当前位置:网站首页>I plan to take part in security work. How about information security engineers and how to prepare for the soft exam?
I plan to take part in security work. How about information security engineers and how to prepare for the soft exam?
2022-07-07 10:36:00 【qq123yyy】
Information security engineer is an intermediate subject in the soft exam , Only two subjects are needed . Information security engineer is a new exam in recent years , Belong to “ The information system ” major .
The intermediate information security engineer of the soft exam takes two subjects :
Morning subject 1 : Basic knowledge of information security ,150 minute , written examination 75 Multiple choice questions
Afternoon subject 2 : Information security application technology ,150 minute , written examination 5/6 Questions and answers
Post requirements :
- Proficient in network security technology : Including ports 、 Service Vulnerability Scanning 、 Program vulnerability analysis and detection 、 Rights management 、 Intrusion and attack analysis tracking 、 Website penetration 、 Virus and Trojan horse prevention, etc .
- be familiar with tcp/ip agreement , be familiar with sql Injection principle and manual detection 、 Familiar with the principle of memory buffer overflow and preventive measures 、 Familiar with information storage and transmission security 、 Familiar with packet structure 、 be familiar with ddos There are some differences in attack types and principles ddos Attack and defense experience , be familiar with iis Security Settings 、 be familiar with ipsec、 Group policy and other system security settings .
- be familiar with windows or linux System , Master php/shell/perl/python/c/c++ Wait for at least one language ; Be responsible for discovering and verifying the security vulnerabilities of the company's information system , Provide technical support , Promote vulnerability repair .
How to prepare for exams efficiently :
Information security engineer examination requirements , Is more technical , So the difficulty is certain . The basic knowledge must be thoroughly mastered 、 Full understanding . Applied technology is to examine the ability to apply knowledge and the ability to analyze topics at the first level , So preparing for the exam requires more time to study .
Refer to the official tutorial 《 Information Security Engineer tutorial 》, The true theme of the past years ( Including resolution ), Video Course
- The first stage is mainly to understand the examination situation , On the examination form 、 You need to have a clear understanding of the exam requirements , And have a clear understanding of the distribution of examination sites over the years , Be able to sort out the core test site content .
- The second stage , It is also the core of the learning stage of information security engineers . Learn the course of information security engineer to lay a solid foundation , Understand and master the important contents of the information security engineer exam , We should not only know what it is, but also know why .
Have a holistic concept , You can't cut them apart . Laws and regulations 、 security management 、 Safety technology 、 Case studies are actually It's a whole , An information security engineer should know and know 、 Theory and knowledge that should be mastered .
- The third stage , Connect the knowledge of information security engineers , Have a more systematic understanding . Through a period of knowledge exercises to strengthen training , Form a more reasonable way to solve problems .
- The fourth stage , Brush the question sprint stage ( Consolidate knowledge -- Brush problem -- Leak filling — summary ) Knowledge points for information security engineers 、 The whole framework system is clear in my heart .
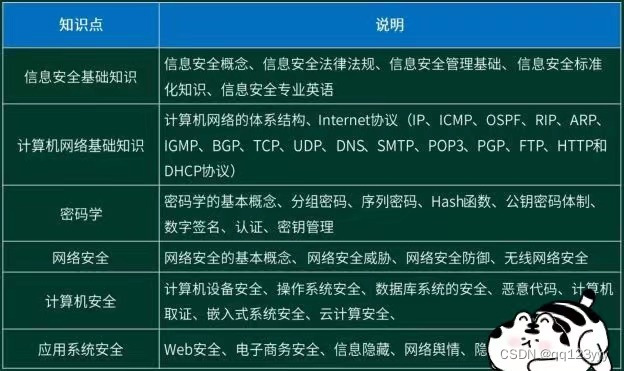
Basic knowledge of information security ( Morning questions )
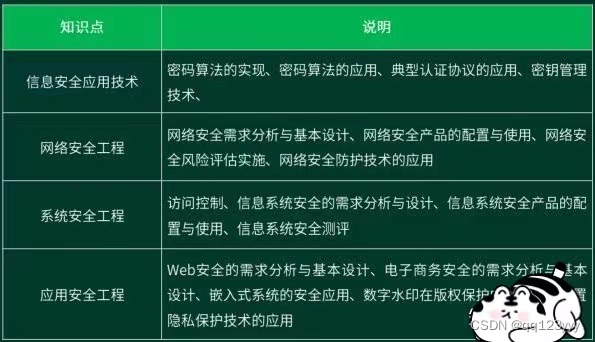
Information security application technology ( Afternoon question )
Exam notes :
- 1. Admission ticket Print :A4 Paper printing , Black and white ; Try to print on one page , It is recommended to use UC Browser printing , Remove header and footer ; Or print at a nearby printing shop .
