当前位置:网站首页>Distributed base theory
Distributed base theory
2022-07-06 00:53:00 【It blade out of sheath】
Original website :
brief introduction
This article introduces BASE theory .
For business systems , We often choose to sacrifice consistency for system availability and partition fault tolerance . But the point here is , So-called “ Sacrifice consistency ” It's not all about giving up data consistency , It's sacrifice Strong consistency Exchange for Weak consistency .
Base theory : Basic available (Basically Available), Soft state (Soft State), Final consistency (Eventually Consistent)
Basic Available
Suppose the system , There was an unforeseen breakdown , But it still works , Compared with a normal system, there are the following losses :
- Loss of response time : Example : Normal search engines 0.5 Seconds to return the result to the user , And basically available search engines can be found in 2 Second action returns the result .
- Loss of function : Example : On an e-commerce website , Under normal circumstances , Users can successfully complete every order . But when it comes to the promotion period , In order to protect the stability of the shopping system , Some consumers may be directed to a degraded page .
Soft State
Hard state : Compared with atomicity , The data copies of multiple nodes are required to be consistent .
Soft state : Allow data in the system to have intermediate states , It is considered that this state does not affect the overall availability of the system , That is to say, the system is allowed to have data delay in data copies of multiple different nodes .
Eventually Consistent
It says soft state , Then it can't be soft all the time , There must be a time limit . After the deadline , Data consistency should be guaranteed for all copies , So as to achieve the final consistency of data . This time period depends on the network delay 、 System load 、 Data replication scheme design and other factors .
In practical engineering practice , The final consistency is divided into 5 Kind of :
| term | explain |
| Causal consistency (Causal consistency) | If node A After updating some data, the node is notified B, Then the node B Later, the access and modification of the data are based on A Updated value . meanwhile , And nodes A Nodes without causality C There are no such restrictions on data access . |
| Read what you have written (Read your writes) | node A After updating a data , It always has access to the latest values it has updated , Instead of seeing the old value . Actually, it's also a kind of causal consistency . |
| Conversation consistency (Session consistency) | Session consistency frames the process of accessing system data in a session : The system can guarantee the same effective session “ Read what you have written ” The consistency of , in other words , After performing the update operation , The client can always read the latest value of the data item in the same session . |
| Monotonous reading consistency (Monotonic read consistency) | If a node reads a value of a data item from the system , Then the system should not return the older value for any subsequent data access of the node . |
| Monotonous writing consistency (Monotonic write consistency) | A system should be able to ensure that writes from the same node are executed sequentially . |
In practice , this 5 These systems are often used in combination , To build a distributed system with ultimate consistency .
actually , It's not just distributed systems that use ultimate consistency , Relational database in a certain function , Also using final consistency . Such as backup , The database replication process takes time , In this replication process , The value read by the business is old . Of course , In the end, data consistency was achieved . This is a classic case of ultimate consistency .
ACID It can guarantee the strong consistency of transactions , That is, the data is consistent in real time . This is no problem in local transactions , In distributed transactions , Strong consistency will greatly affect the performance of distributed systems , So the distributed system follows BASE Theory is enough .
Different business scenarios of distributed systems have different requirements for consistency . Such as in the trading scenario , It requires strong consistency , At this point you need to follow ACID theory , And send SMS verification code after registration , There's no need for real-time consistency , So follow BASE Theory is enough .
According to specific business scenarios , stay ACID and BASE Find a balance between .
Other websites
《 from Paxos To Zookeeper Principle and practice of distributed consistency 》
边栏推荐
- Cf:d. insert a progression [about the insert in the array + the nature of absolute value + greedy top-down]
- China Taiwan strategy - Chapter 8: digital marketing assisted by China Taiwan
- The relationship between FPGA internal hardware structure and code
- MCU realizes OTA online upgrade process through UART
- 面试必刷算法TOP101之回溯篇 TOP34
- 云导DNS和知识科普以及课堂笔记
- Five challenges of ads-npu chip architecture design
- An understanding of & array names
- 程序员搞开源,读什么书最合适?
- 如何制作自己的机器人
猜你喜欢
看抖音直播Beyond演唱会有感
2020.2.13
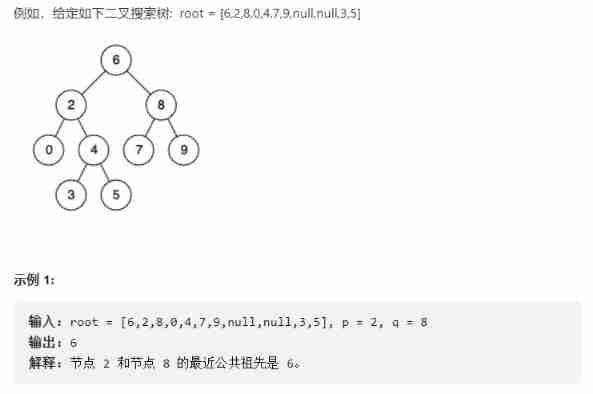
Finding the nearest common ancestor of binary search tree by recursion

After 95, the CV engineer posted the payroll and made up this. It's really fragrant
Intensive learning weekly, issue 52: depth cuprl, distspectrl & double deep q-network
测试/开发程序员的成长路线,全局思考问题的问题......
