当前位置:网站首页>Security level
Security level
2022-07-05 01:47:00 【Salted fish Feifei】
In cryptography , The security level is an encryption primitive ( Such as a ciphertext or a hash function ) Measurement of the safety intensity that can be achieved , Its unit is usually bit. An encryption scheme is n-bit Safe , It means that an attacker wants to break the scheme , Must perform at least  operations . for example AES-128( The key length is 128bit) The security level of is 128-bit, It's about equal to 3072-bit Of RSA.
operations . for example AES-128( The key length is 128bit) The security level of is 128-bit, It's about equal to 3072-bit Of RSA.
The target security level is , The security level that must be achieved in the design of this scheme . If the attacker can break this scheme at a lower cost , It means that the target security level is not reached .
Different encryption schemes are right “ Break through ” The definition of is not necessarily the same , It depends on the security requirements of the problem solved by the solution . For example, an encryption scheme , Such as RAS, According to some ciphertext pairs , find RSA The key of . A hash function , It may be to find an original image whose hash value is a fixed value , That is, the original image of hash function is stable , It is also possible to find that the hash values of two plaintext are the same , That is, the collision problem .
Generally speaking , For symmetric encryption scheme , The security level is the length of the key , such as AES-128 The security level of is 128bit. Of course, for hash functions , The original image problem is the length of the key , The collision problem is half the length of the key . however Phelix( One basis MAC Stream cipher of XOR operation ) have 256bit The key of , But it only provides 128bit Security level of .SHA-3 Of SHAKE variant , about 256bit Output , The security level of the original image and collision is 128bit.
For asymmetric encryption , It's a little different . Usually come a Book , Asymmetric encryption is based on a difficult mathematical problem , The problem goes in one direction ( Encryption direction ) It's simple. , And its reverse direction ( Decryption direction ) It's difficult , Need some help information ( secret key ) Can be solved simply . Breaking this encryption scheme can often be prescribed to solve a difficult problem , such as RSA It can be reduced to the problem of large integer factorization . therefore , The security level of asymmetric encryption is defined according to the time required by the best algorithm to solve this difficult problem . and , These algorithms are often faster than brute force cracking .
about “ Break through ” An encryption scheme , It refers to finding an algorithm that can break the scheme , The operation required is lower than the security level he claims . however , In practice, it may not be possible .
Now, , Less than  It can be solved . and
It can be solved . and  To
To  It may be solved in the future .
It may be solved in the future .
Reference resources :
Wikipedia :security level
边栏推荐
- Wechat applet: new independent backstage Yuelao office one yuan dating blind box
- 如何搭建一支搞垮公司的技术团队?
- Using openpyxl module to write the binary list into excel file
- Numpy library introductory tutorial: basic knowledge summary
- Heartless sword English translation of Xi Murong's youth without complaint
- 【LeetCode】88. Merge two ordered arrays
- PHP Joseph Ring problem
- Database postragesq PAM authentication
- Comment mettre en place une équipe technique pour détruire l'entreprise?
- [CTF] AWDP summary (WEB)
猜你喜欢

Comment mettre en place une équipe technique pour détruire l'entreprise?
