当前位置:网站首页>File upload vulnerability test based on DVWA
File upload vulnerability test based on DVWA
2022-07-06 01:07:00 【wishLifeJumP】
Catalog
DVWA
Low
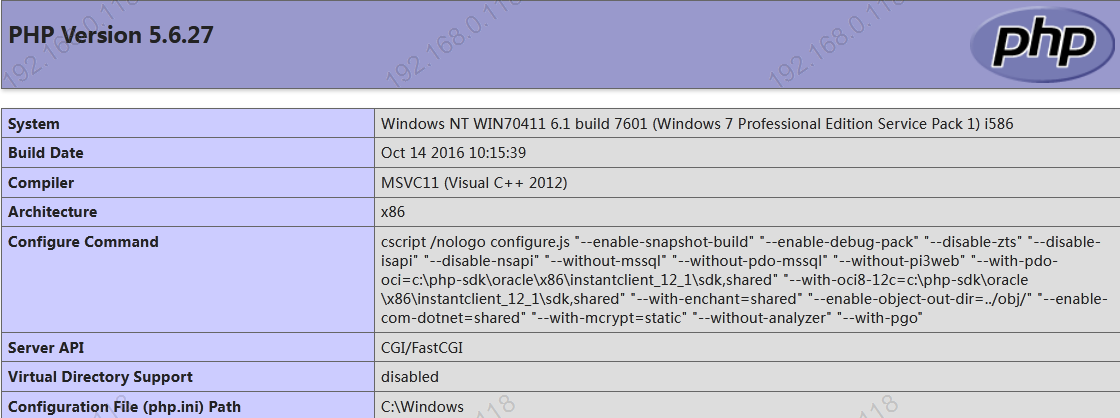
DVWA Security Of “low” Levels can be uploaded directly “ In a word ” Trojan horse .
1.1 Write test Trojan
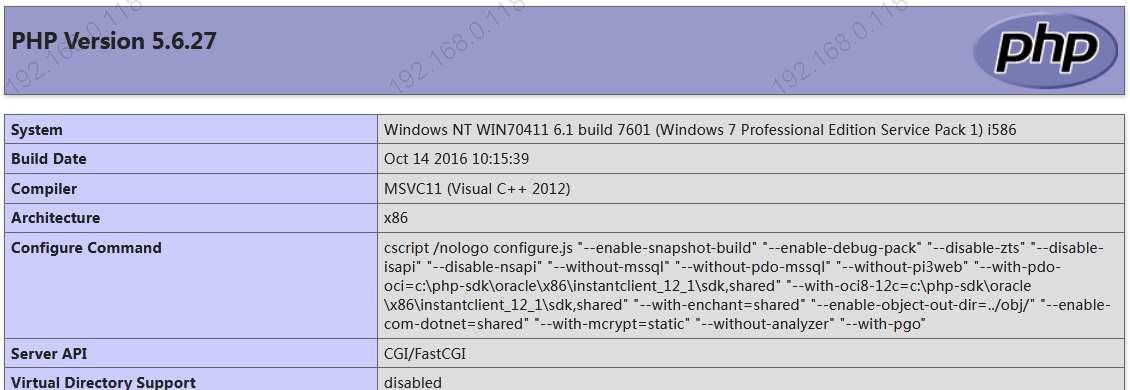
<?php
phpinfo();
?>1.2 Upload directly without suffix filtering

1.3 Echo the upload path , Just visit directly
http://localhost/dvwa/hackable/uploads/info.php
Medium
Medium Level different from Low Level ,Medium The sector imposes upload restrictions on the front end , By bypassing the detection mechanism , Capture packets and change the suffix to achieve the upload effect .
