当前位置:网站首页>Basic concept and usage of redis
Basic concept and usage of redis
2022-07-05 00:29:00 【liangzai2048】
List of articles
- Redis
- Redis What is it?
- NoSQL classification
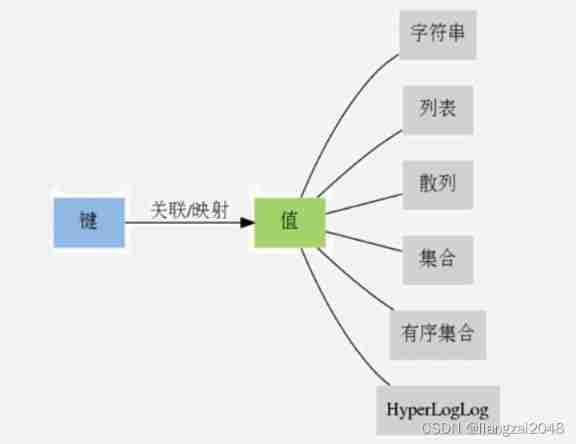
- Redis Data model
- key Key
- String
- command
- Get help after logging in to the client
- Help @string
- Set string value
- Be overdue
- Set string values for multiple keys
- When the key doesn't exist , Set string value
- Lookup key
- step
- Bitmap bitmap
- Set the value of a bit
- Get the value of a bit
- Returns the specified value 0 perhaps 1 The position of the first occurrence on the specified interval
- Bit operation
- Statistics means that the value on the positioning interval is 1 The number of
- Redis Binary bit of
- Log in to different libraries
- Clear current data
- Clear all data in the library
- Statistics of the maximum number of website users ( Active users )
- Count the active users of the website by day
Redis
Redis What is it?
- Open source (BSD agreement ), Use ANSI C To write , Memory based and persistent , High performance Key-Value Of NoSQL database .
- Support data structure type rich , Like a character string (strings), hash (hashes), list (lists), aggregate (sets), Ordered set (sorted sets) And scope query , bitmaps, hyperloglogs and Geographical space (geospatial) Index radius query .
- Rich client support for mainstream languages ,C、C++、Python、Erlang、R、C#、Java、PHP、Objective-C、Perl、Ruby、Scala、Go、JavaScript.
- purpose : cache 、 database ( Microblogging )、 Message middleware ( Microblogging )
- Official website :https://redis.io
NoSQL classification

Redis Data model
key Key
- Redis key Values are binary safe , This means that any binary sequence can be used as key value , From the shape as ”foo” A simple string to a JPEG The content of the document can be . Empty strings are also valid key value .
- Key Value principle
- The key does not need to be too long , Memory consumption , And the calculation cost of finding such key value in the data is higher
- The key value should not be too short , Poor readability
String
- String is one of the most basic Redis Value type .Redis Strings are binary safe , This means a Redis A string can contain any type of data
- for example : a sheet JPEG Format picture or a serialized Ruby object
- A string type value can store up to 512M The contents of bytes
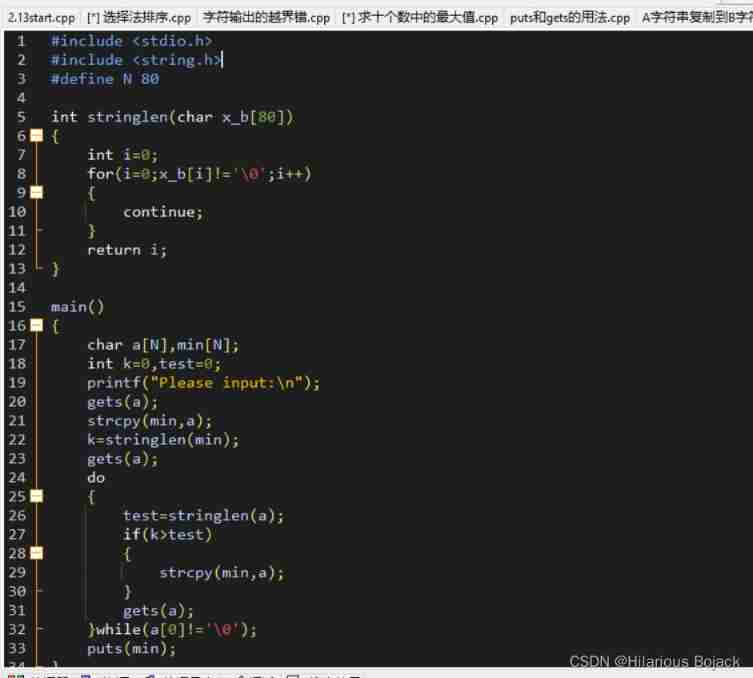
command
Get help after logging in to the client
- Help
- Help
- Help set
- Help @string
Help
help
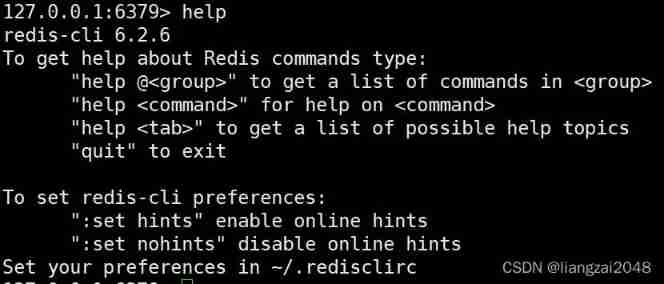
Help set
help set

