当前位置:网站首页>EVM proof in appliedzkp zkevm (11)
EVM proof in appliedzkp zkevm (11)
2022-07-04 04:58:00 【mutourend】
1. introduction
EVM Proof Used to prove :
- state trie root The change is correct , By verifying that the transactions contained in a block have correct execution results .
EVM circuit Will be re implemented EVM, But it is verified from the perspective of verification , That means ,Prover Can help provide clues , As long as these clues do not contradict the results . Such as ,Prover Can provide information about call Whether or not to revert A clue to , Or something opcode Will you encounter the wrong clue , And then the EVM circuit It can be verified that the execution result is correct .
Transactions contained within a block can be simple ether transfers、contraction creation or contract interactions, Because every transaction has variable execution trace, Cannot use fixed circuit layout To verify specific region Specific to logic, So , We need to a chip To verify all possible logics, The chip Repeat yourself to achieve the whole circuit.
2. Custom type
The following types are customized for clues :
| Name | Type | Description |
|---|---|---|
GlobalCounter | int | Order of random access to BusMapping, which should be in sequence |
BusMapping | List[Tuple[int, ...]] | List of random read-write access data in sequence with GlobalCounter as index |
3. Random Accessible Data
EVM The parser can do any random access to data Similar to account balance、account storage、stack in current scope、memeory in current scope, But for EVM circuit Come on , It is difficult to track these data to ensure the real-time consistency of these data .
therefore ,EVM proof have State proof To provide a valid list of random read-write access records indexed by the GlobalCounter as a lookup table to do random access at any moment.
take random read-write access records list be called BusMapping, Because its function is similar to that in computers bus, Used to transmit data between different parts . Allied ,read-only The data to random access The way is from lookup table load .
| Target | Index | Accessible By | Description |
|---|---|---|---|
Block | {enum} | Read | Block constant decided before executing the block |
BlockHash | {index} | Read | Previous 256 block hashes as a encoded word array |
AccountNonce | {address} | Read, Write | Account’s nonce |
AccountBalance | {address} | Read, Write | Account’s balance |
AccountCodeHash | {address} | Read, Write | Account’s code hash |
AccountStorage | {address}.{key} | Read, Write | Account’s storage as a key-value mapping |
Code | {hash}.{index} | Read | Executed code as a byte array |
Call | {id}.{enum} | Read | Call’s context decided by caller (includes EOA and internal calls) |
CallCalldata | {id}.{index} | Read | Call’s calldata as a byte array (only for EOA calls) |
CallSignature | {id}.{index} | Read | Call’s signature as a byte array (only for EOA calls) |
CallState | {id}.{enum} | Read, Write | Call’s internal state |
CallStateStack | {id}.{index} | Read, Write | Call’s stack as a encoded word array |
CallStateMemory | {id}.{index} | Read, Write | Call’s memory as a byte array |
3. Circuit Constraints
This repetition chip have 2 individual main states, A call initializes , Another one for bytecode execution.
Reference material
[1] EVM Proof
边栏推荐
- Operate the server remotely more gracefully: the practice of paramiko Library
- RPC - gRPC简单的demo - 学习/实践
- 中科磐云—模块A 基础设施设置与安全加固 评分标准
- 红队视角下的防御体系突破之第二篇案例分析
- 加密和解密
- Dp83848+ network cable hot plug
- CRS-4013: This command is not supported in a single-node configuration.
- Fault analysis | mongodb 5.0 reports an error, and the legal instruction solves it
- 中科磐云—D模块解析以及评分标准
- YoloV6实战:手把手教你使用Yolov6进行物体检测(附数据集)
猜你喜欢

