当前位置:网站首页>CORS is not intended to protect API endpoints - nikofischer
CORS is not intended to protect API endpoints - nikofischer
2022-07-04 06:34:00 【Jiedao jdon】
CORS Will not protect API The endpoint is protected from attack , Because you can always make the same request outside the browser , And it will not protect any site from cross site requests , because CORS It can always be disabled on the server side .
CORS It can prevent malicious websites from cheating unmodified browsers to make cross site requests for legitimate websites . If the user has the authentication of legal website cookie,cookie Will be sent with the request . therefore , Malicious websites can trade on behalf of users on legitimate websites , Although it cannot access authentication directly cookie.
CORS Further complicate , Because some forms of cross site requests have always been allowed by browsers , So for backward compatibility , Must remain enabled by default . For different websites GET The request is allowed , Because this is always allowed , For example, images embedded in other fields .POST The request is allowed , But be careful not to check the results , Because you've always been able to learn from a html Launch a post to different websites in the form .
This article It's because I'm looking for Vue APP Verify to Drupal Back end approach .Designkojo Is one of the first articles to appear on the top of search engines . Besides , This article is charming : Very good description , concise . Especially for beginners , The method described is easy to implement . It shows that : adopt API Key authentication is Web Common ways of applications . This is where it becomes dangerous : Especially inexperienced developers may be fooled , And think this is through Web Common methods of authentication of applications to the back end .
The settings introduced in the article : The back end consists of Drupal Provide .Drupal From version 8 Began to integrate in the core JSON API, It can be easily activated through module management . With this , You can now access all entities ( For example, users 、 Nodes etc. ) And pass GET Request to read them .
JSON API be based on Drupal Permissions defined in the system . therefore , If the user does not have read permission for a certain content , Then the content cannot pass JSON API load . The same is true of write access : Only when the access user has appropriate permissions , To create 、 Modify or delete entities .
The author describes how he works on the client Vue Access in the application Drupal Back end to create content . Only logged in users can create articles . therefore , To pass through JSON API Create articles , He must first verify himself .
There are several ways to Drupal Authentication . The usual method is through user name and password . This can not only be achieved directly through the front end , It can also be done through API Realization . here Drupal After successful verification, a session is returned ID, You can cache it and use it for all further requests .
The author now uses another way : He installed Key auth modular . This will create one for each user in the backend API secret key , It can be used for API Authentication of . So , The parameter must be “api-key” Pass with the key as the value of each call . such , Users will be Drupal Automatic authentication in , And have all assigned permissions . As described in the article “Key auth” The module is just a substitute for user name and password .
Here he made a dangerous mistake : He will come from Drupal Back end API The key is integrated into his Vue.js In the application , In order to be able to API Authenticate and create content .Vue.js The application executes on the client side of the user's browser . This means that the source code is sent directly from the server to the browser . Now? , Users have full access to the source code , You can also read the authentication key contained in it .
CORS Settings ensure that the backend can only be accessed from a site domain name ?
No, ! No, CORS It is an implementation in the browser , It aims to protect users from malicious applications by ensuring that resources in browsers only allow access to specific endpoints .
The implementation of this browser can be bypassed at any time . First , It depends on the browser itself : If CORS Not integrated , Or it is not integrated cleanly , Then it won't work . Server sends a CORS header , It's up to the browser to decide how to handle it . This is not a safety factor , Because it is not in the hands of the server to deny access here , And completely in the hands of the browser .
Attackers can get through Web Application source code access API Key and use it , For example, through cURL Request direct access to the backend API resources . Use cURL, No, CORS take effect , Therefore, the attacker can directly access all the privileges of the user .
API Keys are substitutes for user names and passwords . No one would expect to be in Web The user name and password are stored in the source code of the application .
As described in the article “Key auth” The module is just a substitute for user name and password .