Help @string
help @string

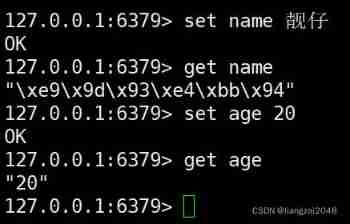
Set string value
- SET key value [EX seconds] [PX milliseconds] [NX|XX]
- EX Set expiration time , second , Equate to SETEX key seconds value
- PX Set expiration time , millisecond , Equate to PSETEX key milliseconds value
- NX The key doesn't exist , To set , Equate to SETNX key value
- XX When the bond exists , To set
Here we mainly know CRUD( Add, delete, change and delete )
set K V
#set K V
set name handsome young man
# check The result here is 16 Binary stored
get name
set age 20
get age
Be overdue
- Redis You can give to Key Set a lifetime ( Seconds or milliseconds ), When this time is reached , These key values will be automatically deleted
- Set how many seconds or milliseconds to expire
- EXPIRE key seconds
- PEXPIRE key milliseconds
- Set to specify Unix Time stamp expired
- EXPIREAT key timestamp
- PEXPIREAT key milliseconds-timestamp
- Delete expired
- PERSIST key
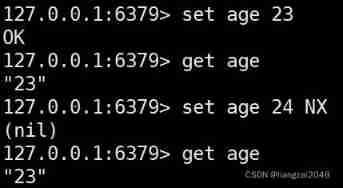
set K V NX
NX The key doesn't exist , To set , Equate to SETNX key value
set score 100 NX
get score

