当前位置:网站首页>Hash quiz game system development how to develop hash quiz game system development (multiple cases)
Hash quiz game system development how to develop hash quiz game system development (multiple cases)
2022-07-04 20:34:00 【VC_ MrsFu123】
A hash table is a key - value (key-indexed) Structure of stored data , We just input the value to be searched key, You can find the corresponding value .
The idea of hash is very simple , If all keys are integers , Then you can use a simple unordered array to achieve : Key as index , Value is its corresponding value , In this way, you can quickly access the value of any key . This is for simple keys , We extend it to keys that can handle more complex types .
How is hash applied in blockchain?
In the blockchain,each block has the hash value of the previous block,which is called the parent block of the current block.Since each block has the hash value of the previous block,when modifying any data of the current block,the hash value of the block will change,which will have an impact on the previous block,because it contains the address of the previous block.
For example,there are currently two blocks,one is the current block,and the other is the parent block.The current block has the address of the parent block.If you need to modify the data of the current block,you need to modify the parent blockchain.It is easier to modify data if there are only two blocks,but in fact,there are many blocks on the blockchain.
There are two steps to using hash lookup :
1. Use the hash function to convert the key to the index of the array . In an ideal situation , Different keys will be converted to different index values , But in some cases we need to deal with multiple keys being hashed to the same index value . So the second step of hash lookup is to handle conflicts
2. Handle hash collision conflicts . There are many ways to handle hash collision conflicts , The zipper method and linear detection method will be introduced later in this paper .
Hash table is a classic example of making a trade-off between time and space . If there is no memory limit , Then you can directly use the key as the index of the array . Then all the search time complexity is O(1); If there is no time limit , Then we can use unordered arrays and look them up in order , This requires very little memory . Hashtable uses a moderate amount of time and space to find a balance between these two extremes . Just adjust the hash function algorithm to make the trade-off between time and space .
stay Hash In the table , There is a definite relationship between the position of the record in the table and its keywords . In this way, we can know the position of the keyword in the table in advance , To find records directly by subscript . send ASL Approach and 0.
1) Hash (Hash) A function is a map , namely : Map a set of keywords to an address set , Its settings are flexible , As long as the size of this address set does not exceed the allowable range ;
2) Because the hash function is a compressed image , therefore , In general , Easy to produce “ Conflict ” The phenomenon , namely :key1!=key2, and f(key1)=f(key2).
3). Conflicts can only be minimized but not completely avoided , This is because the keyword set is usually large , Its elements include all possible keywords , The elements of the address set are only the address values in the hash table
In constructing this special “ Lookup table ” when , In addition to choosing one “ good ”( As little conflict as possible ) Outside the hash function of ; We still need to find one “ Handling conflicts ” Methods .
Compared with traditional notarization and other third-party deposit forms,blockchain deposit has the following advantages:
1.It cannot be tampered with.Blockchain technology can package a certain range of electronic data in a recognized way,then"Encrypt and calculate",get a"check value",and form a"block".All the information in this"block"will be included in the next"block".As the number of blocks increases gradually,the blocks become a chain connected end to end.Because the data changes of each block must follow the algorithm rules within the blockchain,and the update of the data on the chain needs to reach an agreement with all other blocks,the more blocks the chain contains,the less the probability of being modified,until it can be ignored,In this way,after being fixed and saved by blockchain and its extension technology,electronic data has the property of anti-counterfeiting.
2.Prevent loss.Blockchain certificate deposit has the advantage of anti loss,which is derived from the tamper resistant nature of blockchain.Each block will store data completely according to the chain structure.As long as not all blocks are damaged,the information will not be lost.
3.Traceability.Since the blockchain is arranged in sequence according to the time sequence of each block,users can trace back to the source of the information according to the timestamp information on the blockchain,and the authenticity and accuracy of the information can be guaranteed.
4.Efficient and convenient.Compared with traditional electronic data collection,it has the disadvantages of high fixed cost and low efficiency.Blockchain deposit can technically fix evidence,reduce the cost of proof and improve the efficiency of judicial work.At the same time,blockchain certificate deposit can gradually reduce the links of third-party authentication,authentication or notarization in the review process,thereby reducing the investment of judicial review time and energy.