- 2. Essential tools : Admission ticket 、 Original ID card 、 For examination 2B The pencil 、 Eraser 、 Black neutral pen ;
- ( Prepare a transparent file bag , Put the certificate into the bag in advance , Avoid the entrance invigilator taking out his certificate in a hurry and losing it .) 3. Bar code The invigilator will distribute it uniformly before the exam .
- 4. Check the bus route in advance , Please advance 30 Arrive at the examination room in about minutes , Don't be late for the exam . If the distance is too far, it is recommended to book a hotel in advance , So as not to delay the exam .
- 5. Please read carefully the instructions for candidates on the admission ticket , The items required for the exam are all explained .
- 6. If you encounter any problems in the exam, please raise your hand in time to signal the invigilator .
- 7. Keep a good attitude when approaching the exam , Win in stability ~
- 8. Remember to set the alarm clock the day before the exam , Get enough sleep , relax ~
- 9. Please turn your mobile phone off after the exam / Mute state .
- 10. Try to drink less before the exam , You can prepare some chocolate 、 Mineral water , Long exam time , Replenish energy at critical moments .
边栏推荐
猜你喜欢
CAS mechanism
![[second on] [jeecgboot] modify paging parameters](/img/59/55313e3e0cf6a1f7f6b03665e77789.png)
[second on] [jeecgboot] modify paging parameters
![[daiy5] jz77 print binary tree in zigzag order](/img/ba/b2dfbf121798757c7b9fba4811221b.png)
[daiy5] jz77 print binary tree in zigzag order
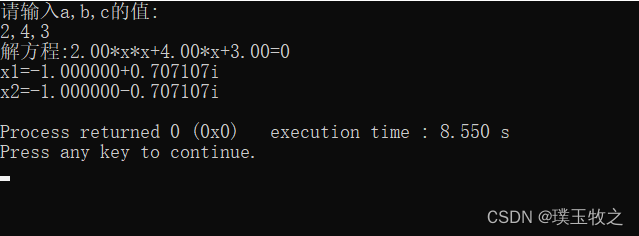
求方程ax^2+bx+c=0的根(C语言)

Openinstall and Hupu have reached a cooperation to mine the data value of sports culture industry
1323:【例6.5】活动选择
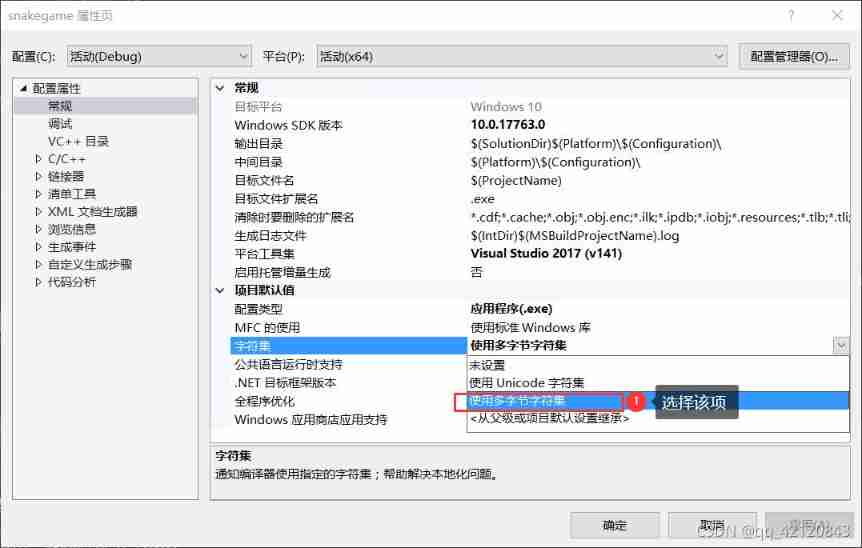
The variables or functions declared in the header file cannot be recognized after importing other people's projects and adding the header file

软考一般什么时候出成绩呢?在线蹬?
