当前位置:网站首页>Protection strategy of server area based on Firewall
Protection strategy of server area based on Firewall
2022-07-07 14:48:00 【51CTO】
Protection strategy of firewall server area
Principle overview :
A firewall ( English :Firewall) Technology is through the organic combination of all kinds of software and hardware equipment for safety management and screening , Help the computer network in it 、 Build a relatively isolated protective barrier between the external networks , A technology to protect user data and information security .
The function of firewall technology is to discover and deal with the possible security risks when the computer network is running 、 Data transmission and so on , The treatment measures include isolation and protection , At the same time, it can record and test all operations in computer network security , To ensure the security of computer network operation , Guarantee the integrity of user data and information , Better for users 、 More secure computer network experience .
So-called “ A firewall ” It refers to an intranet and public access network ( Such as Internet) The way of separation , It is actually an applied security technology based on modern communication network technology and information security technology , Isolation technology . It is more and more used in the interconnection environment of private network and public network , Especially with access Internet The Internet is the most important .
Firewall is a protective barrier between the internal and external network environment with the help of hardware and software , So as to block the unsafe network factors of the computer . Only with the consent of the firewall , Users can enter the computer , If you don't agree, you'll be blocked out , The alarm function of firewall technology is very powerful , When an external user wants to enter the computer , The firewall will quickly send out the corresponding alarm , And remind users of their behavior , And make self judgment to decide whether to allow external users to enter the interior , As long as the user is in the network environment , This kind of firewall can carry out effective query , At the same time, the information found will be displayed to the user , Then users need to implement corresponding settings for the firewall according to their own needs , Block the disallowed user behavior . Through the firewall, you can also effectively view the traffic of information data , And it can also master the speed of uploading and downloading data information , It is convenient for users to have good control judgment on the use of computers , The internal situation of the computer can also be viewed through this firewall , It also has the function of starting and closing the program , And the internal log function of the computer system , In fact, it is also a summary of the real-time situation of the firewall and the internal security of the computer system .
Firewall is a kind of access control scale which is executed when two networks communicate , It can prevent hackers from accessing your network to the maximum extent . It's set up on different networks ( Such as trusted intranet and untrusted public network ) Or a combination of components between network security domains . It is the only access to information between different networks or network security domains , Be able to control according to the safety policy of the enterprise ( allow 、 Refuse 、 monitoring ) Information flow in and out of the network , And it has strong anti attack ability . It's about providing information security services , Infrastructure for network and information security . Logically , The firewall is a separator , A limiter , It's also an analyzer , Effectively monitored the intranet and Internet Any activity between , Ensure the security of the internal network .
The firewall scans its network traffic , This will filter out some attacks , In case it is executed on the target computer . Firewalls can also shut down unused ports . And it can also disable outgoing traffic on specific ports , Block the Trojan horse . Last , It can disable access from special sites , To prevent all communications from unknown intruders .
The barrier of network security
A firewall ( As a blocking point 、 The control points ) It can greatly improve the security of an internal network , And reduce risk by filtering unsafe Services . Because only carefully selected application protocols can pass through the firewall , So the network environment becomes more secure . For example, firewalls can prohibit such as well-known unsafe NFS Protocol access to protected network , In this way, it is impossible for external attackers to use these fragile protocols to attack the internal network . Firewalls can also protect the network from routing based attacks , Such as IP Source routing attacks and ICMP Redirection path in redirection . The firewall should be able to reject all messages of the above types of attacks and notify the firewall administrator .
Strengthen network security strategy
Configure through a firewall centric security scheme , All security software ( Like a password 、 encryption 、 Identity Authentication 、 Audit, etc ) Configure on the firewall . Compared with dispersing network security issues to various hosts , Centralized security management of firewall is more economical . For example, during network access , The one-time password system and other identity authentication systems do not have to be scattered on each host , And focus on the firewall .
Monitoring audit
If all access passes through the firewall , that , The firewall can record these accesses and log them , At the same time, it can also provide statistical data of network usage . When something suspicious happens , The firewall can give appropriate alarm , And provide detailed information on whether the network is monitored and attacked . in addition , It is also very important to collect the usage and misuse of a network . The first reason is to know whether the firewall can resist the detection and attack of attackers , And know whether the control of firewall is sufficient . Network usage statistics are also very important for network demand analysis and threat analysis .
Prevent the leakage of internal information
By using firewall to divide the internal network , It can realize the isolation of key network segments of intranet , Thus, the impact of local key or sensitive network security issues on the global network is limited . also , Privacy is an issue of great concern to the intranet , An unnoticed detail in an internal network may contain clues about security and attract the interest of external attackers , Some security vulnerabilities of the internal network have even been exposed . Using a firewall, you can hide those internal details, such as Finger,DNS Etc .Finger Displays the registered names of all users of the host 、 real name , Last login time and use shell Type, etc . however Finger The information displayed is very easy for attackers to learn . An attacker can know how often a system is used , Whether there are users connecting to the Internet in this system , Whether the system is noticed when being attacked, etc . Firewalls can also block information about internal networks DNS Information , The domain name of such a host and IP The address will not be known to the outside world . In addition to safety , The firewall also supports Internet Service enterprise internal network technology system VPN( Virtual private network ).
Logging and event notification
All data entering and leaving the network must pass through the firewall , The firewall records it through logs , It can provide detailed statistical information of network use . When a suspicious event occurs , The firewall can alarm and notify according to the mechanism , Provide information on whether the network is threatened .
The experiment purpose :
Understand and master the firewall protection strategy for the server area
The topology :
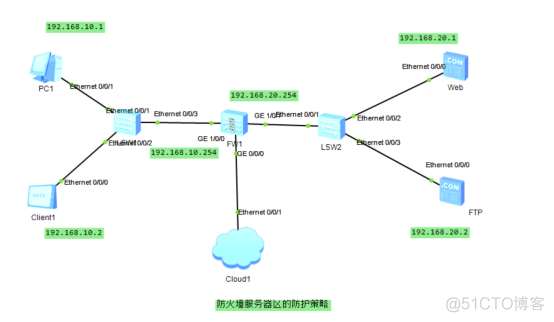
Basic configuration :
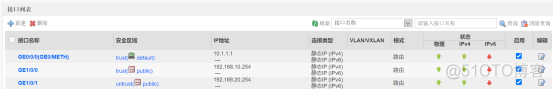
Firewall configuration :
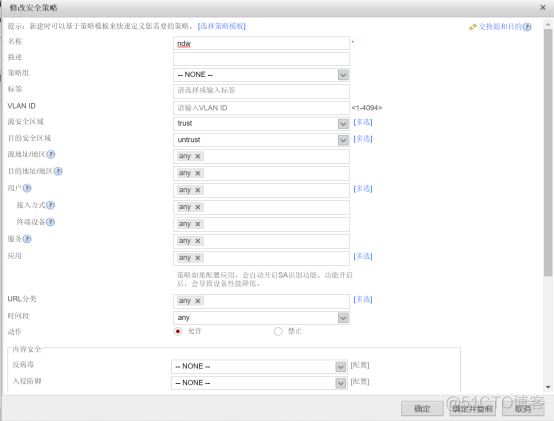
Configure security policy ;

