当前位置:网站首页>What is information security? What is included? What is the difference with network security?
What is information security? What is included? What is the difference with network security?
2022-07-05 23:59:00 【Xingyun housekeeper】
In life, we often hear that we need to protect our own or enterprise information security . What exactly is information security ? What content does information security contain ? What's the difference with network security ? Today, let's take a closer look at .
What is information security ?
Information security is defined as follows : Technology established and adopted for data processing system 、 Management security , To protect computer hardware 、 Software 、 Data is not destroyed by accidental and malicious reasons 、 Changes and leaks .
What content does information security contain ?
1、 Hardware security : That is, the security of network hardware and storage media . We should protect these hard facilities from damage , Be able to work normally .
2、 software security : That is, computers and their networks r All kinds of software will not be tampered with or destroyed , Not be operated illegally or by mistake , The function will not fail , Not illegally copied .
3、 Running service security : That is, each information system in the network can operate normally and exchange information through the network . Through the monitoring of the operating conditions of various equipment in the network system , If unsafe factors are found, it can alarm in time and take measures to change the unsafe state , Ensure the normal operation of the network system .
4、 Data security : That is, the security of existing and circulating data in the network . To protect the data in the network from tampering 、 Illegal addition and deletion 、 Copy 、 Decrypt 、 Show 、 Use, etc . It is the most fundamental purpose to ensure network security .
What is the difference between information security and network security ?
Information security is mainly about the security of computer systems and the protection of various protocols , As long as there are some relevant signs in the system that can threaten information security , Information security will provide overall security protection . and Network security It is aimed at the security of computers in the network environment , The devices for information security and network security are different , The emphasis of the two is also different , They all have their own advantages .
Knowledge development : Several measures for enterprises to improve information security
1、 Strengthen the management of office environment and physical security , Install anti-virus software uniformly ;
2、 Beware of phishing emails , Important matters should be verified and confirmed ;
3、 Set complex passwords , And replace it regularly ;
4、 Protect your privacy , Guard against telecommunications fraud ;
5、 Do a good job of data backup , Implement data security measures ;
6、 Pay attention to the safety protection measures of mobile terminals such as mobile phones ;
7、 Protect your personal information assets during business trips ;
8、 Comply with laws, regulations and safety policies .
边栏推荐
- 亲测可用fiddler手机抓包配置代理后没有网络
- What are the functions of Yunna fixed assets management system?
- FFMPEG关键结构体——AVFormatContext
- GFS分布式文件系統
- [online chat] the original wechat applet can also reply to Facebook homepage messages!
- 提升工作效率工具:SQL批量生成工具思想
- What are Yunna's fixed asset management systems?
- 妙才周刊 - 8
- 单商户V4.4,初心未变,实力依旧!
- 关于结构体所占内存大小知识
猜你喜欢
How to rotate the synchronized / refreshed icon (EL icon refresh)
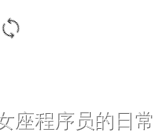
Bao Yan notes II software engineering and calculation volume II (Chapter 13-16)
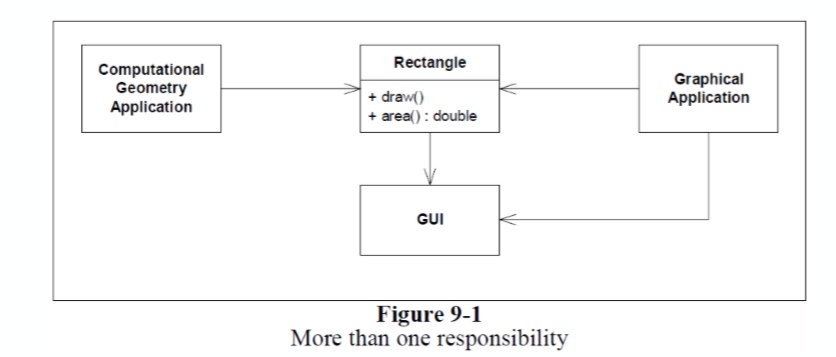
The difference of time zone and the time library of go language
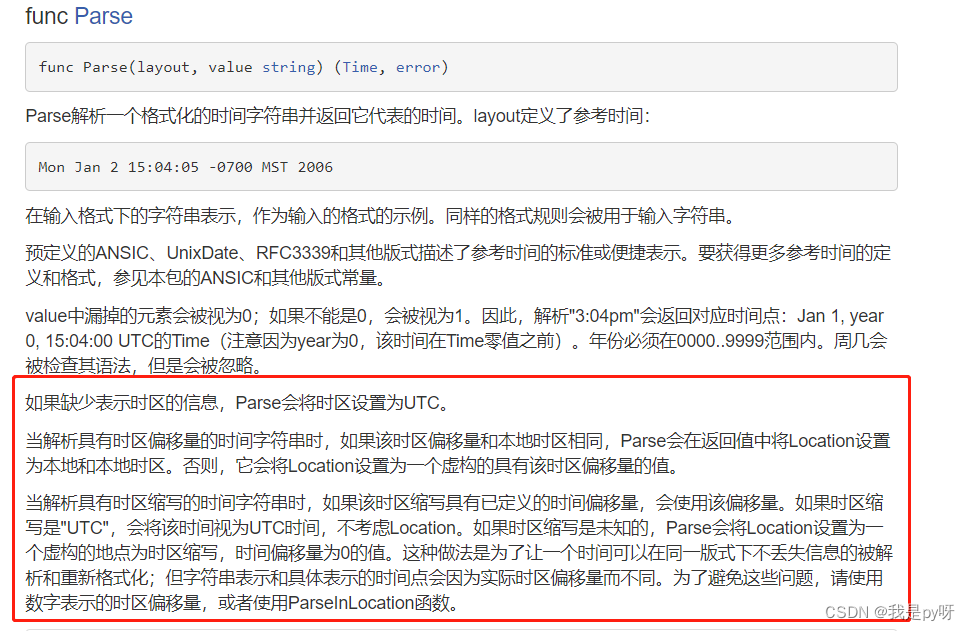
Spire Office 7.5.4 for NET

云呐|公司固定资产管理系统有哪些?
