当前位置:网站首页>4. Binary search
4. Binary search
2022-07-06 13:25:00 【It's Wang Jiujiu】
Catalog
arr[]={1,2,3,4,5,6,7,8,9,10}, How to find numbers 7?
Traverse
utilize for loop , From the subscript for 0 Start looking for the number of , When the cycle reaches the seventh , Find the number 7.
When the number of numbers in the array is uncertain , Can pass sizeof To calculate .sizeof(arr) What I want is the size of the entire array ,sizeof(arr[0]) What we need is the size of the first element , Unit is byte . Divide the former by the latter , Get the number of numbers .
// Traverse
#include<stdio.h>
int main()
{
int arr[] = { 1,2,3,4,5,6,7,8,9,10 };
int input = 0;
scanf("%d", &input);
int i = 0;
int sz = sizeof(arr) / sizeof(arr[0]);
for (i = 0; i < sz; i++)
{
if (arr[i] == input)
{
printf(" eureka , Subscript to be %d\n", i);
break;
}
}
return 0;
}utilize for Loop traversal seems to solve this kind of problem , But if 1~10000 Find a certain number in , If one by one traversal seems to be a waste of time , Now let's introduce binary search .
Two points search
Binary search is also called binary search (Binary Search), It is an efficient search method . however , Half search requires that the linear table must use Sequential storage structure , And the elements in the table are arranged in order by keywords .
Be careful : The premise of binary search must be An orderly sequence of numbers !!!
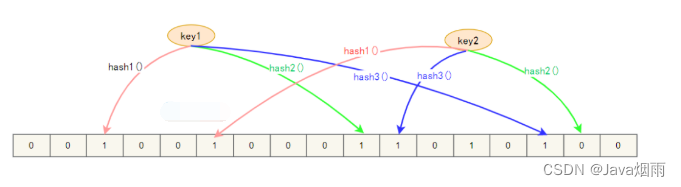
Principle demonstration
Find the subscript of the element : utilize sizeof, adopt sizeof(arr) / sizeof(arr[0]) Count the number of elements , Because the subscript of an array is from 0 At the beginning , Reduce the result by 1, Is the subscript number of the last element .
Record the median : Set two variables left、right To lock our subscript range , utilize (right-letf)/2 To find the median . Each time the range is gradually reduced by hours ,left、right The corresponding subscript range should also be updated .
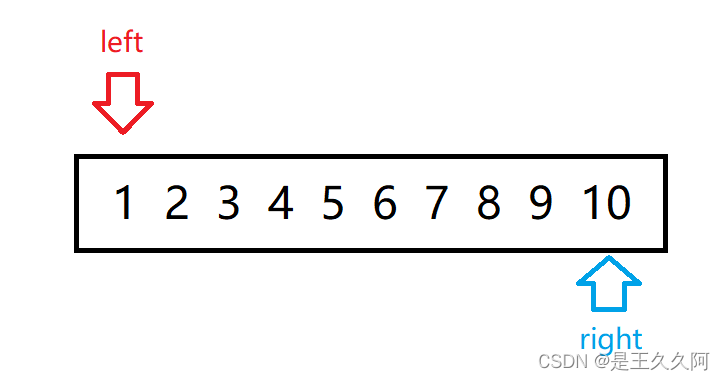
initialization : take left Lower calibration is 0,right Subscript positioning 9.
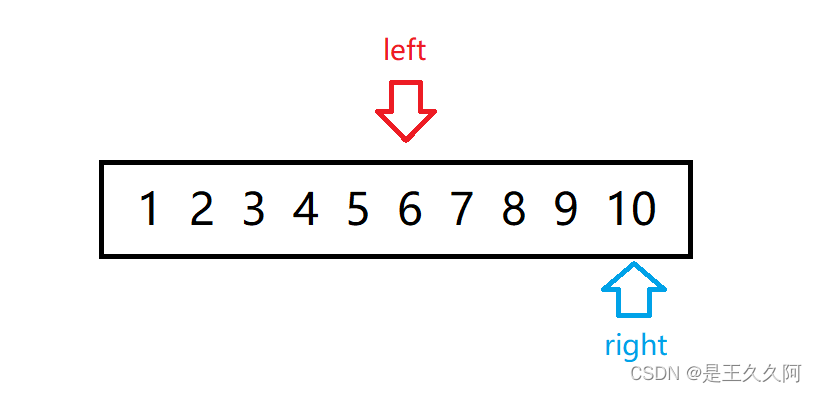
First search for : Judge left、righ The middle number of and 7 Size :5<7, take left Moved to 5+1.
