当前位置:网站首页>Attack and defense world crypto WP
Attack and defense world crypto WP
2022-07-05 13:43:00 【Sex sex ~ ~】
One 、 Catalog
1.base64
2.caesar
3.Morse
4. Idempotent encryption
5.Railfence
6. Mixed encoding
Two 、 Their thinking
1.base64
Open the file attachment

The prompt given in the title is base64 encryption , Decrypt online

obtain flag: cyberpeace{Welcome_to_new_World!}
2.caesar
Open the file attachment

The title says yes caesar encryption , Decrypt online ,key The value of the 0~25 One by one, try to be on duty 14 When you get rid of flag

3.Morse
Open the file attachment

The title has told us that it is moss encryption , Then observe that the attachments are made of 1 and 0 form , Just like the one in moss code - and . Take care of each other
Edit the file as -- --- .-. ... . -.-. In the form of

Then decrypt

flag:cyberpeace{morsecodeissointeresting}
4. Idempotent encryption
Open the file attachment

The encryption method mentioned in the title is idempotent encryption , But we observe the attachment , Normal idempotent encryption only starts from 0~5, There will be no 8,
I learned through Baidu that this is the cloud shadow password , Let's first learn about cloud shadow encryption .
Cloud shadow encryption : Cloud shadow encryption , also called 01248 password … Unlike binary power encryption , This encryption method uses 0 Make interval , Other than 0 Numbers are separated and combined to represent serial numbers 1~26 One of the letters (a/A,b/B,c/C…z/Z).

View Title Requirements flag For the eight capital letters solved , According to the nature of cloud shadow encryption , With 0 Separate this string of arrays as an interval, which is exactly eight groups , Add the numbers in each array , Then the total number corresponds to A~Z Letters in .

flag:cyberpeace{WELLDONE}
5.Railfence

According to the title, it is fence encryption , There are two kinds of fence encryption , There is another way W Type fence encryption , Decrypt the attachment first , The title says 5 A chicken , therefore key May be 5


And the result seems to be incorrect flag, Then the characters are W Type fence decryption

flag:cyberpeace{railfence_cipher_gogogo}
6. Mixed encoding
Open the file attachment

There are two equal signs at the end of the file , It can be seen that base64 encryption , To decrypt

Baidu knows that the character revealed is an encryption method , by Unicode code , Turn it into ascll code

Observation characters have English case and numbers , May be base64 encryption , To decrypt

Observe the decrypted characters , Between numbers / Separated and these numbers do not exceed 126, It may correspond to ascll clock , Put these numbers one A contrast ascll clock

flag:cyberpeace{welcometoattackanddefenceworld}
边栏推荐
- Mmseg - Mutli view time series data inspection and visualization
- [深度学习论文笔记]UCTransNet:从transformer的通道角度重新思考U-Net中的跳跃连接
- 【MySQL 使用秘籍】一网打尽 MySQL 时间和日期类型与相关操作函数(三)
- 53. Maximum subarray sum: give you an integer array num, please find a continuous subarray with the maximum sum (the subarray contains at least one element) and return its maximum sum.
- 【华南理工大学】考研初试复试资料分享
- Basic characteristics and isolation level of transactions
- Record in-depth learning - some bug handling
- [深度学习论文笔记]使用多模态MR成像分割脑肿瘤的HNF-Netv2
- 基于微信小程序的订餐系统
- Pancake Bulldog robot V2 (code optimized)
猜你喜欢
![Primary code audit [no dolls (modification)] assessment](/img/b8/82c32e95d1b72f75823ca91c97138e.jpg)
Primary code audit [no dolls (modification)] assessment
![[深度学习论文笔记]使用多模态MR成像分割脑肿瘤的HNF-Netv2](/img/52/5e85743b1817de96a52e02b92fd08c.png)
[深度学习论文笔记]使用多模态MR成像分割脑肿瘤的HNF-Netv2

