当前位置:网站首页>Describe the process of key exchange
Describe the process of key exchange
2022-07-06 18:39:00 【JohnnyFang】
key exchange (IKE,Internet Key Exchange ) There are mainly two ways to implement , One is public key encryption , One is to make use of DH Algorithm encryption for key exchange .
- Public key encryption
1.1 Symmetric encryption
Suppose there are two people Alice and Bob,Alice As the sender, it is necessary to transmit data to the receiver Bob, The two directly discussed a secret key to encrypt the data ,Bob After receiving it, you can directly open the original data by using the negotiated secret key ( Here's the picture ).
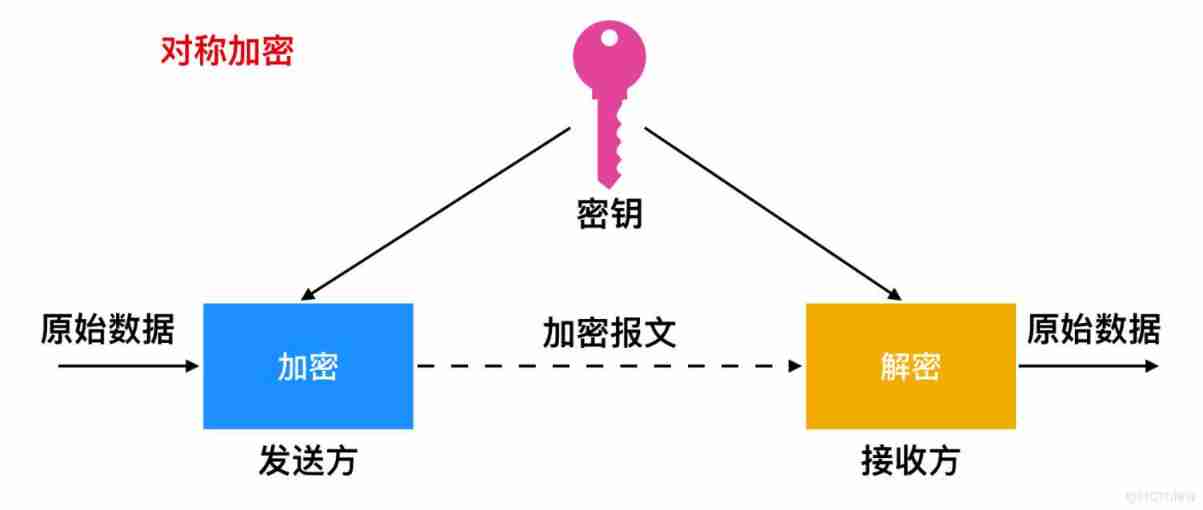
Of course, this is the ideal state , If someone else gets the secret key , And intercepted the data , You can also view data , Public key exchange can be improved on this basis .
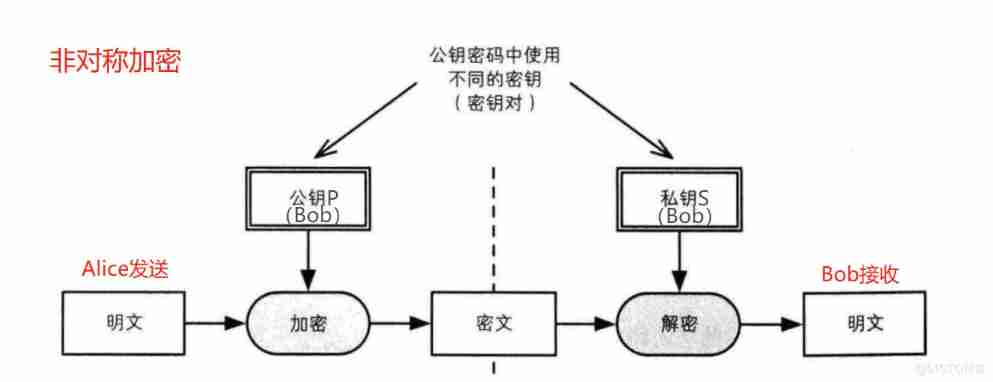
1.2 Asymmetric encryption
Public key exchange is realized by asymmetric encryption , Both sender and receiver have their own public and private keys , And use in pairs . We still use Alice towards Bob Take data transmission as an example ,Bob The public key and private key of are P and S,Alice Before sending the data , utilize Bob The public key P To encrypt the data , And to decrypt , Only Bob The private key S To open , Even if others intercept the data , Can't view it ( Here's the picture ).
