当前位置:网站首页>14. Users, groups, and permissions (14)
14. Users, groups, and permissions (14)
2022-07-05 19:51:00 【51CTO】
Special permissions for the file system
linux There are three common permissions in , There are also three special permissions :suid,sgid,sticky
Special privileges suid
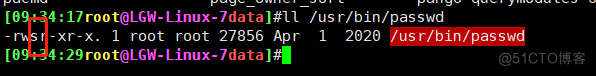
Premise : Processes have owners and groups , The file has the owner and the group ( occupy user The execution permission bit of , The numerical method is 4)
1、 Whether an executable program file of any process can be started as a process , It depends on whether the initiator has Execution Authority on the program file
2、 After starting as a process , The process belongs to the main initiator , The process group is the initiator Group
3、 Permissions for a process to access a file , It depends on the initiator of the process
a、 The originator of the process , The owner of the same document : Then the application file belongs to the primary authority
b、 The originator of the process , Belongs to the file group : Then the file belongs to group permission is applied
c、 Apply file other permissions
Binary executable suid Authority function
Can any executable file be started as a process : It depends on whether the initiator has execution permission for the program file
After starting as a process , The owner of the process is the owner of the original program file
suid Valid only for binary executables
suid Setting on the directory makes no sense
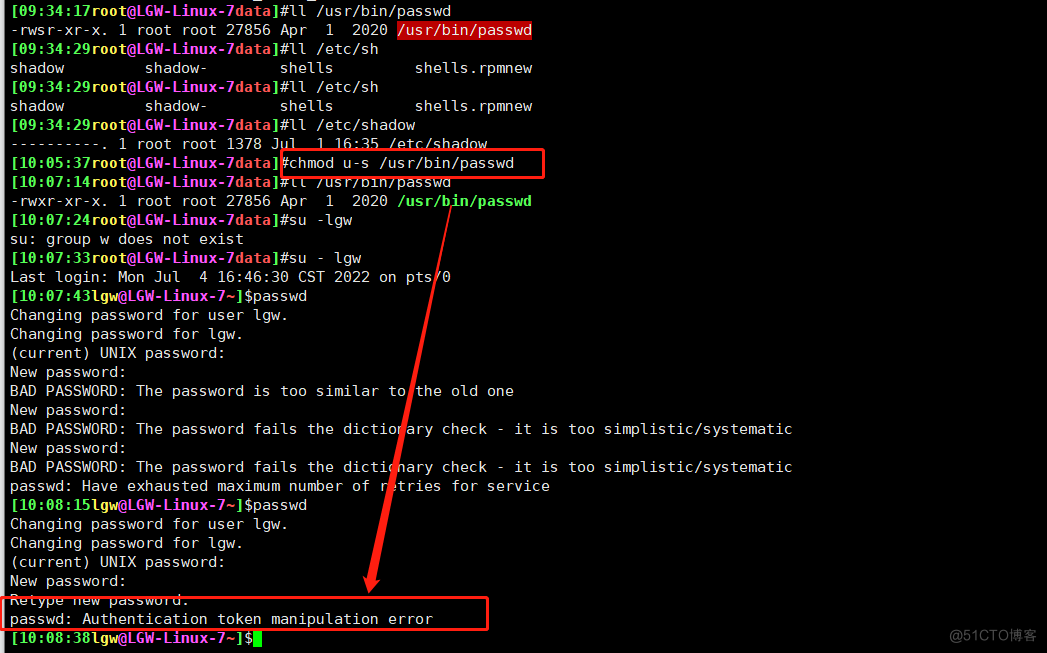
suid Permission setting
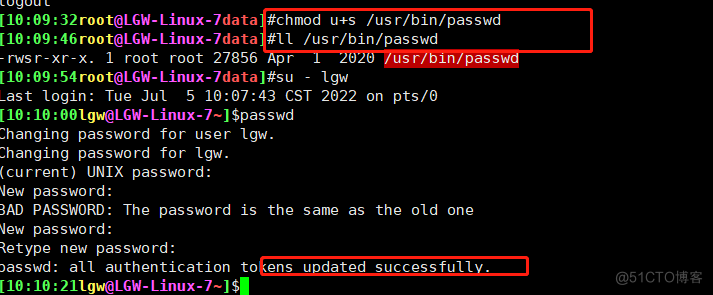
chmod u+s file... chmod 6xxx file chmod u-s file ...
