当前位置:网站首页>Trying to use is on a network resource that is unavailable
Trying to use is on a network resource that is unavailable
2022-07-06 08:33:00 【MAR-Sky】
Processing steps
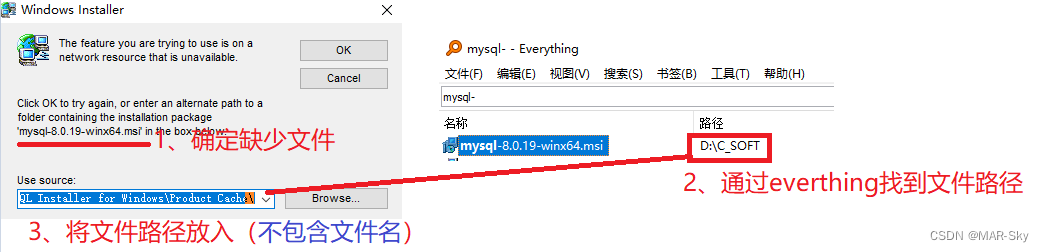
Personally, I think it's caused by
Used to be used in computers 360 Move the installed software to another location , Cause problems in the uninstall path . The essence of feeling is After installing the files, the installation files are moved , Thus, the uninstallation path cannot be found during uninstallation . I don't know if this is the reason , If you know something, you can leave a message
边栏推荐
- 角色动画(Character Animation)的现状与趋势
- marathon-envs项目环境配置(强化学习模仿参考动作)
- hutool优雅解析URL链接并获取参数
- Sublime text in CONDA environment plt Show cannot pop up the problem of displaying pictures
- 优秀的软件测试人员,都具备这些能力
- 电脑F1-F12用途
- 同一局域网的手机和电脑相互访问,IIS设置
- Colorlog结合logging打印有颜色的日志
- 深度剖析C语言数据在内存中的存储
- On the inverse order problem of 01 knapsack problem in one-dimensional state
猜你喜欢
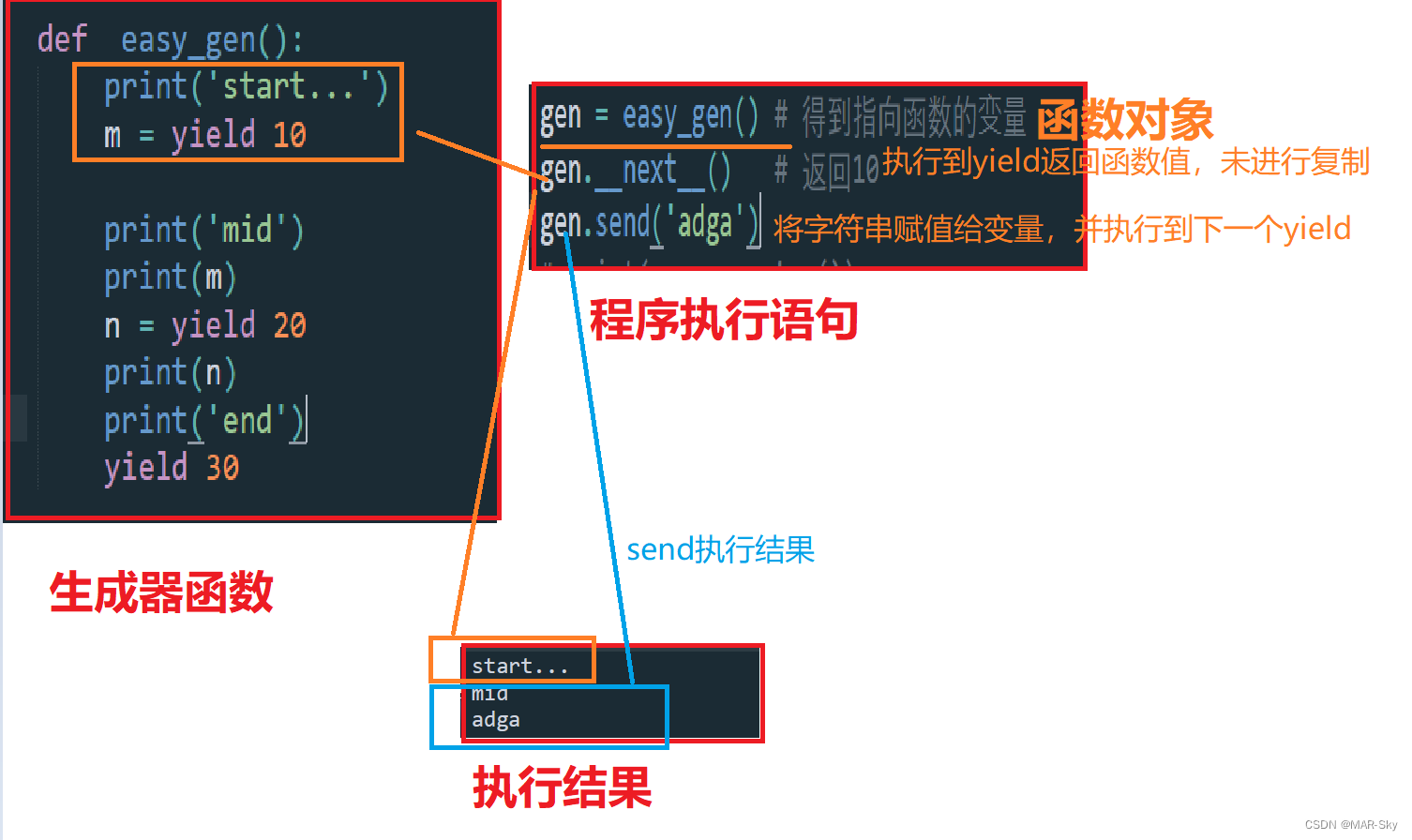
生成器参数传入参数

Deep analysis of C language data storage in memory
Chrome浏览器的crash问题

IOT -- interpreting the four tier architecture of the Internet of things
All the ArrayList knowledge you want to know is here
