当前位置:网站首页>2022 Guangxi Autonomous Region secondary vocational group "Cyberspace Security" competition and its analysis (super detailed)
2022 Guangxi Autonomous Region secondary vocational group "Cyberspace Security" competition and its analysis (super detailed)
2022-07-06 01:20:00 【Lonely fish】
2022 Secondary vocational group of Guangxi Autonomous Region in “ Cyberspace Security ” Event module B analysis
- 2022 Guangxi autonomous region competition assignment of secondary vocational group
- modular A Infrastructure setting and security reinforcement (200 branch )
- modular B Network security event response 、 Digital forensics investigation and application security (400 branch )
- modular C CTF Flag capture - attack (200 branch )
- modular D CTF Flag capture - defense (200 branch )
- If you don't understand, you can send a private letter to the blogger !
2022 Guangxi autonomous region competition assignment of secondary vocational group
One 、 Competition time
A total of :360 minute
Module number Module name Competition time ( Hours ) A weight
A Infrastructure setting and security reinforcement 1.5 20%
B Network security event response 、 Digital forensics investigation and application security 1.5 40%
C CTF Flag capture - attack 1.5 20%
D CTF Flag capture - defense 1.5 20%
modular A Infrastructure setting and security reinforcement (200 branch )
One 、 Project and task description :
Suppose you are a network security engineer in an enterprise , For enterprise server system , Ensure the normal operation of all services according to the task requirements , And through the comprehensive use of login and password
边栏推荐
- Electrical data | IEEE118 (including wind and solar energy)
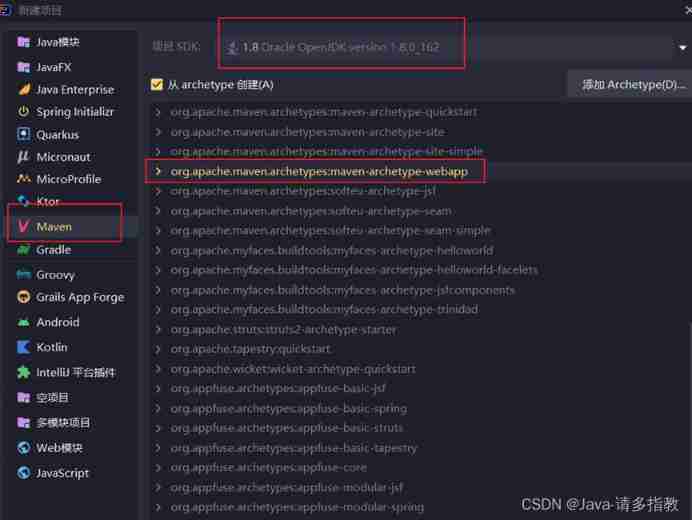
- 基於DVWA的文件上傳漏洞測試
- MUX VLAN configuration
- 电气数据|IEEE118(含风能太阳能)
- [Yu Yue education] Liaoning Vocational College of Architecture Web server application development reference
- Study diary: February 13, 2022
- 黄金价格走势k线图如何看?