边栏推荐
- Arcpy uses the updatelayer function to change the symbol system of the layer
- [backpack DP] backpack problem
- Common usage of time library
- Software keywords and process information intercepted by Golden Shield video player
- After the festival, a large number of people change careers. Is it still time to be 30? Listen to the experience of the past people
- C réaliser des jeux de serpents gourmands
- [MySQL] introduction, function, creation, view, deletion and modification of database view (with exercises)
- Sword finger offer II 038 Daily temperature
- 对List进行排序工具类,可以对字符串排序
- 剑指 Offer II 038. 每日温度
猜你喜欢
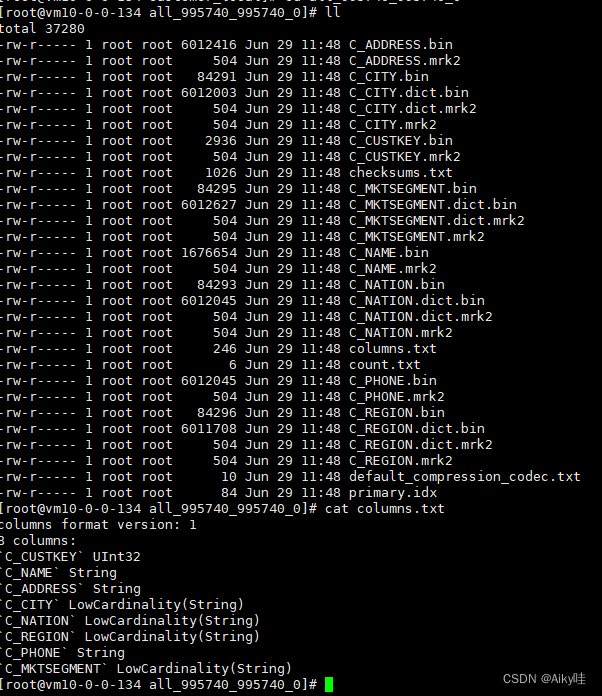
《ClickHouse原理解析与应用实践》读书笔记(4)

QT QTableWidget 表格列置顶需求的思路和代码
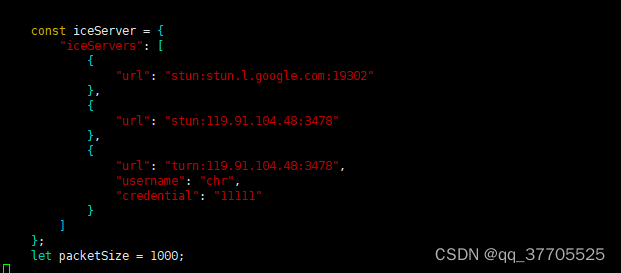
webrtc 快速搭建 视频通话 视频会议
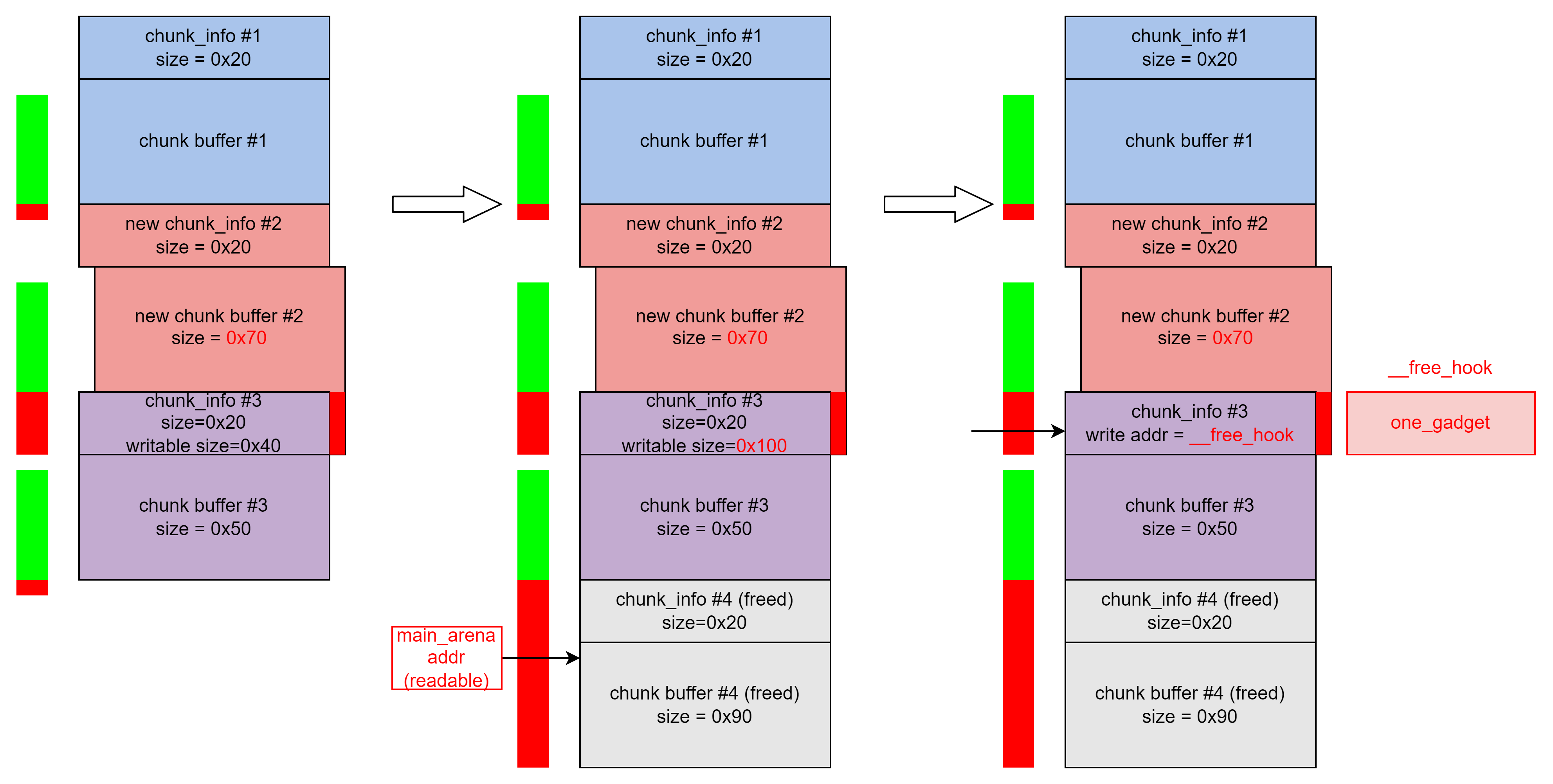