set age 23
get age
set age 24 NX
get age
set K V [EX|PX]
#EX In seconds , It means how many seconds you only survive ,5 The value cannot be obtained after seconds
set ttl dead EX 5
get ttl
get ttl
#PX In milliseconds , It means how many milliseconds it only survives ,5000 The value cannot be obtained after milliseconds
set ttl dead PX 5000
get ttl
get ttl
get ttl
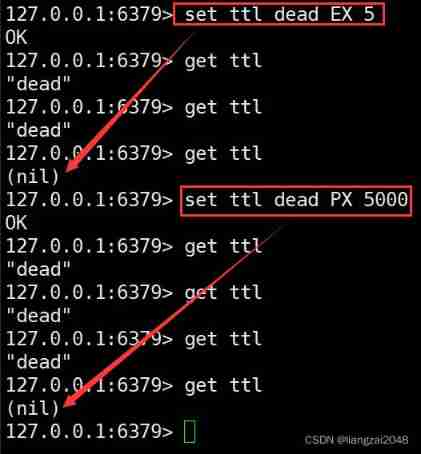
This command is suitable for hot search cache , The survival time will expire as soon as it passes , There is no need to keep this data forever
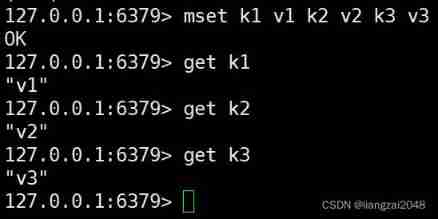
Set string values for multiple keys
- MSET key value [key value …]
mset k1 v1 k2 v2 k3 v3
get k1
get k2
get k3
When the key doesn't exist , Set string value
- MSETNX key value [key value …]
- Be careful : This is an atomic operation
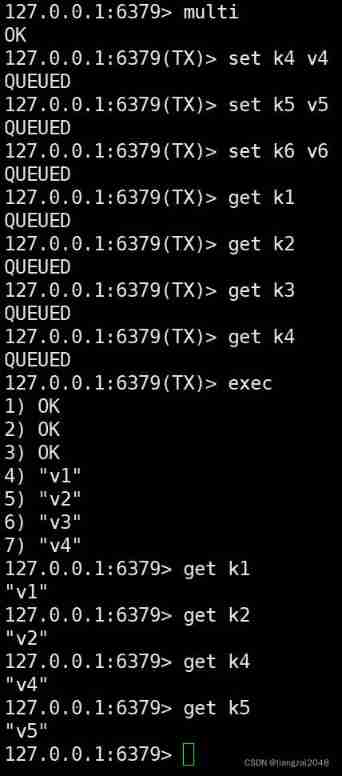
multi
set k4 v4
set k5 v5
set k6 v6
get k1
get k4
exec
get k1
get k2
get k4
get k5
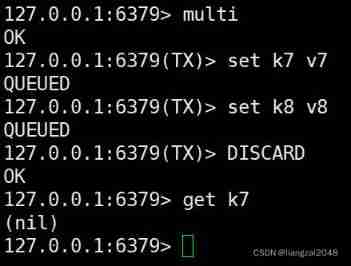
multi
set k7 v7
set k8 v8
DISCARD
get k7
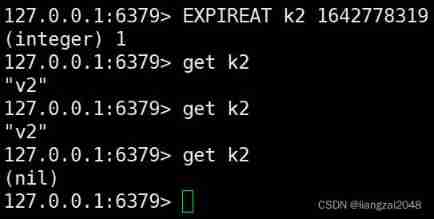
EXPIRE Be overdue
EXPIRE k4 6
get k4
# etc. 6 second
get k4

# When the timestamp reaches this time, it will expire
EXPIREAT k2 1642778319
get k2
get k2
get k2
Delete expired PERSIST KEY
expire k3 11
PERSIST k3
get k3
# Wait for the command to execute 11 Second to view the data
get k3

Time to live
- Time To Live,Key The remaining lifetime of
Check the remaining lifetime
- TTL key
- PTTL key
- key Exists but not set TTL, return -1
- key There is , But it's still alive , Returns the remaining seconds or milliseconds
- key Once existed , But it's dead , return -2(2.8 Return before version -1)
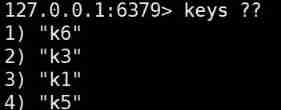
Lookup key
- KEYS pattern
pattern Value
- Any length of characters
? Any character
[] Character set , The representation can be any one of the sets
KEYS pattern
# Here is the idea of regular expressions
keys k*
keys k?
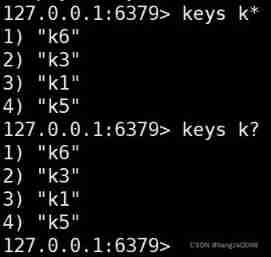
keys k[1365]