边栏推荐
- Template_ Judging prime_ Square root / six prime method
- Six stones programming: about code, there are six triumphs
- C language - Introduction - Foundation - grammar - process control (VII)
- Template_ Large integer subtraction_ Regardless of size
- Neural network IOT platform construction (IOT platform construction practical tutorial)
- NLP、视觉、芯片...AI重点方向发展几何?青源会展望报告发布[附下载]
- SSRS筛选器的IN运算(即包含于)用法
- 什么是区块哈希竞猜游戏系统开发?哈希竞猜游戏系统开发(案例成熟)
- 太方便了,钉钉上就可完成代码发布审批啦!
- How to adapt your games to different sizes of mobile screen
猜你喜欢
![[problem] Druid reports exception SQL injection violation, part always true condition not allow solution](/img/cc/160bc8ccdc378901510c1b61c3f5d3.png)
[problem] Druid reports exception SQL injection violation, part always true condition not allow solution
输入的查询SQL语句,是如何执行的?
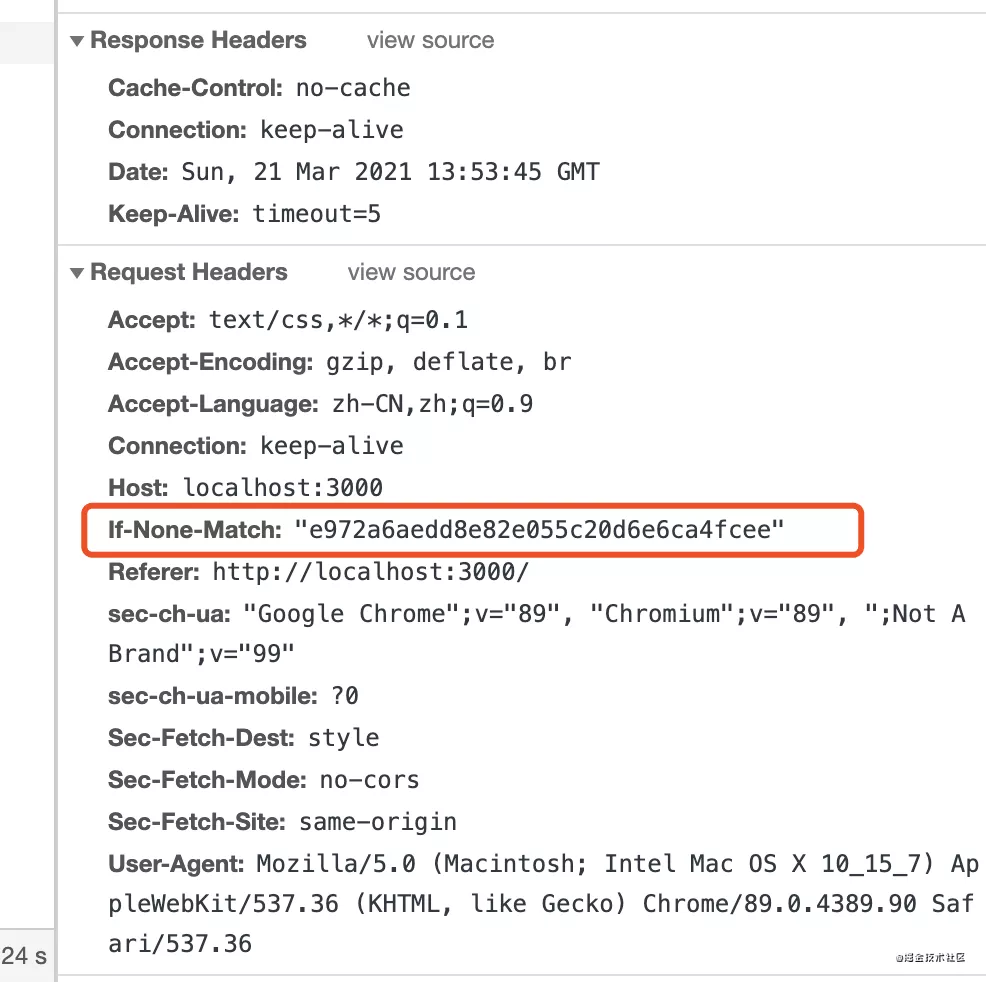
Practical examples of node strong cache and negotiation cache

In the first month of its launch, the tourist praise rate of this campsite was as high as 99.9%! How did he do it?
