当前位置:网站首页>PIP audit: a powerful security vulnerability scanning tool
PIP audit: a powerful security vulnerability scanning tool
2022-07-02 21:42:00 【kali_ Ma】
About pip-audit
pip-audit Is a powerful security vulnerability scanning tool , This tool is mainly aimed at Python Environmental Science , It can help researchers scan and test Python Known security vulnerabilities in the package .pip-audit Used PythonPackagingAdvisory database PyPIJSONAPI As the source of vulnerability report .
Function is introduced
1、 Support for local environment and dependent components (requirements Style file ) Conduct safety audits ;
2、 Support a variety of vulnerability Services (PyPI、OSV);
3、 Support with CycloneDX XML or JSON Format send SBOM;
4、 Provide output formats readable by humans and machines (columnar、JSON);
5、 Seamless access / Reuse local pip cache ;
Tool installation
pip-audit be based on Python Development , And the local environment is required to be Python 3.7 Or later . Install and configure Python After the environment , You can use the following commands and pass pip To install pip-audit 了 :
python -m pip install pip-audit
Third party package
pip-audit The normal operation of requires the use of multiple third-party packages , The specific component package name and version are shown in the figure below :

besides , We can also go through conda To install pip-audit:
conda install -c conda-forge pip-audit
【 One > All resources get < One 】
1、 Network Security Learning Route
2、 electronic text ( amateur )
3、 Safety factory internal video
4、100 Share src file
5、 Common safety interview questions
6、ctf Analysis of the classic title of the competition
7、 Complete kit
8、 Emergency response notes
Tool use
We can directly pip-audit Run as a stand-alone program , Or through “python -m” function :
pip-audit --help
python -m pip_audit --help
usage: pip-audit [-h] [-V] [-l] [-r REQUIREMENTS] [-f FORMAT] [-s SERVICE]
[-d] [-S] [--desc [{on,off,auto}]] [--cache-dir CACHE_DIR]
[--progress-spinner {on,off}] [--timeout TIMEOUT]
[--path PATHS] [-v] [--fix] [--require-hashes]
audit the Python environment for dependencies with known vulnerabilities
optional arguments:
-h, --help show this help message and exit
-V, --version show program's version number and exit
-l, --local show only results for dependencies in the local
environment (default: False)
-r REQUIREMENTS, --requirement REQUIREMENTS
audit the given requirements file; this option can be
used multiple times (default: None)
-f FORMAT, --format FORMAT
the format to emit audit results in (choices: columns,
json, cyclonedx-json, cyclonedx-xml) (default:
columns)
-s SERVICE, --vulnerability-service SERVICE
the vulnerability service to audit dependencies
against (choices: osv, pypi) (default: pypi)
-d, --dry-run without `--fix`: collect all dependencies but do not
perform the auditing step; with `--fix`: perform the
auditing step but do not perform any fixes (default:
False)
-S, --strict fail the entire audit if dependency collection fails
on any dependency (default: False)
--desc [{on,off,auto}]
include a description for each vulnerability; `auto`
defaults to `on` for the `json` format. This flag has
no effect on the `cyclonedx-json` or `cyclonedx-xml`
formats. (default: auto)
--cache-dir CACHE_DIR
the directory to use as an HTTP cache for PyPI; uses
the `pip` HTTP cache by default (default: None)
--progress-spinner {on,off}
display a progress spinner (default: on)
--timeout TIMEOUT set the socket timeout (default: 15)
--path PATHS restrict to the specified installation path for
auditing packages; this option can be used multiple
times (default: [])
-v, --verbose give more output; this setting overrides the
`PIP_AUDIT_LOGLEVEL` variable and is equivalent to
setting it to `debug` (default: False)
--fix automatically upgrade dependencies with known
vulnerabilities (default: False)
--require-hashes require a hash to check each requirement against, for
repeatable audits; this option is implied when any
package in a requirements file has a `--hash` option.
