当前位置:网站首页>Shell Scripting
Shell Scripting
2022-07-06 15:59:00 【Star age Cao Botao】
Shell Programming
Once in a while Linux Write something simple in the environment Shell Script , This article can be used as a reference , Write some simple scripts .
Grammatical norms
Define the execution environment
#!/usr/bin/bash
perhaps
#!/usr/bin/env bash | python |perl
perform
Modify the permissions
chmod +x ./demo.sh
perhaps
chmod 700 ./demo.sh
./demo.sh
perhaps
bash ./demo.sh
sh ./demo.sh
# adopt bash sh There is no need to modify permissions , Specify the execution environment
Special symbols
| Symbol | explain |
|---|---|
| ~ | Home directory |
| - | Upper level directory |
| !! | Execute the last order |
| $ | Get environment variables ${USER} |
| ±*/% | Operator |
| * | wildcard Multiple |
| ? | One |
| | | Pipe, |
| \ | Escape character |
| > | Redirect (echo abc > ./demo.txt) |
| >> | Redirect (echo abc >> ./demo.txt) Additional |
| < | wc < abc.txt |
| << |
notes
:<<EOF
The comment ...
The comment ...
The comment ...
EOF
Variable
# Defining variables
name="zhangsan"
age=18
# read-only
readonly name
# Delete variables
unset age
# visit
echo ${name}
# Get string length
echo ${
#name}
# Extract substring
echo ${string:0:2} # Output unoo
Array
arr=("a" "b" "c" "d")
echo arr[0]
# Get all
echo arr[@]
echo arr[*]
# Gets the length of the array
length=${
#arr[@]}
operation
Native bash Simple mathematical operations are not supported , But you can do it with other commands , for example awk and expr,expr The most commonly used .
$(( Arithmetic expression )) or $[ Arithmetic expression ], More efficient .
#!/bin/bash
val=`expr 2 + 2`
echo " The sum of the two is : $val"
# 1.(())
echo $((1+1))
# 2.let
let a+=6 c=a+b
# Be careful , For similar let x+y This way of writing ,Shell Although the calculation x+y Value , But discard the result ; If you don't want to , have access to let sum=x+y take x+y The result of is saved in the variable sum in .
read Read console input
Two points attention :
Space between expression and operator , for example 2+2 It is not right , Must be written as 2 + 2, This is different from most programming languages we are familiar with .
The complete expression is to be `` contain , Note that this character is not a common single quotation mark , stay Esc Key bottom .
Conditional expressions should be placed between square brackets , And there should be spaces , for example : [ a = = a== a==b] It's wrong. , Must be written as [ $a == $b ].
Multiplication sign (*) There must be a backslash in the front () To achieve multiplication ;
| Operator | explain | give an example |
|---|---|---|
| ! | Non operation , Expression for true Then return to false, Otherwise return to true. | [ ! false ] return true. |
| -o | Or operations , There is an expression for true Then return to true. | [ $a -lt 20 -o $b -gt 100 ] return true. |
| -a | And operation , Both expressions are true To return to true. | [ $a -lt 20 -a $b -gt 100 ] return false. |
The file test operator is used to detect Unix Various attributes of the file .
| The operator | explain | give an example |
|---|---|---|
| -b file | Check if the file is a block device file , If it is , Then return to true. | [ -b $file ] return false. |
| -c file | Check whether the file is a character device file , If it is , Then return to true. | [ -c $file ] return false. |
| -d file | Check if the file is a directory , If it is , Then return to true. | [ -d $file ] return false. |
| -f file | Check if the file is a normal file ( It's not a catalog , It's not a device file ), If it is , Then return to true. | [ -f $file ] return true. |
| -g file | Check if the file is set SGID position , If it is , Then return to true. | [ -g $file ] return false. |
| -k file | Check whether the file is set with the adhesive bit (Sticky Bit), If it is , Then return to true. | [ -k $file ] return false. |
| -p file | Check if the file is a named pipeline , If it is , Then return to true. | [ -p $file ] return false. |
| -u file | Check if the file is set SUID position , If it is , Then return to true. | [ -u $file ] return false. |
| -r file | Check whether the file is readable , If it is , Then return to true. | [ -r $file ] return true. |
| -w file | Check whether the file is writable , If it is , Then return to true. | [ -w $file ] return true. |
| -x file | Check if the file is executable , If it is , Then return to true. | [ -x $file ] return true. |
| -s file | Check if the file is empty ( Is the file size greater than 0), Not empty return true. | [ -s $file ] return true. |
| -e file | Test files ( Including directory ) Whether there is , If it is , Then return to true. | [ -e $file ] return true. |
Other checkers :
- -S: Determine whether a file is socket.
