当前位置:网站首页>Is it safe to speculate in stocks on mobile phones?
Is it safe to speculate in stocks on mobile phones?
2022-07-08 00:44:00 【Koufu Q & A】
Take the answer 1:
The specific account opening process is as follows :
1. Get your bank card ready , Id card .
2. Contact the account manager on the line to download the account opening link , After entering, there are basically several steps : Cell phone number verification , The business department and account opening personnel choose , Fill in the basic information , Upload the front and back of ID card , Digital certificate download , Video verification , Risk assessment , Bind a third-party depository bank card , Submission for review .
3. After the audit , Mobile phone receiving fund account number . Basically . Opening an account during non trading hours should wait until the next trading day .
Friends who need to open an account can add wechat to communicate with me online , You can open accounts online all over the country , Help you deal with the low commission for free vip Account , Greatly save your transaction costs , Let your investment go smoothly .
边栏推荐
- Tapdata 的 2.0 版 ,开源的 Live Data Platform 现已发布
- Reentrantlock fair lock source code Chapter 0
- 股票开户免费办理佣金最低的券商,手机上开户安全吗
- Codeforces Round #804 (Div. 2)(A~D)
- 丸子官网小程序配置教程来了(附详细步骤)
- Course of causality, taught by Jonas Peters, University of Copenhagen
- 52歲的周鴻禕,還年輕嗎?
- Summary of the third course of weidongshan
- Binder核心API
- SDNU_ ACM_ ICPC_ 2022_ Summer_ Practice(1~2)
猜你喜欢
随机推荐
【obs】Impossible to find entrance point CreateDirect3D11DeviceFromDXGIDevice
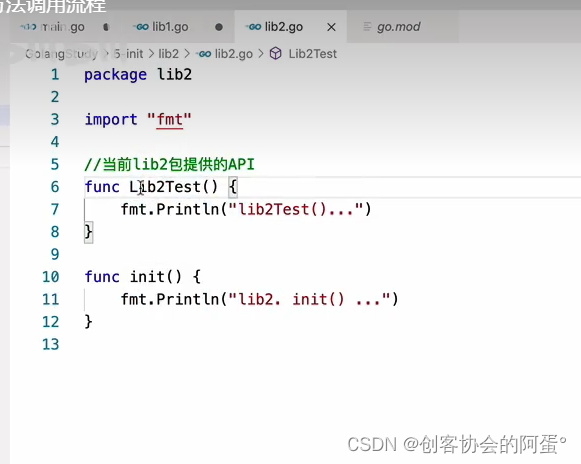
【愚公系列】2022年7月 Go教学课程 006-自动推导类型和输入输出
Codeforces Round #804 (Div. 2)(A~D)
接口测试进阶接口脚本使用—apipost(预/后执行脚本)
Langchao Yunxi distributed database tracing (II) -- source code analysis
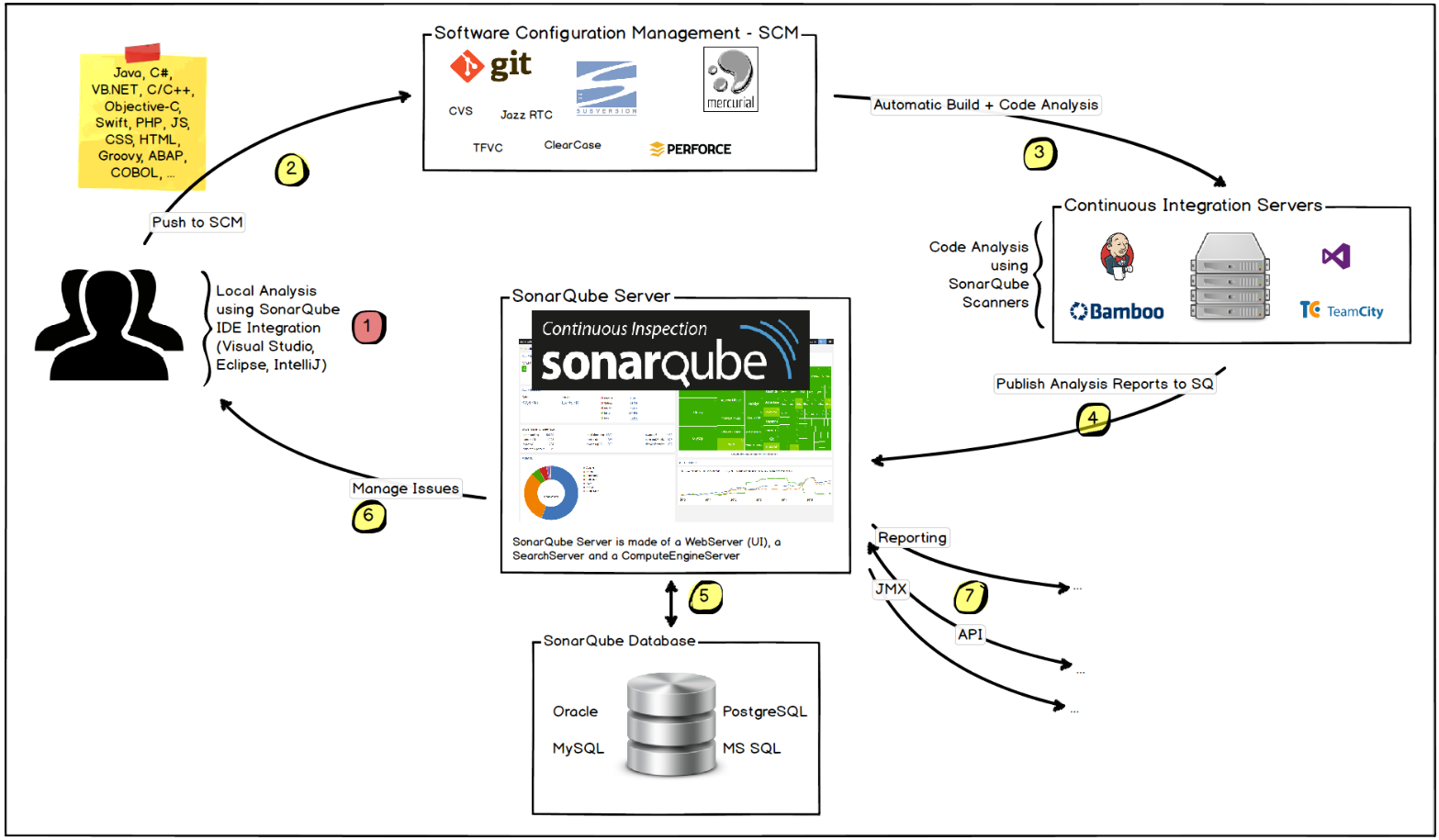
Jouer sonar
Cascade-LSTM: A Tree-Structured Neural Classifier for Detecting Misinformation Cascades(KDD20)
[Yugong series] go teaching course 006 in July 2022 - automatic derivation of types and input and output
【obs】Impossible to find entrance point CreateDirect3D11DeviceFromDXGIDevice
Experience of autumn recruitment in 22 years
Class head up rate detection based on face recognition
取消select的默认样式的向下箭头和设置select默认字样
Operating system principle --- summary of interview knowledge points
爬虫实战(八):爬表情包
【测试面试题】页面很卡的原因分析及解决方案
Installation and configuration of sublime Text3
2022-07-07:原本数组中都是大于0、小于等于k的数字,是一个单调不减的数组, 其中可能有相等的数字,总体趋势是递增的。 但是其中有些位置的数被替换成了0,我们需要求出所有的把0替换的方案数量:
Vscode software
他们齐聚 2022 ECUG Con,只为「中国技术力量」
Sqlite数据库存储目录结构邻接表的实现2-目录树的构建