2.1 Upload legal files , Open the agent
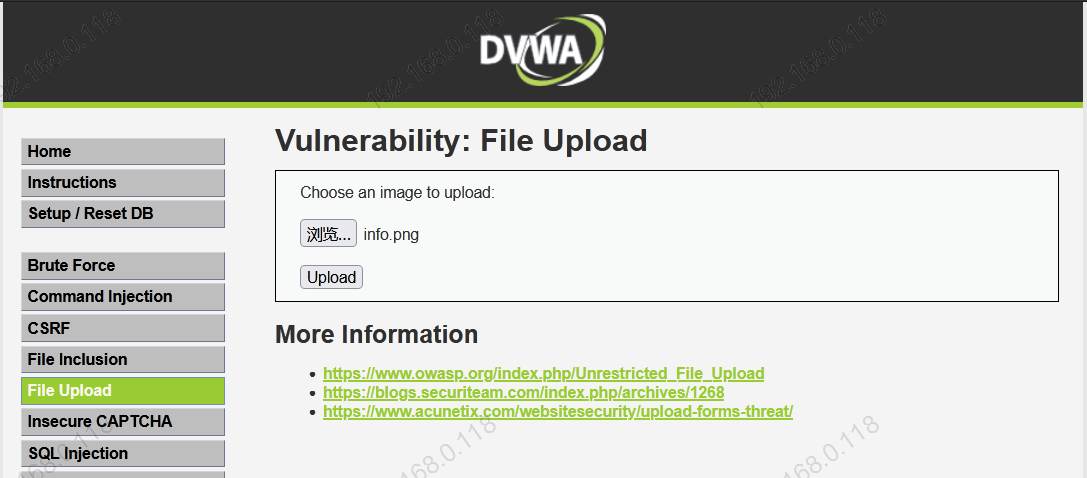
2.2 After catching the packet ,send to repeater
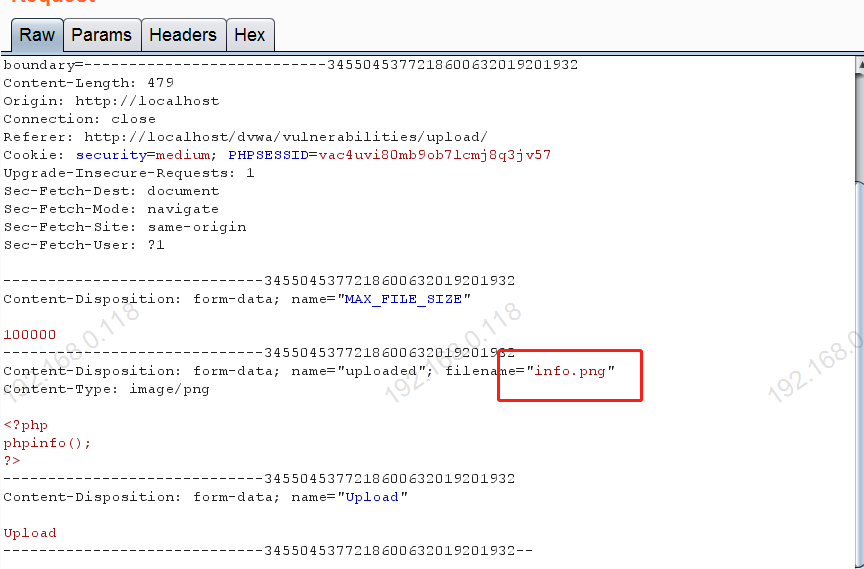
info.png Change it to info.php
The response code is 200 Instructions uploaded successfully .
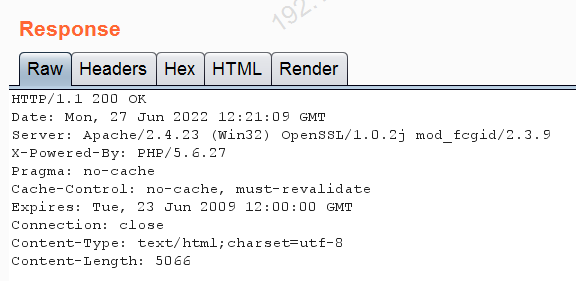
2.3 perform php Script
https://localhost/dvwa/hackable/uploads/info.php
边栏推荐
- Keepalive component cache does not take effect
- cf:D. Insert a Progression【关于数组中的插入 + 绝对值的性质 + 贪心一头一尾最值】
- Promise
- [groovy] JSON serialization (convert class objects to JSON strings | convert using jsonbuilder | convert using jsonoutput | format JSON strings for output)
- Recoverable fuse characteristic test
- What is the most suitable book for programmers to engage in open source?
- Recursive method converts ordered array into binary search tree
- How spark gets columns in dataframe --column, $, column, apply
- 图解网络:TCP三次握手背后的原理,为啥两次握手不可以?
- Live broadcast system code, custom soft keyboard style: three kinds of switching: letters, numbers and punctuation
猜你喜欢
Comment faire votre propre robot
![[groovy] JSON serialization (jsonbuilder builder | generates JSON string with root node name | generates JSON string without root node name)](/img/dd/bffe27b04d830d70f30df95a82b3d2.jpg)
[groovy] JSON serialization (jsonbuilder builder | generates JSON string with root node name | generates JSON string without root node name)

95后CV工程师晒出工资单,狠补了这个,真香...