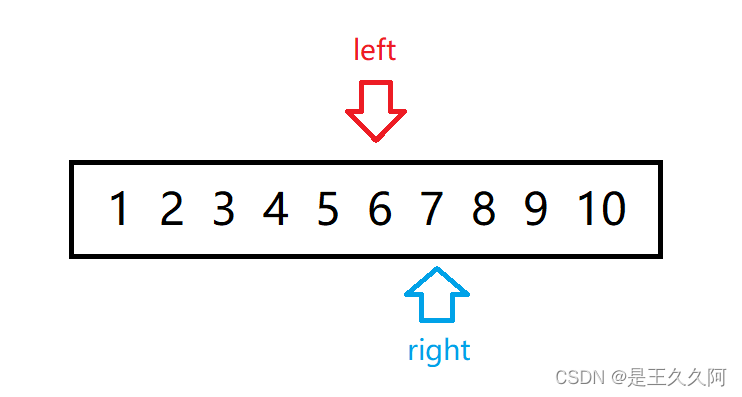
Second search : Judge left、righ The middle number of and 7 Size :8>7, take right Moved to 8-1 It's about .
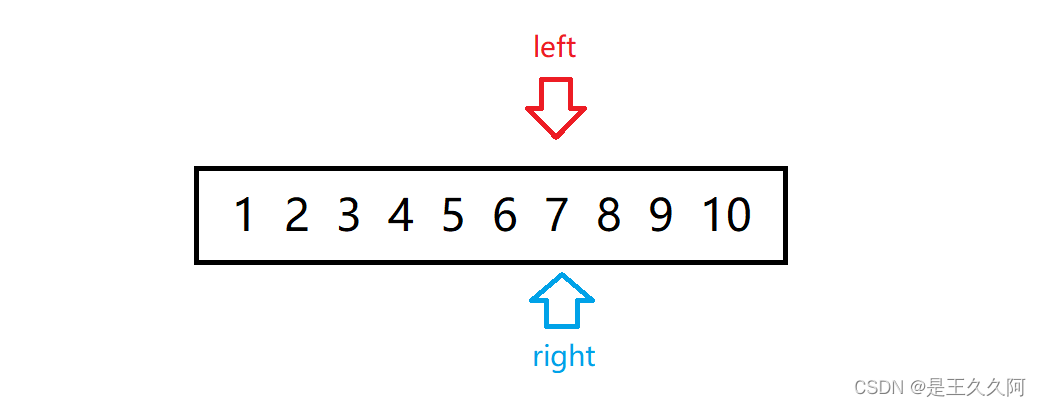
The third search : Judge left、righ The middle number of and 7 Size :6<7, take right Moved to 6+1 It's about .
Fourth search : Judge left、righ The middle number of and 7 Size :7=7, eureka .