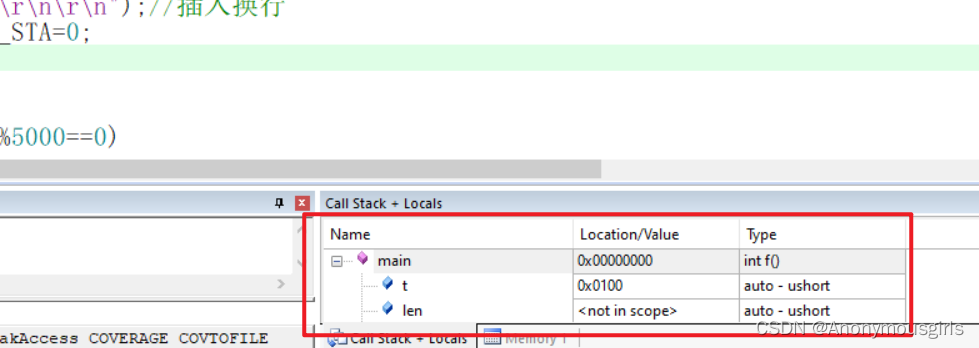
Set data real-time update during MDK debug
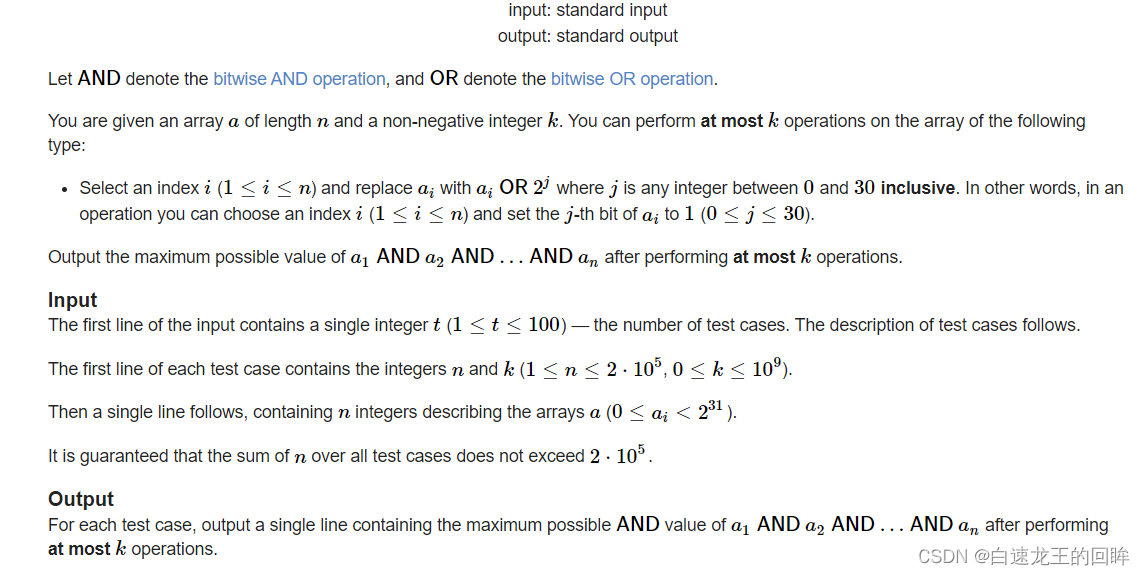
cf:H. Maximal AND【位运算练习 + k次操作 + 最大And】

The third season of ape table school is about to launch, opening a new vision for developers under the wave of going to sea
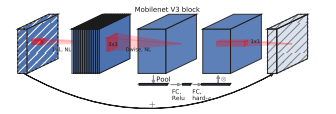
MobileNet系列(5):使用pytorch搭建MobileNetV3并基于迁移学习训练
随机推荐
Idea远程提交spark任务到yarn集群
Recoverable fuse characteristic test
Model analysis of establishment time and holding time
2022-02-13 work record -- PHP parsing rich text
Five challenges of ads-npu chip architecture design
关于#数据库#的问题:(5)查询库存表中每本书的条码、位置和借阅的读者编号
MySQL storage engine
Extension and application of timestamp
Spark-SQL UDF函数
Arduino hexapod robot
Starting from 1.5, build a micro Service Framework - call chain tracking traceid
Promise
Uniapp development, packaged as H5 and deployed to the server
An understanding of & array names
MobileNet系列(5):使用pytorch搭建MobileNetV3并基于迁移学习训练
[groovy] XML serialization (use markupbuilder to generate XML data | create sub tags under tag closures | use markupbuilderhelper to add XML comments)
[groovy] compile time metaprogramming (compile time method interception | find the method to be intercepted in the myasttransformation visit method)
Spark DF adds a column
The detailed page returns to the list and retains the original position of the scroll bar
Anconda download + add Tsinghua +tensorflow installation +no module named 'tensorflow' +kernelrestart: restart failed, kernel restart failed