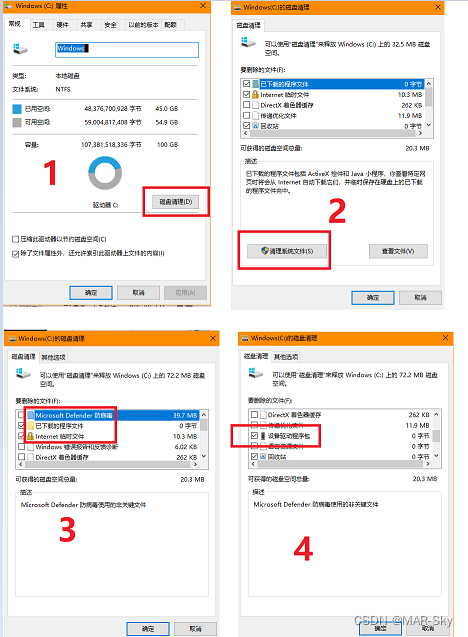
电脑清理,删除的系统文件
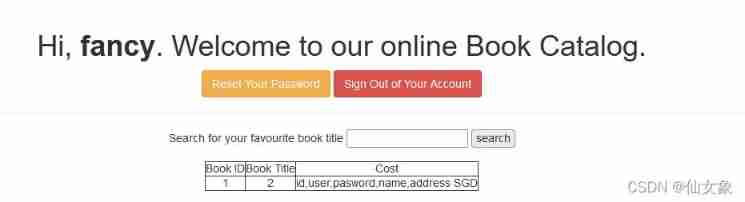
vulnhub hackme: 1
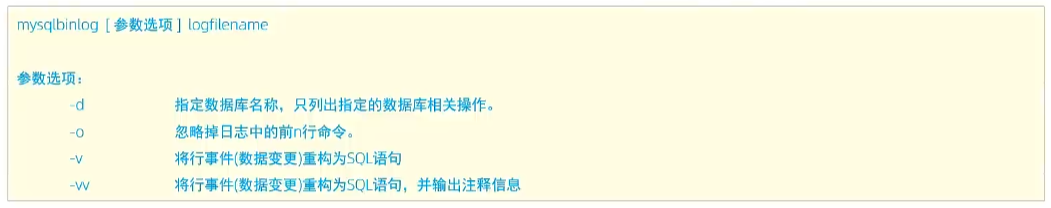
【MySQL】日志
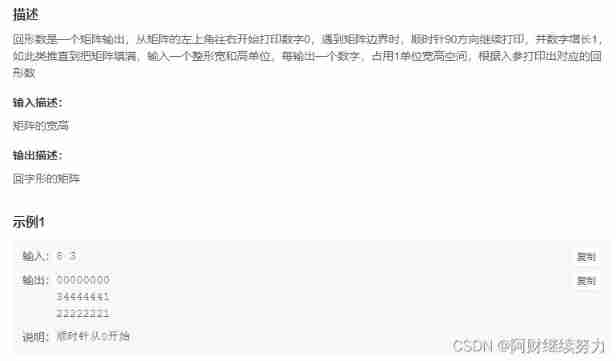
2022.02.13 - NC004. Print number of loops
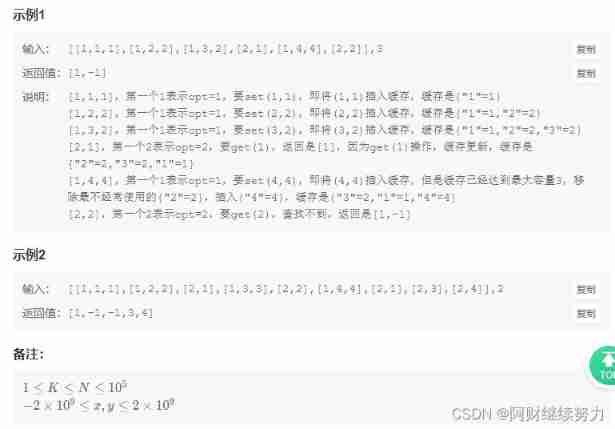
2022.02.13 - NC003. Design LRU cache structure
随机推荐
Restore backup data on S3 compatible storage with br
2022.02.13 - NC002. sort
Restore backup data on S3 compatible storage with tidb lightning
Unified ordering background interface product description Chinese garbled
Introduction to backup and recovery Cr
JVM performance tuning and practical basic theory - Part 1
【Nvidia开发板】常见问题集 (不定时更新)
sublime text中conda环境中plt.show无法弹出显示图片的问题
JVM performance tuning and practical basic theory - Part 1
The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower
MySQL learning record 07 index (simple understanding)
堆排序详解
Synchronized solves problems caused by sharing
Sort according to a number in a string in a column of CSV file
synchronized 解决共享带来的问题
Cisp-pte practice explanation
Use dumping to back up tidb cluster data to S3 compatible storage
根据csv文件某一列字符串中某个数字排序
Tidb backup and recovery introduction
Is it safe to open an account in Zheshang futures?