keys ??
Key type
- TYPE key
Does the key exist
- EXISTS key
The key to rename
- RENAME key newkey
- RENAMENX key newkey
Key delete
- DEL key [key …]
Get value
- GET key
Get the values of multiple given keys
- MGET key [key …]
Returns the old value and sets the new value
- GETSET key value
- If the key doesn't exist , Create and assign
String length
- STRLEN key
Append string
- APPEND key value
- If the key exists, append ; If it does not exist, it is equivalent to SET key value
Get substring
- GETRANGE key start end
- Index value from 0 Start , A negative number means counting from the right to the left of the string ,-1 Indicates that there is one character at most
Override string
- SETRANGE key offset value
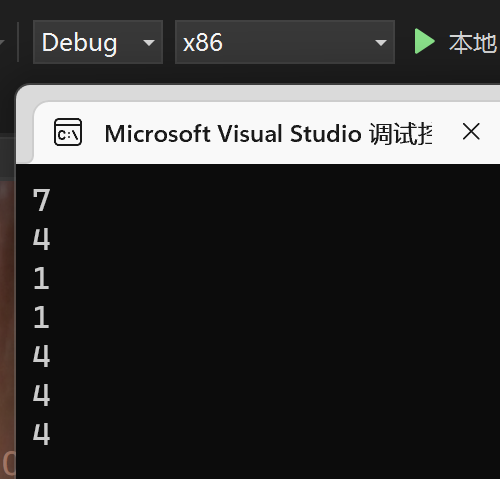
step
step 1 Increase and decrease of
- INCR key
- DECR key
- The string value will be interpreted as 64 Bit signed decimal integer to operate , The result is still converted to a string
Step increase or decrease
- INCRBY key decrement
- DECR key decrement
- The string value will be interpreted as 64 Bit signed decimal integer to operate , The result is still converted to a string
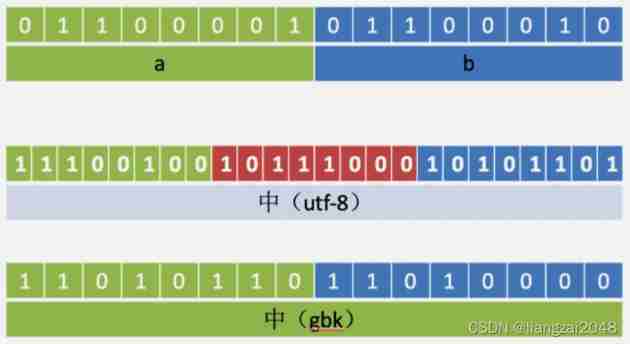
Bitmap bitmap
- Bitmaps are not really data types , It is defined in a string type
- A string type value can store up to 512M The contents of bytes
- Bit upper limit :2(9+10+10+3)=232b
Set the value of a bit
- SETBIT key offset value
- offset Offset , from 0 Start
- value Don't write , The default is 0
Get the value of a bit
- GETBIT key offset
Returns the specified value 0 perhaps 1 The position of the first occurrence on the specified interval
- BITPOS key bit [start] [end]
Bit operation
- For one or more strings that hold binary bits key Perform bit operation , And save the result to dteskey On
- operation It can be AND 、 OR 、 NOT 、 XOR Any of the four operations
- BITOP AND destkey key [key …] , To one or more key Seek logic and , And save the result to destkey
- BITOP OR destkey key [key …] , To one or more key Seek logic or , And save the result to destkey
- BITOP XOR destkey key [key …] , To one or more key Seek logical XOR , And save the result to destkey
- BITOP NOT destkey key , For given key Logic is not , And save the result to destkey
- except NOT Out of operation , Other operations can accept one or more key As input
- When BITOP When dealing with strings of different lengths , The missing part of the shorter string will be treated as 0
- Empty key It is also seen as containing 0 String sequence of
- reflection :a Bit or b What is it? ?
Statistics means that the value on the positioning interval is 1 The number of
- BITCOUNT key [start] [end]
- From left to right 0 Start , From right to left -1 Start , Pay attention to the official start、end Yes , After the test is byte
- BITCOUNT testkey 0 0 Indicates from index to 0 Bytes to index 0 Bytes , Is the statistics of the first byte
- BITCOUNT testkey 0 -1 Equate to BITCOUNT testkey
- The most common is BITCOUNT testkey
Redis Binary bit of
Log in to different libraries
- redis-cli --help
- redis-cli -n 2
Clear current data
- FLUSHDB
Clear all data in the library
- FLUSHALL
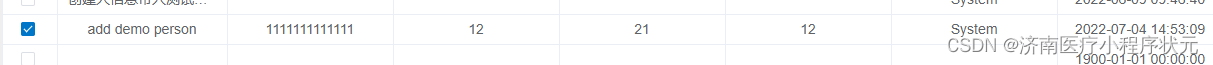
Statistics of the maximum number of website users ( Active users )
user ID by key, Days as offest, Set online to 1
ID by 500 Users of , This year's 1 Skyline 、 The first 30 Skyline
SETBIT u500 1 1
SETBIT u500 30 1
BITCOUNT u500
KYES u*
Count the active users of the website by day
Days as key, user ID by offset, Set online to 1
Find the number of active users in a period of time
SETBIT 20160602 15 1
SETBIT 20160601 123 1
SETBIT 20160606 123 1
seek 6 month 1 The day is coming 6 month 10 Active users of the day
BITOP OR 20160601-10 20160601 20160602 20160603 20160610
BITCOUNT 20160601-10
The result is 2
边栏推荐
- 公司要上监控,Zabbix 和 Prometheus 怎么选?这么选准没错!
- P4281 [ahoi2008] emergency assembly / gathering (LCA)
- 模板的进阶
- Summary of week 22-07-02
- 2022.07.03(LC_6109_知道秘密的人数)
- 业务场景功能的继续修改
- 微服务(Microservice)那点事儿
- [论文阅读] CarveMix: A Simple Data Augmentation Method for Brain Lesion Segmentation
- OpenHarmony资源管理详解
- 《论文笔记》Multi-UAV Collaborative Monocular SLAM
猜你喜欢
Learn C language from scratch day 024
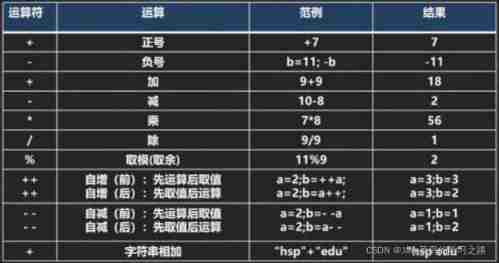
Operator explanation

