当前位置:网站首页>Redis' cache penetration, cache breakdown, cache avalanche
Redis' cache penetration, cache breakdown, cache avalanche
2022-07-06 01:01:00 【Middle aged leaning on crutches to learn java】
Prior to redis In the article of , We said redis Master-slave replication of , Now let's talk about redis Frequent concentration problems
1, Cache penetration , It refers to data not in the cache and not in the database , This will result in cache misses , Because there is no such data in the database , So it will not be written to the cache after the request , This will lead to direct access to the data source , Result in crushing the data source
2, Cache breakdown , Refer to key The corresponding data exists , But it expired in the cache . At this time, a large number of highly concurrent data requests come , It will lead to direct access to the data source because there is no cache , After accessing, you need to write the data back to the data source , This will easily overwhelm the data source
3, Cache avalanche , This is when the cache server restarts or the cache fails within a time period , This will invalidate all caches , To crush the data source
Solution
For cache penetration , I know about two ways
The first is to use a large enough bitmap( use bitmap, Because it can save more space ) Put all possible key It's all in it , In this way, non-existent requests will be filtered out
The second is to use a null value storage , After a nonexistent request calls , Not in cache , Will go to the data source to check , At this time, because there is no data source, we will not write back to the cache , But to avoid cache penetration , We can also save this null value , It's just that the expiration time is set shorter .
