当前位置:网站首页>File upload of DVWA range
File upload of DVWA range
2022-07-06 07:49:00 【zyf-16】
Upload files
Refers to a vulnerability that allows us to upload our files , Through this vulnerability, we can upload some Trojans
Now let's analyze low Level source code

first if Confirm our upload operation , after $target_path Function to determine the location of the file we upload , Get the name of our file , If the file is not moved to the location specified by the function, the upload fails , Otherwise, the upload will succeed
because low The level is not filtered, so we can upload at will
So let's see medium Level

Here he gets the name of the file we uploaded , type , size , If the type of file we upload is not jpeg,png And the size of the file we uploaded is not less than 100kb Cannot upload , The file will be moved when it meets the requirements , Upload failed without moving , After successfully moving, it will be uploaded successfully
We can go through burpsuite To bypass , When we upload other types of files, grab their packages and send them to repeater, Modify the file type to image/png Send again to bypass


Now let's talk about high Level

Here is the definition of a white list , use uploaded_ext Function to get your extension name , Your file extension name must meet the requirements
边栏推荐
- Emo diary 1
- [1. Delphi foundation] 1 Introduction to Delphi Programming
- 软件测试界的三无简历,企业拿什么来招聘你,石沉大海的简历
- If Jerry needs to send a large package, he needs to modify the MTU on the mobile terminal [article]
- Nc204382 medium sequence
- The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower
- When the Jericho development board is powered on, you can open the NRF app with your mobile phone [article]
- Three treasures of leeks and Chinese men's football team
- 解决方案:智慧工地智能巡檢方案視頻監控系統
- opencv学习笔记八--答题卡识别
猜你喜欢
![[nonlinear control theory]9_ A series of lectures on nonlinear control theory](/img/a8/03ed363659a0a067c2f1934457c106.png)
[nonlinear control theory]9_ A series of lectures on nonlinear control theory
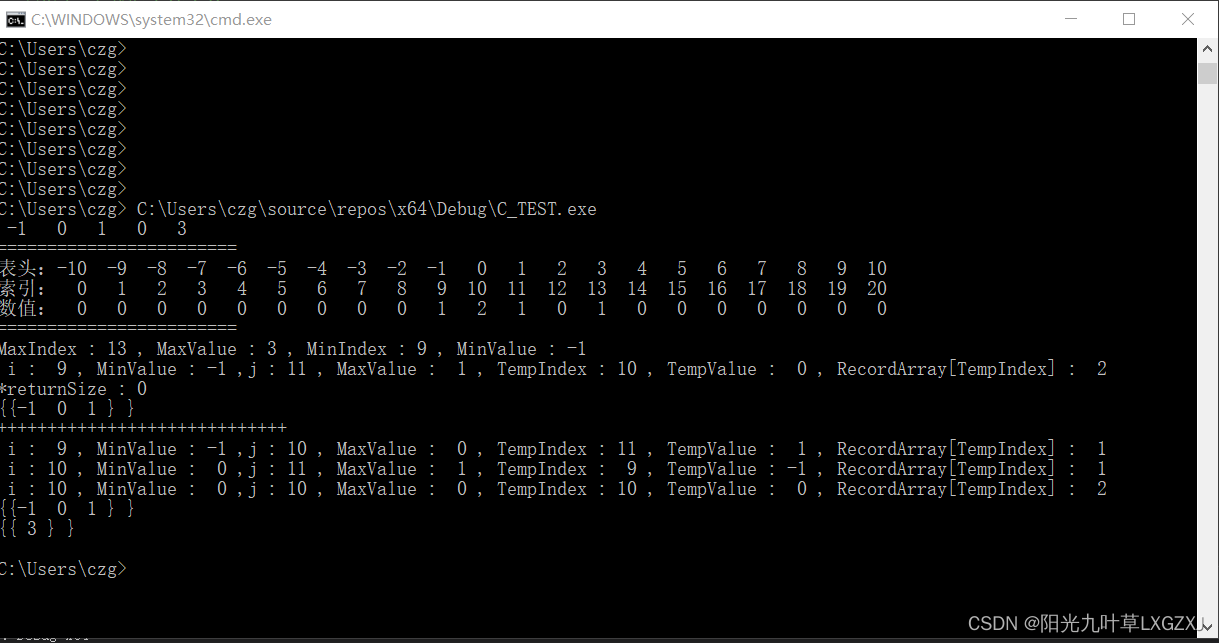
leecode-C语言实现-15. 三数之和------思路待改进版
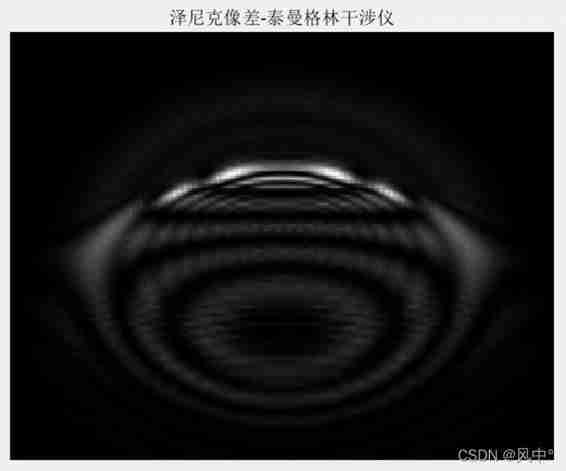
Simulation of Teman green interferometer based on MATLAB
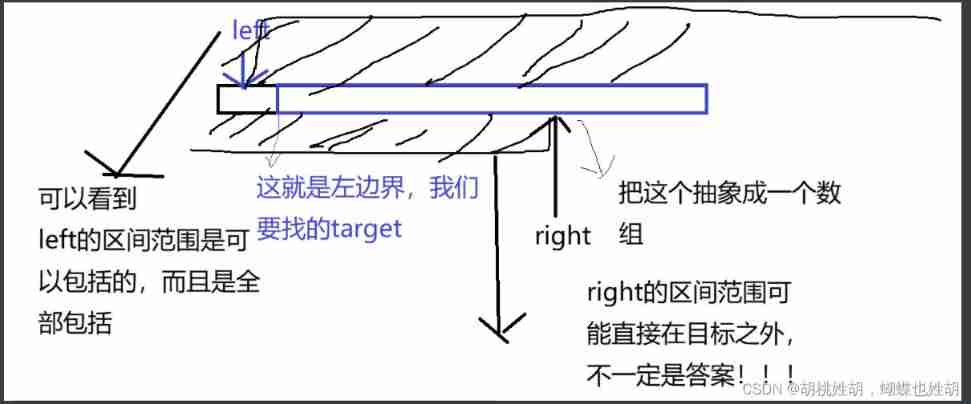
Do you really think binary search is easy
![Ble of Jerry [chapter]](/img/ce/127b597cdd238bb0c37326f5cf8265.png)
Ble of Jerry [chapter]
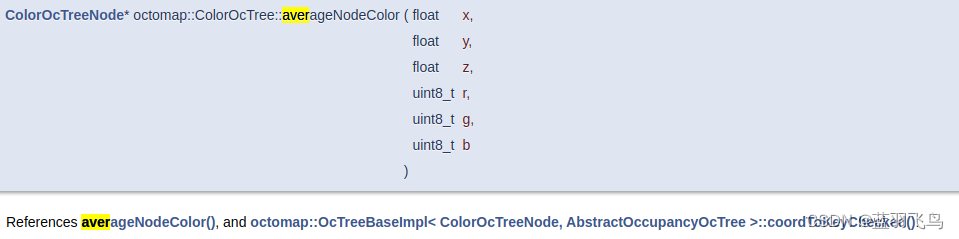
Description of octomap averagenodecolor function
![Ble of Jerry [chapter]](/img/00/27486ad68bf491997d10e387c32dd4.png)
Ble of Jerry [chapter]
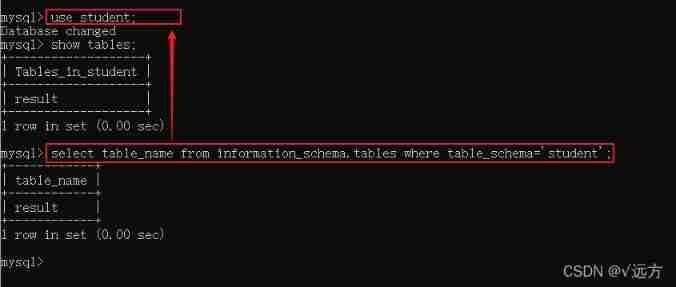
Database basic commands

