当前位置:网站首页>Connect to blog method, overload, recursion
Connect to blog method, overload, recursion
2022-07-07 12:35:00 【Xiaobai shelter】
1. In and out
Enter the reference : Do it Unknown condition required
The ginseng : Feedback needed after completion
2. Method overloading (overload)
Definition : Same method name , Different parameter list . The list is divided into : Different numbers and types
The method is unique : Method name and parameters
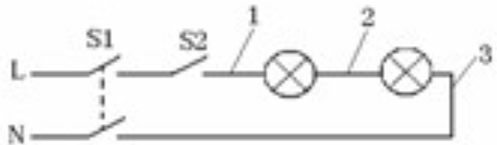
3. Memory division :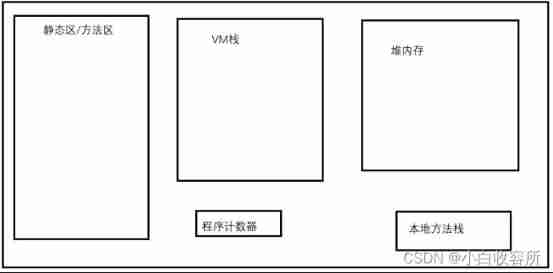
Java Runtime Data Area : java Runtime area , General name JVM Memory
*
- Program counter :
A small area of memory . Action can be seen as a position indicator of the current program execution- Static zone / Method area :
Save program files (class file ) And static data , Before the method is called , Also stored in the static area , There is also a runtime constant pool inside- VM Stack : Also called stack memory
Stack memory is a space opened up based on stack data structure , The feature is first in and last outStack : It's a data structure , First in, then out , Like a clip- The components of the stack
Stack space : Stack memory is stack spaceStack frame : Every stack element in the stack space It's called stack frame ( such as Every bullet in the magazine It's called stack frame )Stack bottom element : The first stack frame put inTop element of stack : The last stack frame put in- Stack operation
Pressing stack : It refers to the process of putting elements into stack spaceBomb stack : Is the process of ejecting elements- Stack memory , Is used to execute methods , Execution of all methods , Must be done in stack memory
- Native Method Stack :
Used to execute some local methods , such as hashCode etc. , The model and operation are similar to VM Stack consistency , Never mind ,- Heap memory :
To save objects
4. recursive
Definition : Method calls the current method
recursive thinking : a. Recursion and iteration are equivalent It's a cycle b. The basic idea is to analogy in turn