buuctf-pwn write-ups (8)
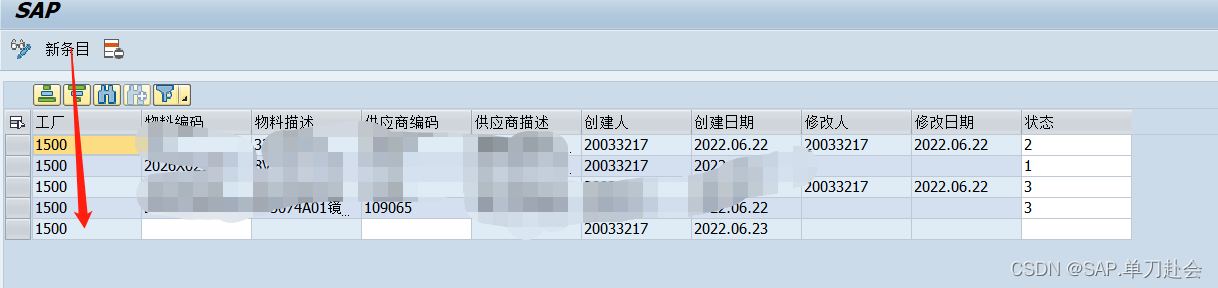
Abap:ooalv realizes the function of adding, deleting, modifying and checking
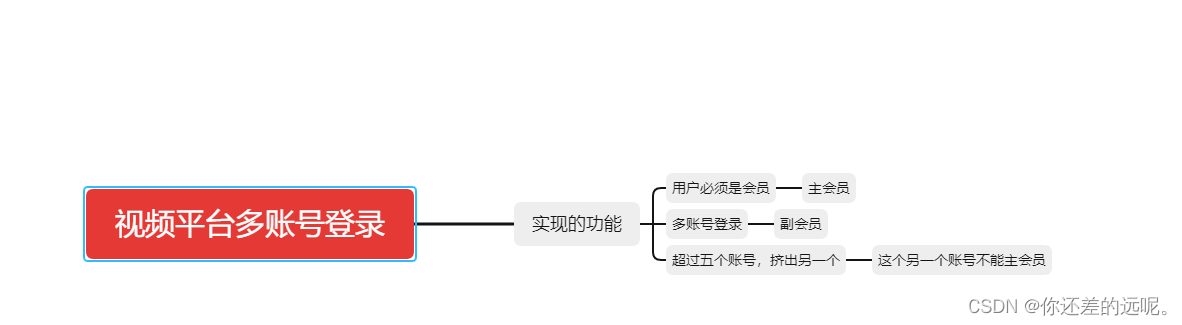
如何实现视频平台会员多账号登录
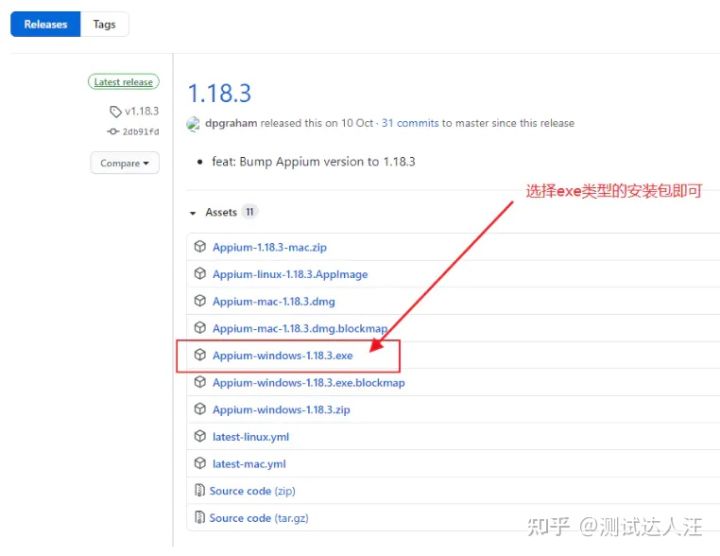
Appium foundation - appium installation (II)

How to choose the middle-aged crisis of the testing post? Stick to it or find another way out? See below
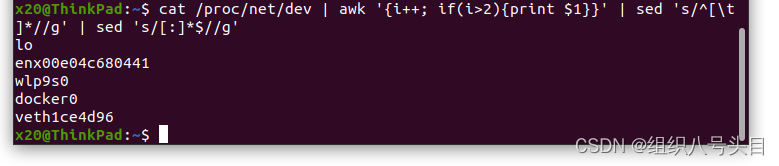
实用的小工具指令

P26-P34 third_ template
随机推荐
Detailed explanation of common APIs for component and container containers: frame, panel, scrollpane
Invalid bound statement (not found): com. example. mapper. TblUserRecordMapper. login
Fast power (template)
8. Factory method
2022 wechat enterprise mailbox login entry introduction, how to open and register enterprise wechat enterprise mailbox?
buuctf-pwn write-ups (8)
C language - Blue Bridge Cup - Snake filling
Sleep quality today 78 points
Notes and notes
C # symmetric encryption (AES encryption) ciphertext results generated each time, different ideas, code sharing
MySQL installation and configuration
Learn about the Internet of things protocol WiFi ZigBee Bluetooth, etc. --- WiFi and WiFi protocols start from WiFi. What do we need to know about WiFi protocol itself?
Internet of things protocol ZigBee ZigBee module uses the concept of protocol stack
Native Cloud - SSH articles must be read on Cloud (used for Remote Login to Cloud Server)
Abap:ooalv realizes the function of adding, deleting, modifying and checking
Component、Container容器常用API详解:Frame、Panel、ScrollPane
实用的小工具指令
分布式CAP理论
如何实现视频平台会员多账号登录
Stc8h development (XII): I2C drive AT24C08, at24c32 series EEPROM storage