当前位置:网站首页>Xin'an Second Edition: Chapter 26 big data security demand analysis and security protection engineering learning notes
Xin'an Second Edition: Chapter 26 big data security demand analysis and security protection engineering learning notes
2022-07-06 17:34:00 【Moon Dream Studio】
One 、 The outline of this chapter requires
9. Big data security demand analysis and security protection engineering
9.1 Big data security threat and demand analysis
9.1.1 Big data security threat analysis
◆ Concept and characteristics of big data ◆ Big data security
9.1.2 Big data security requirements analysis
◆ Basic requirements for data security ( The authenticity of the data 、 The real time 、 Confidentiality 、 integrity 、 Usability 、 traceability )
◆ Big data security compliance
◆ Big data cross-border security
◆ Big data privacy protection
◆ Big data processing platform security
◆ Big data business security
◆ Secure operation of big data
9.2 Big data security protection mechanism and technical scheme
9.2.1 Big data self security protection technology
◆ Data source authentication ◆ Data traceability ◆ Data user identification and identification ◆ Data resource access control
9.2.2 Big data platform security protection technology
◆ Big data platform border security
◆ Big data network communication security
◆ Identity authentication and authority management of big data users
◆ Big data computing security
◆ Big data platform emergency disaster recovery
◆ Big data audit and monitoring
9.2.3 Big data service security protection technology
◆ Business authorization ◆ Business logic security ◆ Sensitive data security check
9.2.4 Big data privacy security protection technology
◆ Data identity anonymity ◆ Data differential privacy ◆ Data desensitization ◆ Data encryption ◆ Data access control
9.2.5 Big data operation security protection technology
◆ Security maintenance of big data processing system
◆ Big data processing system security policy update
◆ Big data processing system security equipment configuration
◆ Big data processing system security event monitoring and emergency response
◆ Big data processing system intrusion detection and network security situational awareness
◆ Big data processing system network attack forensics
◆ Big data processing system security audit 、 Safety fortress machine
◆ Disaster recovery backup of big data processing system
9.2.6 Big data security management and Standards
◆ Big data security level protection and understanding of relevant standards and specifications
<边栏推荐
- [ciscn 2021 South China]rsa writeup
- 信息与网络安全期末复习(基于老师给的重点)
- The NTFS format converter (convert.exe) is missing from the current system
- Total / statistics function of MySQL
- [VNCTF 2022]ezmath wp
