当前位置:网站首页>I What is security testing
I What is security testing
2022-07-04 10:48:00 【weixin_ thirty-four million three hundred and twenty-two thousa】
1. What is security testing doing ?
scanning ? In the eyes of many people , What's safe is where the tool scans all day , Scanning with a variety of different tools .
Yes , Scanning is an important part of security testing , Scanning can quickly and effectively find problems . The ease of use of scanning tools , Convenience determines its important position . But the limitations of scanning tools , It is also obvious that the program is not flexible enough . Whether it's the analysis of the scan report 、 Deep mining of loopholes 、 The organization of testing and other work are inseparable from security testers , So it can only be said that the scanning tool reduces the workload of testers , It's a means of security testing
2. How do security testers position themselves ?
We often hear some names about security , Like software security 、 Information security 、 Network security 、 Computer security and so on , These areas are all about security , Which one do we belong to ?
【 software security 】 At a small scale, it's a software product , In addition to hardware, it's software .
【 Information security 】 Look at the name, we know that the key is information , But what is information , Customer data is all useful data ?
【 Network security 】 What is the Internet , Network system hardware 、 Software is a kind of vague concept
【 Computer security 】PC? The server ? Router ?
We can see that these concepts have become all kinds of devices that make up our Internet today, including all kinds of embedded machines 、 external USB、 Hardware and software of Bluetooth and other devices , And the use of 、 maintain 、 Managing these things, the whole security of people
Looking at the difference between them , They focus on different places , Or say something , They have no obvious boundaries, but they have their own priorities
What's our focus , What kind of product is our product ? We have web service 、 Interface services 、 File service 、 Video and other services , We call them our system , So we are doing the security test of this system , So I think we should position it as system security testing