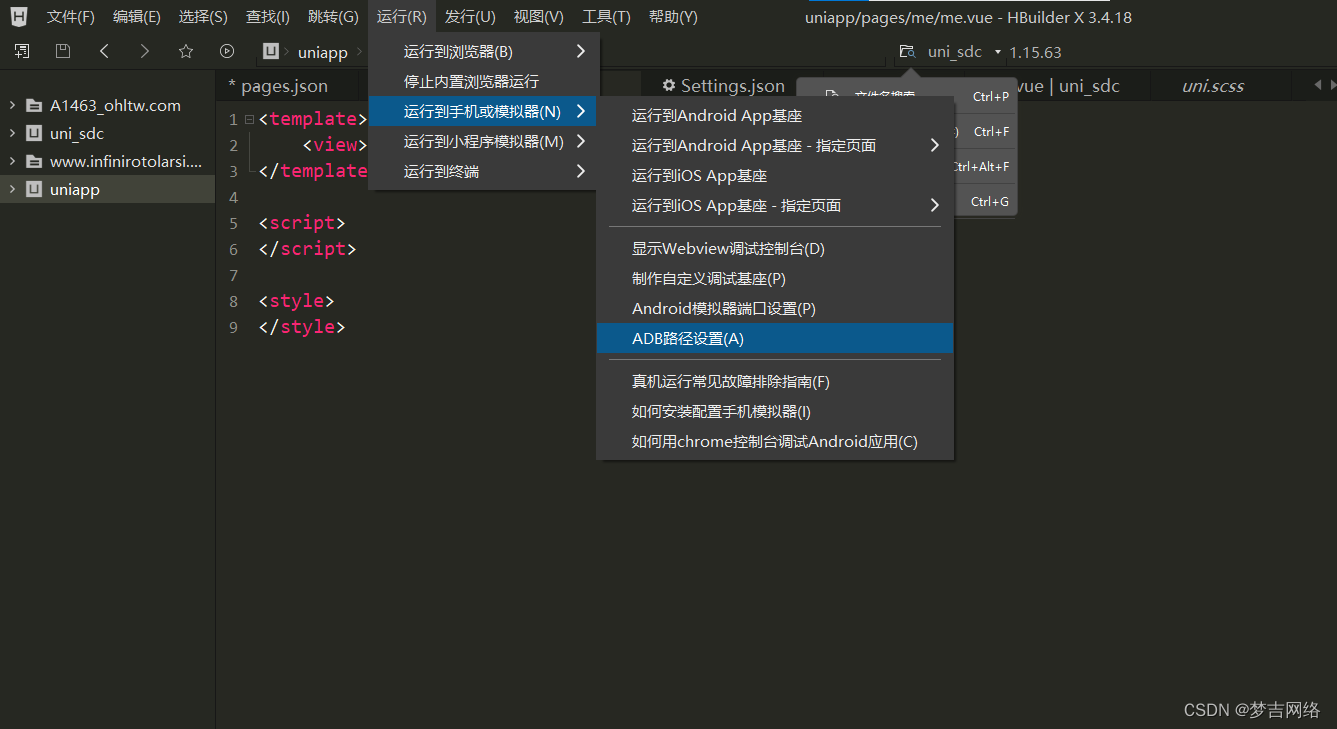
教你在HbuilderX上使用模拟器运行uni-app,良心教学!!!