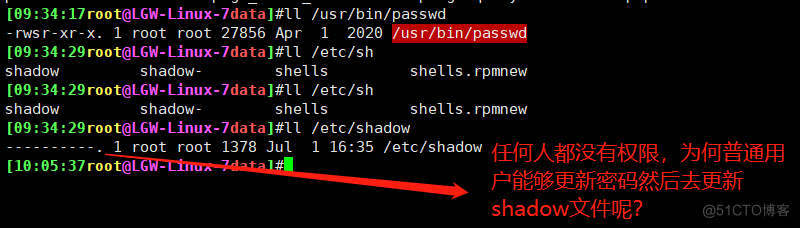
Get rid of s After permission , There is an error in changing the password
To endow with suid The permission can be updated successfully ( Conclusion : have suid Authority ;lgw The user calls passwd On command , Temporarily available /usr/bin/passwd The authority of the owner of and then on shadows updated )
Special privileges sgid
On the binary executable sgid Authority function ( occupy group The execution permission bit of , The numerical method is 2)
Can any executable program file be driven as a process : It depends on whether the initiator has execution permission for the program file
After starting as a process , The process group is the owner of the source program file
sgid Permission setting chmod g+s file... chmod 2xxx file chmod g-s file...
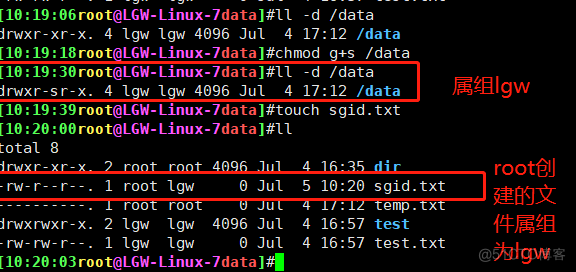
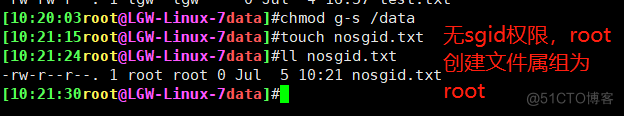
