当前位置:网站首页>What is the development of block hash quiz game system? Hash quiz game system development (case mature)
What is the development of block hash quiz game system? Hash quiz game system development (case mature)
2022-07-04 20:36:00 【VC_ MrsFu123】
01.Hash function
One way hash function , Also known as one-way Hash function 、 Hash function , It is a function that changes the input message string of any length into a fixed output string, and it is difficult to get the input string from the output string . This output string is called the hash value of the message . Generally used to generate message summaries , Key encryption, etc .
Hash algorithm is widely used in many scenarios , For example, secure encryption and hash table lookup in data structures , Bloom filter and load balancing ( Consistent Hashing ) wait .
02. common Hash function
common Hash Function has MD series 、SHA series 、MAC and CRC etc. .
MD series
MD Full name Message Digest, According to the Standard Version, it is divided into MD2、MD4、MD5 Three algorithms , At present, the most commonly used is MD5 Version algorithm .
MD4 Algorithm
1990 year , stay MD2 On the basis of the development of MD4 Algorithm .
MD5 Algorithm
1991 year ,MD4 Its founder developed MD5 Algorithm . No matter how long the string is , Use MD5 The calculated length is the same , It is convenient for the statistics and management of information at ordinary times .
after MD5 Encryption generates a fixed length of 128bit String of . because 128 position 0 and 1 The binary string expression of is not friendly , So it turns into 16 Base number ,128/4=32 Bit 16 Base number . take 32 Before removing bit 8 Position and back 8 Bit gets 16 position . So there will be MD5 Of 32 Bit and 16 Bit encryption .
SHA series
SHA(Security Hash Algorithm) It's American NIST and NSA A standard of design Hash Algorithm ,SHA Standard algorithm for digital signature DSS in , It is also a kind of high security Hash Algorithm .
SHA-1
SHA-1 The input message length of the algorithm is less than 264bit, The final output value is 160 Bits,SHA-1 And MD4 By comparison , It mainly increases the extension transformation , Add the output of the previous round to the next one , This increases the avalanche effect , And because of it 160 Bits Output , More resistant to exhaustive attacks .
The general implementation process : Convert the message digest into a bit string , Carry on the place filling operation to the converted bit string , Attach the length value and initialize the cache , Then calculate the message digest .
SHA-256
SHA-256 The maximum length of algorithm input message does not exceed 264 Bits, Enter the 512 Bits Work in groups , The output produced is a 256 Bits Message summary of .
SHA-2 Other derivative algorithms of
Include SHA-224、SHA-256、SHA-384、SHA-512, Together these versions make up SHA big family .
SHA-224:SHA-256 Of “ Castration plate ”, Can generate length 224bit A summary of the information .
SHA-512: Can generate length 512bit A summary of the information .
SHA-384:SHA-512 Of “ Castration plate ”, Can generate length 384bit A summary of the information .
SHA The newest member of the family SHA-3 Already in 2015 It came out in .
MAC
MAC Algorithm (Message Authentication Codes) With a secret key Hash function .
MAC There are two forms of Algorithm , Namely CBC-MAC Algorithm and HMAC Algorithm . stay HTTP Most used in MAC The algorithm is HMAC Algorithm .
HMAC(Hash-based Message Authentication Code) The algorithm uses Hash Algorithm as encryption primitive ,HMAC combination Hash There are many variations of the algorithm , such as HMAC-SHA-1、HMAC-SHA256、HMAC-SHA512. Don't mistake HMAC The algorithm is Hash The algorithm adds a key ,HMAC The algorithm is just based on Hash Algorithm , The internal implementation is quite complicated .