Cache breakdown is now commonly used in the way of locking , Xiaobian is a little sleepy , I'll share these with you next time .
边栏推荐
- Promise
- The value of applet containers
- WordPress collection plug-in automatically collects fake original free plug-ins
- [groovy] compile time meta programming (compile time method interception | method interception in myasttransformation visit method)
- The relationship between FPGA internal hardware structure and code
- Recursive method converts ordered array into binary search tree
- 面试必刷算法TOP101之回溯篇 TOP34
- Cf:c. the third problem
- 有谁知道 达梦数据库表的列的数据类型 精度怎么修改呀
- [groovy] JSON string deserialization (use jsonslurper to deserialize JSON strings | construct related classes according to the map set)
猜你喜欢
关于#数据库#的问题:(5)查询库存表中每本书的条码、位置和借阅的读者编号
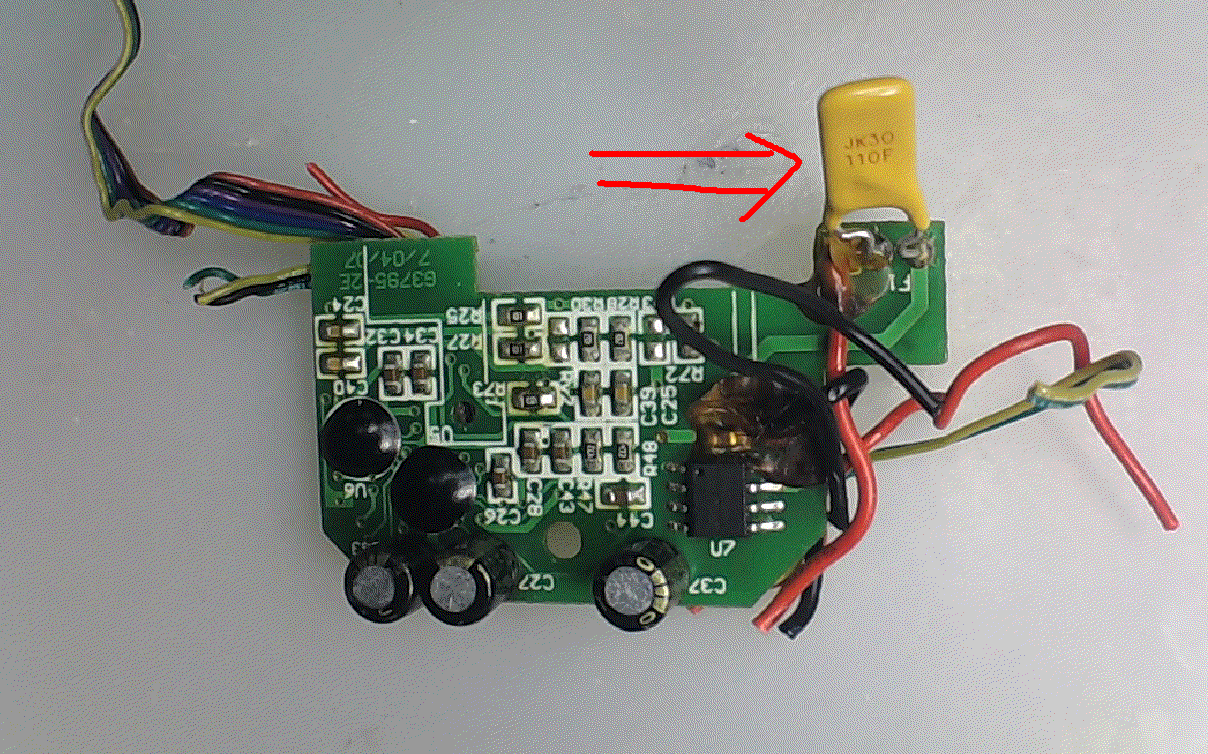
Recoverable fuse characteristic test

MCU通过UART实现OTA在线升级流程
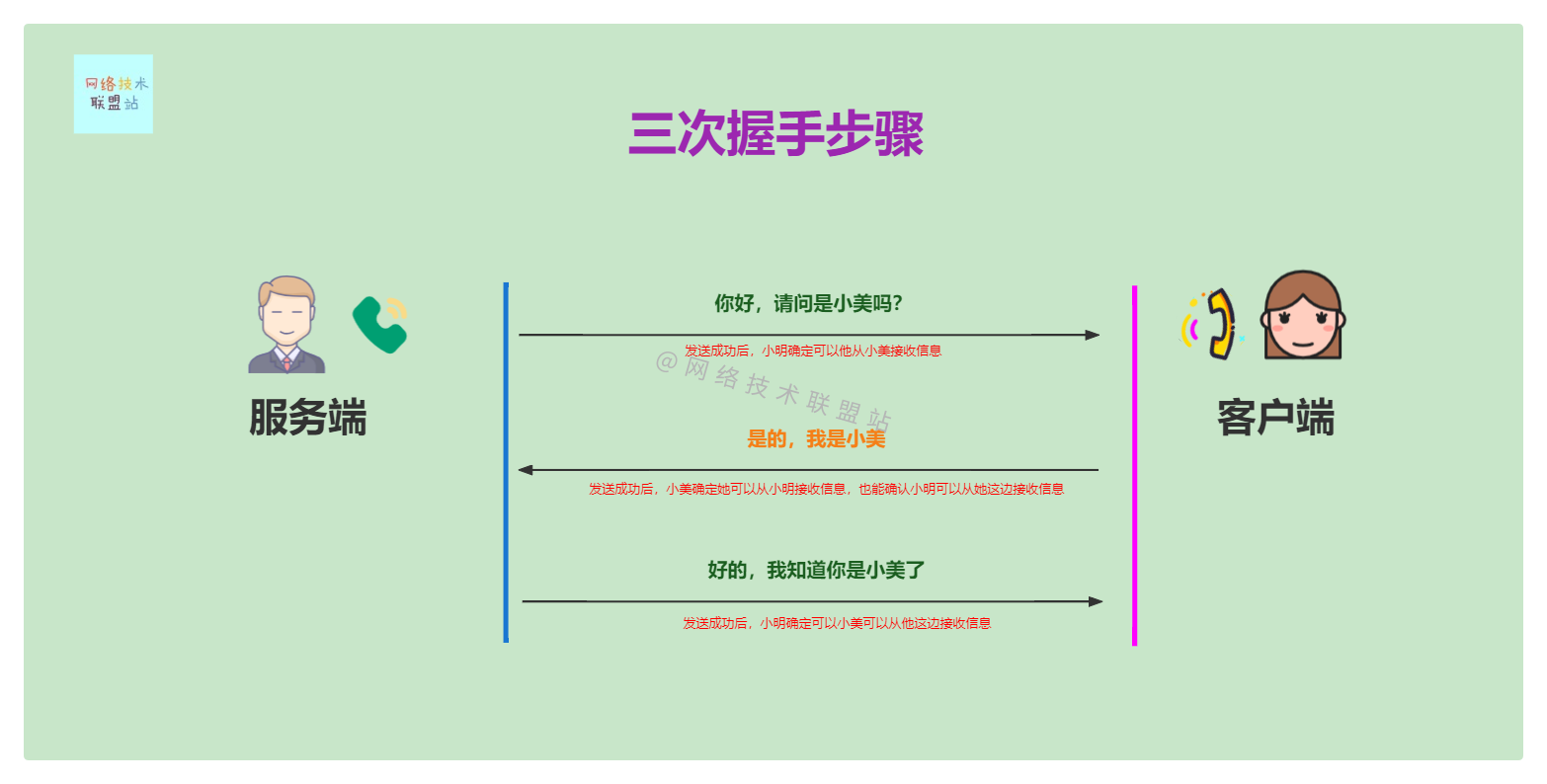
图解网络:TCP三次握手背后的原理,为啥两次握手不可以?
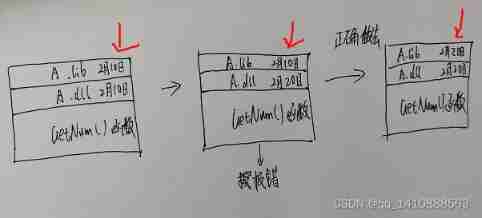
The inconsistency between the versions of dynamic library and static library will lead to bugs
![Cf:d. insert a progression [about the insert in the array + the nature of absolute value + greedy top-down]](/img/9e/c933f454a39d906a407e4d415f0b87.png)
Cf:d. insert a progression [about the insert in the array + the nature of absolute value + greedy top-down]

Keepalive component cache does not take effect
如何制作自己的機器人
