当前位置:网站首页>Offer harvester: add and sum two long string numbers (classic interview algorithm question)
Offer harvester: add and sum two long string numbers (classic interview algorithm question)
2022-07-07 08:12:00 【Extraordinary~】
In the interview , To ease the embarrassment of the interview , In some interviews, you will write simple algorithm problems to ease the atmosphere, such as bubbling, simple algorithm problems , Today, I bring you an algorithm problem I encountered, and share it with him , Ideas are written in the comments of the corresponding code , If you don't understand, you can have a look , You can point out what is wrong with the code
package com.interview;
import com.sun.javafx.image.BytePixelSetter;
public class Test2 {
public static void main(String[] args) {
String str1 = "568658123123312123123123123123131233132123123123131231233123131231231231231";
String str2 = "132121231231231312312312312312312312312312312312313123123101";
//reverse() The method is to reverse the string .
//StringBuffer Class is a variable string class , It can be used to store strings .
StringBuffer s1 = new StringBuffer(str1).reverse();
StringBuffer s2 = new StringBuffer(str2).reverse();
StringBuffer res = new StringBuffer();
int len1 = s1.length();
int len2 = s2.length();
int len;
// If two strings are not the same length , Then take the length of the larger string .
if (len1 < len2) {
// intend : If len1<len2, be len=len2, otherwise len=len1.
len = len2;
// use len2-len1 To fill in len1 The vacancy of .
int count = len2 - len1;
// Complete the shorter string with the longer string .
while (count-- > 0)
// Fill that vacancy . Additional
s1.append("0");
} else {
// If two strings have the same length , Then take the length of the larger string .
len = len1;
// use len1-len2 To fill in len2 The vacancy of .
int count = len1 - len2;
// Complete the shorter string with the longer string .
while (count-- > 0)
s2.append("0");
}
int overflow = 0;
int num;
// Traverse each character of two strings , Add two characters .
for (int i = 0; i < len; i++) {
//charAt() The method is to return the character at the specified index .
//num It's string ASCII Code value .
num = s1.charAt(i) - '0' + s2.charAt(i) - '0' + overflow;
// If the added number is greater than 9, Then subtract 10, And will overflow Set to 1.
if (num >= 10) {
// Subtract... From the added number 10.
overflow = 1;
// Convert the added numbers into characters .
num = num - 10;
} else {
// If the added number is less than 10, Will overflow Set to 0.
overflow = 0;
}
// Convert the added numbers into characters .
res.append(String.valueOf(num));
}
// If the added number is greater than 9, Then subtract 10, And will overflow Set to 1.
if (overflow == 1)
// Convert the added numbers into characters .
res.append("1");
// Convert the result to a string .
System.out.println(res.reverse().toString());
}
}
This is the main idea, which is to sum through inversion
边栏推荐
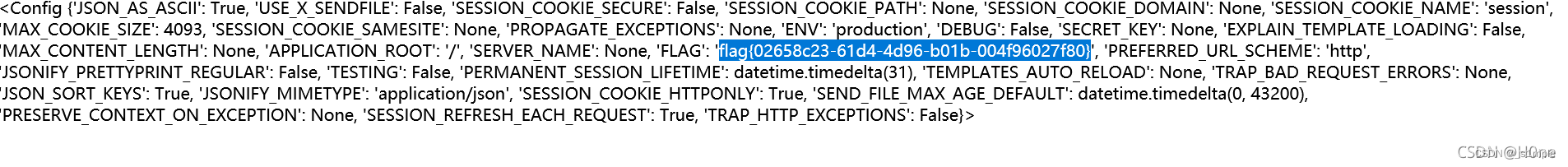
- Bugku CTF daily one question chessboard with only black chess
- 漏洞複現-Fastjson 反序列化
- 贝叶斯定律
- Basic use of CTF web shrink template injection nmap
- Linux server development, MySQL index principle and optimization
- Use of JMeter
- Who has docker to install MySQL locally?