1.3 Asymmetric encryption realizes digital signature
Because the public key is public ,Alice You can give Bob To transmit data , Others can also , To ensure that the data received by the receiver is transmitted by the agreed sender , The form of digital signature can be adopted on the basis of asymmetric encryption .
Because the secret key is used in pairs , Public key disclosure , And the secret key is confidential ,Alice You can encrypt data with your private key , Others intercepted it and don't know who sent it , and Bob know Alice There is an encrypted data transmission , use Alice Decrypt the public key to view the data ( Here's the picture ).
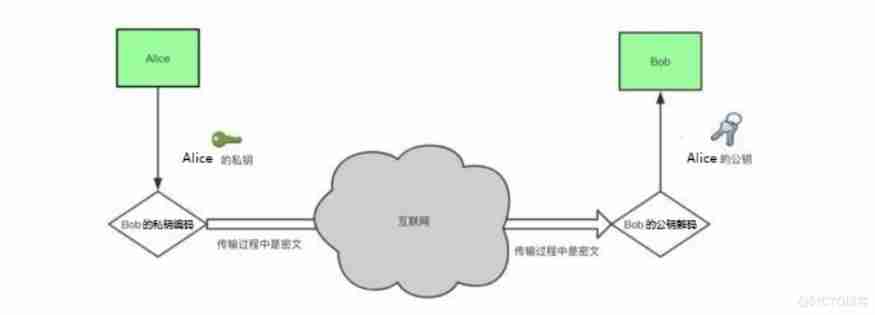
Given the complexity of the transmission environment on the Internet , Public key encryption will also be used RSA Algorithm 、DSA Algorithm 、 Combination of hash algorithm and Algorithm , To ensure the reliability of data encryption transmission .
- DH Algorithm encryption
In addition to the form of public key encryption to achieve key exchange , You can also use DH Algorithm to achieve encryption .
2.1 DH Introduction to algorithm encryption
①DH Secret key exchange by Whitfield · Di fe (Bailey Whitfield Diffie) Martin · Herman (Martin Edward Hellman) stay 1976 In published .
② It's a security protocol , Let both parties establish a key through an insecure channel without any prior information of the other party , This key is generally used as “ Symmetric encryption ” The key is used by both parties in subsequent data transmission .
③DH The mathematical principle is base Discrete logarithm problem , There are asymmetric encryption algorithms that do similar things , Such as :RSA.
④ It is widely used , stay SSH、VPN、Https... All have applications , Modern mi Code cornerstone .