![[groovy] JSON serialization (convert class objects to JSON strings | convert using jsonbuilder | convert using jsonoutput | format JSON strings for output)](/img/52/021931181ad3f4bef271b4e98105c2.jpg)
[groovy] JSON serialization (convert class objects to JSON strings | convert using jsonbuilder | convert using jsonoutput | format JSON strings for output)
Intensive learning weekly, issue 52: depth cuprl, distspectrl & double deep q-network
随机推荐
1791. Find the central node of the star diagram / 1790 Can two strings be equal by performing string exchange only once
Questions about database: (5) query the barcode, location and reader number of each book in the inventory table
Cf:c. the third problem
详细页返回列表保留原来滚动条所在位置
Mlsys 2020 | fedprox: Federation optimization of heterogeneous networks
如何制作自己的機器人
curlpost-php
Kotlin core programming - algebraic data types and pattern matching (3)
The third season of ape table school is about to launch, opening a new vision for developers under the wave of going to sea
[groovy] JSON serialization (convert class objects to JSON strings | convert using jsonbuilder | convert using jsonoutput | format JSON strings for output)
I'm interested in watching Tiktok live beyond concert
Building core knowledge points
孤勇者
MYSQL GROUP_ The concat function realizes the content merging of the same ID
Obstacle detection
Cannot resolve symbol error
KDD 2022 | EEG AI helps diagnose epilepsy
测试/开发程序员的成长路线,全局思考问题的问题......
[groovy] compile time metaprogramming (compile time method injection | method injection using buildfromspec, buildfromstring, buildfromcode)
Why can't mathematics give machine consciousness