds intranet Yum source server
Good looking UI mall source code has been scanned, no back door, no encryption
Three dimensional anti-terrorism Simulation Drill deduction training system software
[Verilog quick start of Niuke network question brushing series] ~ priority encoder circuit ①
The latest software scheme of the intelligent information management system of the armed police force
An example of data analysis of an old swatch and an old hard disk disassembly and assembly combined with the sensor of an electromagnetic press
Sword finger offer II 105 Maximum area of the island
Maizeer: the two batches of products reported by the media have been taken off the shelves and sealed, and consumer appeals are accepted
February 16, 2022 Daily: graph neural network self training method under distribution and migration
Rotation order and universal lock of unity panel
Petrv2: a unified framework for 3D perception of multi camera images
Kia recalls some K3 new energy with potential safety hazards