Microservice
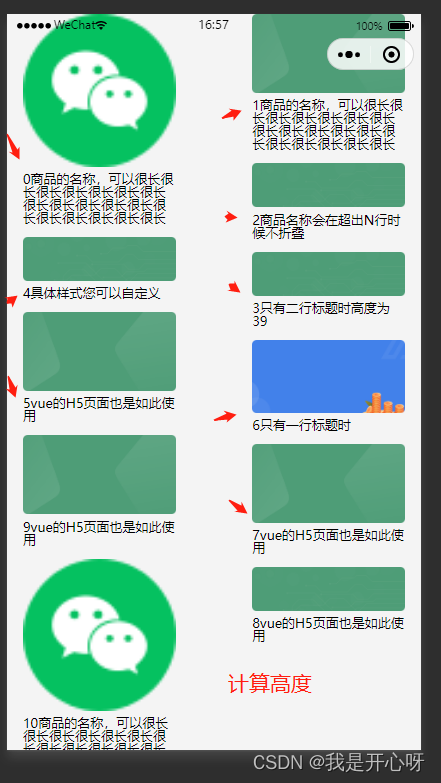
The waterfall flow layout demo2 (method 2) used by the uniapp wechat applet (copy and paste can be used without other processing)
企业公司项目开发好一部分基础功能,重要的事保存到线上第一a
【C】(笔试题)指针与数组,指针
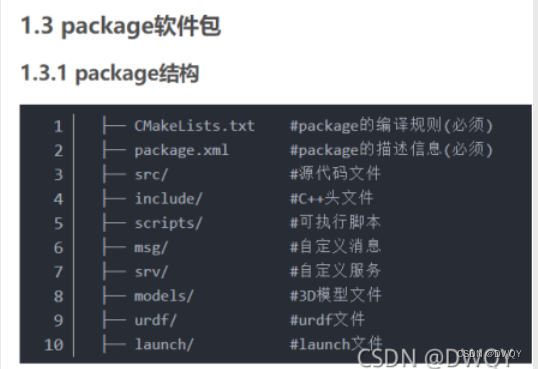
初识ROS

Identifiers and keywords

A new method for analyzing the trend chart of London Silver

公司要上监控,Zabbix 和 Prometheus 怎么选?这么选准没错!
随机推荐
Parsing of XML
Learning of basic amplification circuit
Introduction to ACM combination counting
人生无常,大肠包小肠, 这次真的可以回家看媳妇去了。。。
skimage: imread & imsave & imshow
Power operation and maintenance cloud platform: open the new mode of "unattended and few people on duty" of power system
【雅思阅读】王希伟阅读P4(matching1)
The pit of sizeof operator in C language
ORB(Oriented FAST and Rotated BRIEF)
Continuous modification of business scenario functions
Using fast parsing intranet penetration to realize zero cost self built website
Paper notes multi UAV collaborative monolithic slam
Illustrated network: what is gateway load balancing protocol GLBP?
【selenium自动化】常用注解
Five papers recommended for the new development of convolutional neural network in deep learning
Relationship between classes and objects
打新债开户注册安全吗?有没有风险的?靠谱吗?
Réseau graphique: Qu'est - ce que le Protocole d'équilibrage de charge de passerelle glbp?
巩固表达式C# 案例简单变量运算
实战模拟│JWT 登录认证