当前位置:网站首页>Deep learning notes (constantly updating...)
Deep learning notes (constantly updating...)
2022-07-03 01:57:00 【North Village South】
Data preprocessing One-Hot - You know (zhihu.com)
A person without touching each other , In a special way , Have a series of questions and answers with each other . If for a long time , He can't judge whether the other party is a person or a computer based on these questions , Then it can be considered that the computer is intelligent .
—— Alan · Turing (Alan Turing)
《Computing Machinery and Intelligence 》
Knowledge system
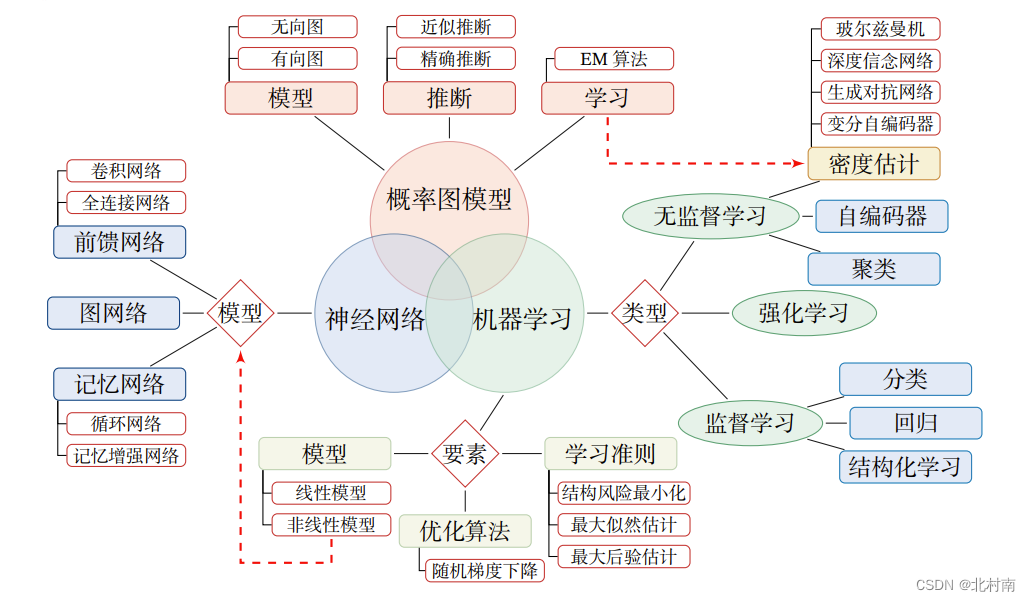
Why does deep learning mainly use neural networks ?
The main reason is that the neural network model can use error back propagation BP Algorithm , So we can better solve the problem of contribution distribution
What neural networks need to learn : The weight parameter of the connection between each neuron
Why use activation functions : If you don't use the activation function , Then the output of each layer is the linear function of the input of the previous layer , Then eventually, the whole network is linear , That is, the most primitive perceptron (Perceptron), Its presentation ability is poor
Neuron
Neural networks are composed of Neuron Composed of , The structure of each neuron is as follows

Activation function
among f Is the activation function , common Activation function as follows
Sigmoid function

ReLu function

Swish function

Network structure
There are three common network structures , Feedforward networks FNN Similar to a directed acyclic graph , Information can only spread in one direction , It's simpler . Memory network MN Similar to a directed cyclic graph , Information can be transmitted in one direction or two directions , More complicated . Figure network GN It is the generalization of feedforward network and memory network , Each square is one or a group of neurons

Reference material
《 Neural networks and deep learning 》-- Professor Qiu Xipeng
《 Hands-on deep learning 》Pytorch Open source -- Li Mu
《2022 Deep learning and machine learning 》-- Wu enda
边栏推荐
- 网络安全-木马
- 网络安全-破解系统密码
- 2022 spring "golden three silver four" job hopping prerequisites: Software Test interview questions (with answers)
- [data mining] task 5: k-means/dbscan clustering: double square
- DML Foundation
- Caused by: com.fasterxml.jackson.databind.exc.MismatchedInputException: Cannot construct instance o
- [camera topic] how to save OTP data in user-defined nodes
- [camera special topic] Hal layer - brief analysis of addchannel and startchannel
- Network security NAT network address translation
- [Appendix 6 Application of reflection] Application of reflection: dynamic agent
猜你喜欢

Button button adaptive size of wechat applet

Asian Games countdown! AI target detection helps host the Asian Games!