- -L: Check whether the file exists and is a symbolic link .
Process control
if
if condition1
then
command1
elif condition2
then
command2
else
commandN
fi
for
for var in item1 item2 ... itemN
do
command1
command2
...
commandN
done
for((i=1;i<=5;i++))
do
echo " This is the first $i Secondary call ";
done;
while
while condition
do
command
done
# Example
#!/bin/bash
int=1
while(( $int<=5 ))
do
echo $int
let "int++"
done
File contains
adopt . Import the files that need to be included
边栏推荐
猜你喜欢
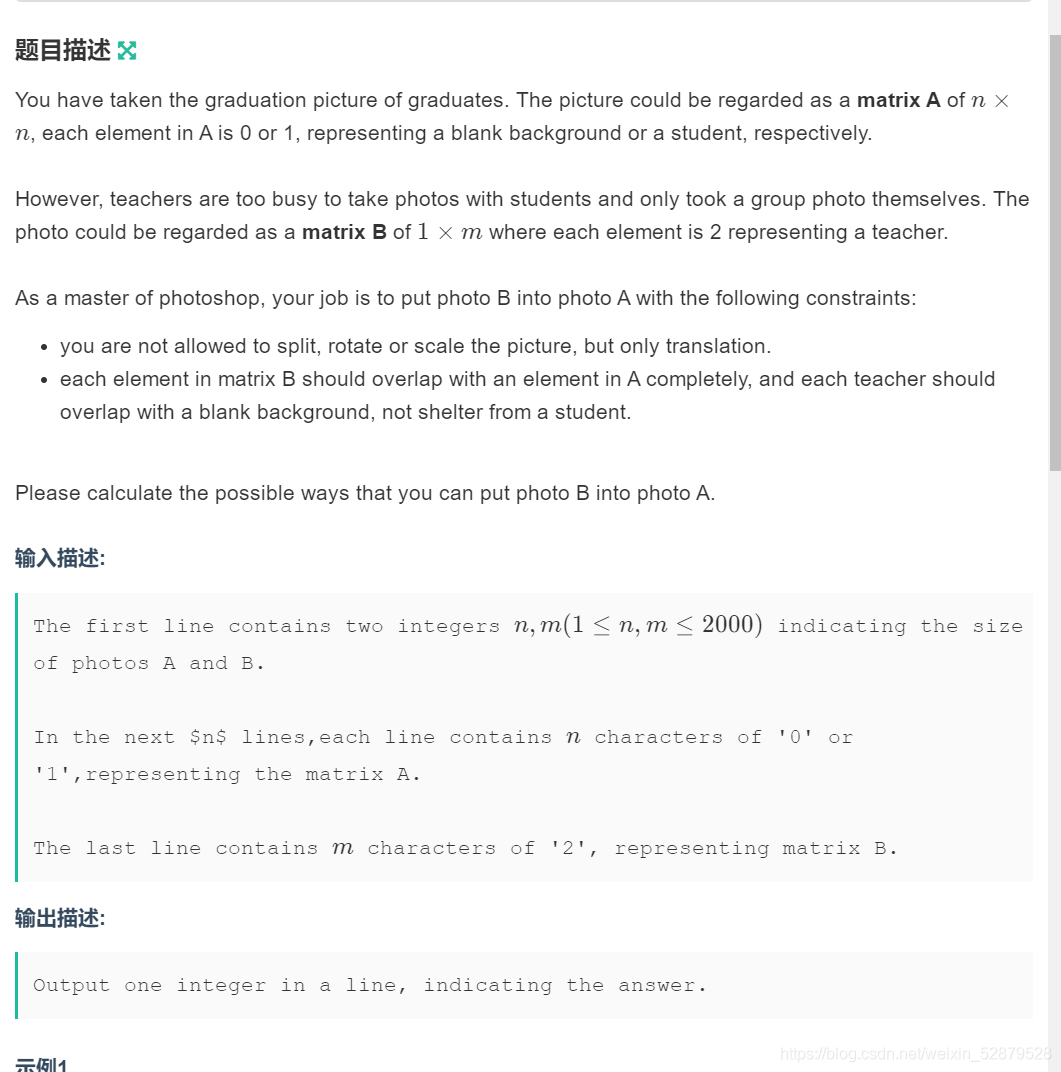
Determine the Photo Position
Gartner: five suggestions on best practices for zero trust network access

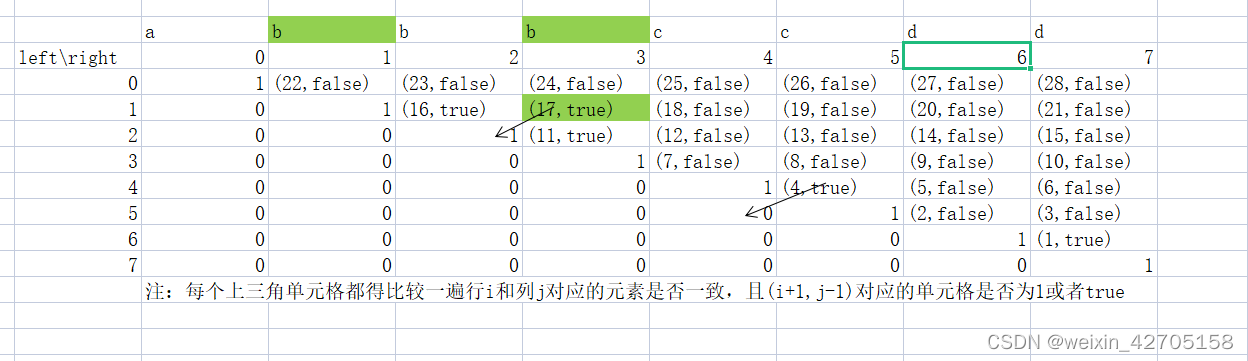