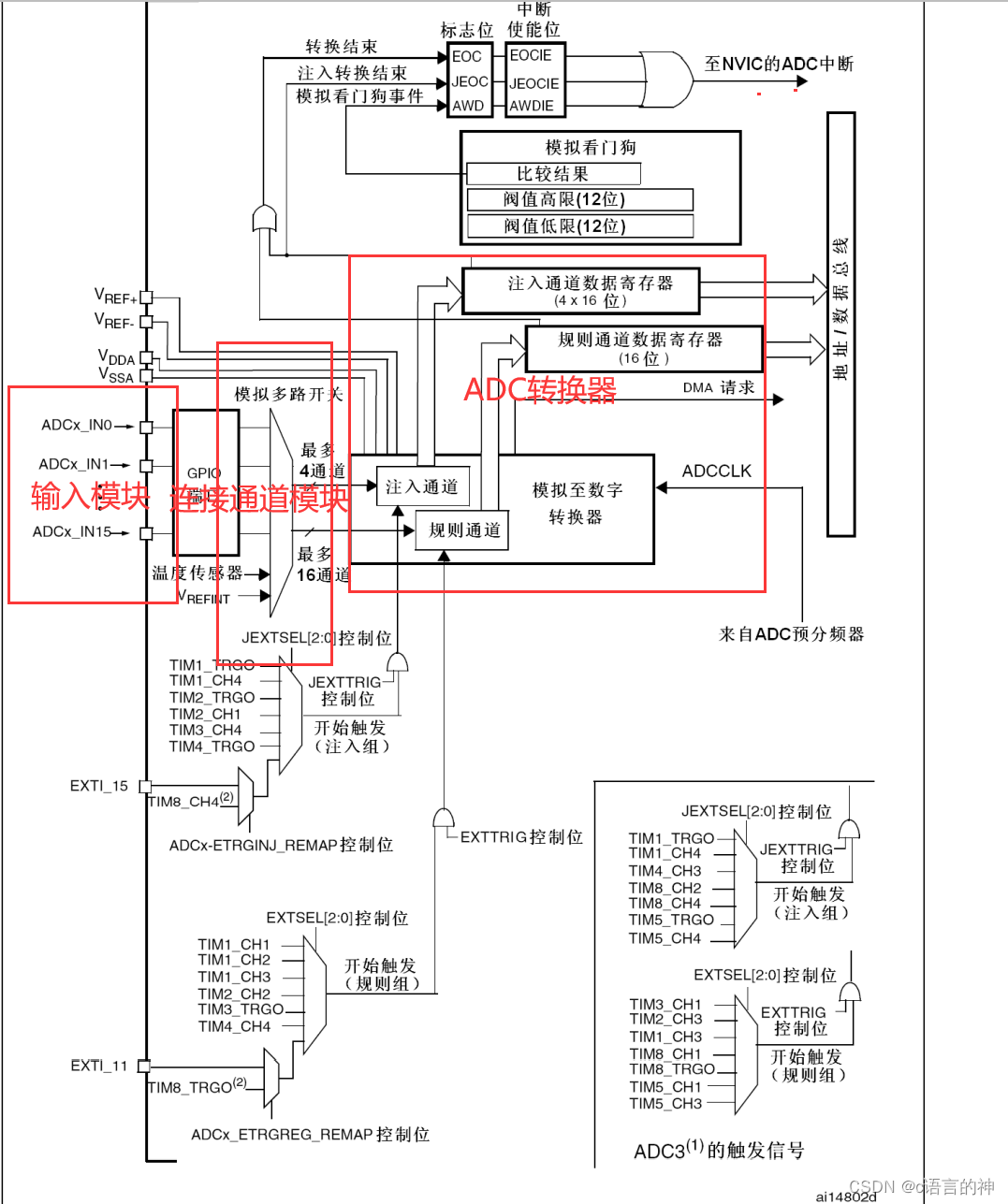
STM32__ 06 - single channel ADC
What are the functions of Yunna fixed assets management system?
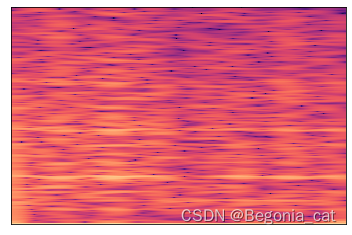
认识提取与显示梅尔谱图的小实验(观察不同y_axis和x_axis的区别)
Tools to improve work efficiency: the idea of SQL batch generation tools
随机推荐
21. PWM application programming
GFS Distributed File System
Online yaml to CSV tool
Configuring OSPF load sharing for Huawei devices
妙才周刊 - 8
Open3D 点云随机添加噪声
【GYM 102832H】【模板】Combination Lock(二分图博弈)
GD32F4xx uIP协议栈移植记录
DEJA_ Vu3d - cesium feature set 055 - summary description of map service addresses of domestic and foreign manufacturers
Bao Yan notebook IV software engineering and calculation volume II (Chapter 8-12)
5. Logistic regression
DEJA_VU3D - Cesium功能集 之 055-国内外各厂商地图服务地址汇总说明
el-cascader的使用以及报错解决
C# 反射与Type
亲测可用fiddler手机抓包配置代理后没有网络
FFmpeg学习——核心模块
Problem solving win10 quickly open ipynb file
PADS ROUTER 使用技巧小记
How to rotate the synchronized / refreshed icon (EL icon refresh)
Cloudcompare & PCL point cloud randomly adds noise