当前位置:网站首页>How to execute an SQL statement in MySQL
How to execute an SQL statement in MySQL
2022-07-06 04:00:00 【ajdhfla】
1.mysql Basic framework :
The connector : Identity authentication and authority related ( Sign in MySQL When ).
The query cache : When executing a query statement , The cache will be queried first (MySQL 8.0 Remove after version , Because this function is not very practical ).
analyzer : If you don't hit the cache ,SQL The statement goes through the parser , The analyzer says that we should first look at your SQL What is the statement , Check your SQL Is the sentence syntax correct .
Optimizer : according to MySQL Think the best plan to carry out .
actuator : Execute statement , Then return the data from the storage engine .
Simply speaking MySQL It is mainly divided into Server Layer and storage engine layer :
Server layer : Mainly including connectors 、 The query cache 、 analyzer 、 Optimizer 、 Actuators etc. , All cross-storage engine functionality is implemented in this layer , Like stored procedures 、 trigger 、 View , Functions, etc , There is also a general log module binglog Log module .
Storage engine : Mainly responsible for data storage and reading , Using a plug-in architecture that can be replaced , Support InnoDB、MyISAM、Memory Wait for multiple storage engines , among InnoDB The engine has its own logging module redolog modular . Now the most commonly used storage engine is InnoDB, It is from MySQL 5.5.5 The version has been used as the default storage engine from the beginning .
2. analysis of sentences :
2.1 Query statement
sql It can be divided into two kinds , One is a query , One is updating ( increase , to update , Delete ). Let's analyze the query statement first , The statement is as follows :
select * from tb_student A where A.age='18' and A.name=' Zhang San ';
Combined with the above instructions , Let's analyze the execution flow of this statement :
First check whether the statement has permission , If you don't have permission , Return error message directly , If you have authority , stay MySQL8.0 Version before , The cache will be queried first , With this sql Statement for key Query in memory for results , If there is a direct cache , without , Perform the next step .
Lexical analysis by Analyzer , extract sql Key elements of the statement , For example, extracting the above statement is a query select, Extract the table name to be queried as tb_student, Need to query all columns , The query criteria are id='1'. And then judge this sql Is there any grammatical error in the statement , For example, whether the keywords are correct, etc , If the check is OK, go to the next step .
Next, the optimizer determines the execution scheme , above sql sentence , There can be two implementation options :
a. First look up the names in the student list “ Zhang San ” Of the students , Then determine if the age is 18. b. First find out the age of the students 18 Year old student , Then check the name as “ Zhang San ” Of the students .
Then the optimizer selects the best execution efficiency scheme according to its own optimization algorithm ( Optimizer thinks , Sometimes it's not the best ). After confirming the implementation plan, we are ready to start the implementation .
Verify authority , If you don't have permission, an error message will be returned , If you have permission, you will call the database engine interface , Returns the execution result of the engine .
2.2 UPDATE statement
The above is a query sql The implementation process of , So let's see how an update statement is executed ?sql The statement is as follows :
update tb_student A set A.age='19' where A.name=' Zhang San ';
This statement will basically follow the flow of the previous query , Just keep a log when updating , This will introduce the log module ,MySQL Built in log module binlog( Archive log ) , All storage engines can use , That we use a lot InnoDB The engine also comes with a log module redo log( Redo log ), We'll take InnoDB Mode to explore the execution process of this statement . The process is as follows :
First, query the data of Zhang San , If you have a cache , Cache is also used .
Then get the query statement , hold age Change it to 19, Then invoke the engine. API Interface , Write this line of data ,InnoDB The engine keeps the data in memory , Simultaneous recording redo log, here redo log Get into prepare state , Then tell the actuator , Execution completed , Ready to submit .
After the actuator receives the notice, it records binlog, Then call the engine interface , Submit redo log Is submitted status .
Update complete .
Why use two log modules :
This is because in the beginning MySQL Not with InnoDB engine ( InnoDB The engine is inserted by other companies in the form of plug-ins MySQL Of ) ,MySQL The engine is MyISAM, But we know that redo log yes InnoDB Engine specific , No other storage engine , This leads to the absence of crash-safe The ability of (crash-safe Even if the database is restarted abnormally , No records submitted before will be lost ),binlog Logs can only be used to archive .