- Introduction to basic components of wechat applet
- JS cross browser parsing XML application
- Qinglong panel -- Huahua reading
猜你喜欢
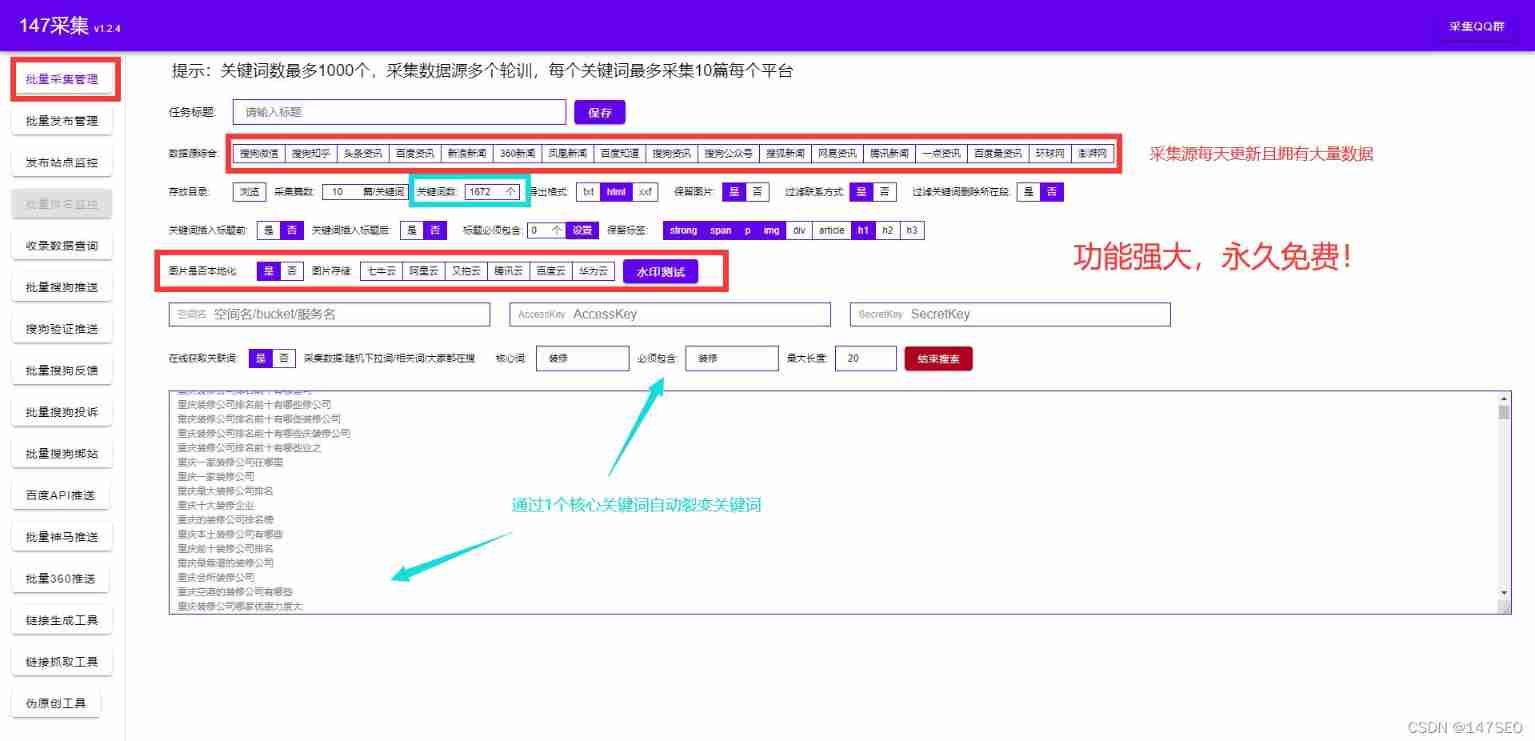
Empire CMS collection Empire template program general

Fast parsing intranet penetration escorts the document encryption industry

Real time monitoring of dog walking and rope pulling AI recognition helps smart city
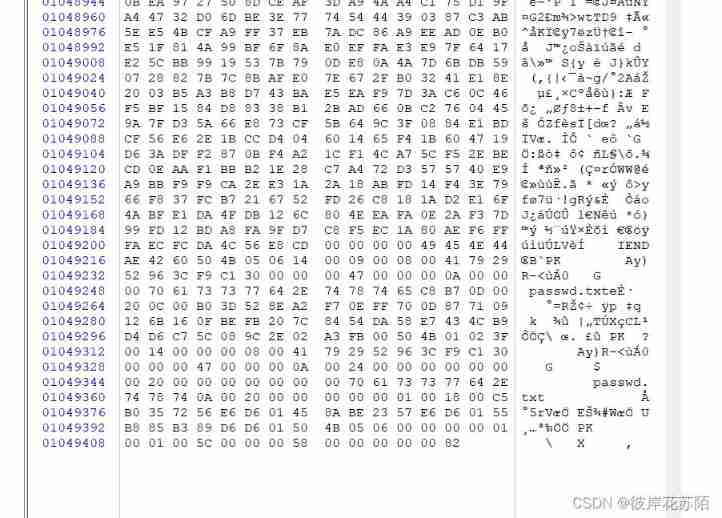
Bugku CTF daily one question chessboard with only black chess
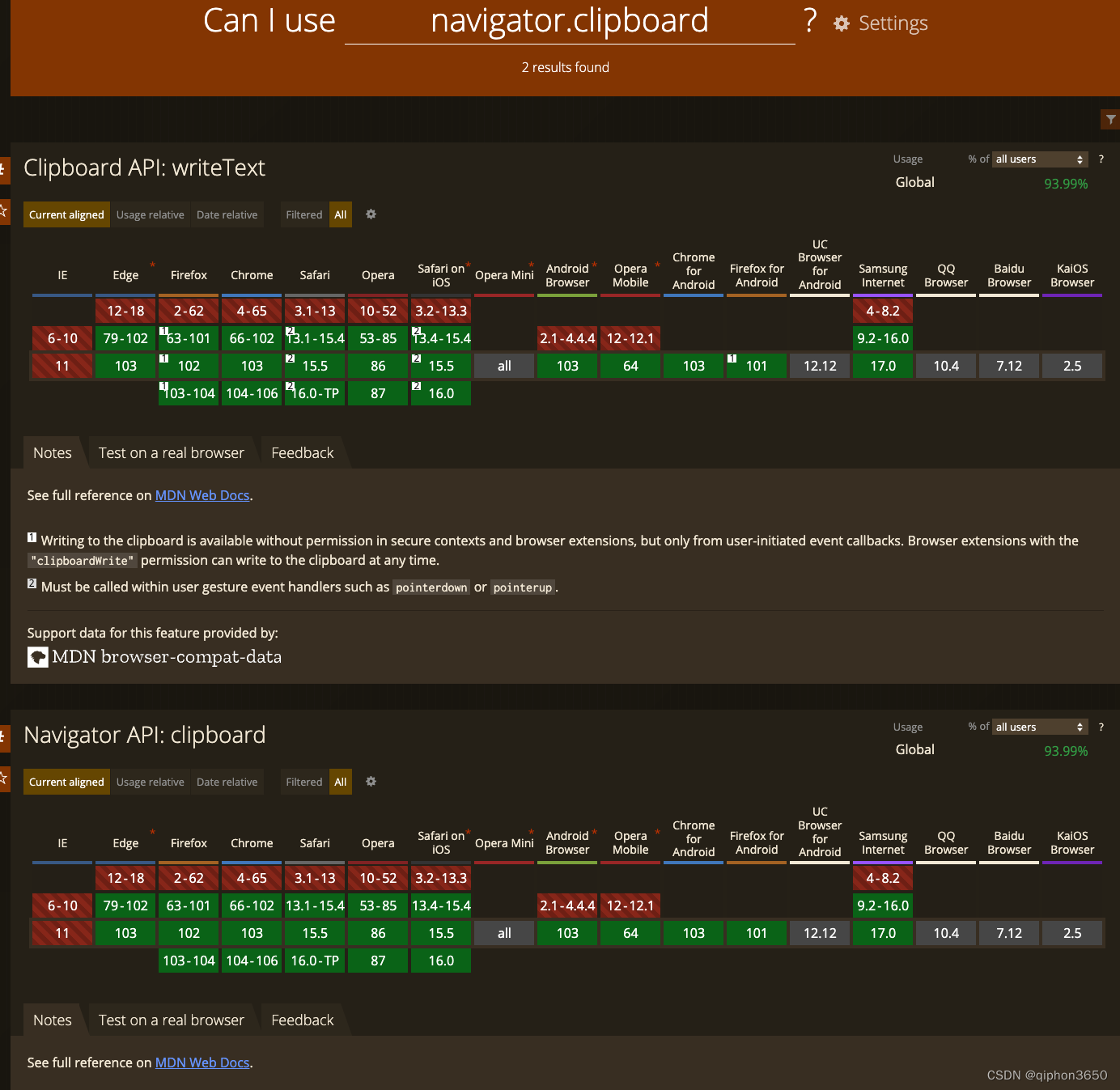
JS复制图片到剪切板 读取剪切板
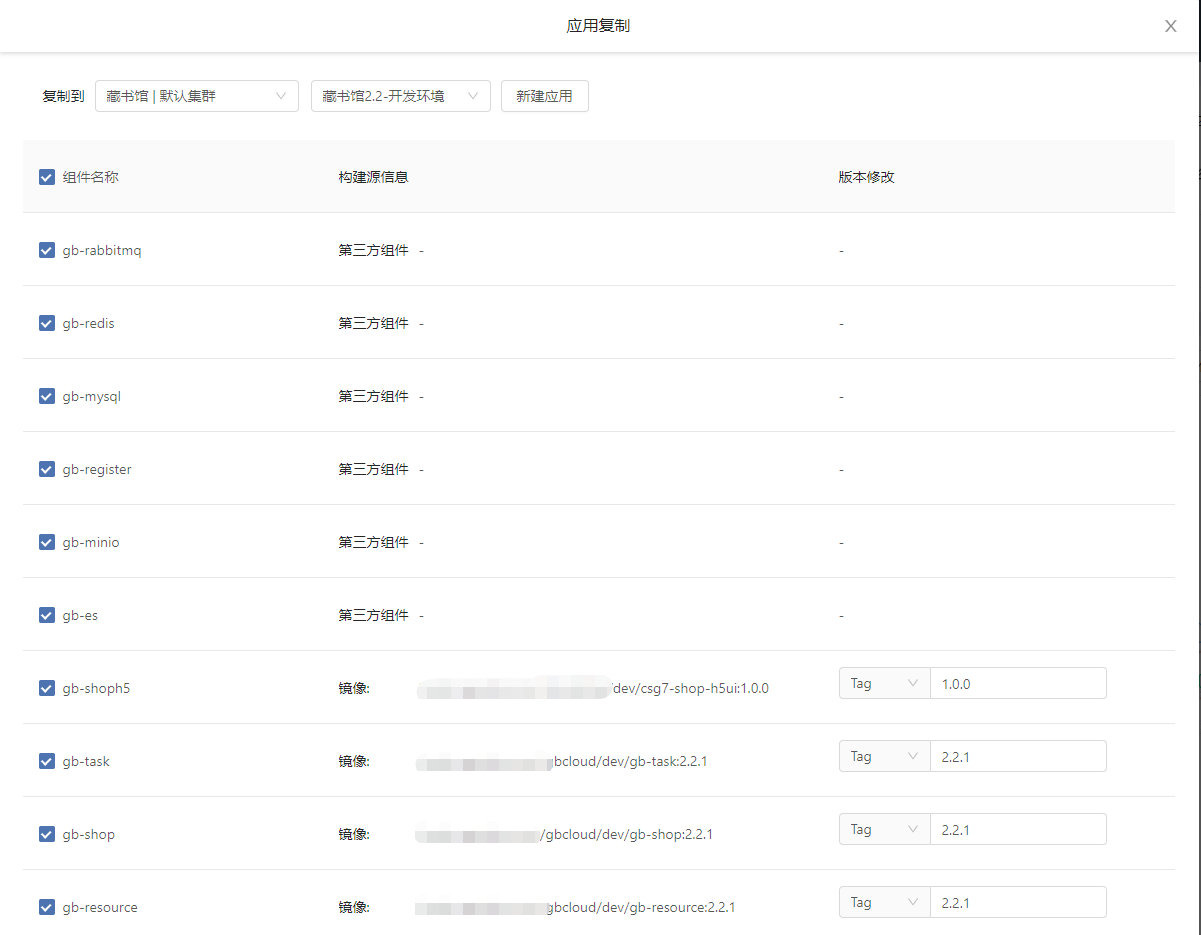
藏书馆App基于Rainbond实现云原生DevOps的实践

Quick analysis of Intranet penetration helps the foreign trade management industry cope with a variety of challenges
央视太暖心了,手把手教你写HR最喜欢的简历
Basic use of CTF web shrink template injection nmap

Interactive book delivery - signed version of Oracle DBA work notes
随机推荐
Complex network modeling (III)
Qinglong panel -- finishing usable scripts
Content of string
Merging binary trees by recursion
2022 National latest fire-fighting facility operator (primary fire-fighting facility operator) simulation questions and answers
Qinglong panel -- Huahua reading
Pytorch(六) —— 模型调优tricks
Avatary的LiveDriver试用体验
Recursive construction of maximum binary tree
The element with setfieldsvalue set is obtained as undefined with GetFieldValue
OpenJudge NOI 2.1 1752:鸡兔同笼
Network learning (I) -- basic model learning
Notes on PHP penetration test topics
Main window in QT learning 27 application
复杂网络建模(一)
海信电视开启开发者模式
2022 Inner Mongolia latest advanced fire facility operator simulation examination question bank and answers
青龙面板--花花阅读
QT learning 26 integrated example of layout management
Implementation of replacement function of shell script