2.2 DH Implementation process
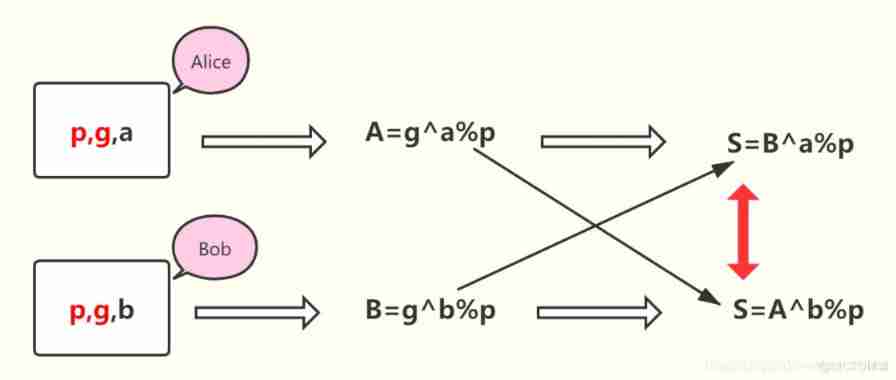
With Alice and Bob For example :
First step :Alice and Bob Negotiate to generate a public integer g And large prime numbers p;
The second step : Privacy data exchange
①Alice Generate privacy data a(a<p), calculated g^a%p, Send to Bob
②Bob Generate privacy data b(b<p), calculated g^b%p, Send to Alice
The third step : Realize secret key exchange
①Alice calculated [(g^b%p)^a]%p = g^ab%p, Generate as key
②Bob calculated [(g^a%p)^b]%p = g^ab%p, Generate as key
At the third step , We can see ,Alice and Bob The secret key obtained is the same , All are g^ab%p, Thus realizing the exchange of secret keys . The implementation process is shown in the following figure :
2.3 DH Example of algorithm encryption
hypothesis Alice and Bob Encrypt the transmitted data , The agreed integer g by 23, Large prime number p by 17,Alice and Bob The privacy data generated respectively are 6 and 11, namely g=23,p=17,a=6,b=11.
① Privacy data exchange link
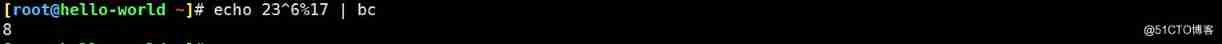
Alice Send to Bob For the g^a%p=23^6%17=8( Here's the picture ).
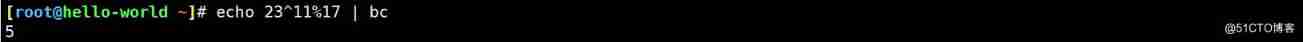
Bob Send to Alice For the g^b%p=23^11%17=5( Here's the picture ).
② Realize secret key exchange
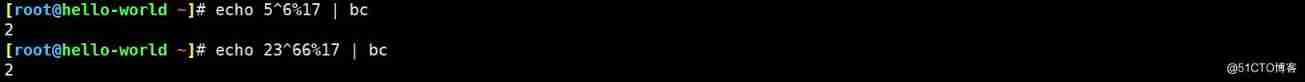
Alice Calculation [(g^b%p)^a]%p =5^6%17=2,g^ab%p=23^66%17=2, These two results are the same , If Bob The calculated result is also 2, It shows that secret key exchange is realized ( Here's the picture ).
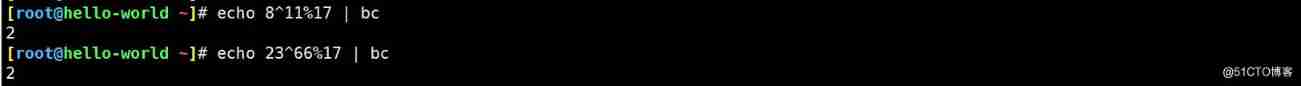
Bob Calculation [(g^a%p)^b]%p = 8^11%17=2=g^ab%p=23^66%17=2( Here's the picture ).
Here we are ,Alice and Bob It forms a common secret key 2, That is to realize the exchange of secret keys .
Of course ,DH Algorithm encryption also has its own lou hole , For example, private data of both parties a and b Will be discarded , The existence of too long will lead to the risk of leakage . meanwhile , because DH In the transport p、g There is no authentication , So there is an opportunity to be implemented as a middleman gong blow , Replace the data transmitted by both parties . Use some CA Certificates and security protocols , It can effectively enhance the safety and reliability of communication or transmission , However, I won't describe more in this article .