- VSphere implements virtual machine migration
- 现货白银的一般操作方法
- Ordinary people end up in Global trade, and a new round of structural opportunities emerge
猜你喜欢
servlet(1)

Mlsys 2020 | fedprox: Federation optimization of heterogeneous networks
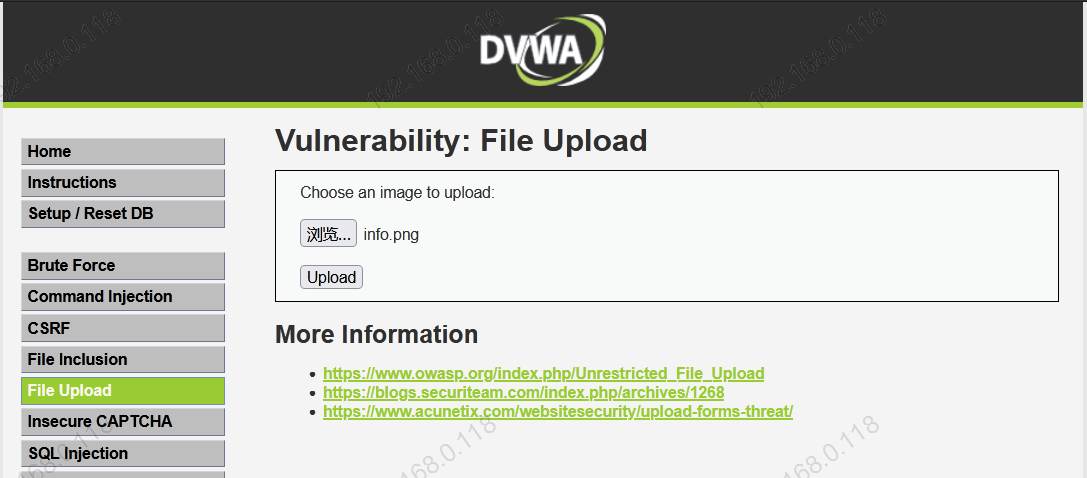
Test de vulnérabilité de téléchargement de fichiers basé sur dvwa
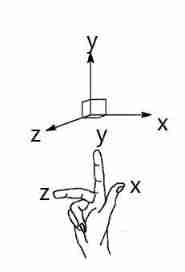
Introduction to robotics I. spatial transformation (1) posture, transformation
![[pat (basic level) practice] - [simple mathematics] 1062 simplest fraction](/img/b4/3d46a33fa780e5fb32bbfe5ab26a7f.jpg)
[pat (basic level) practice] - [simple mathematics] 1062 simplest fraction
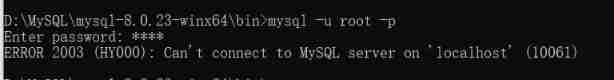
About error 2003 (HY000): can't connect to MySQL server on 'localhost' (10061)
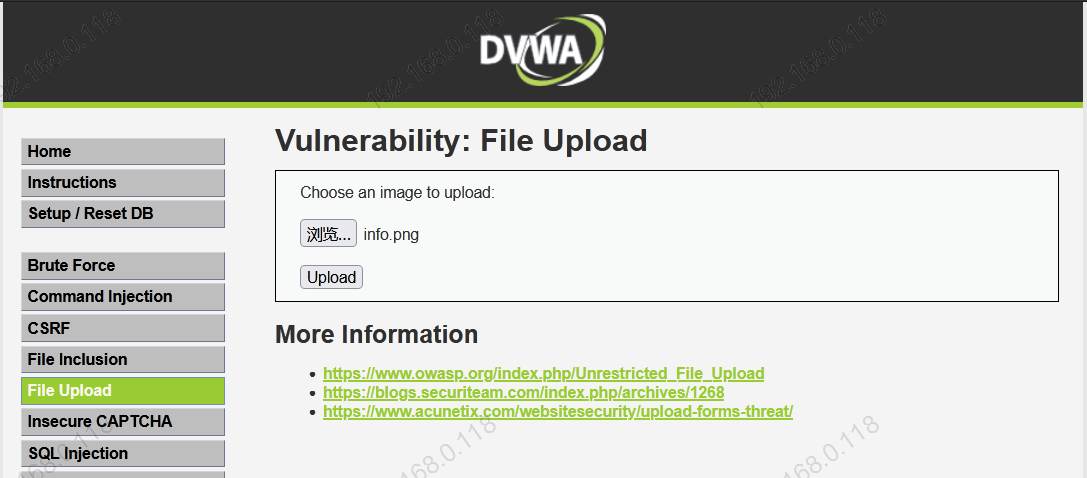
File upload vulnerability test based on DVWA
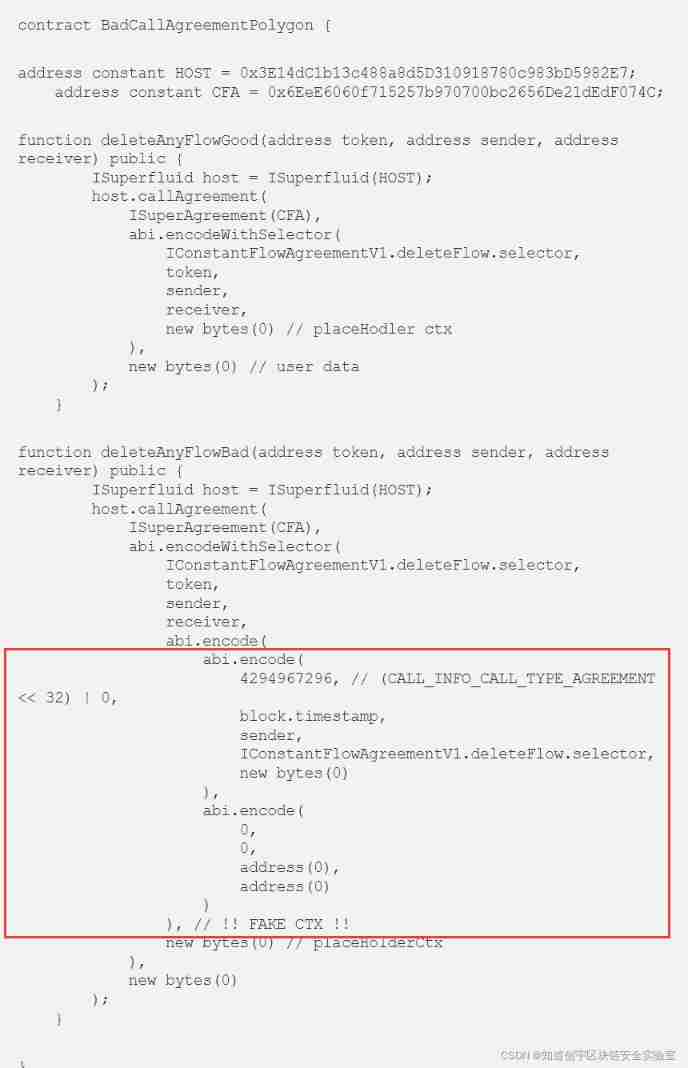
Superfluid_ HQ hacked analysis
![Cf:d. insert a progression [about the insert in the array + the nature of absolute value + greedy top-down]](/img/9e/c933f454a39d906a407e4d415f0b87.png)
Cf:d. insert a progression [about the insert in the array + the nature of absolute value + greedy top-down]