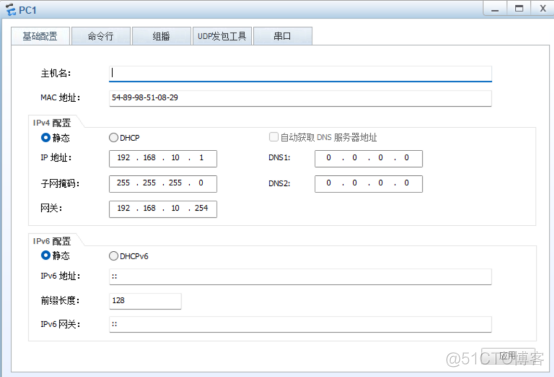
Configure client :

Configure server :


Firewall configuration security protection :

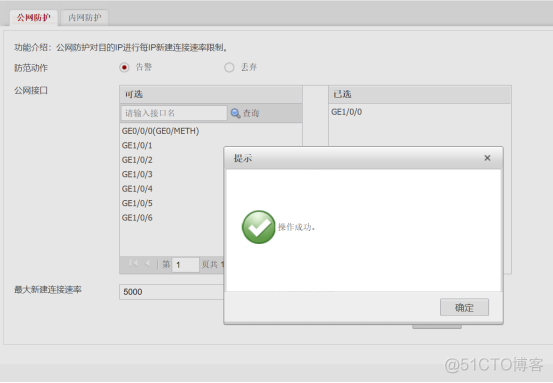
To configure IP Speed limit public network protection :
PC Long ping The server , Check the five tuple packet capture :