微信小程序:星宿UI V1.5 wordpress系统资讯资源博客下载小程序微信QQ双端源码支持wordpress二级分类 加载动画优化
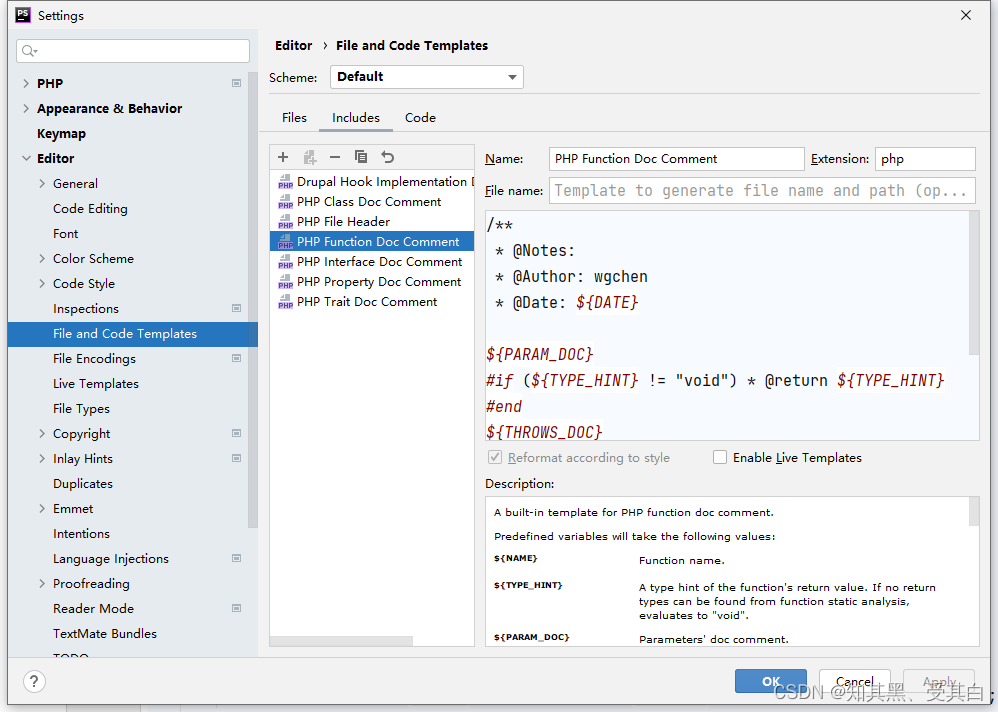
phpstrom设置函数注释说明
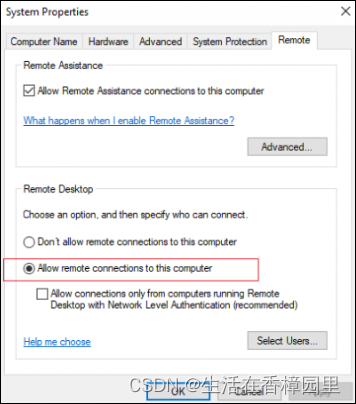
Win:使用 Shadow Mode 查看远程用户的桌面会话
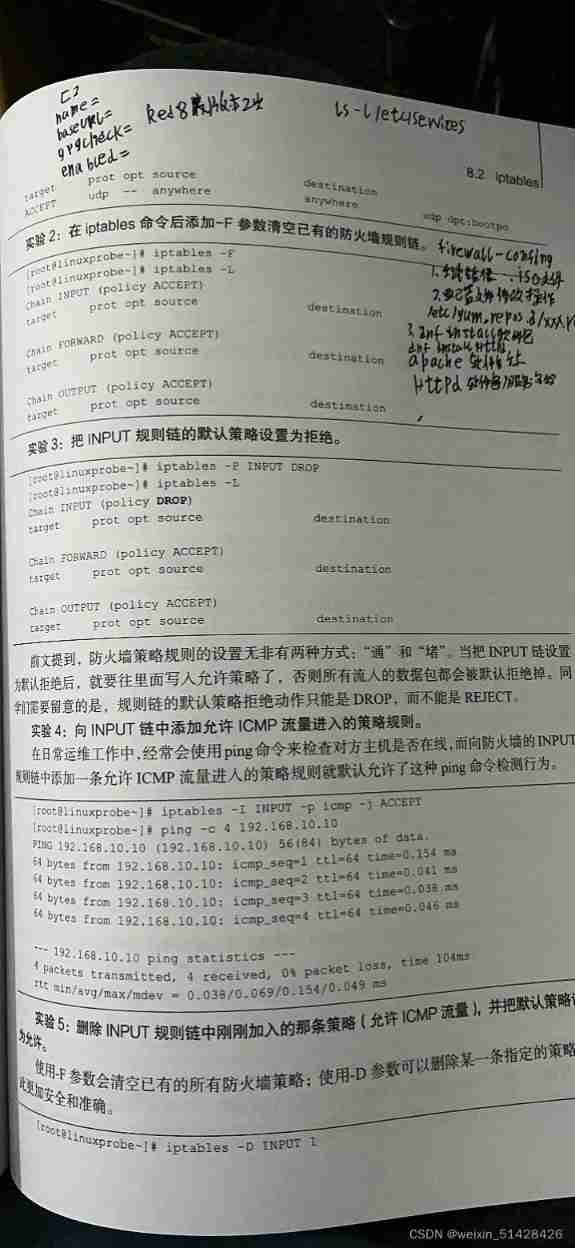
Hedhat firewall
Wechat applet: independent background with distribution function, Yuelao office blind box for making friends
![[swagger]-swagger learning](/img/60/1dbe074b3c66687867192b0817b553.jpg)
[swagger]-swagger learning
The MySQL team development specifications used by various factories are too detailed. It is recommended to collect them!