内网穿透工具 netapp
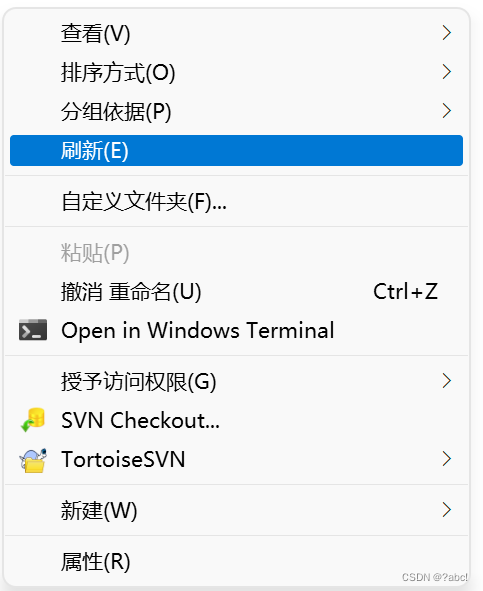
TortoiseSVN使用情形、安装与使用
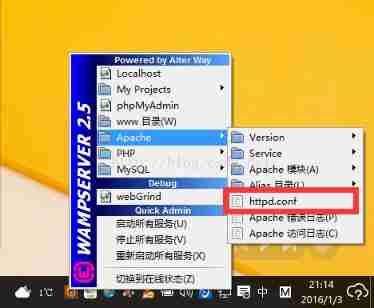
How to deal with the Yellow Icon during the installation of wampserver
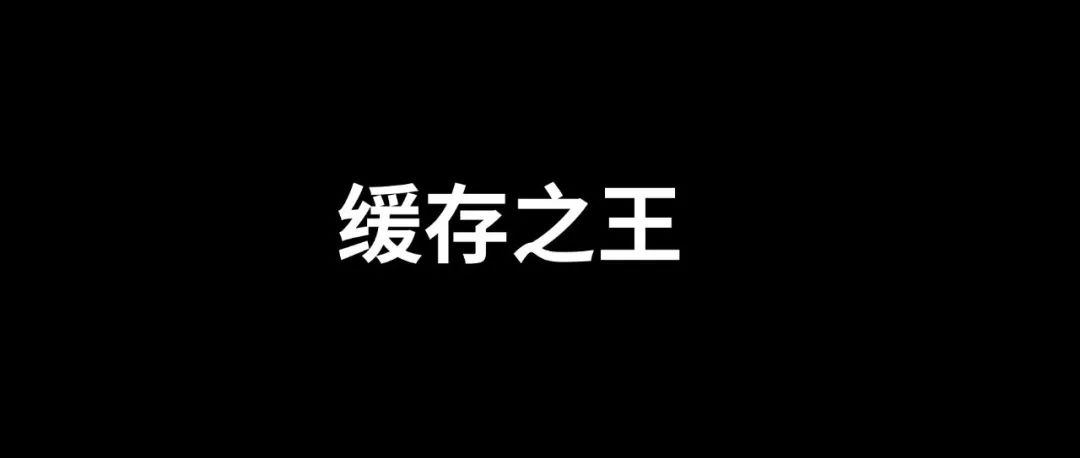
The real king of caching, Google guava is just a brother
![[deep learning paper notes] hnf-netv2 for segmentation of brain tumors using multimodal MR imaging](/img/52/5e85743b1817de96a52e02b92fd08c.png)
[deep learning paper notes] hnf-netv2 for segmentation of brain tumors using multimodal MR imaging
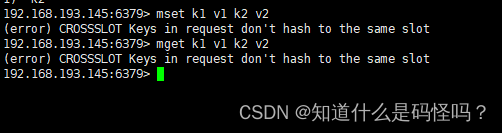
Redis6 master-slave replication and clustering
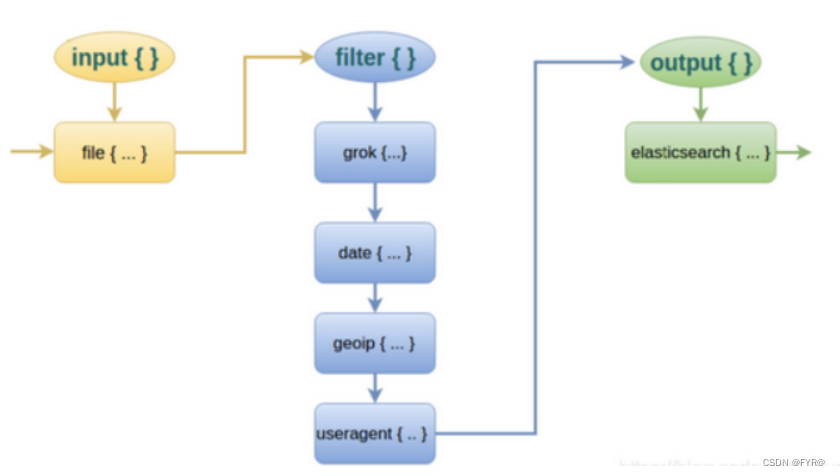
ELFK部署
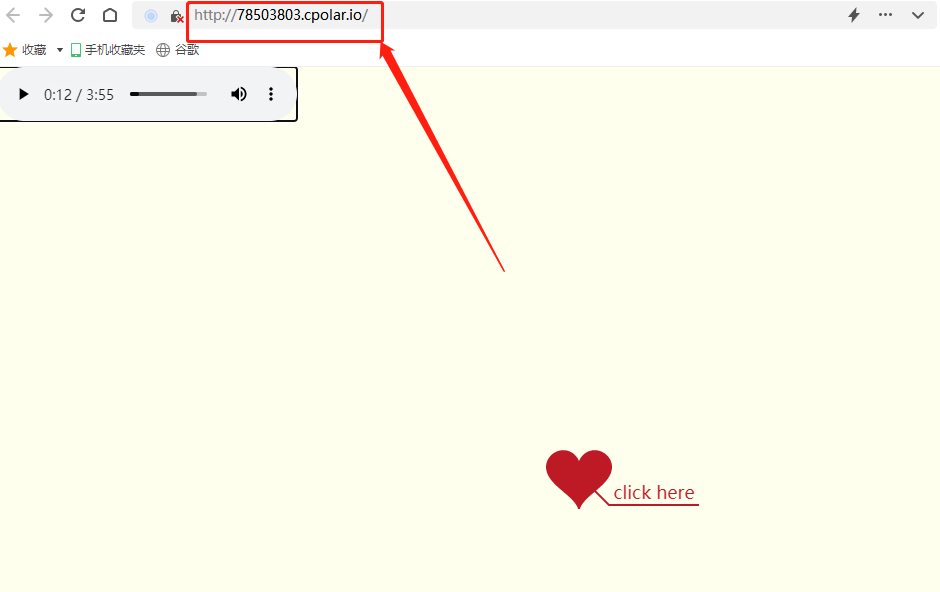
搭建一个仪式感点满的网站,并内网穿透发布到公网 2/2
随机推荐
面试官灵魂拷问:为什么代码规范要求 SQL 语句不要过多的 join?
Network security HSRP protocol
FPGA 学习笔记:Vivado 2019.1 添加 IP MicroBlaze
jenkins安装
Log4j utilization correlation
Get you started with Apache pseudo static configuration
[server data recovery] a case of RAID5 data recovery stored in a brand of server
那些考研后才知道的事
Win10——轻量级小工具
Aspx simple user login
Address book (linked list implementation)
STM32 reverse entry
Require, require in PHP_ once、include、include_ Detailed explanation of the efficiency of repeated introduction of once class library
Integer ==比较会自动拆箱 该变量不能赋值为空
Jetpack Compose入门到精通
How to apply the updated fluent 3.0 to applet development
【MySQL 使用秘籍】一网打尽 MySQL 时间和日期类型与相关操作函数(三)
【 script secret pour l'utilisation de MySQL 】 un jeu en ligne sur l'heure et le type de date de MySQL et les fonctions d'exploitation connexes (3)
【云资源】云资源安全管理用什么软件好?为什么?
私有地址有那些