(default: False)
Exit code
When the task is completed , pip-audit Will quit running , And return a code to show its status , among :
0: No known vulnerabilities detected ;
1: One or more known vulnerabilities have been detected ;
Sample tool use
Audit current Python Dependencies in the environment :
$ pip-audit
No known vulnerabilities found
Audit given requirements File dependency :
$ pip-audit -r ./requirements.txt
No known vulnerabilities found
Audit a requirements file , And exclude the system package :
$ pip-audit -r ./requirements.txt -l
No known vulnerabilities found
Security vulnerabilities found in audit dependencies :
$ pip-audit
Found 2 known vulnerabilities in 1 package
Name Version ID Fix Versions
---- ------- -------------- ------------
Flask 0.5 PYSEC-2019-179 1.0
Flask 0.5 PYSEC-2018-66 0.12.3
Audit depends on ( Include description ):
$ pip-audit --desc
Found 2 known vulnerabilities in 1 package
Name Version ID Fix Versions Description
---- ------- -------------- ------------ --------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Flask 0.5 PYSEC-2019-179 1.0 The Pallets Project Flask before 1.0 is affected by: unexpected memory usage. The impact is: denial of service. The attack vector is: crafted encoded JSON data. The fixed version is: 1\. NOTE: this may overlap CVE-2018-1000656.
Flask 0.5 PYSEC-2018-66 0.12.3 The Pallets Project flask version Before 0.12.3 contains a CWE-20: Improper Input Validation vulnerability in flask that can result in Large amount of memory usage possibly leading to denial of service. This attack appear to be exploitable via Attacker provides JSON data in incorrect encoding. This vulnerability appears to have been fixed in 0.12.3\. NOTE: this may overlap CVE-2019-1010083.
Audit JSON Format dependency :
$ pip-audit -f json | jq
Found 2 known vulnerabilities in 1 package
[
{
"name": "flask",
"version": "0.5",
"vulns": [
{
"id": "PYSEC-2019-179",
"fix_versions": [
"1.0"
],
"description": "The Pallets Project Flask before 1.0 is affected by: unexpected memory usage. The impact is: denial of service. The attack vector is: crafted encoded JSON data. The fixed version is: 1\. NOTE: this may overlap CVE-2018-1000656."
},
{
"id": "PYSEC-2018-66",
"fix_versions": [
"0.12.3"
],
"description": "The Pallets Project flask version Before 0.12.3 contains a CWE-20: Improper Input Validation vulnerability in flask that can result in Large amount of memory usage possibly leading to denial of service. This attack appear to be exploitable via Attacker provides JSON data in incorrect encoding. This vulnerability appears to have been fixed in 0.12.3\. NOTE: this may overlap CVE-2019-1010083."
}
]
},
{
"name": "jinja2",
"version": "3.0.2",
"vulns": []
},
{
"name": "pip",
"version": "21.3.1",
"vulns": []
},
{
"name": "setuptools",
"version": "57.4.0",
"vulns": []
},
{
"name": "werkzeug",
"version": "2.0.2",
"vulns": []
},
{
"name": "markupsafe",
"version": "2.0.1",
"vulns": []
}
]
Audit and try to automatically audit vulnerable dependencies :
$ pip-audit --fix
Found 2 known vulnerabilities in 1 package and fixed 2 vulnerabilities in 1 package
Name Version ID Fix Versions Applied Fix
----- ------- -------------- ------------ ----------------------------------------
flask 0.5 PYSEC-2019-179 1.0 Successfully upgraded flask (0.5 => 1.0)
flask 0.5 PYSEC-2018-66 0.12.3 Successfully upgraded flask (0.5 => 1.0)
License agreement
The development and release of this project follows Apache 2.0 Open source license agreement .
边栏推荐
- Off chip ADC commissioning record
- MySQL learning record (9)
- Analyze comp-206 advanced UNIX utils
- Plastic floating dock Industry Research Report - market status analysis and development prospect forecast
- Research Report on micro gripper industry - market status analysis and development prospect prediction
- Construction and maintenance of business websites [9]
- D4:非成对图像去雾,基于密度与深度分解的自增强方法(CVPR 2022)
- 【剑指 Offer】57. 和为s的两个数字
- Cardinality sorting (detailed illustration)
- Golang embeds variables in strings
猜你喜欢

7. Build native development environment

Redis分布式锁故障,我忍不住想爆粗...
![[shutter] shutter page Jump (route | navigator | page close)](/img/af/3fb2ca18bcec23a5c0c6897570fb53.gif)
[shutter] shutter page Jump (route | navigator | page close)
How does esrally perform simple custom performance tests?