CRC
CRC(Cyclic Redundancy Check): Cyclic redundancy test . It is a hash function that generates a short fixed digit check code based on data packets on the Internet or computer files , It is mainly used to detect or verify the possible errors after data transmission or saving . The generated number is calculated and appended to the data before transmission or storage , The receiver then checks to see if the data has changed . Generally speaking , The values of cyclic redundancy check are 32 An integer . Because this function is easy to use binary computer hardware 、 Easy to do mathematical analysis and especially good at detecting errors caused by transmission channel interference , So it's widely used .
list (Hash table, Also called hash table ) It's a search algorithm , With the list 、 Tree algorithm is different from , Hash table algorithm does not need to do a series of search and keyword search ( A keyword is the value of a data item in a data element , To identify a data element ) Comparison operation of .
Hash table algorithm wants to be able to do as much as possible without any comparison , You can get the data elements you are looking for in one access , Therefore, the storage location of the data element and its keyword must be specified ( You can use key Express ) Establish a definite correspondence between , Make each keyword correspond to a unique storage location in the hash table . So in the search , Just find the position of the given keyword in the hash table according to the corresponding relationship . This correspondence is called a hash function ( You can use h(key) Express ).
The methods used to construct hash functions are :
(1) direct addressing : Take the key or a linear function value of the key as the hash address . namely :h(key)=key or h(key)=a*key+b, among a and b Constant .
(2) Digital analysis
(3) The square method : Take the middle digits after the square of the keyword as the hash address .
(4) Folding method : Divide keywords into parts with the same number of digits , Then take the sum of these parts as the hash address .
