当前位置:网站首页>企业公司项目开发好一部分基础功能,重要的事保存到线上第一a
企业公司项目开发好一部分基础功能,重要的事保存到线上第一a
2022-07-04 23:48:00 【济南医疗小程序状元】
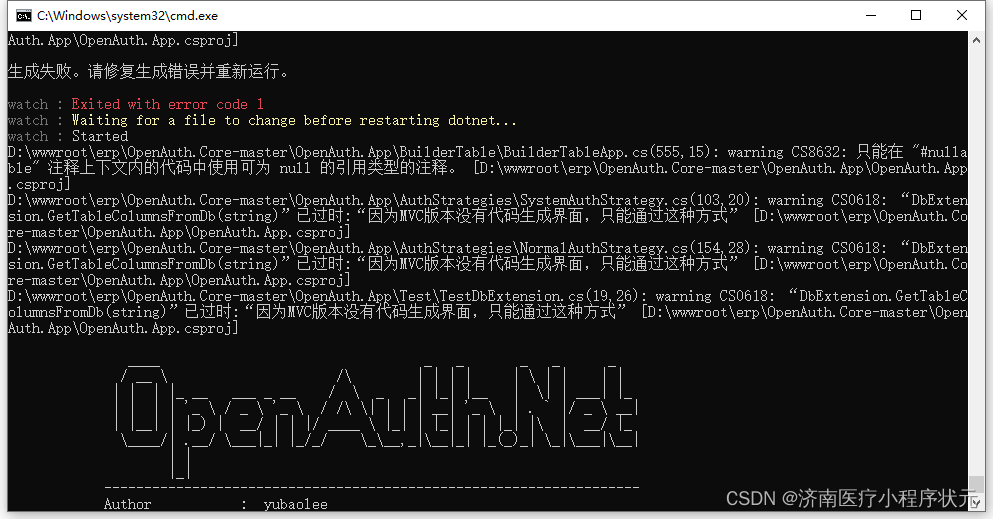
错误的地方,可以跳过去,自动加载后面已经修改的数据值内容.
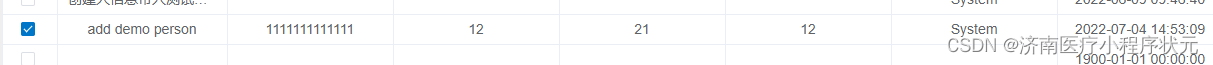
添加数据成功,再逐个进行修改
![]()
1 添加带入创建人完成
最后一个修改.
The vehicle management
完成
![]()
等于又走了一遍,单表开发设计流程的.
保存代码到线上,再修改其他功能的.
边栏推荐
- Phpcms paid reading function Alipay payment
- 高配笔记本使用CAD搬砖时卡死解决记录
- [kotlin] the third day
- 【路径规划】RRT增加动力模型进行轨迹规划
- The difference between cout/cerr/clog
- Stm32 Reverse Introduction to CTF Competition Interpretation
- 微服务(Microservice)那点事儿
- Significance of acrel EMS integrated energy efficiency platform in campus construction
- If you open an account of Huatai Securities by stock speculation, is it safe to open an account online?
- Using fast parsing intranet penetration to realize zero cost self built website
猜你喜欢
ECCV 2022 | Tencent Youtu proposed disco: the effect of saving small models in self supervised learning

Fast parsing intranet penetration helps enterprises quickly achieve collaborative office
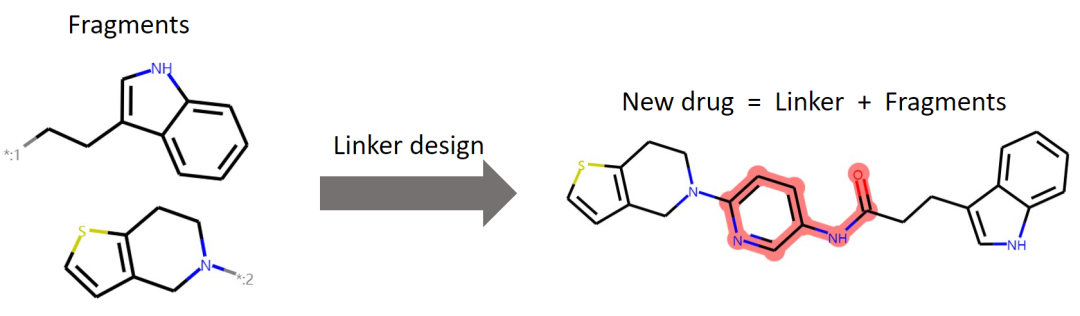
ICML 2022 | 3dlinker: e (3) equal variation self encoder for molecular link design

端口映射和端口转发区别是什么
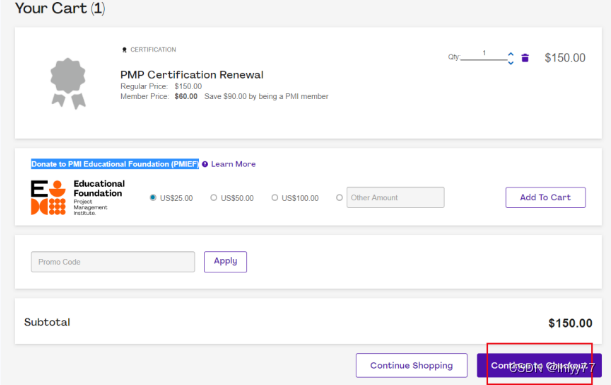
PMP certificate renewal process
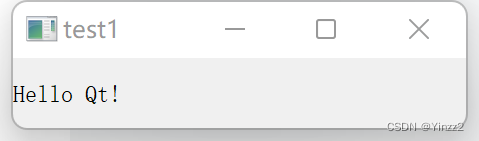
QT personal learning summary

香港珠宝大亨,22亿“抄底”佐丹奴

多回路仪表在基站“转改直”方面的应用

如何用快解析自制IoT云平台

Réseau graphique: Qu'est - ce que le Protocole d'équilibrage de charge de passerelle glbp?
随机推荐
【雅思阅读】王希伟阅读P4(matching1)
Qualcomm WLAN framework learning (30) -- components supporting dual sta
机器人强化学习——Learning Synergies between Pushing and Grasping with Self-supervised DRL (2018)
How to do the project of computer remote company in foreign Internet?
CTF競賽題解之stm32逆向入門
图解网络:什么是网关负载均衡协议GLBP?
How to apply for PMP project management certification examination?
电力运维云平台:开启电力系统“无人值班、少人值守”新模式
List related knowledge points to be sorted out
Financial markets, asset management and investment funds
IELTS examination process, what to pay attention to and how to review?
[crawler] XPath for data extraction
XML的解析
Go pit - no required module provides Package: go. Mod file not found in current directory or any parent
Face recognition 5- insight face padding code practice notes
【js】-【排序-相关】-笔记
初试为锐捷交换机跨设备型号升级版本(以RG-S2952G-E为例)
如何在外地外网电脑远程公司项目?
How to use fast parsing to make IOT cloud platform
Jar批量管理小工具