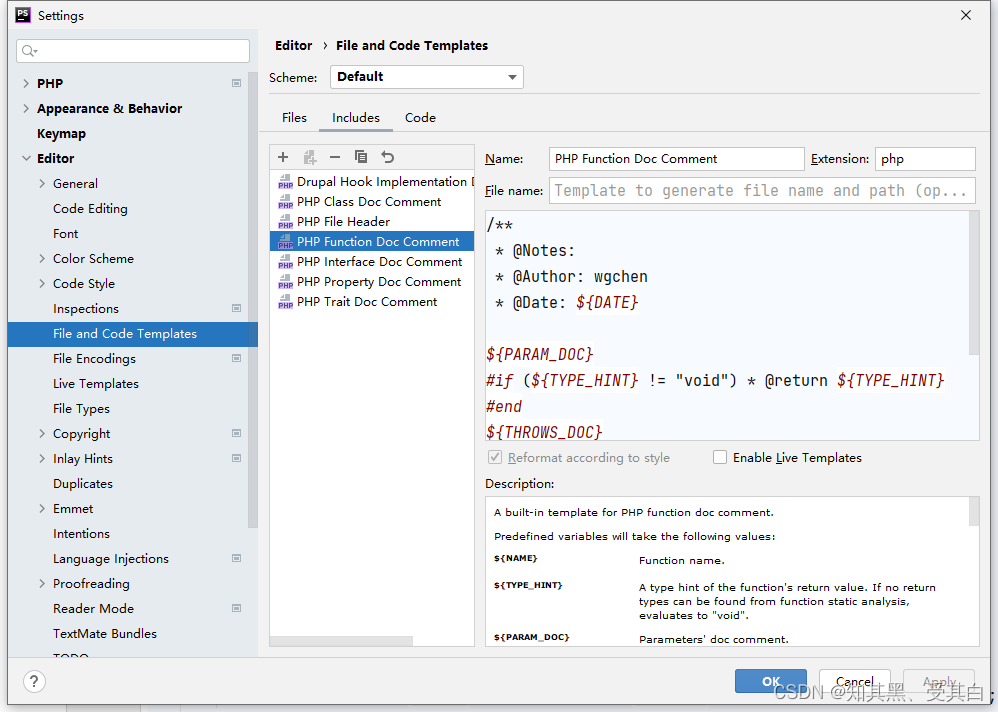
Phpstrom setting function annotation description
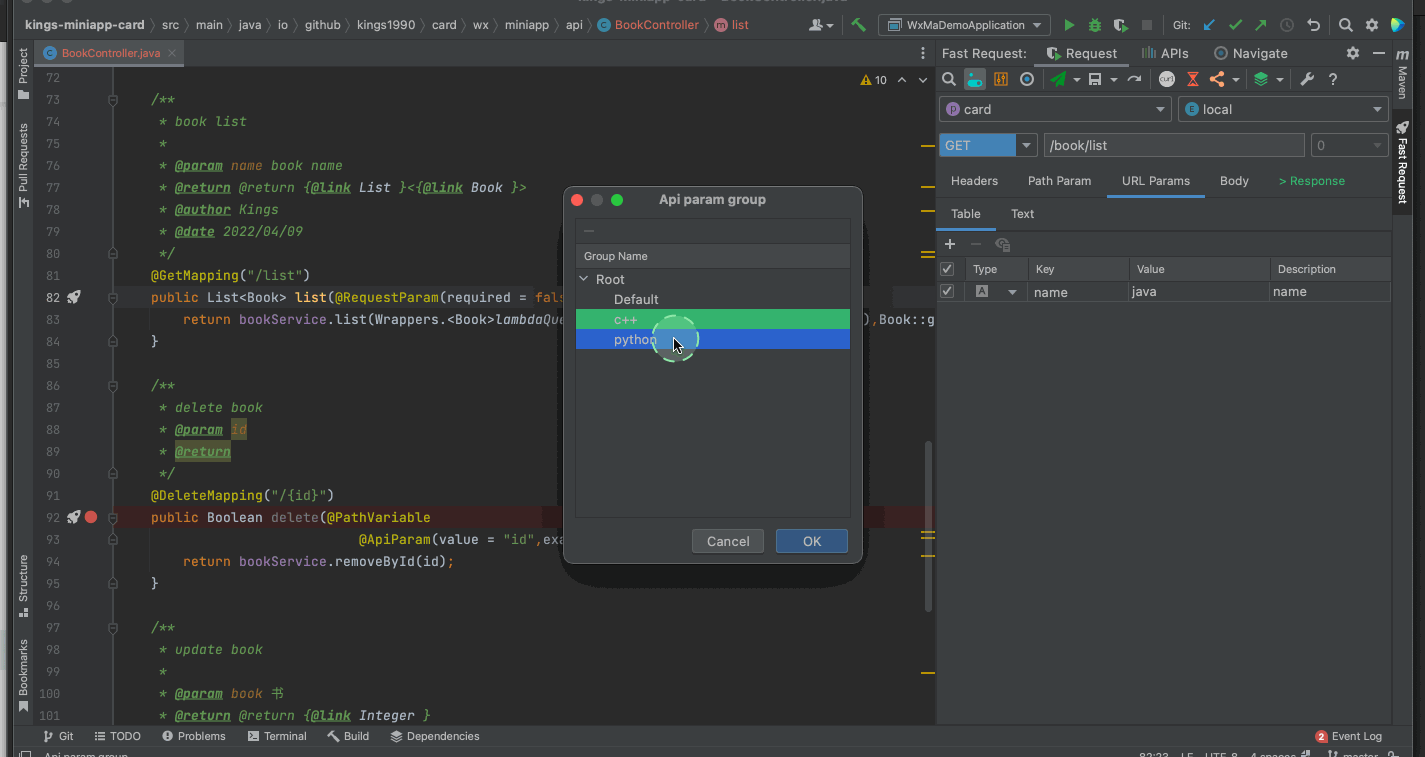
Restful Fast Request 2022.2.1发布,支持cURL导入
随机推荐
Mysql database | build master-slave instances of mysql-8.0 or above based on docker
Win: use shadow mode to view the Desktop Session of a remote user
Interesting practice of robot programming 16 synchronous positioning and map building (SLAM)
Restful Fast Request 2022.2.1发布,支持cURL导入
Using openpyxl module to write the binary list into excel file
179. Maximum number - sort
Valentine's Day flirting with girls to force a small way, one can learn
Pytorch common code snippet collection
如何搭建一支搞垮公司的技術團隊?
What is the current situation and Prospect of the software testing industry in 2022?
Rabbit MQ message sending of vertx
Wechat applet: independent background with distribution function, Yuelao office blind box for making friends
官宣!第三届云原生编程挑战赛正式启动!
[Chongqing Guangdong education] National Open University spring 2019 1042 international economic law reference questions
如何搭建一支搞垮公司的技术团队?
Li Kou Jianzhi offer -- binary tree chapter
JVM's responsibility - load and run bytecode
Interesting practice of robot programming 15- autoavoidobstacles
Database postragesql client connection default
Grpc message sending of vertx