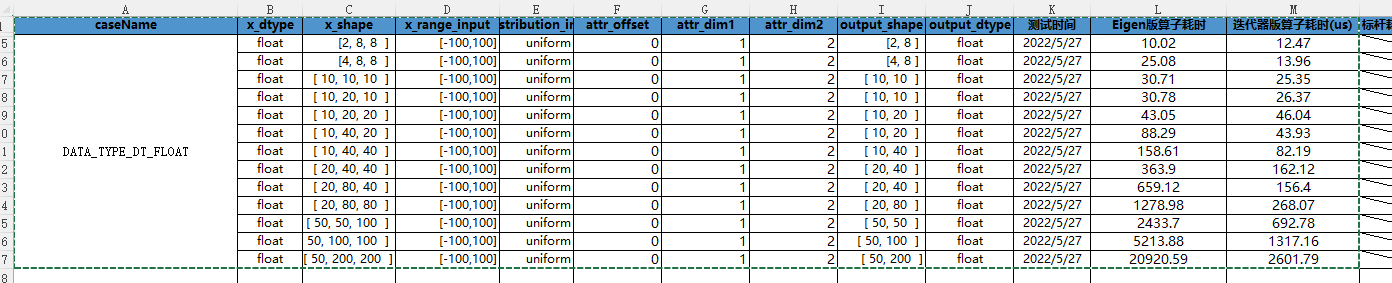
Cann operator: using iterators to efficiently realize tensor data cutting and blocking processing
![Employment prospects of neural network Internet of things application technology [welcome to add]](/img/b0/fe525a1c4788c2c377d49e6b98cf74.png)
Employment prospects of neural network Internet of things application technology [welcome to add]
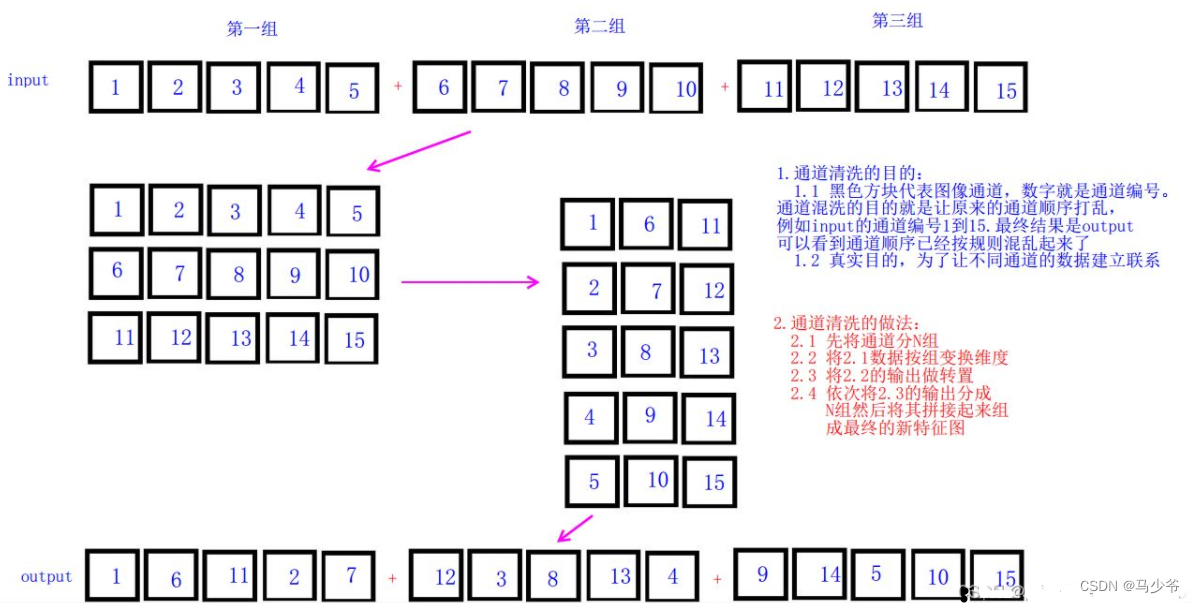
YOLOv5s-ShuffleNetV2
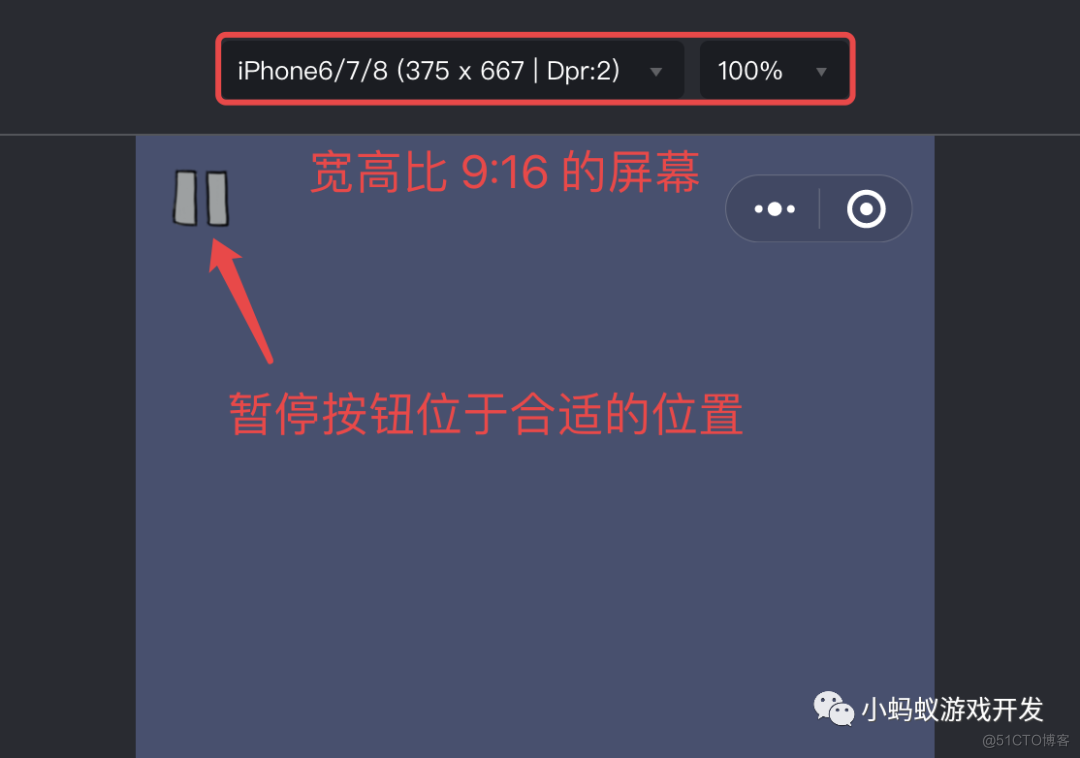
How to adapt your games to different sizes of mobile screen
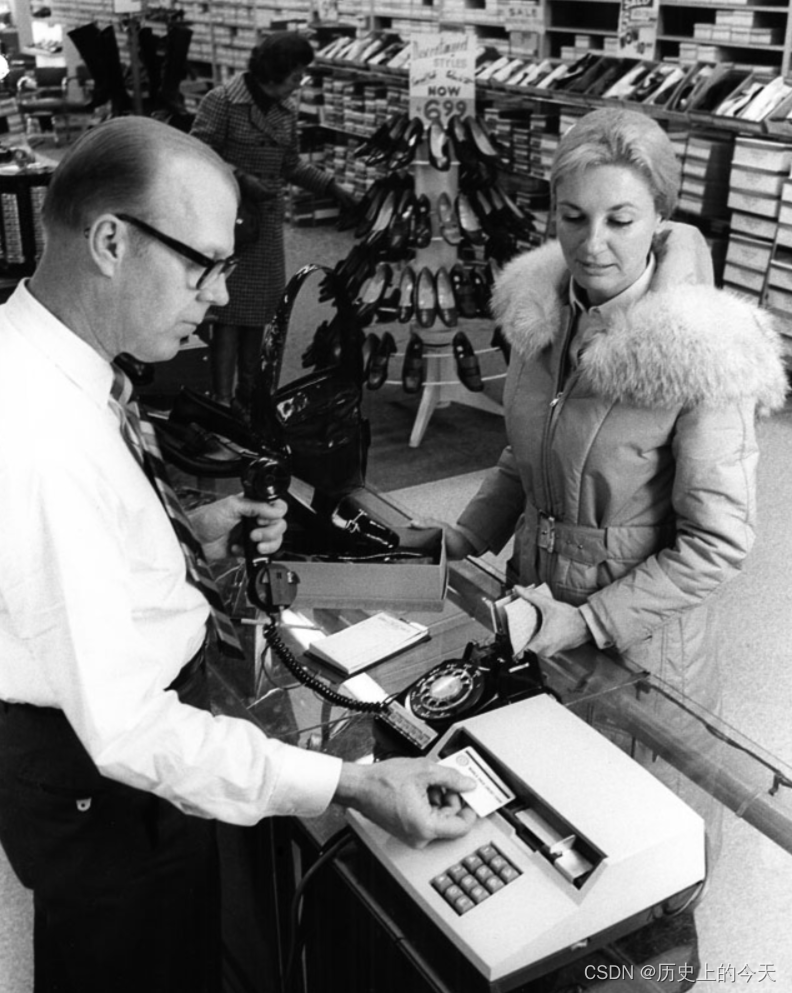
【历史上的今天】7 月 4 日:第一本电子书问世;磁条卡的发明者出生;掌上电脑先驱诞生
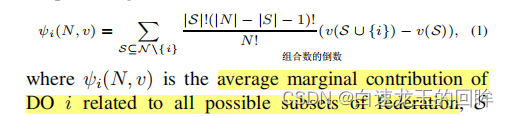
关于联邦学习和激励的相关概念(1)
随机推荐