Code section
The search process is in the main function :
// Two points search
#include<stdio.h>
int main()
{
int arr[] = { 1,2,3,4,5,6,7,8,9,10 };
int sz = sizeof(arr) / sizeof(arr[0]);
int input = 0;
scanf("%d", &input);
int left = 0;
int right = sz-1;
int mid = 0;
while (left <= right)
{
mid = left+(right - left) / 2;
if (arr[mid] < input)
{
left = mid + 1;
}
else if (arr[mid] > input)
{
right = mid - 1;
}
else
break;
}
if (arr[mid] == input)
printf(" eureka , The subscript is %d\n", mid);
else
printf(" Did not find \n");
return 0;
}The lookup process is in the function :
#include<stdio.h>
void check(int sz,int* arr,int input)//int* arr And int arr[] Agreement , It is the address of the first element of the array
{
int left = 0;
int right = sz - 1;
int mid = 0;
while (left <= right)
{
mid = left + (right - left) / 2;
if (arr[mid] < input)
{
left = mid + 1;
}
else if (arr[mid] > input)
{
right = mid - 1;
}
else
break;
}
if (arr[mid] == input)
printf(" eureka , The subscript is %d\n", mid);
else
printf(" Did not find \n");
}
int main()
{
int arr[] = { 1,2,3,4,5,6,7,8,9,10 };
int sz = sizeof(arr) / sizeof(arr[0]);
int input = 0;
scanf("%d", &input);
check(sz, arr, input);
return 0;
}边栏推荐
- String class