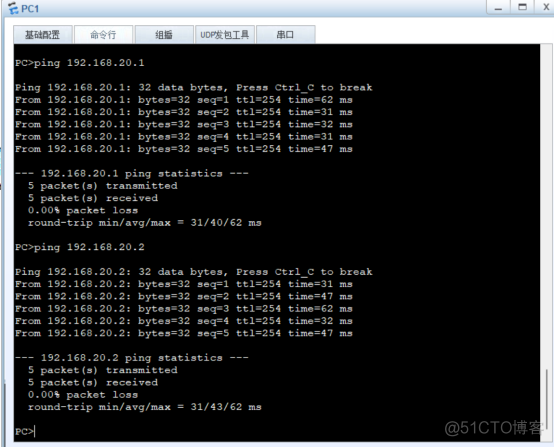
PC ping web and FTP The server :
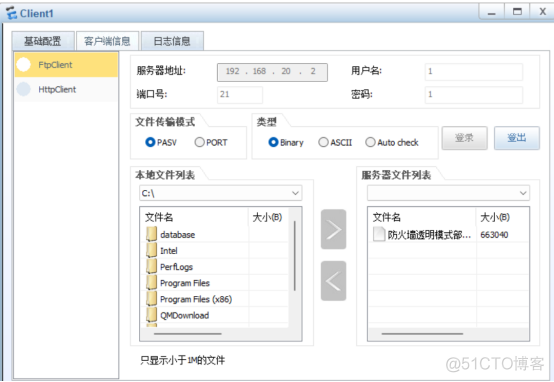
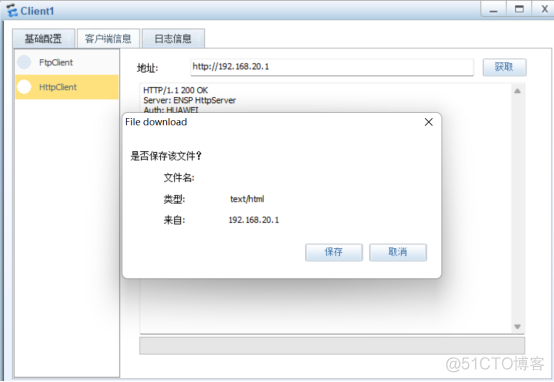
Client obtain Web and FTP Server services :
End of experiment ;
remarks : If there is a mistake , Please understand !
This article is my study notes , For reference only ! If there is a repetition !!! Please contact me
边栏推荐
- 时空可变形卷积用于压缩视频质量增强(STDF)
- PyTorch模型训练实战技巧,突破速度瓶颈
- JS in the browser Base64, URL, blob mutual conversion
- The world's first risc-v notebook computer is on pre-sale, which is designed for the meta universe!
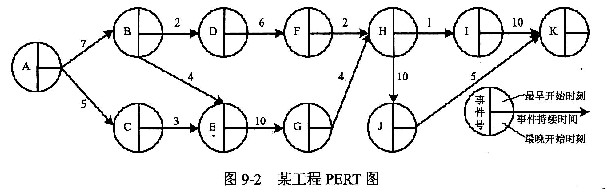
- Pert diagram (engineering network diagram)
- OAuth 2.0 + JWT protect API security
- Data connection mode in low code platform (Part 2)
- Computer win7 system desktop icon is too large, how to turn it down
- Equipment failure prediction machine failure early warning mechanical equipment vibration monitoring machine failure early warning CNC vibration wireless monitoring equipment abnormal early warning
- 低代码平台中的数据连接方式(下)
猜你喜欢
随机推荐
PG基础篇--逻辑结构管理(锁机制--表锁)
Démontage de la fonction du système multi - Merchant Mall 01 - architecture du produit
EMQX 5.0 发布:单集群支持 1 亿 MQTT 连接的开源物联网消息服务器
Wechat applet - Advanced chapter component packaging - Implementation of icon component (I)
OAuth 2.0 + JWT protect API security
Five pain points for big companies to open source
2022 cloud consulting technology series high availability special sharing meeting
Beginner JSP
什么是云原生?这回终于能搞明白了!
13 ux/ui/ue best creative inspiration websites in 2022
数据库如何进行动态自定义排序?
华为云数据库DDS产品深度赋能
[Yugong series] go teaching course 005 variables in July 2022
What is cloud primordial? This time, I can finally understand!
Xiaomi's path of chip self-development
LeetCode每日一题(636. Exclusive Time of Functions)
Oracle non automatic submission solution
Because the employee set the password to "123456", amd stolen 450gb data?
Attribute keywords serveronly, sqlcolumnnumber, sqlcomputecode, sqlcomputed
一个程序员的水平能差到什么程度?尼玛,都是人才呀...