- MySQL basic addition, deletion, modification and query of SQL statements
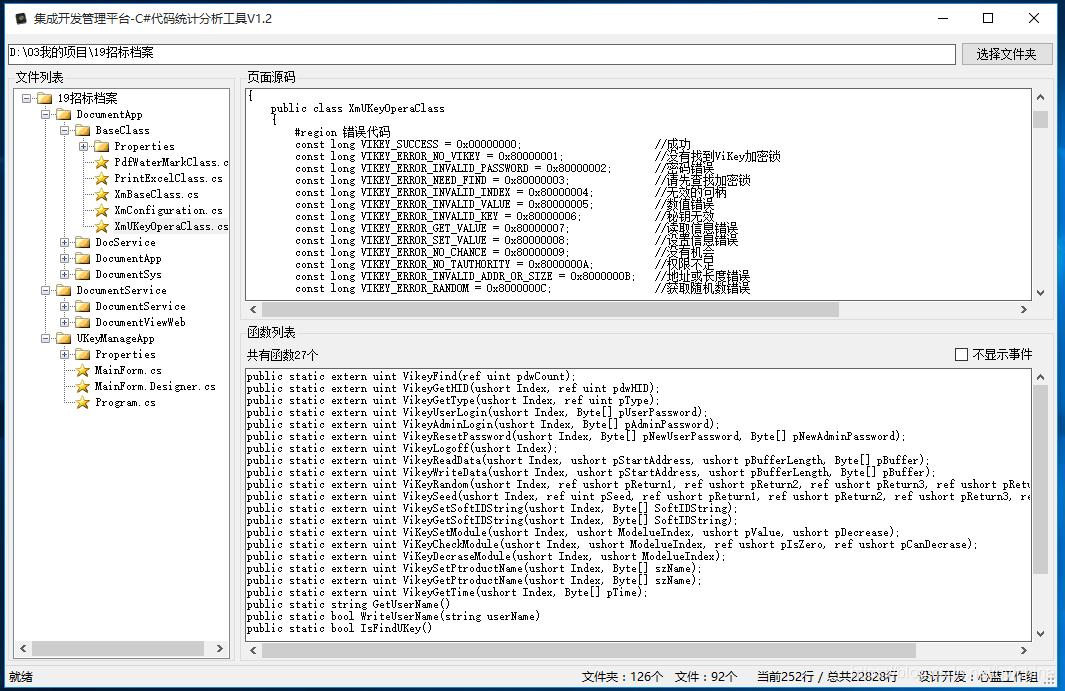
- 03个人研发的产品及推广-计划服务配置器V3.0
- 【逆向初级】独树一帜
- 华为认证云计算HICA
- Models used in data warehouse modeling and layered introduction
猜你喜欢
随机推荐
Redis quick start
02 personal developed products and promotion - SMS platform
List set data removal (list.sublist.clear)
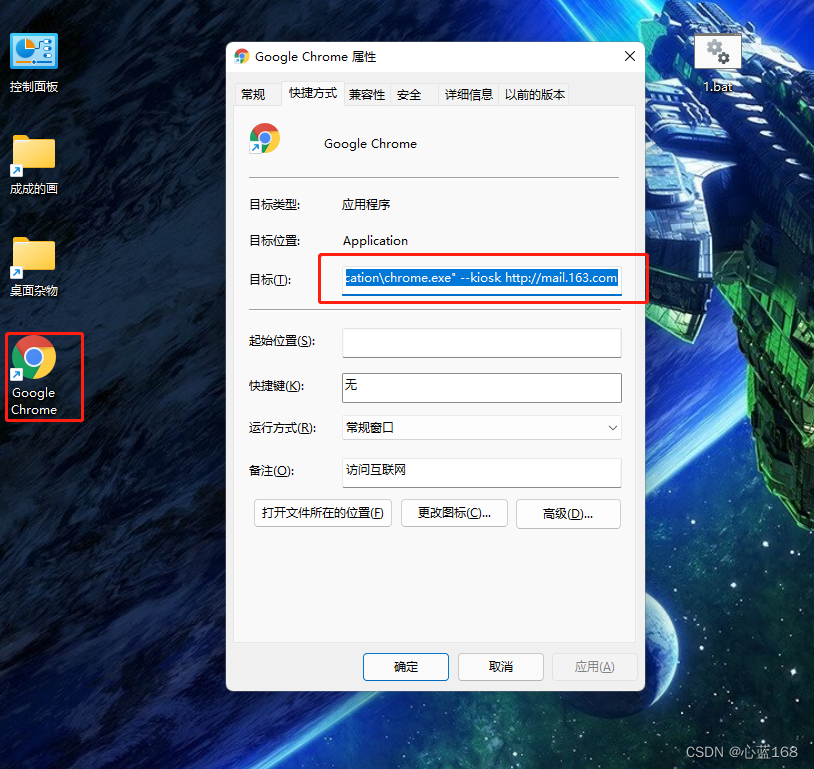
Uipath browser performs actions in the new tab
Flink源码解读(一):StreamGraph源码解读
[reverse] repair IAT and close ASLR after shelling
Akamai anti confusion
Jetpack compose 1.1 release, based on kotlin's Android UI Toolkit
Wu Jun's trilogy experience (VII) the essence of Commerce
Interpretation of Flink source code (II): Interpretation of jobgraph source code
Serial serialold parnew of JVM garbage collector
Final review of information and network security (based on the key points given by the teacher)
【Elastic】Elastic缺少xpack无法创建模板 unknown setting index.lifecycle.name index.lifecycle.rollover_alias
EasyRE WriteUp
信息与网络安全期末复习(完整版)
沉淀下来的数据库操作类-C#版(SQL Server)
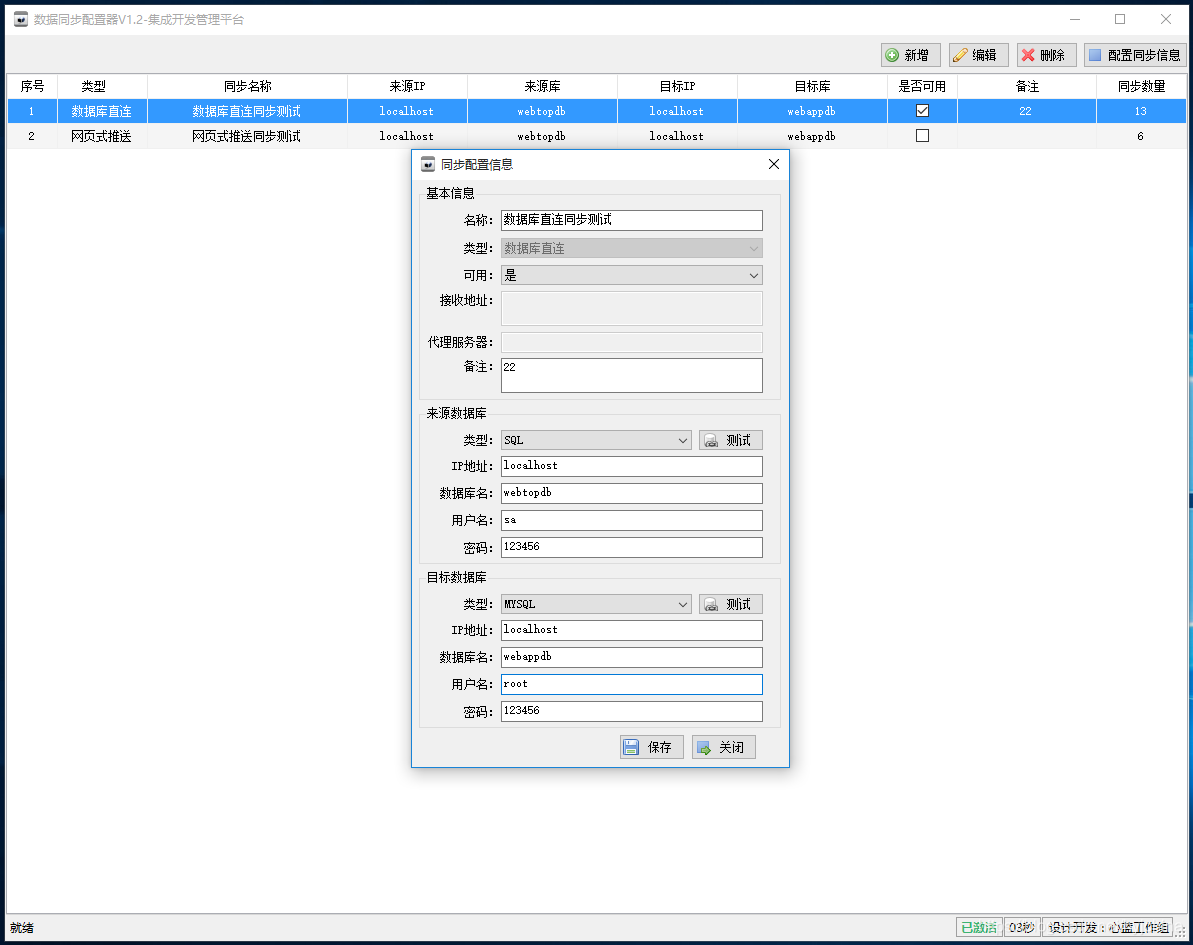
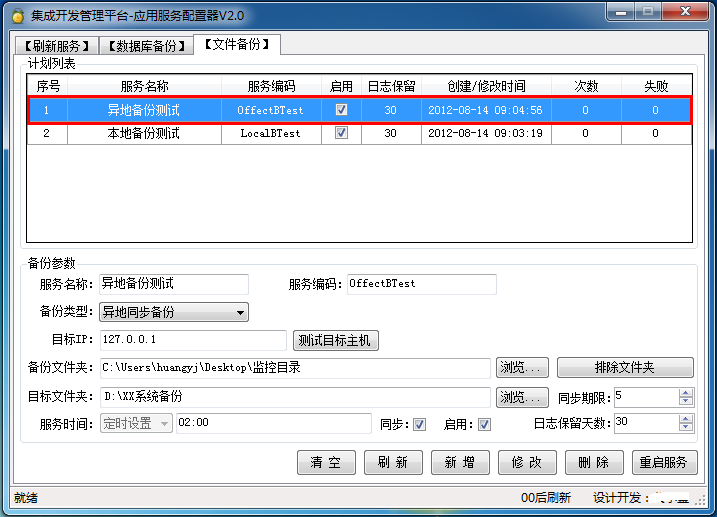
Application service configurator (regular, database backup, file backup, remote backup)
吴军三部曲见识(四) 大家智慧
yarn : 无法加载文件 D:\ProgramFiles\nodejs\yarn.ps1,因为在此系统上禁止运行脚本
Flink 解析(三):内存管理
![[reverse intermediate] eager to try](/img/5a/568533850ddfd1c41117da0df50e20.png)