当前位置:网站首页>interrupt and pendSV
interrupt and pendSV
2022-07-31 07:39:00 【South wave son】
1. Overview
The reader has already understood the detailed process of task switching through the task and task switching section. In fact, it is far from enough to realize the function of task switching.Because, the operation of PSP must be in privileged mode, and the user's program is working in thread mode.Therefore, if the user wants to realize the task switching function, he must find a way to make the CPU work in the privileged mode.I might need to know more to understand how embedding is an operating system implementation.
The following content is highly platform-dependent, but the principles are similar.The content mentioned here is explained based on the ARM Cortex-M processor.
2. Operating modes and privilege levels of the CPU
Generally, a CPU will have different operation modes and privilege levels to realize the distinction between the operating system level and the user level, and then further control the operation authority.We all know that each user of the Linux system has different operating permissions from the root user, and the application layer and the kernel layer also have different permissions for hardware operations.How does Linux implement permission control?I wonder if any readers have asked similar questions?In fact, the control of permissions is not only implemented at the software level, but also needs to be supported by hardware at a certain level.
We take the ARM Cortex-M family of processors as an example, which supports two processor operating modes and two privilege levels.
Two modes of operation:
- handler mode: interrupt and exception execution code is in this mode
- thread mode: other code is in this mode
The original intention of introducing the two modes is to distinguish the code of the ordinary application and the code of the exception service routine - including the code of the interrupt service routine.
Two privilege levels:
- Privilege Level
- User level
This can provide a protection mechanism for memory access, so that ordinary user program code cannot accidentally, even maliciously, perform critical operations.The processor supports two privilege levels, which is also a basic security model.
边栏推荐
猜你喜欢
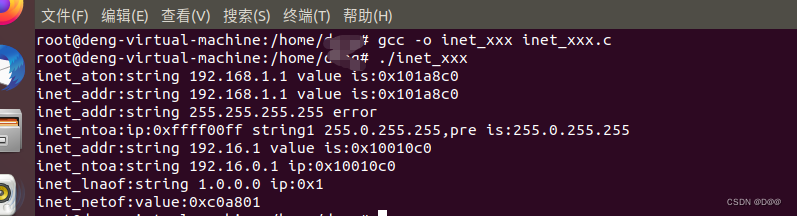
Obtaining server and client information

2. (1) Chained storage of stack, operation of chain stack (illustration, comment, code)

【第四章】详解Feign的实现原理

小实战项目之——吃货联盟订餐系统

电脑开机密码怎么设置?如何给你的电脑加上“安全锁”

LeetCode brush # 376 # Medium - swing sequence

Leetcode952. 按公因数计算最大组件大小
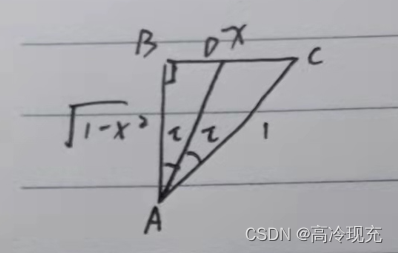
关于求反三角函数的三角函数值

那些破釜沉舟入局Web3.0的互联网精英都怎么样了?
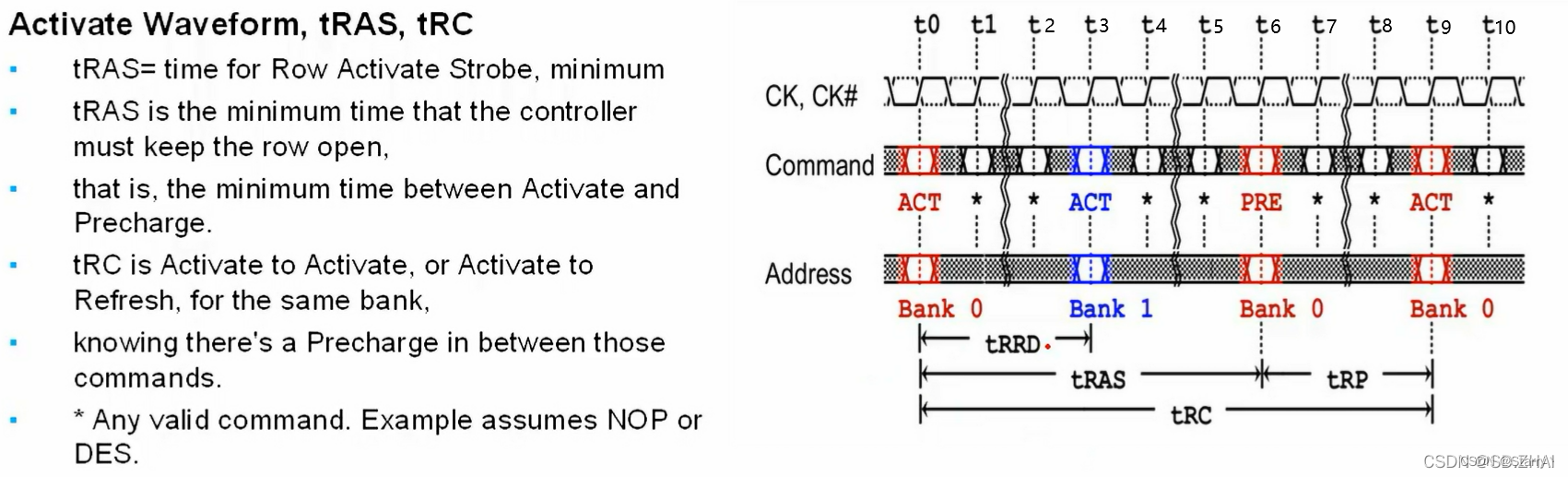
双倍数据速率同步动态随机存储器(Double Data Rate Synchronous Dynamic Random Access Memory, DDR SDRAM)- 逻辑描述部分
随机推荐
Kubernetes scheduling
【Go】Go 语言切片(Slice)
MySQL笔记下
SQL Server Datetime2数据类型
2022.07.15_每日一题
那些破釜沉舟入局Web3.0的互联网精英都怎么样了?
金融租赁业务
【Go报错】go go.mod file not found in current directory or any parent directory 错误解决
外贸网站优化-外贸网站优化教程-外贸网站优化软件
leetcode 406. Queue Reconstruction by Height
2022.07.20_每日一题
芯塔电子斩获第十一届中国双创大赛芜湖赛区桂冠
Difficulty comparison between high concurrency and multithreading (easy to confuse)
【解决】mysql本地计算机上的MySQL服务启动后停止。某些服务在未由其他服务或程序使用时将自动停止
Install the gstreamer development dependency library to the project sysroot directory
2.(1)栈的链式存储、链栈的操作(图解、注释、代码)
【微服务】Nacos集群搭建以及加载文件配置
测试 思维导图
2022.07.12_每日一题
mysql索引失效的常见9种原因详解