边栏推荐
- Epoll () whether it involves wait queue analysis
- UFIDA OA vulnerability learning - ncfindweb directory traversal vulnerability
- Five data structures of redis
- 10、 Process management
- ORACLE进阶(四)表连接讲解
- 解读云原生技术
- [sword finger offer] 60 Points of N dice
- Cobra quick start - designed for command line programs
- Excellent open source fonts for programmers
- Coco2017 dataset usage (brief introduction)
猜你喜欢
287. Find duplicates
Splay
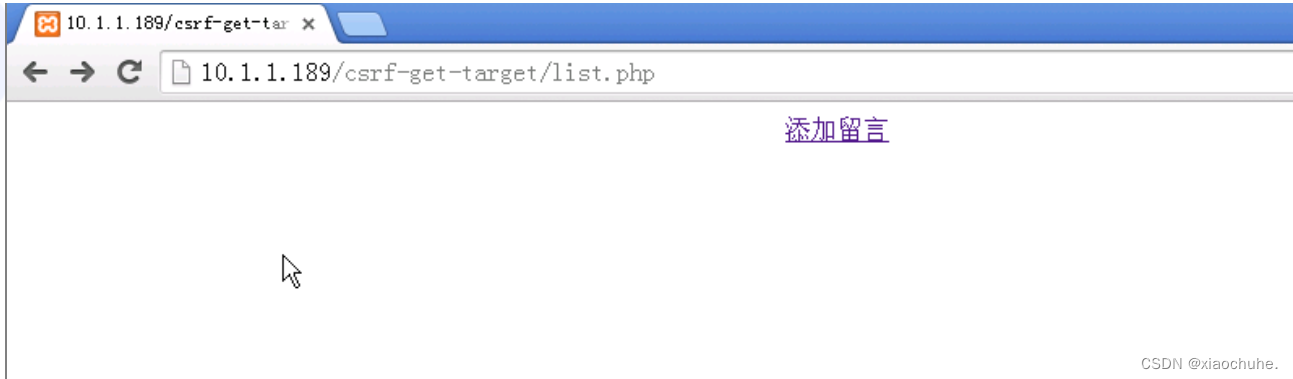
CSRF漏洞分析
![Jerry is the custom background specified by the currently used dial enable [chapter]](/img/32/6c22033bda8ff1b53993bacef254cd.jpg)
Jerry is the custom background specified by the currently used dial enable [chapter]
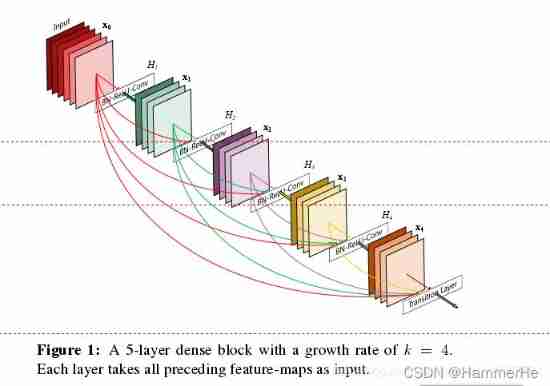
Medical image segmentation

被疫情占据的上半年,你还好么?| 2022年中总结
Distiller les connaissances du modèle interactif! L'Université de technologie de Chine & meituan propose Virt, qui a à la fois l'efficacité du modèle à deux tours et la performance du modèle interacti