In the catalogue sgid Authority function : By default , When a user creates a file , Its group is the primary group to which the user belongs , Once a directory is set to sgid, The group to which the files created in this directory by users with write permission belong is the group to which this directory belongs , Usually used to create a collaboration Directory .
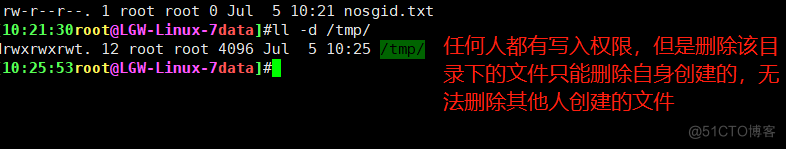
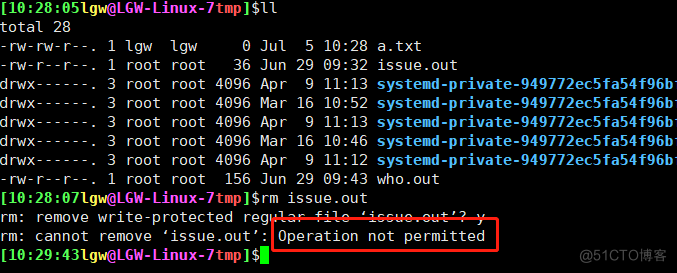
Special privileges sticky
A directory with write permission. Usually, the user can delete any file in the directory , No matter the permission or ownership of the file is set by Ma Yanling sticky position , Only the owner of the document or root You can delete the file .( occupy other The execution permission bit of , The numerical method is 1)
sticky Permission setting chmod o+t dir chmod 1xxx dir chmod o-t dir
other Yes /tmp Directory has write permission , Theoretically, you can delete any file in this directory , But join sticky After permission , You can't
Set the special properties of the file
Set the special properties of the file , You can visit root Users misoperate or modify files