Small hair cat Internet of things platform construction and application model
泰山OFFICE技术讲座:关于背景(底纹和高亮)的顺序问题
Informatics Olympiad 1336: [example 3-1] find roots and children
What should we pay attention to when doing social media marketing? Here is the success secret of shopline sellers!
#夏日挑战赛#带你玩转HarmonyOS多端钢琴演奏
Oracle database, numbers Force 2 decimal places to display-Alibaba Cloud
Flet教程之 06 TextButton基础入门(教程含源码)
Aiming at the "amnesia" of deep learning, scientists proposed that based on similarity weighted interleaved learning, they can board PNAS
Process of manually encrypt the mass-producing firmware and programming ESP devices
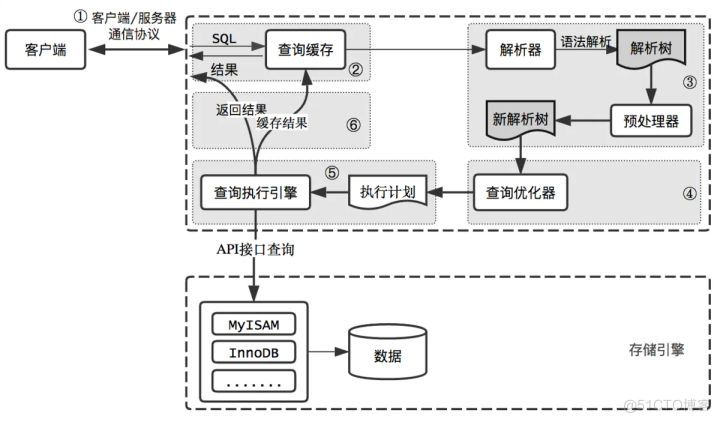
How is the entered query SQL statement executed?
Win11共享文件打不开怎么办?Win11共享文件打不开的解决方法
CDGA|数据治理不得不坚持的六个原则
Introduction to ACM combination counting
FS4061A升压8.4V充电IC芯片和FS4061B升压12.6V充电IC芯片规格书datasheet
Neural network IOT platform construction (IOT platform construction practical tutorial)
2022 version of stronger jsonpath compatibility and performance test (snack3, fastjson2, jayway.jsonpath)
NLP, vision, chip What is the development direction of AI? Release of the outlook report of Qingyuan Association [download attached]
On communication bus arbitration mechanism and network flow control from the perspective of real-time application
In operation (i.e. included in) usage of SSRs filter
Flet教程之 07 PopupMenuButton基础入门(教程含源码)