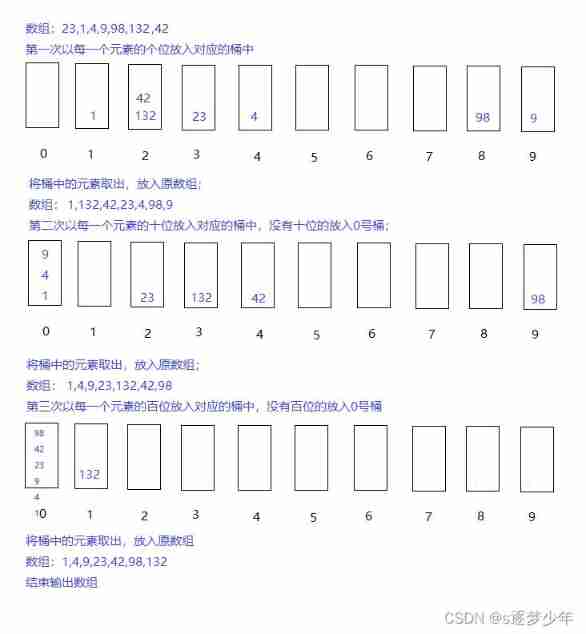
Cardinality sorting (detailed illustration)
![[shutter] statefulwidget component (floatingactionbutton component | refreshindicator component)](/img/17/b5889ec263687aeacf19214785ea8a.jpg)
[shutter] statefulwidget component (floatingactionbutton component | refreshindicator component)
![[shutter] shutter layout component (Introduction to layout component | row component | column component | sizedbox component | clipoval component)](/img/45/735431f59a84e9554225a72a551ab8.jpg)
[shutter] shutter layout component (Introduction to layout component | row component | column component | sizedbox component | clipoval component)

Gbase8s database type
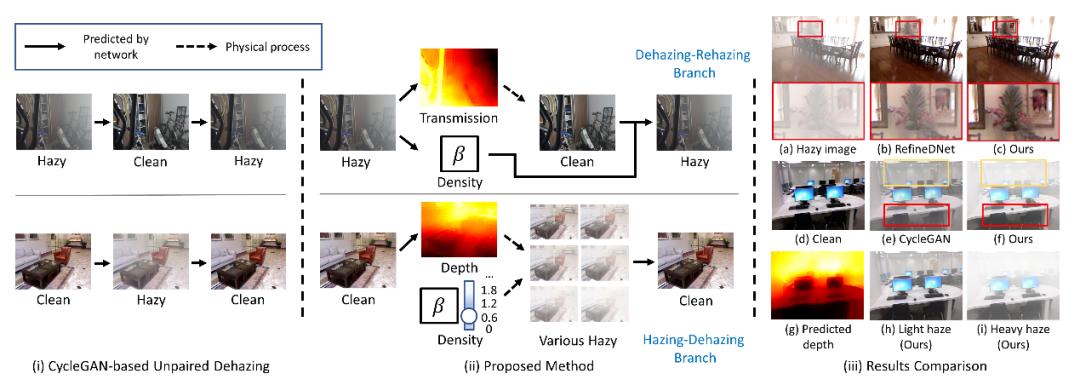
D4: unpaired image defogging, self enhancement method based on density and depth decomposition (CVPR 2022)
![[shutter] shutter layout component (fractionallysizedbox component | stack layout component | positioned component)](/img/5f/e96baefd9481c496024fed345e31fe.jpg)
[shutter] shutter layout component (fractionallysizedbox component | stack layout component | positioned component)
随机推荐
Huawei Hongmeng watch achieves fireworks display effect on New Year's Eve
Etcd Raft 协议
Plastic floating dock Industry Research Report - market status analysis and development prospect forecast
MySQL learning record (7)
发现你看不到的物体!南开&武大&ETH提出用于伪装目标检测SINet,代码已开源!...
[shutter] shutter layout component (physicalmodel component)
Pyqt picture decodes and encodes and loads pictures
Analysis of enterprise financial statements [4]
6 pyspark Library
[CV] Wu Enda machine learning course notes | Chapter 12
Research Report on micro gripper industry - market status analysis and development prospect prediction
Construction and maintenance of business websites [9]
MySQL learning record (5)
VictoriaMetrics 简介
Free open source web version of xshell [congratulations on a happy new year]
Import a large amount of data to redis in shell mode
Blue Bridge Cup Eliminate last one (bit operation, code completion)
AES encryption CBC mode pkcs7padding filling Base64 encoding key 32byte iv16byte
The neo4j skill tree was officially released to help you easily master the neo4j map database
Hot backup routing protocol (HSRP)