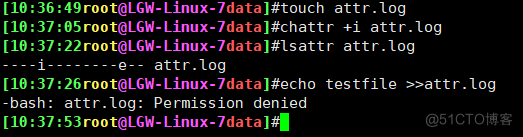
Can't delete , Change of name , change chattr +i
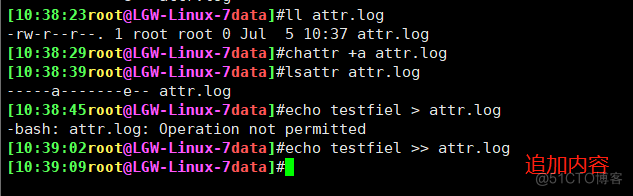
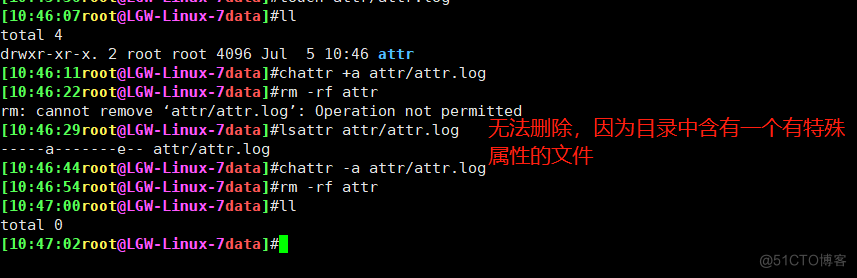
Can only add content , Can't delete , Change of name chattr +a
List specific attributes lsattr
Access control list (ACL)
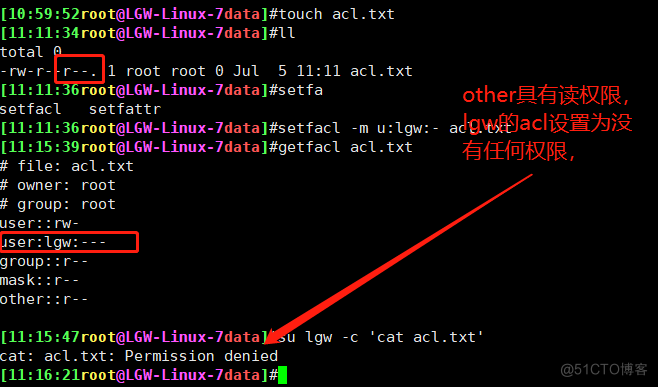
acl:access control list Realize flexible permission management
Except for the owner of the document 、 Group and other, You can set permissions for more users
centos7 Created by default xfs and ext4 The file system has acl function
tune2fs -o acl /dev/sdb1 mount -o acl /dev/sdb1 /mnt
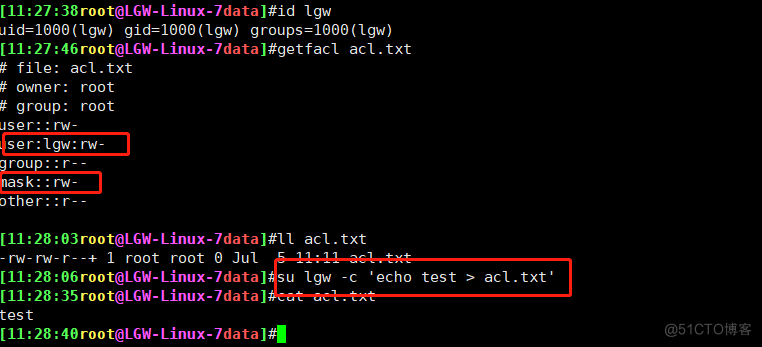
acl The order of entry into force : owner 、 Custom user 、 Subordinate to the group | Custom groups , others
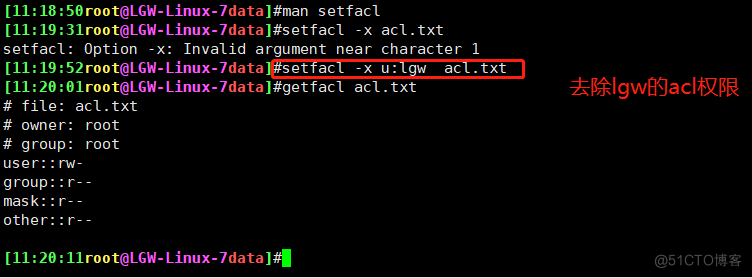
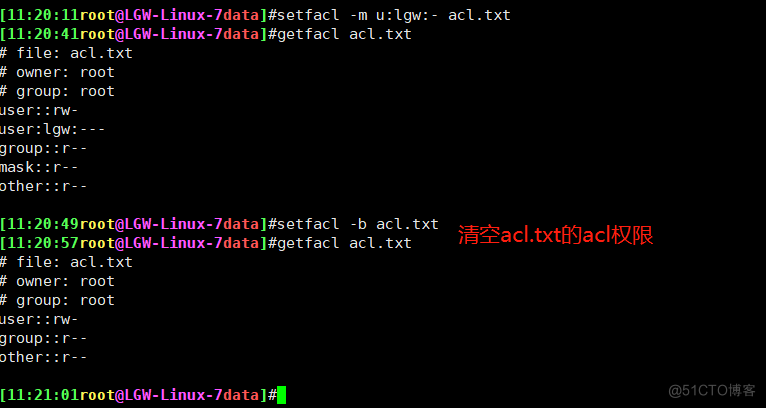
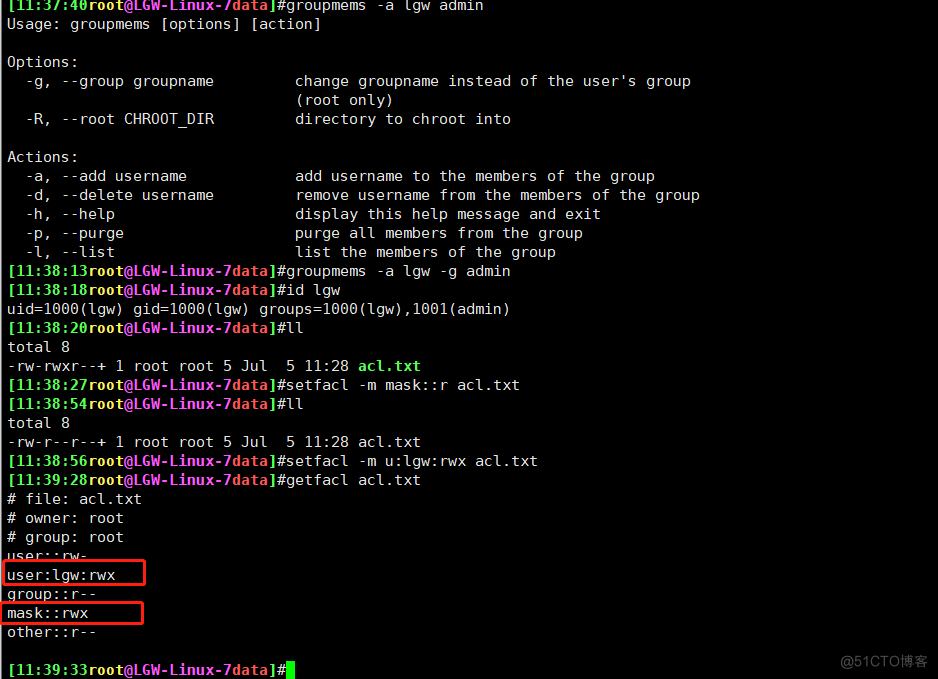
Relevant command setfacl、getfacl
setfacl Set up acl jurisdiction
getfacl Check the settings acl jurisdiction