(5) Division and remainder : The keyword is not longer than the hash table m Number of numbers p The remainder after division is the hash address , namely :h(key)=key MOD p p≤m
(6) Random number method : Choose a random function , Take the random function value of the keyword as its hash address , namely :h(key)=random(key)
So construct a useful hash table , The most important thing is to do the following two things well :
To design a " good " Hash function to calculate Key value .( A good hash function should avoid conflicts as much as possible , And the calculation should be as simple and fast as possible )
What is a block hash?
The block hash value is the DNA of a piece of data,and each block hash value is unique,random and unbreakable."Hashfun"is hello DAPP,the SK application launched by fun blockchain ecology in the gamefi stage,has a mission to implement the"interesting investment and mining"mechanism and attract millions of Genesis residents.
What is blockchain?
In essence,blockchain is a shared database of data or information stored in it.It has the characteristics of unforgeability,full trace,traceability,openness and transparency,collective maintenance,etc
边栏推荐
- 解密函数计算异步任务能力之「任务的状态及生命周期管理」
- 什么叫内卷?
- Talking about cookies of client storage technology
- ICML 2022 | meta proposes a robust multi-objective Bayesian optimization method to effectively deal with input noise
- FS4061A升压8.4V充电IC芯片和FS4061B升压12.6V充电IC芯片规格书datasheet
- Is it necessary to apply for code signing certificate for software client digital signature?
- 15million employees are easy to manage, and the cloud native database gaussdb makes HR office more efficient
- Integritee通过XCM集成至Moonriver,为其生态系统带来企业级隐私解决方案
- 2022 Health Exhibition, health exhibition, Beijing Great Health Exhibition and health industry exhibition were held in November
- 长城证券开户安全吗 股票开户流程网上开户
猜你喜欢
Introduction to ACM combination counting
![[problem] Druid reports exception SQL injection violation, part always true condition not allow solution](/img/cc/160bc8ccdc378901510c1b61c3f5d3.png)
[problem] Druid reports exception SQL injection violation, part always true condition not allow solution
Neural network IOT platform construction (IOT platform construction practical tutorial)