The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower
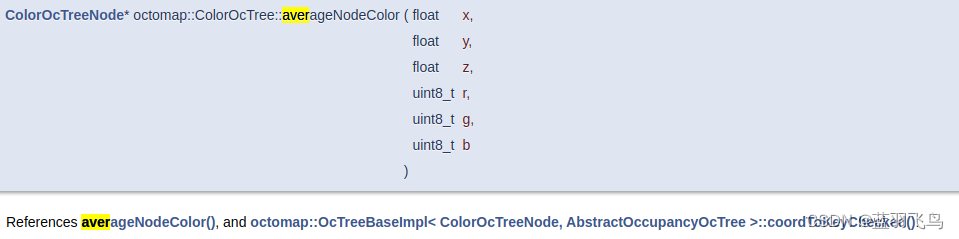
octomap averageNodeColor函数说明
随机推荐
[CF Gym101196-I] Waif Until Dark 网络最大流
1015 reversible primes (20 points) prime d-ary
Simulation of Teman green interferometer based on MATLAB
Parameter self-tuning of relay feedback PID controller
The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower
Simulation of holographic interferogram and phase reconstruction of Fourier transform based on MATLAB
Three no resumes in the software testing industry. What does the enterprise use to recruit you? Shichendahai's resume
Ble of Jerry [chapter]
Onie supports pice hard disk
Simulation of Michelson interferometer based on MATLAB
Iterator Foundation
2022年Instagram运营小技巧简单讲解
[factorial inverse], [linear inverse], [combinatorial counting] Niu Mei's mathematical problems
C intercept string
opencv学习笔记九--背景建模+光流估计
Jerry's general penetration test - do data transmission with app Communication [article]
继电反馈PID控制器参数自整定
Scala语言学习-08-抽象类
Get the path of edge browser
Redis builds clusters