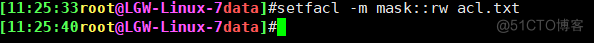
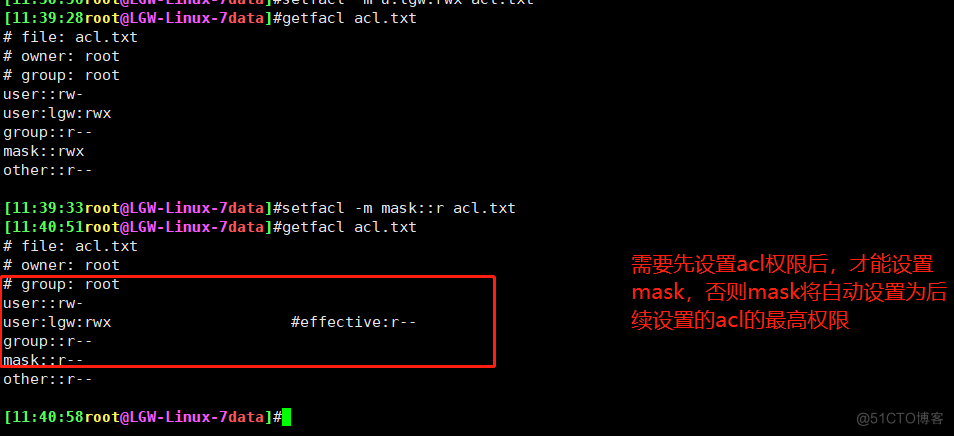
mask jurisdiction
mask Only affect owners and other Maximum permissions for people and groups other than
mask After logic and operation with the user's front line , To become effective permissions (effectice permission)
User or group settings must exist in mask It will take effect only when the permission is set
setfacl -m mask::rx file
other Set up acl Permission is rwx, Lead to mask Also for the rmx
setfacl --set u::rw,u:wang:rw,g::r,o::- file1 --setfacl Option will change the original acl Delete all items , Replace... With a new one , It should be noted that we must treasure the line ugo Set up , Can not be like -m Just add acl Can
Backup restore acl
The main file operation commands are cp and mv All support acl, as long as cp The order needs to add -p Parameters , however tar And other common backup tools don't keep directories and files acl Information
Backup acl getfacl -R /tmp/dir > acl.txt
