当前位置:网站首页>Socket编程
Socket编程
2022-07-03 01:31:00 【玻璃晴朗橘子辉煌】
边栏推荐
- 小程序开发黑马购物商城中遇到的问题
- Network security - scan
- Network security - scanning and password explosion 2
- [data mining] task 2: mimic-iii data processing of medical database
- [North Asia data recovery] data recovery case of raid crash caused by hard disk disconnection during data synchronization of hot spare disk of RAID5 disk array
- 网络安全-ACL访问控制列表
- [camera topic] how to save OTP data in user-defined nodes
- 深度(穿透)选择器 ::v-deep/deep/及 > > >
- [error record] an error is reported in the fluent interface (no mediaquery widget ancestor found. | scaffold widgets require a mediaquery)
- Processing of tree structure data
猜你喜欢

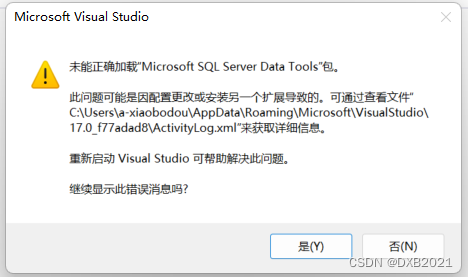
Ni visa fails after LabVIEW installs the third-party visa software
![[shutter] animation animation (animatedbuilder animation use process | create animation controller | create animation | create components for animation | associate animation with components | animatio](/img/32/fa1263d9a2e5f77b0434fce1912cb2.gif)
[shutter] animation animation (animatedbuilder animation use process | create animation controller | create animation | create components for animation | associate animation with components | animatio

Smart management of Green Cities: Digital twin underground integrated pipe gallery platform
![[Appendix 6 Application of reflection] Application of reflection: dynamic agent](/img/e7/0ee42902b178b13e9a41385267e7b6.jpg)
[Appendix 6 Application of reflection] Application of reflection: dynamic agent

Performance test | script template sorting, tool sorting and result analysis
![[data mining] task 5: k-means/dbscan clustering: double square](/img/e7/678197e703d1a28b765a0e3afd5580.png)
[data mining] task 5: k-means/dbscan clustering: double square
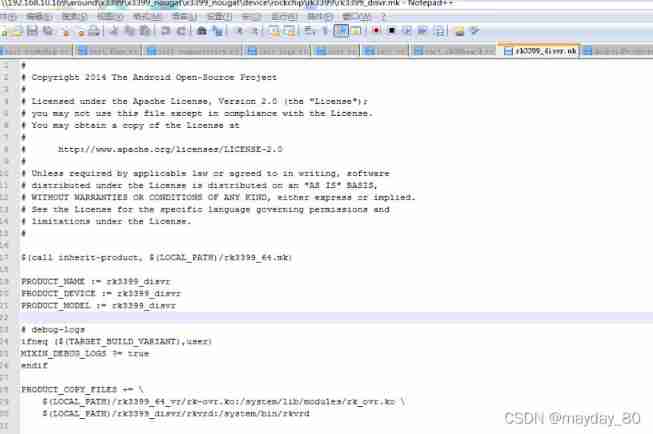
Rockchip3399 start auto load driver

Learn BeanShell before you dare to say you know JMeter
How is the mask effect achieved in the LPL ban/pick selection stage?
C application interface development foundation - form control (1) - form form
随机推荐
Button button adaptive size of wechat applet
深度(穿透)选择器 ::v-deep/deep/及 > > >
网络安全-浅谈安全威胁
Network security - phishing
C application interface development foundation - form control (1) - form form
[leetcode] 797 and 1189 (basis of graph theory)
¢ growth path and experience sharing of getting an offer
[AUTOSAR cantp] -2.11-uds diagnostic response frame data segment data padding data filling and data optimization data optimization (Theory + configuration)
Modify table structure
[Appendix 6 Application of reflection] Application of reflection: dynamic agent
"Jetpack - livedata parsing"
Network security - firewall
Analyzing several common string library functions in C language
[fluent] hero animation (hero animation use process | create hero animation core components | create source page | create destination page | page Jump)
可視化yolov5格式數據集(labelme json文件)
网络安全-ACL访问控制列表
网络安全-病毒
Why can't the start method be called repeatedly? But the run method can?
Vant 实现简单的登录注册模块以及个人用户中心
网络安全-漏洞与木马