Introduction to kotlin collaboration
¢ growth path and experience sharing of getting an offer
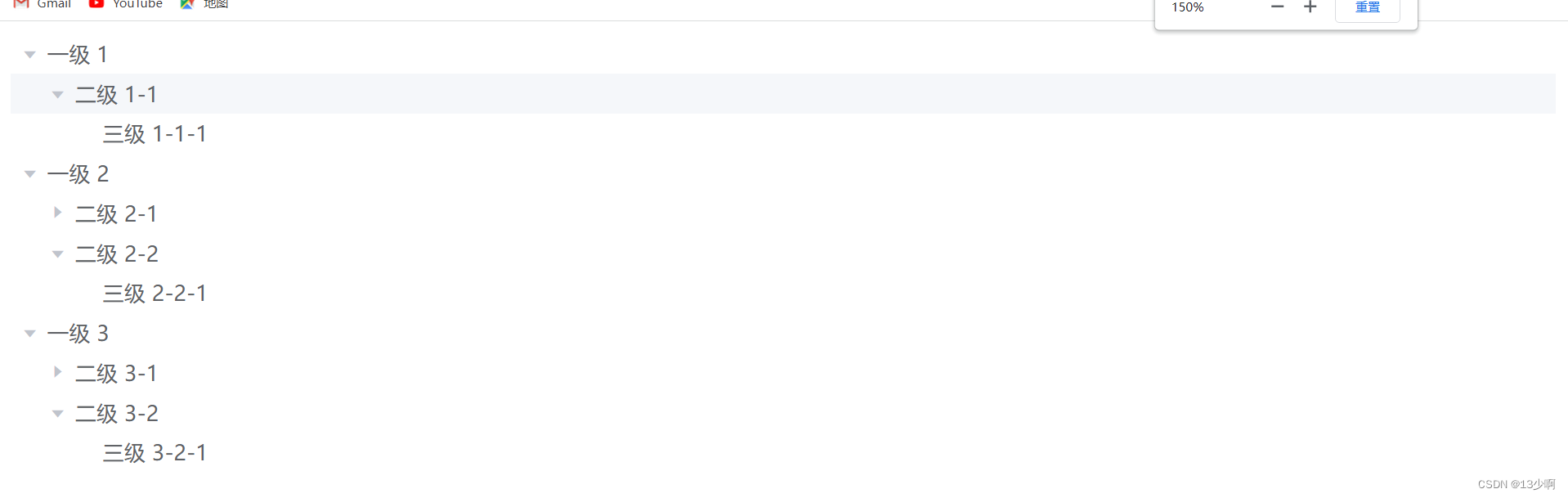
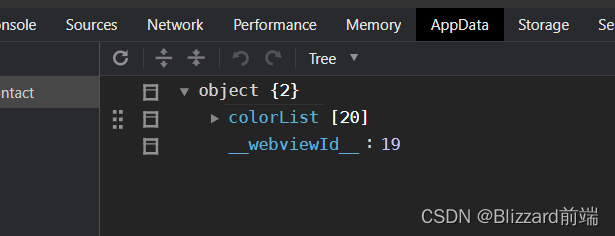
Processing of tree structure data

NCTF 2018 part Title WP (1)
小程序开发的部分功能

Everything文件搜索工具

What are the differences between software testers with a monthly salary of 7K and 25K? Leaders look up to you when they master it
![[error record] navigator operation requested with a context that does not include a naviga](/img/53/e28718970a2f7226ed53afa27f6725.jpg)
[error record] navigator operation requested with a context that does not include a naviga
随机推荐
Everything file search tool
Network security - password cracking
Introduction to kotlin collaboration
Network security - Trojan horse
mysql
机器学习笔记(持续更新中。。。)
全链路数字化转型下,零售企业如何打开第二增长曲线
[camera topic] how to save OTP data in user-defined nodes
微信小程序開發工具 POST net::ERR_PROXY_CONNECTION_FAILED 代理問題
Anna: Beibei, can you draw?
[data mining] task 5: k-means/dbscan clustering: double square
Groovy, "try with resources" construction alternative
Types of map key and object key
网络安全-病毒
【Camera专题】HAL层-addChannel和startChannel简析
[shutter] shutter debugging (debugging control related functions | breakpoint management | code operation control)
【数据挖掘】任务1:距离计算
树形结构数据的处理
One of the C language practical projects is greedy snake
自定义组件、使用npm包、全局数据共享、分包