![[pat (basic level) practice] - [simple mathematics] 1062 simplest fraction](/img/b4/3d46a33fa780e5fb32bbfe5ab26a7f.jpg)
[pat (basic level) practice] - [simple mathematics] 1062 simplest fraction
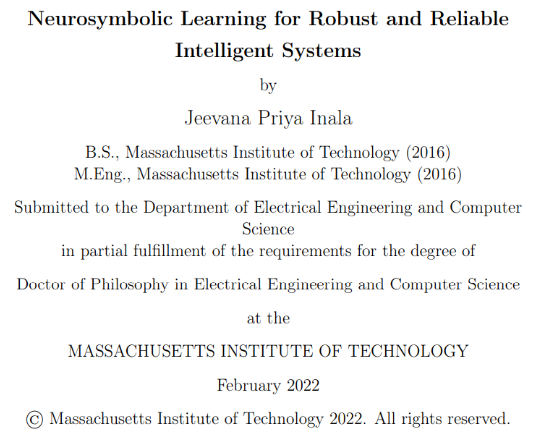
MIT doctoral thesis | robust and reliable intelligent system using neural symbol learning

MCU通过UART实现OTA在线升级流程
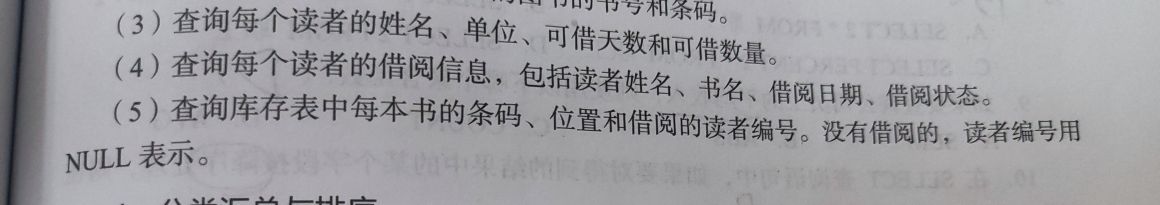
关于#数据库#的问题:(5)查询库存表中每本书的条码、位置和借阅的读者编号
Cf:c. the third problem
![[groovy] compile time metaprogramming (compile time method injection | method injection using buildfromspec, buildfromstring, buildfromcode)](/img/e4/a41fe26efe389351780b322917d721.jpg)
[groovy] compile time metaprogramming (compile time method injection | method injection using buildfromspec, buildfromstring, buildfromcode)
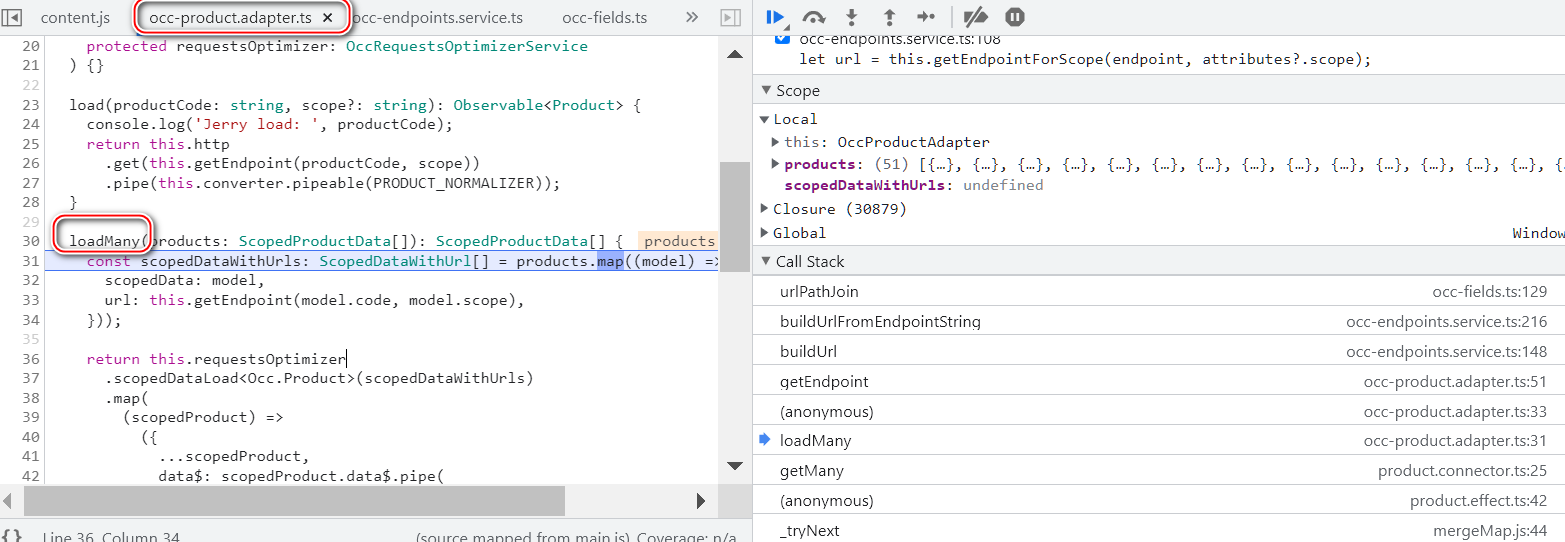
The population logic of the request to read product data on the sap Spartacus home page
随机推荐
The population logic of the request to read product data on the sap Spartacus home page
[groovy] XML serialization (use markupbuilder to generate XML data | create sub tags under tag closures | use markupbuilderhelper to add XML comments)
在产业互联网时代,将会凭借大的产业范畴,实现足够多的发展
朝招金安全吗 会不会亏损本金
Leetcode study - day 35
Recursive method converts ordered array into binary search tree
Programmer growth Chapter 9: precautions in real projects
Study diary: February 13, 2022
MCU realizes OTA online upgrade process through UART
Folding and sinking sand -- weekly record of ETF
China Taiwan strategy - Chapter 8: digital marketing assisted by China Taiwan
Cloud guide DNS, knowledge popularization and classroom notes
golang mqtt/stomp/nats/amqp
Synchronized and reentrantlock
How spark gets columns in dataframe --column, $, column, apply
Recoverable fuse characteristic test
curlpost-php
Browser reflow and redraw
MIT doctoral thesis | robust and reliable intelligent system using neural symbol learning
2020.2.13