eliminate acl setfacl -R -b /tmp/dir
Restore acl setfacl -R --set-file=acl.txt /tmp/dir
see acl getfacl -R /tmp/dir

边栏推荐
- Android interview, Android audio and video development
- 毫米波雷达人体感应器,智能感知静止存在,人体存在检测应用
- c——顺序结构
- [hard core dry goods] which company is better in data analysis? Choose pandas or SQL
- 建立自己的网站(16)
- Based on vs2017 and cmake GUI configuration, zxing and opencv are used in win10 x64 environment, and simple detection of data matrix code is realized
- Multi branch structure
- [AI framework basic technology] automatic derivation mechanism (autograd)
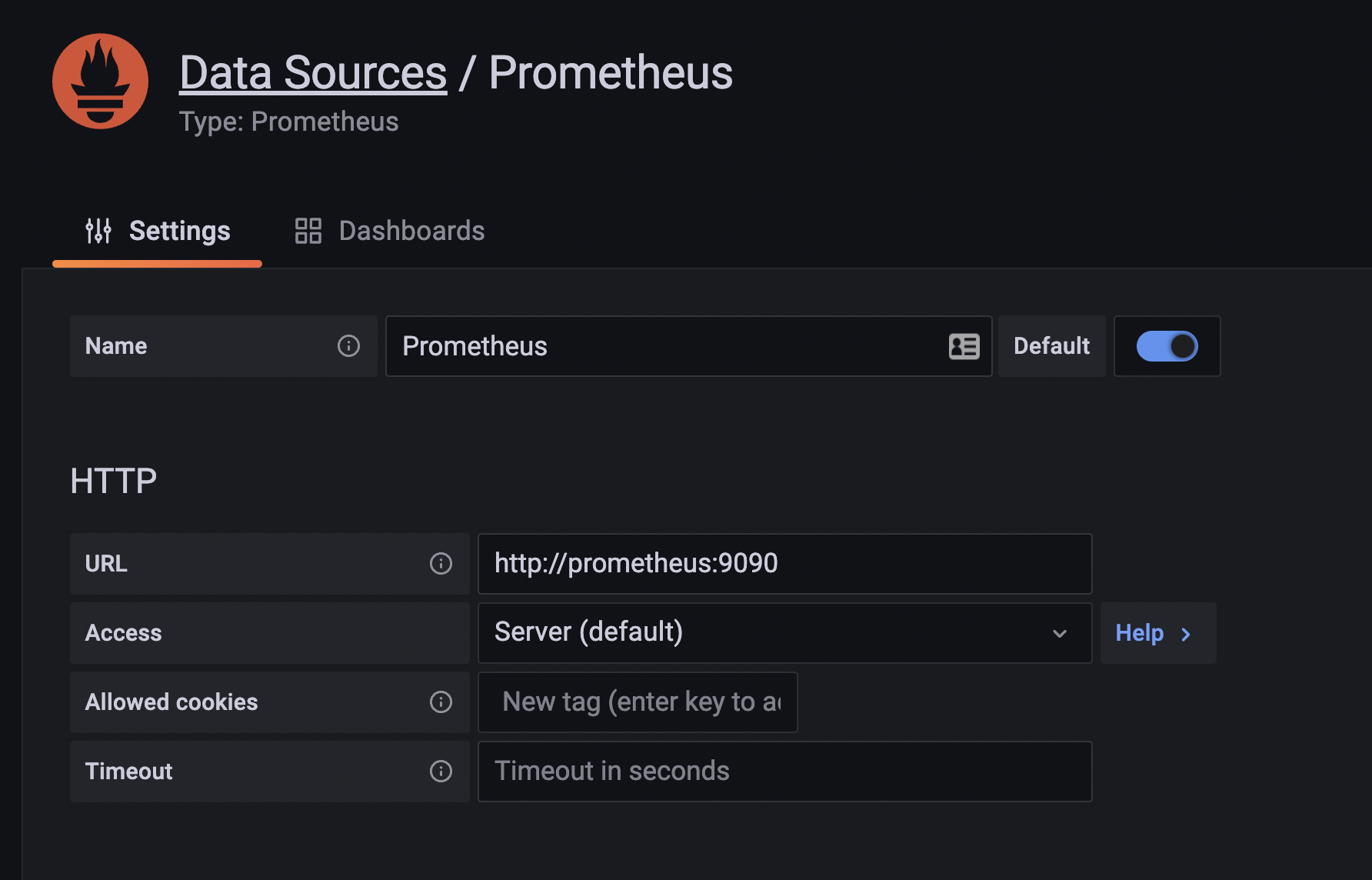
- redis集群模拟消息队列
- How about testing outsourcing companies?
猜你喜欢
![[FAQ] summary of common causes and solutions of Huawei account service error 907135701](/img/1d/0e716533237c0e4463f5d6357395bd.png)
[FAQ] summary of common causes and solutions of Huawei account service error 907135701
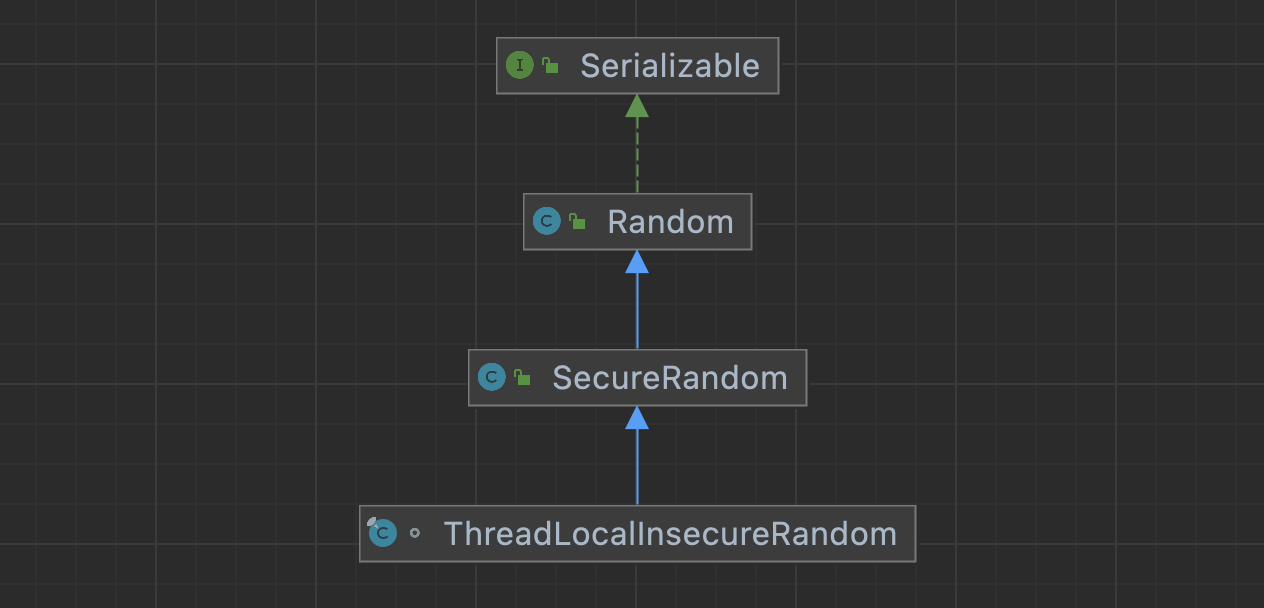
浅浅的谈一下ThreadLocalInsecureRandom
How about testing outsourcing companies?