Of course, our system also involves people 、 When it comes to hardware , This is not our focus , We only recognize it from the perspective of software technology . that , System security testing is different from functional testing , Like performance testing , Special tests listed separately
3. What is the essence of security ?
trust 、 The human nature ( The biggest loophole in network security is people )、 Stop loss 、 defense
These are some of the main arguments on the Internet today , Trust or distrust is the essential starting point of the mainstream
4. Concept definition
【 sensitive data 】 The specific scope depends on the specific application scenarios of the product , The product should be analyzed and judged according to the risk
Typical sensitive data includes passwords 、 Bank Account 、 Mass personal data 、 User communication content and key, etc
【 Personal data 】 It refers to directly passing the data or combining the data with other information , Information that identifies a natural person
【 Anonymity 】 Changes to personal data ( Separate one-way hashing 、 Truncation 、 Replacement, etc , To preserve the correspondence between the true value and the replacement value of personal data , Symmetric encryption or mapping table can be used , But the key / The mapping table must be controlled by all the data ), So that the original personal information can no longer be attributed to an identifiable natural person , Or it costs too much to reason 、 It's a disproportionate time 、 Cost and energy
边栏推荐
- /*Write a function to open the file for input, read the contents of the file into the vector container of string class 8.9: type, and store each line as an element of the container object*/
- [advantages and disadvantages of outsourcing software development in 2022]
- [Galaxy Kirin V10] [desktop] printer
- Open the neural network "black box"! Unveil the mystery of machine learning system with natural language
- Map container
- BGP advanced experiment
- Network disk installation