Use units of measure in your code for a better life

电子元器件商城与数据手册下载网站汇总
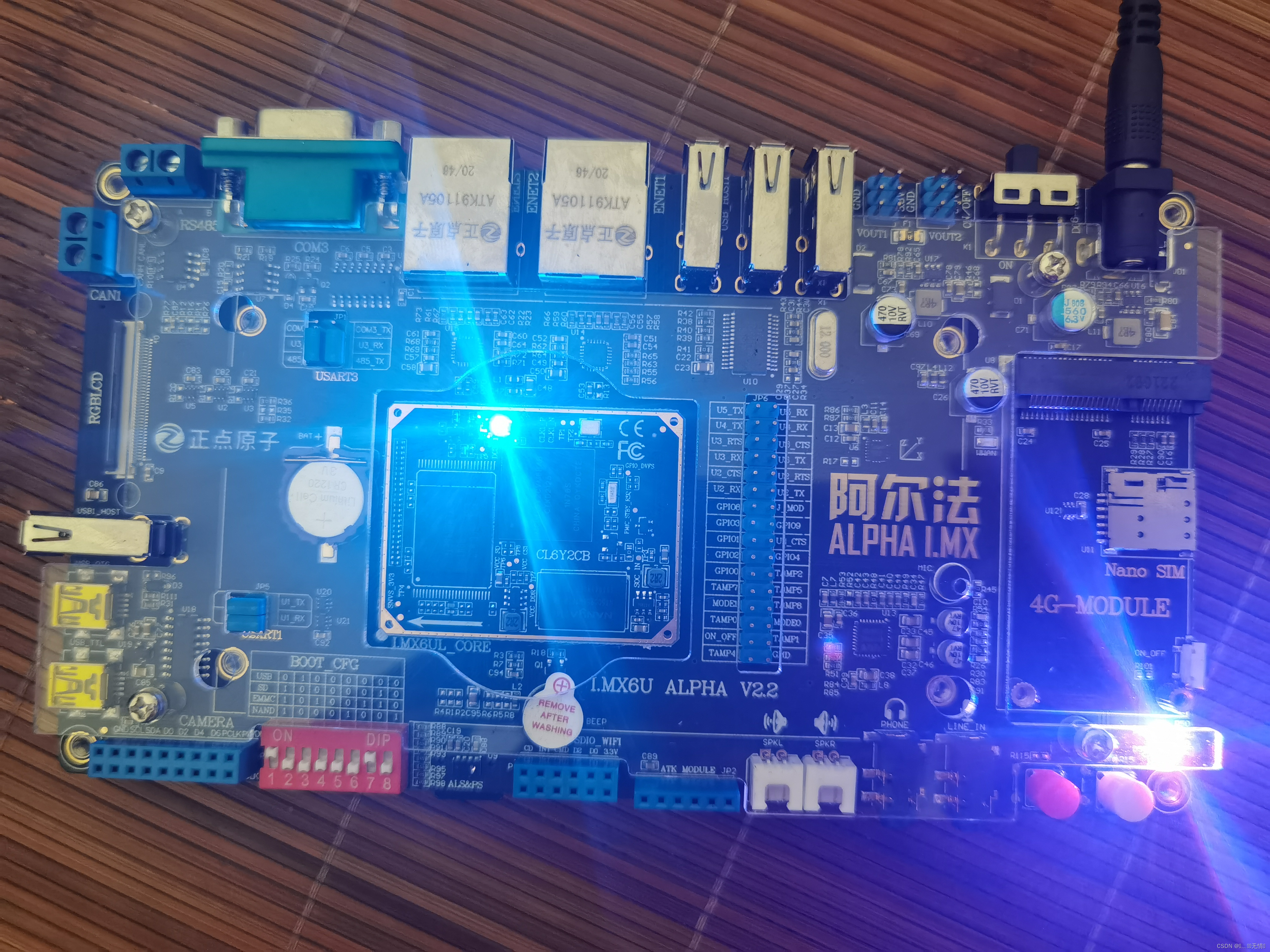
1. Mx6u-alpha development board (LED drive experiment in C language version)
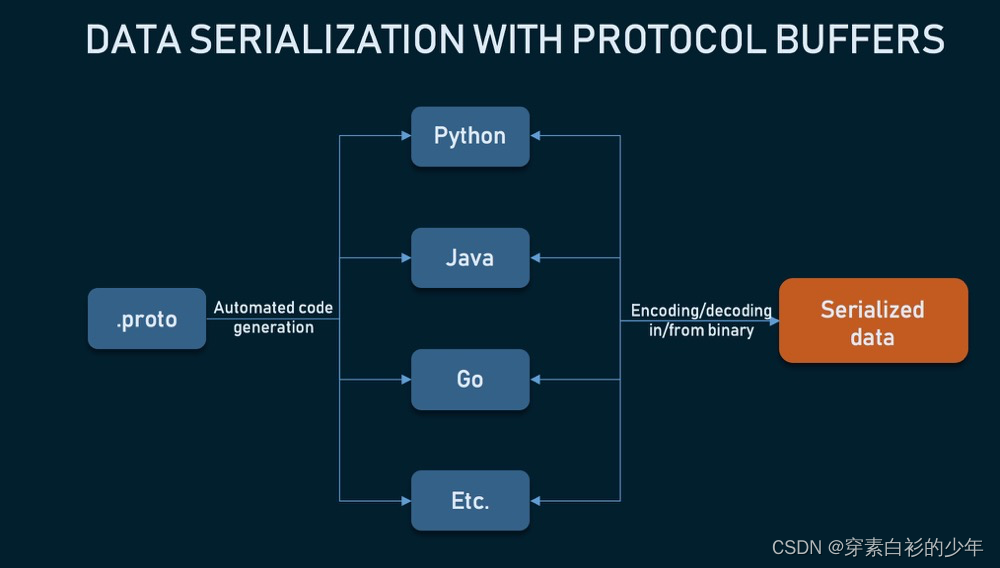
RPC - gRPC简单的demo - 学习/实践