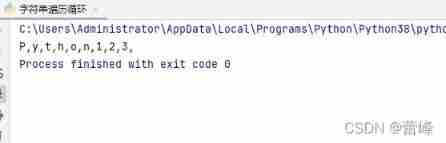
Loop structure of program (for loop)
随机推荐
Differences between standard library functions and operators
Five challenges of ads-npu chip architecture design
Is chaozhaojin safe? Will it lose its principal
测试/开发程序员的成长路线,全局思考问题的问题......
Recursive method to realize the insertion operation in binary search tree
Opinions on softmax function
Cf:d. insert a progression [about the insert in the array + the nature of absolute value + greedy top-down]
ORA-00030
普通人下场全球贸易,新一轮结构性机会浮出水面
Ordinary people end up in Global trade, and a new round of structural opportunities emerge
Exciting, 2022 open atom global open source summit registration is hot
Mysql--- query the top 5 students
3D model format summary
Live broadcast system code, custom soft keyboard style: three kinds of switching: letters, numbers and punctuation
Gartner released the prediction of eight major network security trends from 2022 to 2023. Zero trust is the starting point and regulations cover a wider range
Modify the ssh server access port number
直播系统代码,自定义软键盘样式:字母、数字、标点三种切换
Unity | 实现面部驱动的两种方式
黄金价格走势k线图如何看?
Pbootcms plug-in automatically collects fake original free plug-ins