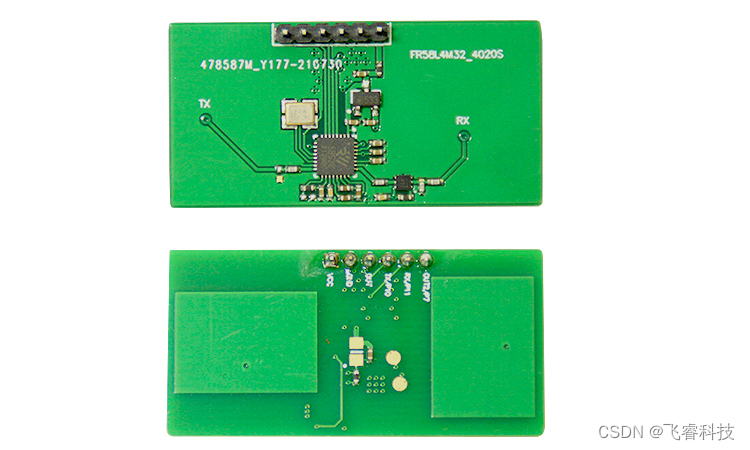
Microwave radar induction module technology, real-time intelligent detection of human existence, static micro motion and static perception
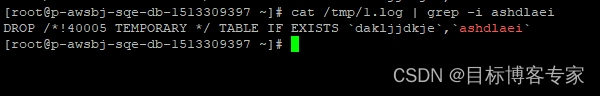
Debezium series: record the messages parsed by debezium and the solutions after the MariaDB database deletes multiple temporary tables

Inventory of the most complete low code / no code platforms in the whole network: Jiandao cloud, partner cloud, Mingdao cloud, Qingliu, xurong cloud, Jijian cloud, treelab, nailing · Yida, Tencent clo
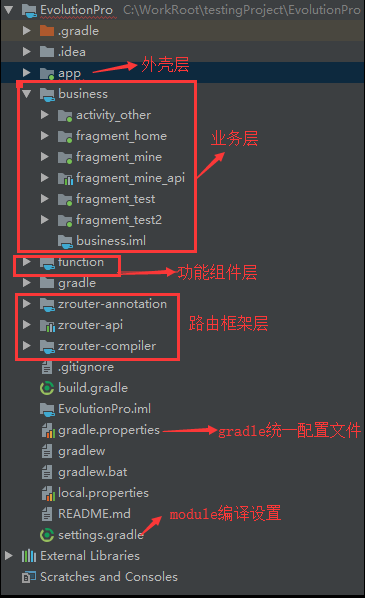
Recommended collection, my Tencent Android interview experience sharing
【无标题】

Bitcoinwin (BCW)受邀参加Hanoi Traders Fair 2022
IBM has laid off 40 + year-old employees in a large area. Mastering these ten search skills will improve your work efficiency ten times
随机推荐
【obs】QString的UTF-8中文转换到blog打印 UTF-8 char*
浅浅的谈一下ThreadLocalInsecureRandom
使用 RepositoryProvider简化父子组件的传值
Common operators and operator priority
成功入职百度月薪35K,2022Android开发面试解答
Redis cluster simulated message queue
Successful entry into Baidu, 35K monthly salary, 2022 Android development interview answer
Debezium series: modify the source code to support drop foreign key if exists FK
How to choose the notion productivity tools? Comparison and evaluation of notion, flowus and WOLAI
太牛了,看这篇足矣了
third-party dynamic library (libcudnn.so) that Paddle depends on is not configured correctl
[FAQ] summary of common causes and solutions of Huawei account service error 907135701
Force buckle 1200 Minimum absolute difference
微波雷达感应模块技术,实时智能检测人体存在,静止微小动静感知
通过POI追加数据到excel中小案例
Debezium series: idea integrates lexical and grammatical analysis ANTLR, and check the DDL, DML and other statements supported by debezium
IBM大面积辞退40岁+的员工,掌握这十个搜索技巧让你的工作效率至上提高十倍
众昂矿业:2022年全球萤石行业市场供给现状分析
UWB ultra wideband positioning technology, real-time centimeter level high-precision positioning application, ultra wideband transmission technology
打新债在哪里操作开户是更安全可靠的呢