This is not to say that only one log module is not allowed , It's just InnoDB The engine just goes through redo log To support affairs . that , Another student will ask , I use two log modules , But don't be so complicated , Why? redo log To introduce prepare Pre submission status ? Here we use the counter evidence method to explain why we should do this ?
First write redo log Submit directly , Then write binlog, Hypothesis complete redo log after , The machine hangs up ,binlog The log was not written , So after the machine restarts , This machine will go through redo log Restore data , But at this point bingog This data is not recorded , When the machine is backed up later , You lose this piece of data , At the same time, master-slave synchronization will also lose this piece of data .
First write binlog, Then write redo log, Let's say it's done binlog, The machine rebooted unexpectedly , Because there is no redo log, This record cannot be recovered by this computer , however binlog There's another record , So the same thing as above , There will be data inconsistencies .
If the redo log The two-stage submission is not the same , finish writing sth. binglog after , Then submit redo log Will prevent the above problems , So as to ensure the consistency of data . So here comes the question , Is there an extreme situation ? hypothesis redo log In pre commit state ,binglog It's finished , What happens when an abnormal restart occurs ? This depends on MySQL The processing mechanism of ,MySQL The process is as follows :
Judge redo log Is it complete , If the judgment is complete , Submit immediately .
If redo log It's just withholding but not commit state , This is the time to judge binlog Is it complete , If it's complete, submit redo log, Rollback transaction if incomplete .
This solves the problem of data consistency .
边栏推荐
- Quick sort function in C language -- qsort
- ESP32_ FreeRTOS_ Arduino_ 1_ Create task
- Serial port-rs232-rs485-ttl
- How does technology have the ability to solve problems perfectly
- The Research Report "2022 RPA supplier strength matrix analysis of China's banking industry" was officially launched
- 【leetcode】22. bracket-generating
- User perceived monitoring experience
- MySQL reads missing data from a table in a continuous period of time
- [analysis of variance] single factor analysis and multi factor analysis
- KS003基于JSP和Servlet实现的商城系统