海力士EMMC5.0及5.1系列对比详解
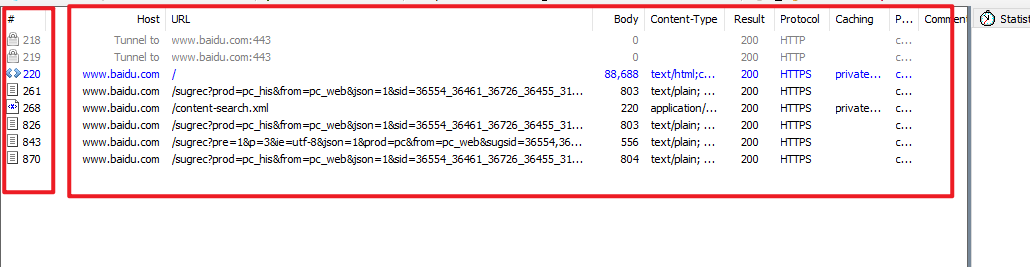
Capturing and sorting out external Fiddler -- Conversation bar and filter

郑州正清园文化传播有限公司:针对小企业的7种营销技巧

2022年6月总结
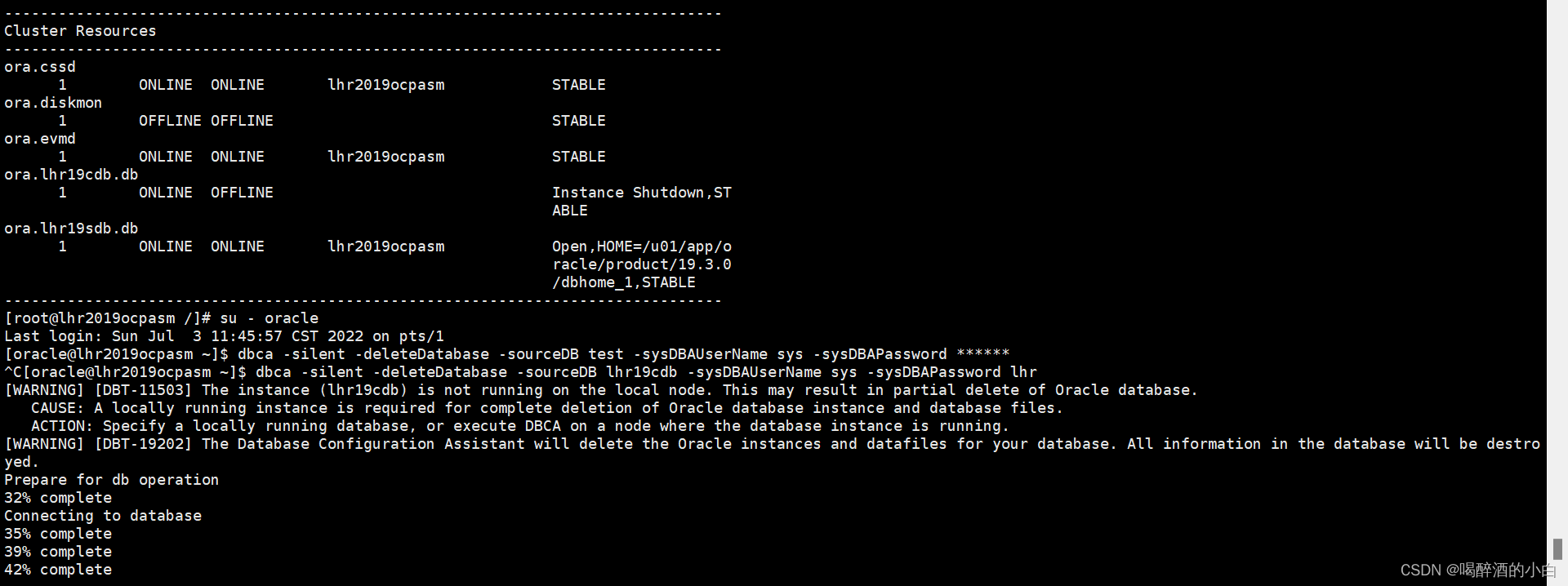
Can closed data be deleted by DBCA? can

Flutter ‘/usr/lib/libswiftCore.dylib‘ (no such file)
随机推荐
【Go】数据库框架gorm
Error response from daemon: You cannot remove a running container 8d6f0d2850250627cd6c2acb2497002fc3
RPC Technology
[wechat applet] good looking carousel map component
附件四:攻击方评分标准.docx
网络设备应急响应指南
6-5 vulnerability exploitation SSH weak password cracking and utilization
Deep understanding of redis -- bloomfilter
YoloV6实战:手把手教你使用Yolov6进行物体检测(附数据集)
Deep parsing structured exception handling (SEH) - by Matt Pietrek
中科磐云—D模块解析以及评分标准
每日刷题记录 (十二)
ADB tools
【MATLAB】MATLAB 仿真模拟调制系统 — VSB 系统
Annex III: scoring standard of the defender docx
MySQL JDBC programming
红队视角下的防御体系突破之第一篇介绍、阶段、方法
中科磐云—2022广西逆向解析思路
GUI application: socket network chat room
QT qtableview data column width adaptation