- 20220211-CTF-MISC-006-pure_ Color (use of stegsolve tool) -007 Aesop_ Secret (AES decryption)
- 系统设计学习(二)Design a key-value cache to save the results of the most recent web server queries
- 最新坦克大战2022-全程开发笔记-3
- (超详细二)onenet数据可视化详解,如何用截取数据流绘图
- vector
- Cloud native trend in 2022
- Record: solution of 404 error of servlet accessing database in dynamic web project
- 继承和多态(下)
- View UI plus released version 1.3.0, adding space and $imagepreview components
猜你喜欢
Ten minutes to thoroughly master cache breakdown, cache penetration, cache avalanche
10 minutes pour maîtriser complètement la rupture du cache, la pénétration du cache, l'avalanche du cache
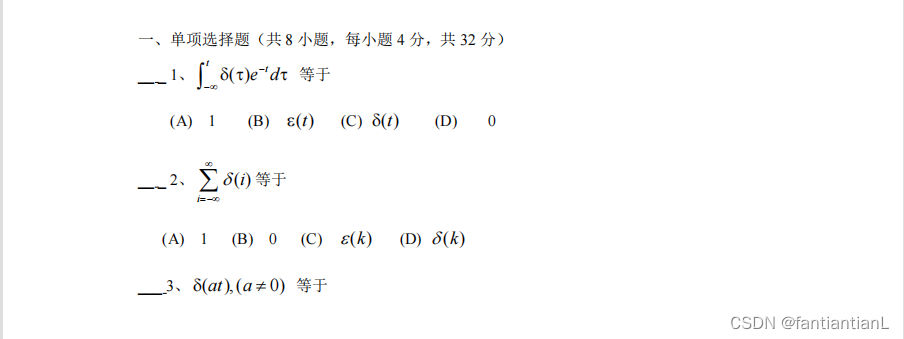
西安电子科技大学22学年上学期《信号与系统》试题及答案
Summary of multiple choice questions in the 2022 database of tyut Taiyuan University of Technology
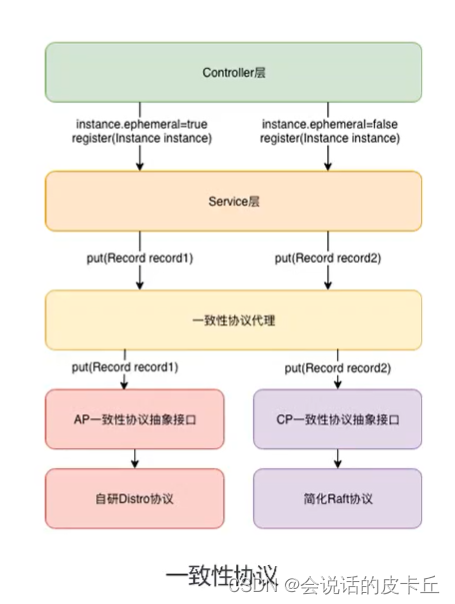
Alibaba cloud microservices (II) distributed service configuration center and Nacos usage scenarios and implementation introduction
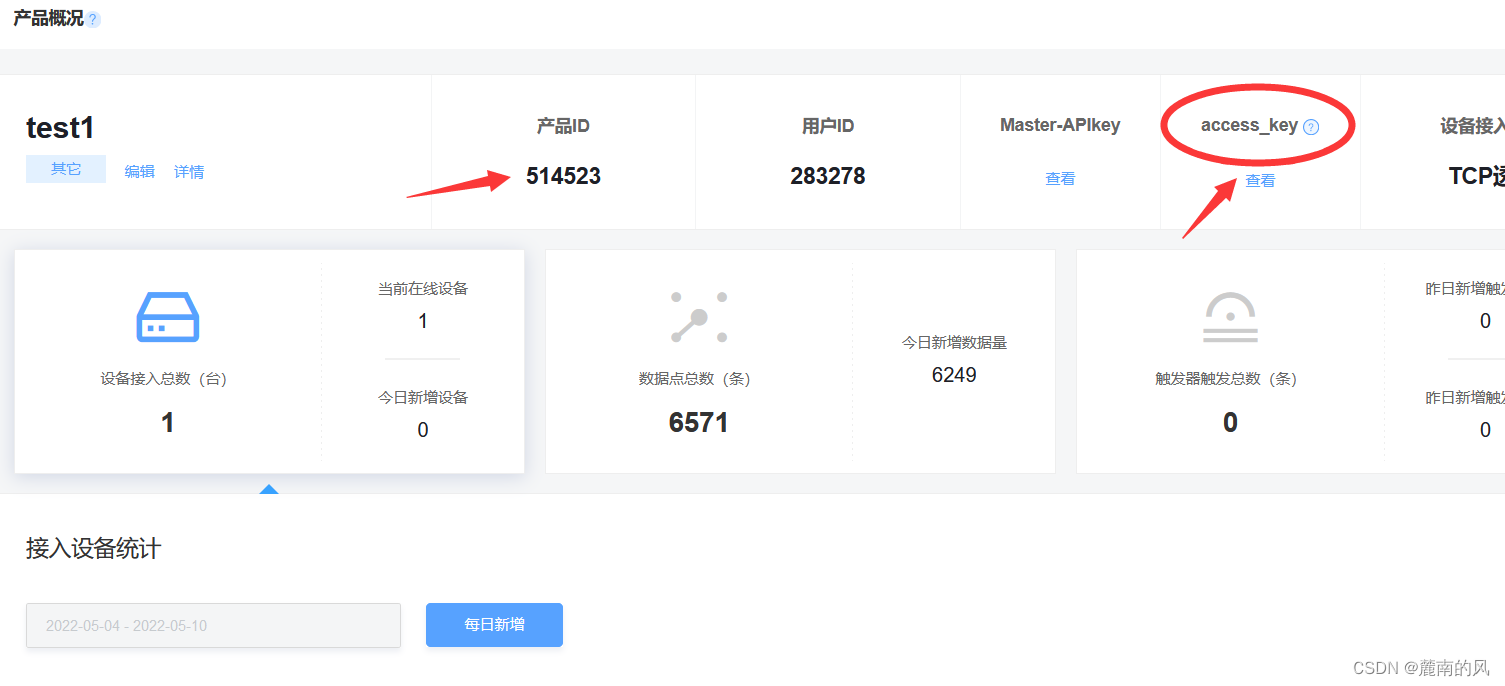
(super detailed II) detailed visualization of onenet data, how to plot with intercepted data flow
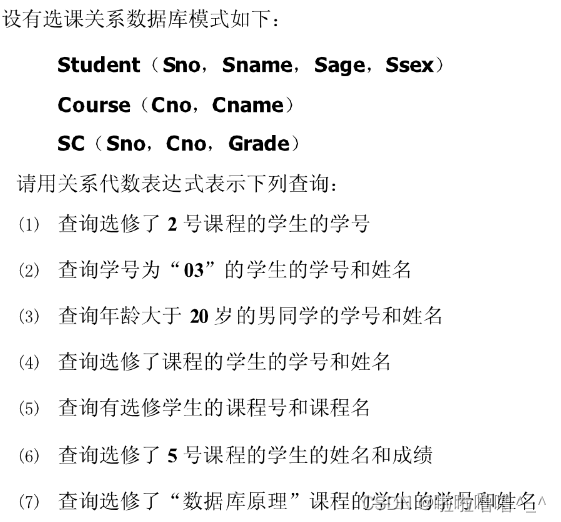
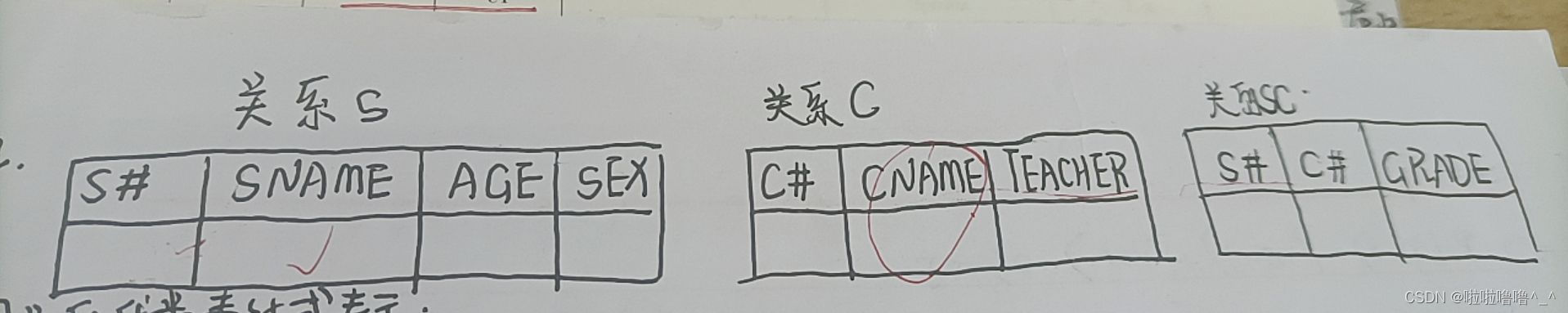