- [Galaxy Kirin V10] [server] KVM create Bridge
- 1. Circular nesting and understanding of lists
- Pod management
猜你喜欢
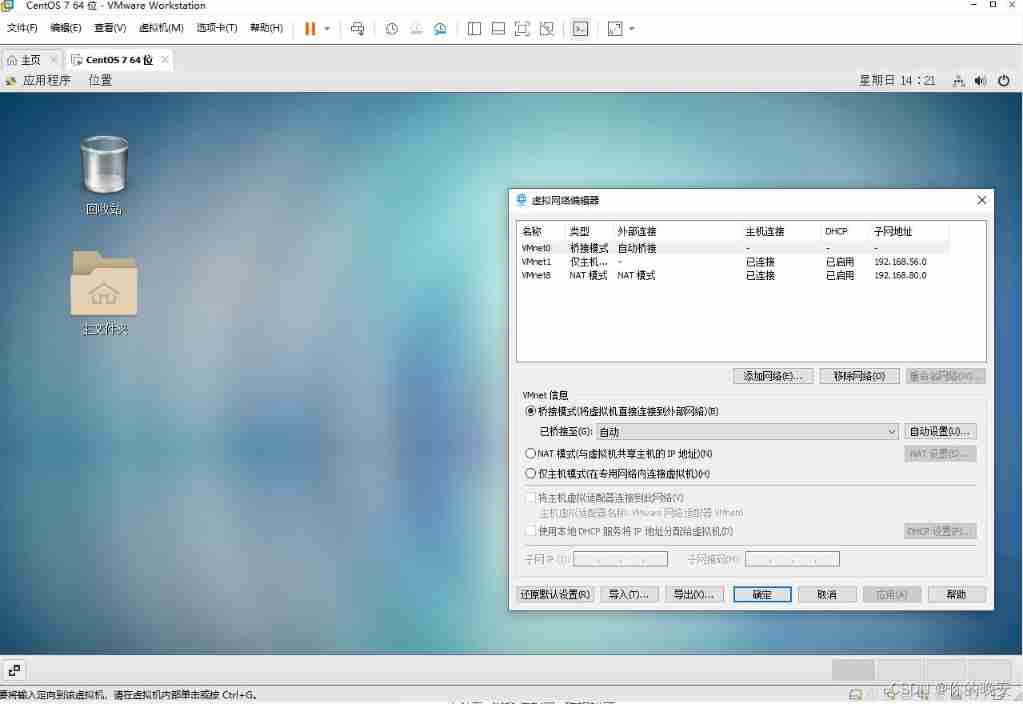
Virtual machine configuration network
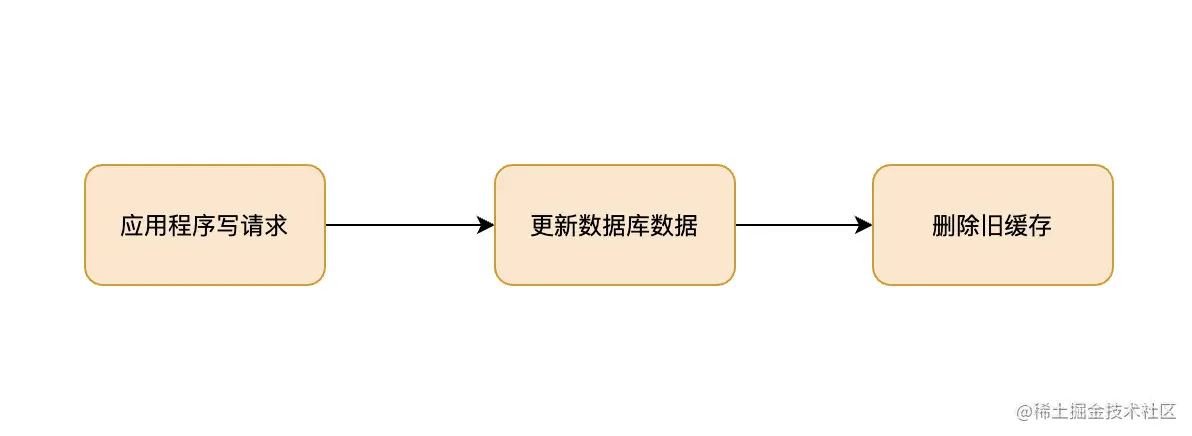
If you don't know these four caching modes, dare you say you understand caching?
![[Galaxy Kirin V10] [server] NFS setup](/img/ed/bd7f1a1e4924a615cb143a680a2ac7.jpg)
[Galaxy Kirin V10] [server] NFS setup
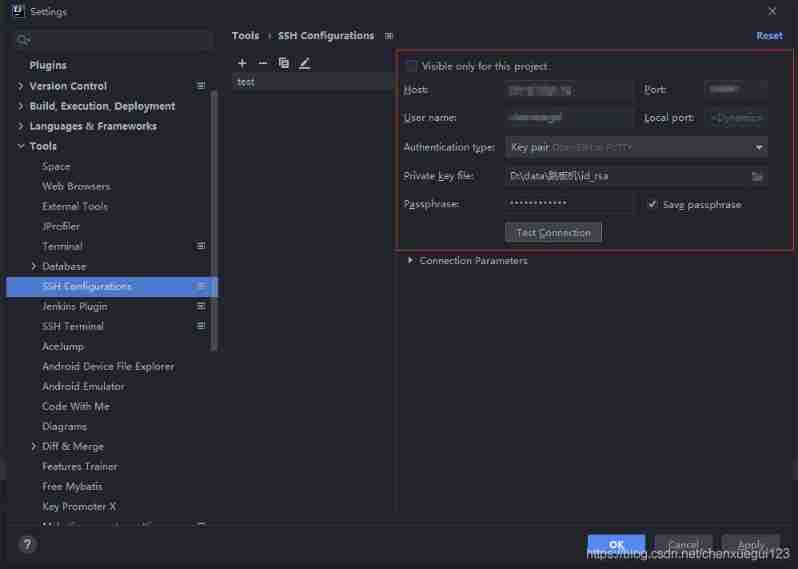
Idea SSH channel configuration
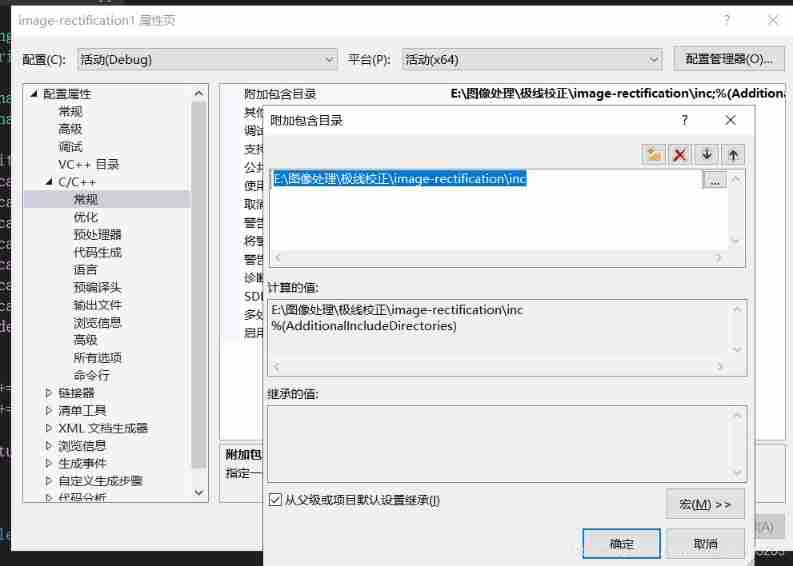
Vs201 solution to failure to open source file HPP (or link library file)
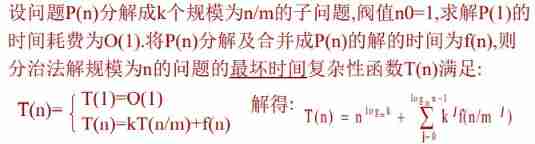
Recursion and divide and conquer strategy
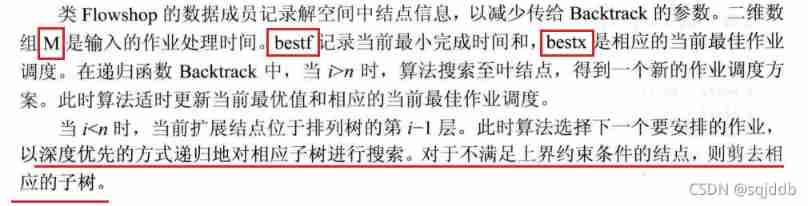
Summary of several job scheduling problems
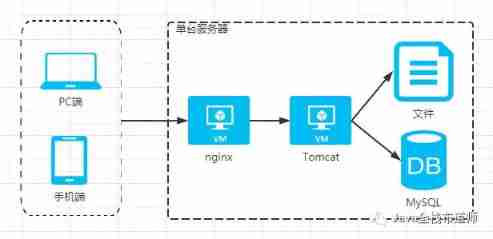
Evolution from monomer architecture to microservice architecture
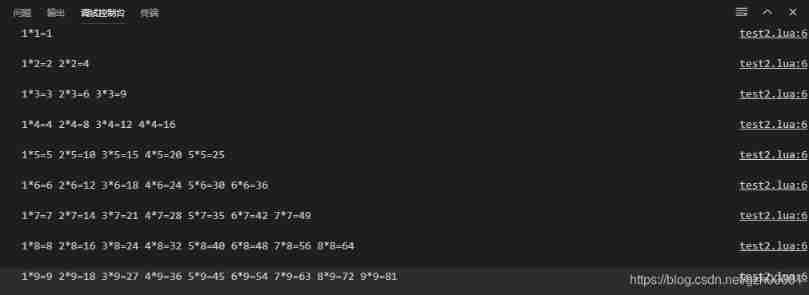
Using Lua to realize 99 multiplication table
![[Galaxy Kirin V10] [desktop] can't be started or the screen is black](/img/68/735d80c648f4a8635513894c473860.jpg)
[Galaxy Kirin V10] [desktop] can't be started or the screen is black
随机推荐
[testing theory] thinking about testing profession
[Galaxy Kirin V10] [desktop] build NFS to realize disk sharing
2022 ape circle recruitment project (software development)
From programmers to large-scale distributed architects, where are you (2)
C language structure to realize simple address book
/*Write a loop to output the elements of the list container in reverse order*/
Jianzhi offer 04 (implemented in C language)
RHCE - day one
BGP advanced experiment
VLAN part of switching technology
DDL language of MySQL database: create, modify alter, delete drop of databases and tables
Collection of practical string functions
DCL statement of MySQL Foundation
Dictionaries and collections
Deepmind proposed a Zuan AI, which specially outputs network attack language
Recursive method to achieve full permutation (C language)
Using SA token to solve websocket handshake authentication
[test theory] test the dimension of professional ability
PHP programming language (1) - operators
Day06 list job