猜你喜欢

C mouse event and keyboard event of C (XXVIII)
Blue Bridge Cup - day of week
![[disassembly] a visual air fryer. By the way, analyze the internal circuit](/img/73/29553d60f47deadfff420be40b7f77.jpg)
[disassembly] a visual air fryer. By the way, analyze the internal circuit

Plus d'un milliard d'utilisateurs de grandes entreprises comme Facebook ont été compromis, il est temps de se concentrer sur le did
![[optimization model] Monte Carlo method of optimization calculation](/img/e6/2865806ffbbfaa8cc07ebf625fcde6.jpg)
[optimization model] Monte Carlo method of optimization calculation
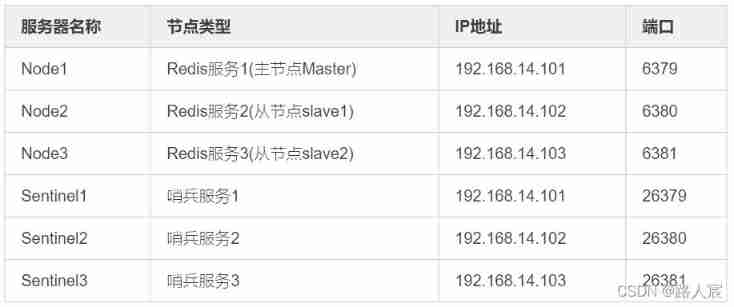
Redis (replicate dictionary server) cache
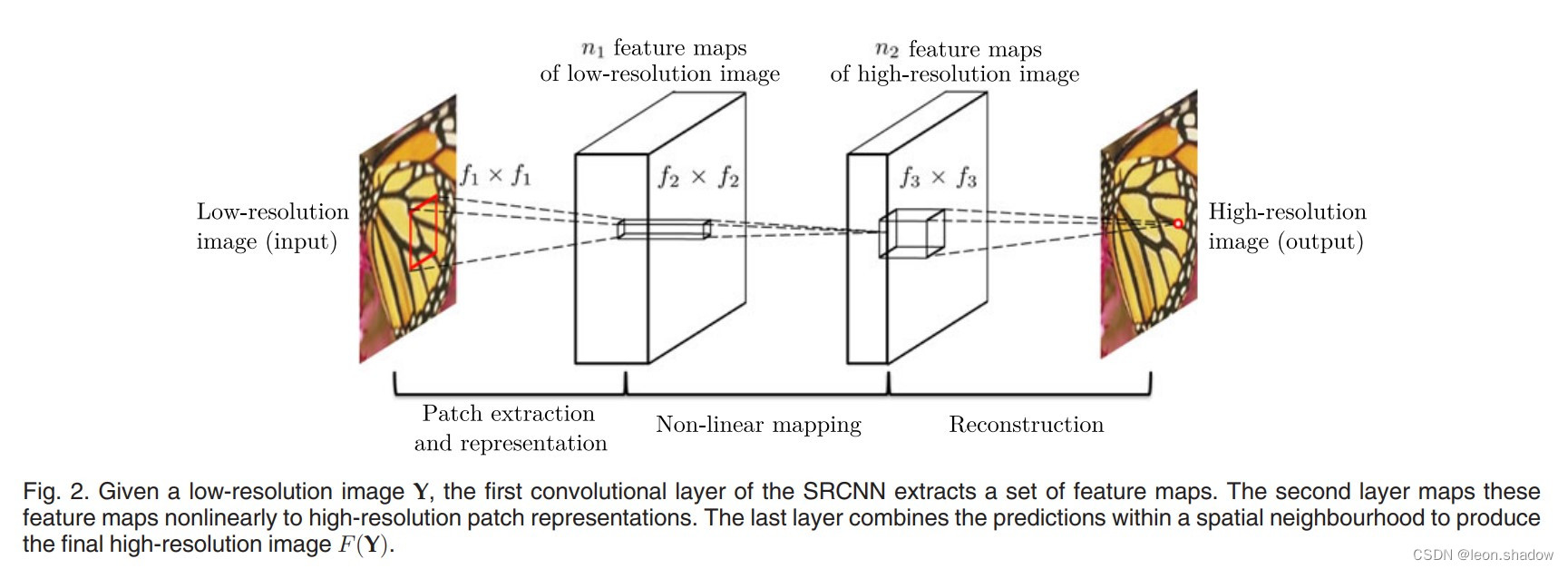
Image super resolution using deep revolutionary networks (srcnn) interpretation and Implementation
![[introduction to Django] 11 web page associated MySQL single field table (add, modify, delete)](/img/8a/068faf3e8de642c9e3c4118e6084aa.jpg)
[introduction to Django] 11 web page associated MySQL single field table (add, modify, delete)
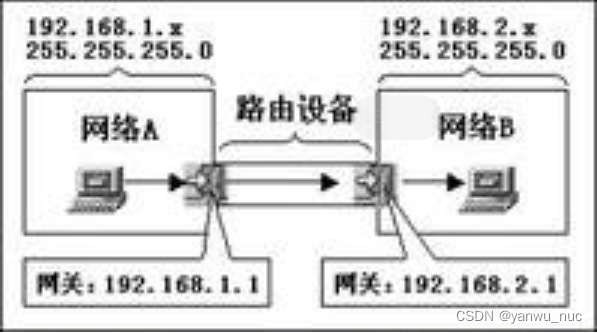
TCP/IP协议里面的网关地址和ip地址有什么区别?
在字节做测试5年,7月无情被辞,想给划水的兄弟提个醒
随机推荐
C#(三十)之C#comboBox ListView treeView
On Data Mining
math_ Derivative function derivation of limit & differential & derivative & derivative / logarithmic function (derivative definition limit method) / derivative formula derivation of exponential functi
[001] [stm32] how to download STM32 original factory data
Ipv4中的A 、B、C类网络及子网掩码
Basic knowledge of binary tree, BFC, DFS
Ks008 SSM based press release system
Thread sleep, thread sleep application scenarios
SSTI template injection explanation and real problem practice
[PSO] Based on PSO particle swarm optimization, matlab simulation of the calculation of the lowest transportation cost of goods at material points, including transportation costs, agent conversion cos
Use js to complete an LRU cache
asp. Core is compatible with both JWT authentication and cookies authentication
Proof of Stirling formula
Ybtoj coloring plan [tree chain dissection, segment tree, tarjan]
Database, relational database and NoSQL non relational database
math_极限&微分&导数&微商/对数函数的导函数推导(导数定义极限法)/指数函数求导公式推导(反函数求导法则/对数求导法)
Error 1045 (28000): access denied for user 'root' @ 'localhost' (using password: no/yes
Record the pit of NETCORE's memory surge
Facebook等大厂超十亿用户数据遭泄露,早该关注DID了
ESP32_ FreeRTOS_ Arduino_ 1_ Create task