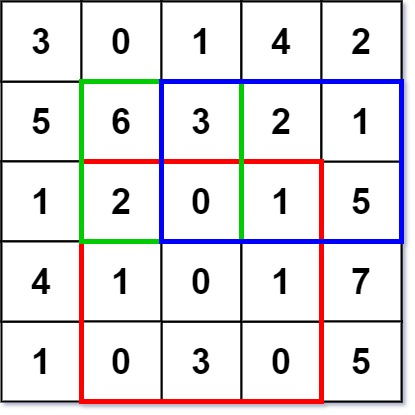
leetcode-304:二维区域和检索 - 矩阵不可变
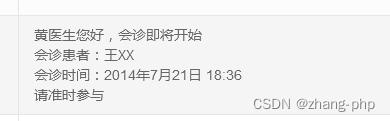
php \n 换行无法输出
随机推荐
Mendeley--免费的文献管理工具,给论文自动插入参考文献
基于HPC场景的集群任务调度系统LSF/SGE/Slurm/PBS
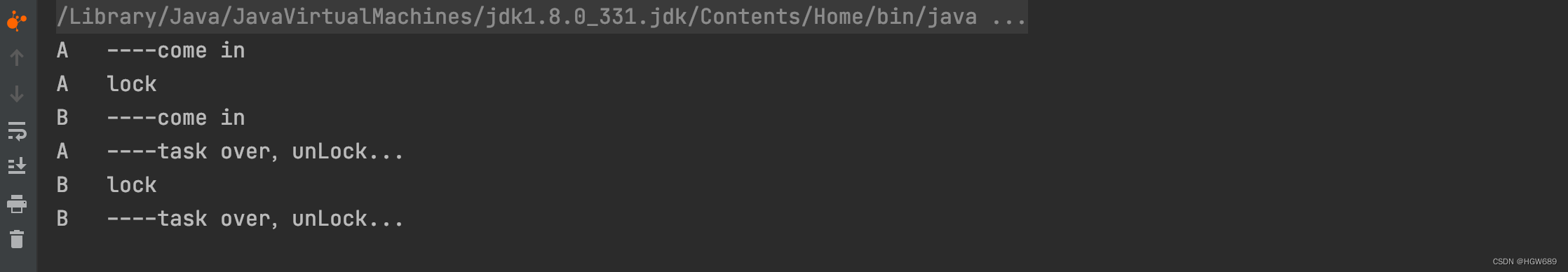
Multithreaded asynchronous orchestration
Applet jump to H5, configure business domain name experience tutorial
Slurm资源管理与作业调度系统安装配置
Trajectory planning for multi-robot systems: Methods and applications 综述阅读笔记
Use the fetch statement to obtain the repetition of the last row of cursor data
TypeScript 接口继承
OpenGL glLightfv 函数的应用以及光源的相关知识
Multisim -- software related skills
软考一般什么时候出成绩呢?在线蹬?
5个chrome简单实用的日常开发功能详解,赶快解锁让你提升更多效率!
555 circuit details
多线程-异步编排
Using U2 net deep network to realize -- certificate photo generation program
Pre knowledge reserve of TS type gymnastics to become an excellent TS gymnastics master
How embedded engineers improve work efficiency
php \n 换行无法输出
0x0fa23729 (vcruntime140d.dll) (in classes and objects - encapsulation.Exe) exception thrown (resolved)
Trajectory planning for multi robot systems: methods and Applications Overview reading notes