TYUT太原理工大学2022数据库之关系代数小题
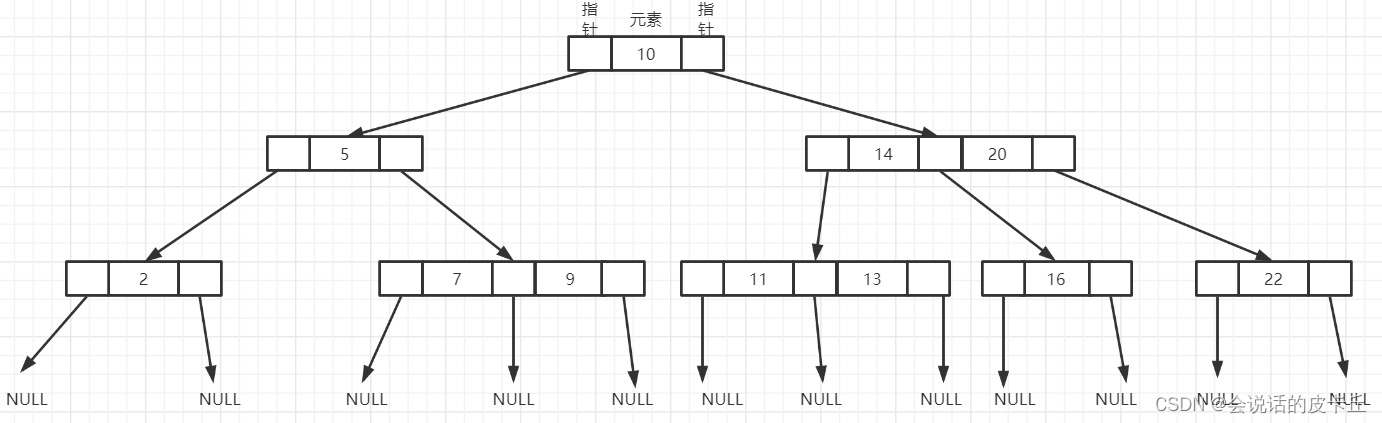
Differences and application scenarios between MySQL index clock B-tree, b+tree and hash indexes

Quickly generate illustrations
Counter attack of flour dregs: redis series 52 questions, 30000 words + 80 pictures in detail.
随机推荐
System design learning (III) design Amazon's sales rank by category feature
Record: Navicat premium can't connect to MySQL for the first time
(超详细二)onenet数据可视化详解,如何用截取数据流绘图
4.30动态内存分配笔记
阿里云微服务(四) Service Mesh综述以及实例Istio
How do architects draw system architecture blueprints?
String类
E-R graph to relational model of the 2022 database of tyut Taiyuan University of Technology
12 excel charts and arrays
13 power map
学编程的八大电脑操作,总有一款你不会
Error: sorting and subscript out of bounds
TYUT太原理工大学2022数据库大题之概念模型设计
【快趁你舍友打游戏,来看道题吧】
Tyut Taiyuan University of technology 2022 introduction to software engineering summary
Network layer 7 protocol
几道高频的JVM面试题
MYSQL索引钟B-TREE ,B+TREE ,HASH索引之间的区别和应用场景
The overseas sales of Xiaomi mobile phones are nearly 140million, which may explain why Xiaomi ov doesn't need Hongmeng
Alibaba cloud microservices (II) distributed service configuration center and Nacos usage scenarios and implementation introduction