Summary of performance knowledge points
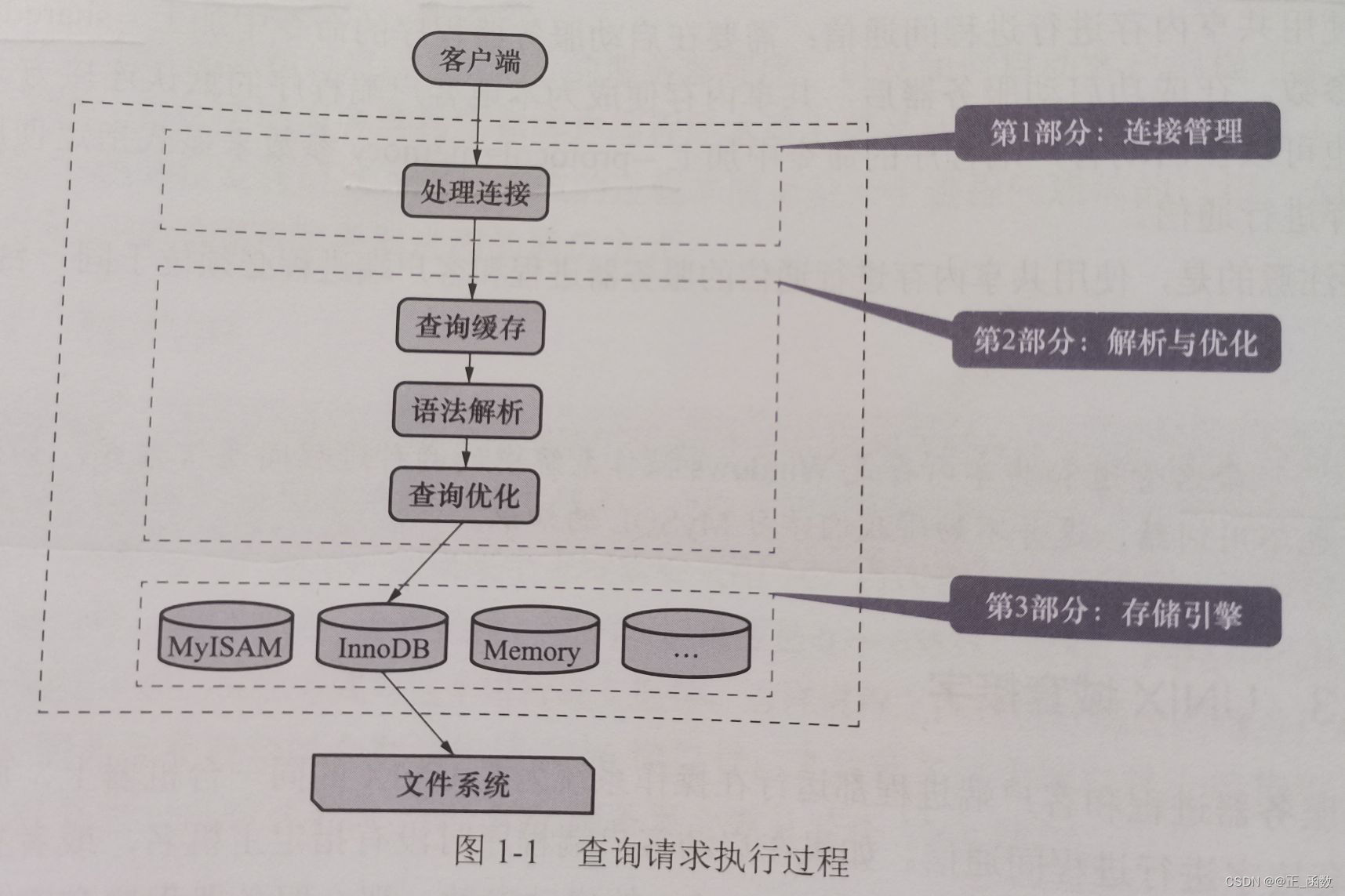
MySQL查询请求的执行过程——底层原理
Excellent open source fonts for programmers
随机推荐
视频化全链路智能上云?一文详解什么是阿里云视频云「智能媒体生产」
Maixll-Dock 摄像头使用
Stm32+esp8266+mqtt protocol connects onenet IOT platform
Interpreting cloud native technology
Execution process of MySQL query request - underlying principle
Transport layer congestion control - slow start and congestion avoidance, fast retransmission, fast recovery
复现Thinkphp 2.x 任意代码执行漏洞
STM32+HC05串口蓝牙设计简易的蓝牙音箱
用友OA漏洞学习——NCFindWeb 目录遍历漏洞
Cobra 快速入门 - 专为命令行程序而生
Specify flume introduction, installation and configuration
CRMEB 商城系统如何助力营销?
Example of implementing web server with stm32+enc28j60+uip protocol stack
node の SQLite
文档编辑之markdown语法(typora)
Five data structures of redis
Grafana 9.0 is officially released! It's the strongest!
SQL injection - access injection, access offset injection
爬虫玩得好,牢饭吃到饱?这3条底线千万不能碰!
Easy to use PDF to SVG program