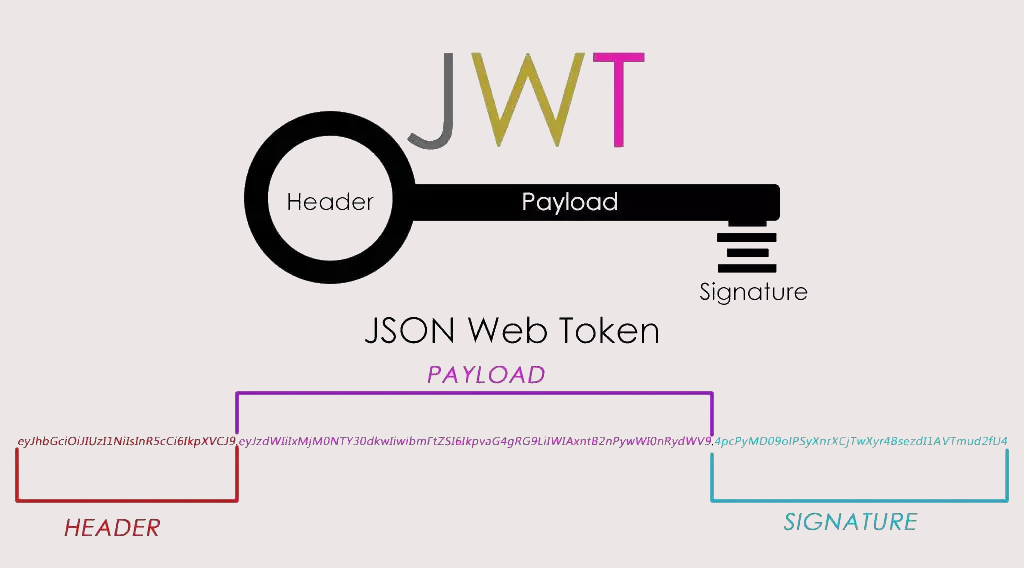
实战模拟│JWT 登录认证
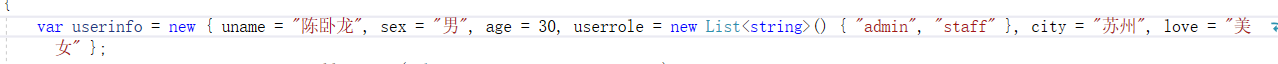
NetCore3.1 Json web token 中间件
Swagger suddenly went crazy
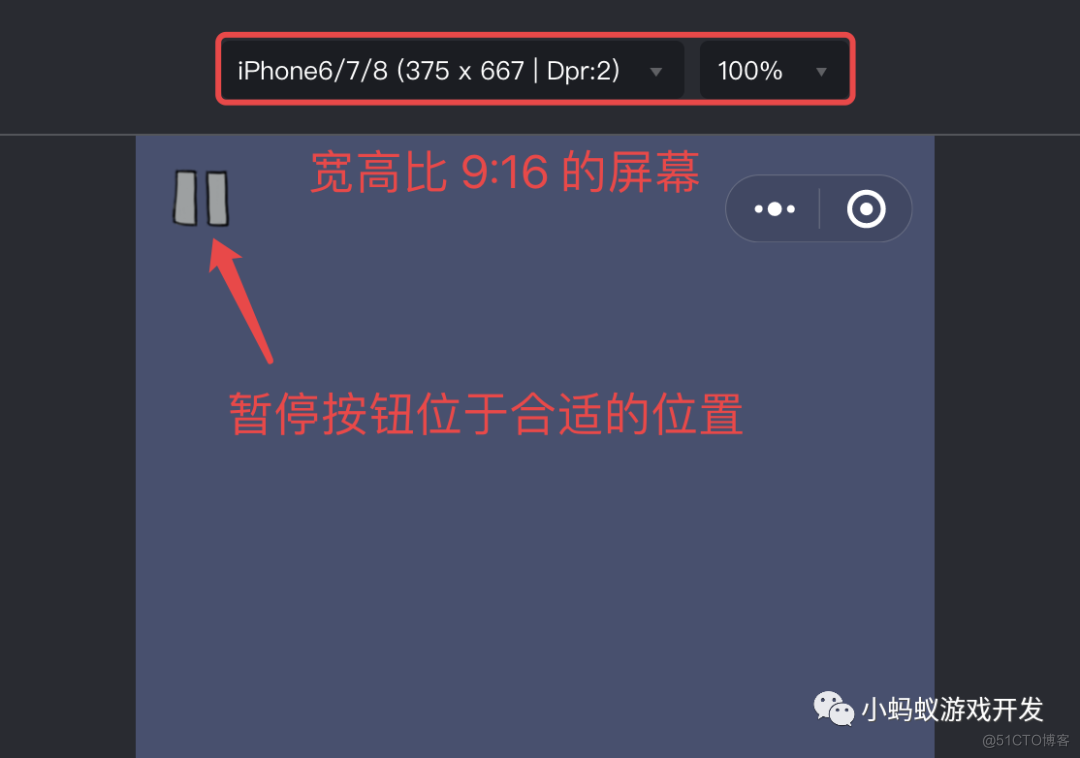
How to adapt your games to different sizes of mobile screen
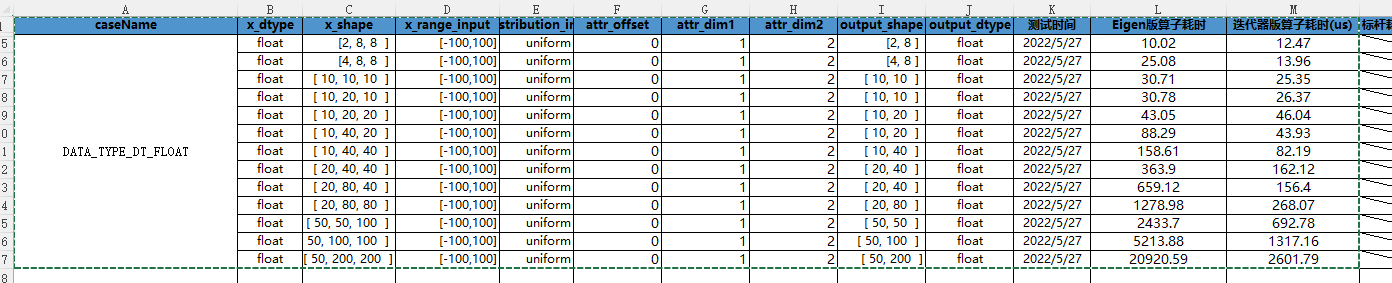
CANN算子:利用迭代器高效实现Tensor数据切割分块处理

What should we pay attention to when doing social media marketing? Here is the success secret of shopline sellers!
![NLP, vision, chip What is the development direction of AI? Release of the outlook report of Qingyuan Association [download attached]](/img/79/82763392e74d102921b4e8e601d4c6.png)
NLP, vision, chip What is the development direction of AI? Release of the outlook report of Qingyuan Association [download attached]
随机推荐
Employment prospects and current situation of Internet of things application technology
【历史上的今天】7 月 4 日:第一本电子书问世;磁条卡的发明者出生;掌上电脑先驱诞生
On communication bus arbitration mechanism and network flow control from the perspective of real-time application
Decryption function calculates "task state and lifecycle management" of asynchronous task capability
In the first month of its launch, the tourist praise rate of this campsite was as high as 99.9%! How did he do it?
Delete the characters with the least number of occurrences in the string [JS, map sorting, regular]
2022 version of stronger jsonpath compatibility and performance test (snack3, fastjson2, jayway.jsonpath)
水晶光电:长安深蓝SL03的AR-HUD产品由公司供应
紫光展锐完成全球首个 5G R17 IoT NTN 卫星物联网上星实测
实战模拟│JWT 登录认证
[in-depth learning] review pytoch's 19 loss functions
Regular replacement [JS, regular expression]
软件客户端数字签名一定要申请代码签名证书吗?
NLP, vision, chip What is the development direction of AI? Release of the outlook report of Qingyuan Association [download attached]
Ziguang zhanrui completed the first 5g R17 IOT NTN satellite on the Internet of things in the world
长城证券开户安全吗 股票开户流程网上开户
In operation (i.e. included in) usage of SSRs filter
Creation of JVM family objects
Free soldier
B2B mall system development of electronic components: an example of enabling enterprises to build standardized purchase, sale and inventory processes