【高老师UML软件建模基础】20级云班课习题答案合集

信息安全-安全编排自动化与响应 (SOAR) 技术解析
力扣刷题记录
![MySQL import database error [err] 1273 - unknown collation: 'utf8mb4_ 0900_ ai_ ci’](/img/e6/f4a696179282fe1f4193410c5a493a.png)
MySQL import database error [err] 1273 - unknown collation: 'utf8mb4_ 0900_ ai_ ci’
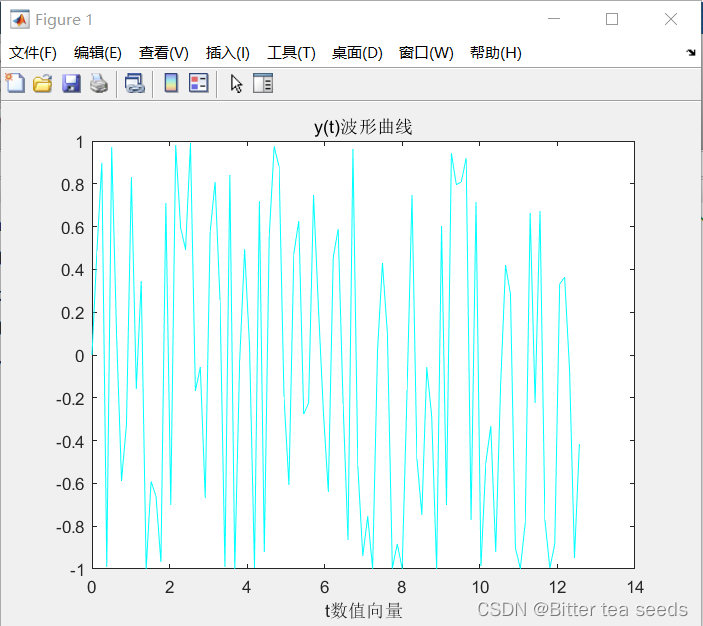
MATLAB综合练习:信号与系统中的应用
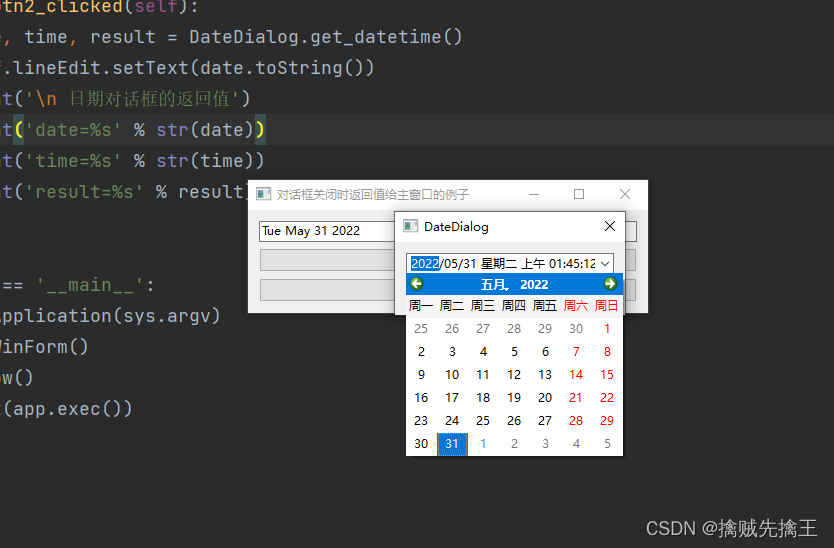
PySide6 信号、槽
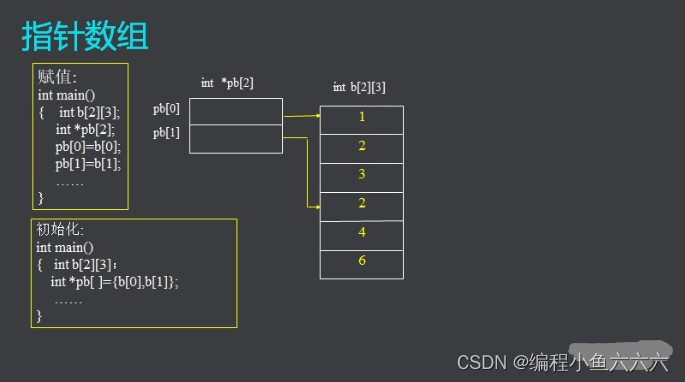
C语言学习笔记
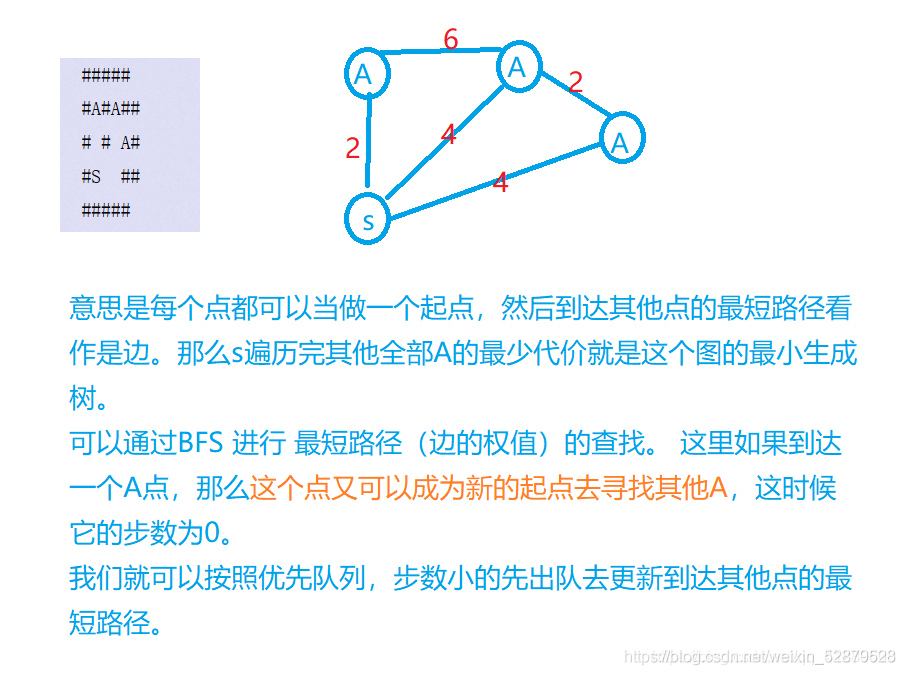
Borg Maze (BFS+最小生成树)(解题报告)
随机推荐
[exercise-4] (UVA 11988) broken keyboard = = (linked list)
信息安全-安全专业名称|CVE|RCE|POC|VUL|0DAY
Market trend report, technical innovation and market forecast of lip care products in China and Indonesia
Opencv learning log 13 corrosion, expansion, opening and closing operations
0-1 knapsack problem (I)
Shell脚本编程
F - Birthday Cake(山东省赛)
【练习-4】(Uva 11988)Broken Keyboard(破损的键盘) ==(链表)
STM32 how to use stlink download program: light LED running light (Library version)
Nodejs+vue online fresh flower shop sales information system express+mysql
动态规划前路径问题优化方式
【练习-7】(Uva 10976)Fractions Again?!(分数拆分)
HDU - 6024 Building Shops(女生赛)
初入Redis
【练习-11】4 Values whose Sum is 0(和为0的4个值)
入门C语言基础问答
【练习-2】(Uva 712) S-Trees (S树)
1010 things that college students majoring in it must do before graduation
【练习-10】 Unread Messages(未读消息)
渗透测试 ( 2 ) --- 渗透测试系统、靶机、GoogleHacking、kali工具