Application scenarios : What a cycle can do , Recursion can do , But in this case, it is preferred to use loops , Recursion should be very memory consuming , Low operating efficiency ; however Like tree structure , You can't do a loop , It can only be done by handing it back
Common recursive application scenarios : So the tree structure ; Folder copy ; Fibonacci sequence
difficulty : It's not easy to understand recursion , drawing , Stack frame call graph
Be careful : There must be termination conditions , Otherwise, it will be like an endless cycle , As a result, the stack memory overflow problem occurs when you keep pressing the stack without bouncing the stack
5. Fibonacci sequence : It means that from the third item, each item is the sum of the first two items namely f(n)=f(n-1)+f(n-2) (n>2)
边栏推荐
- 金融数据获取(三)当爬虫遇上要鼠标滚轮滚动才会刷新数据的网页(保姆级教程)
- Sign up now | oar hacker marathon phase III midsummer debut, waiting for you to challenge
- leetcode刷题:二叉树19(合并二叉树)
- 全球首堆“玲龙一号”反应堆厂房钢制安全壳上部筒体吊装成功
- The road to success in R & D efficiency of 1000 person Internet companies
- 2022-07-07日报:GAN发明者Ian Goodfellow正式加入DeepMind
- Attack and defense world - PWN learning notes
- idm服务器响应显示您没有权限下载解决教程
- Processing strategy of message queue message loss and repeated message sending
- Several methods of checking JS to judge empty objects
猜你喜欢
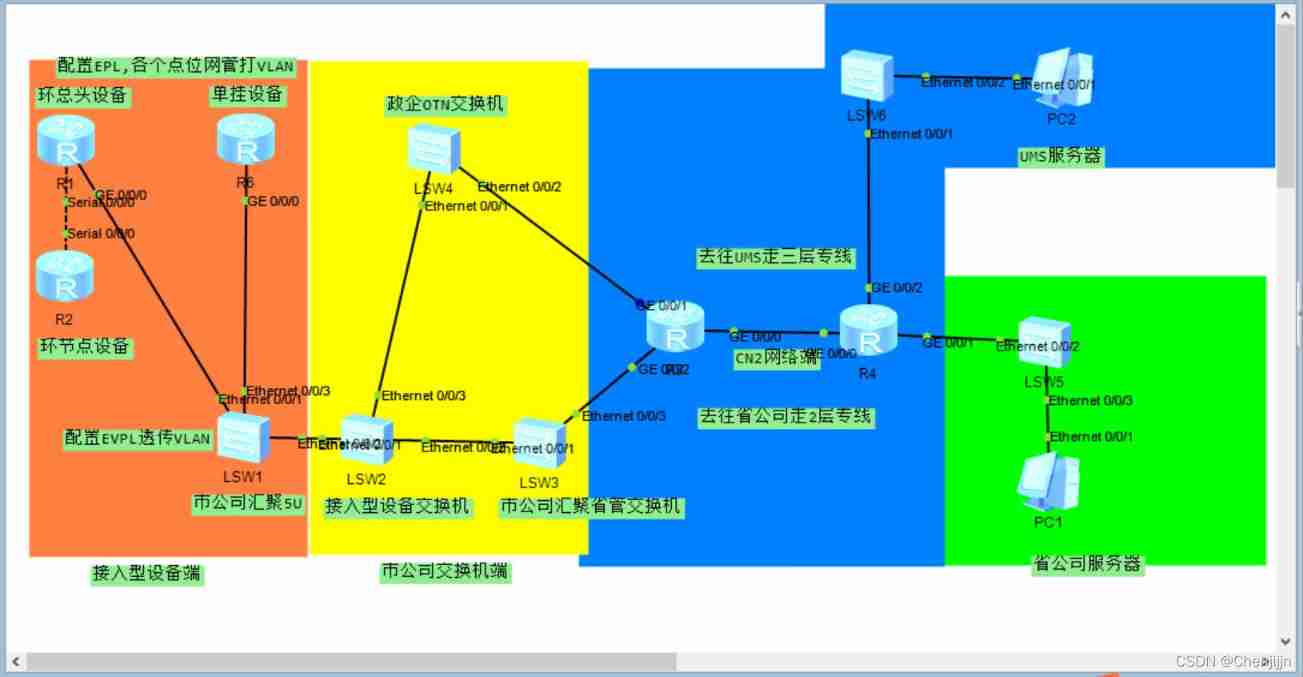
Simple network configuration for equipment management
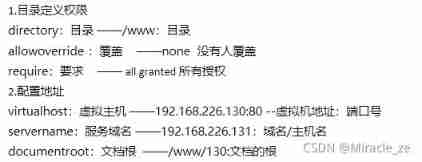
Customize the web service configuration file
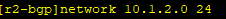
BGP third experiment report

ps链接图层的使用方法和快捷键,ps图层链接怎么做的
2022A特种设备相关管理(锅炉压力容器压力管道)模拟考试题库模拟考试平台操作

Completion report of communication software development and Application
![[deep learning] image multi label classification task, Baidu paddleclas](/img/dd/6f213a396e8bb240a6872e4c03afab.png)
[deep learning] image multi label classification task, Baidu paddleclas
Multi row and multi column flex layout
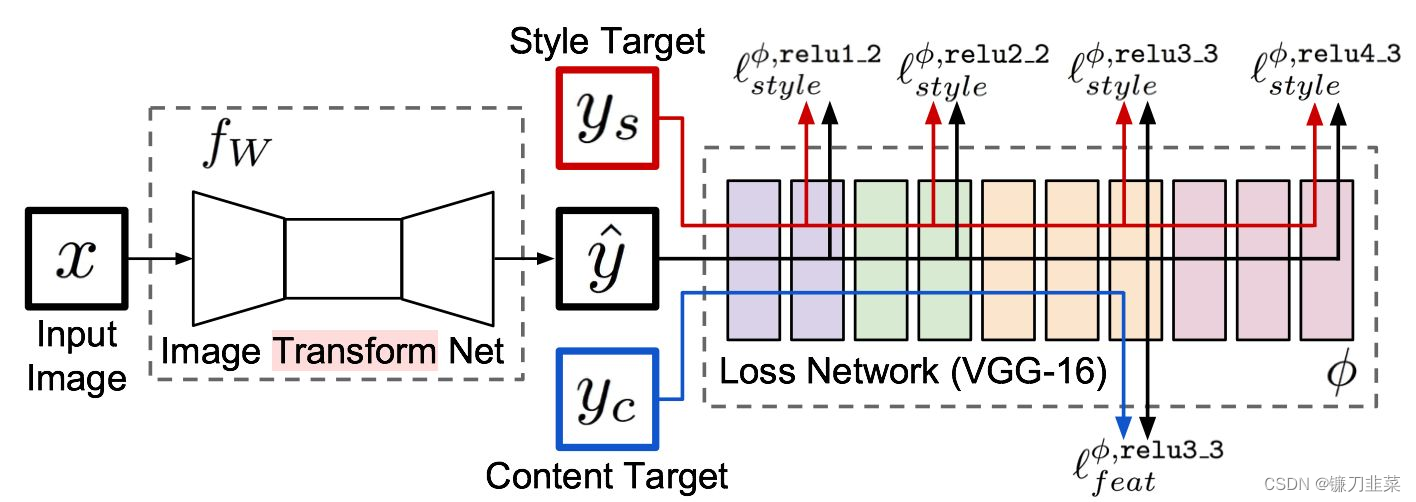
【PyTorch实战】用PyTorch实现基于神经网络的图像风格迁移
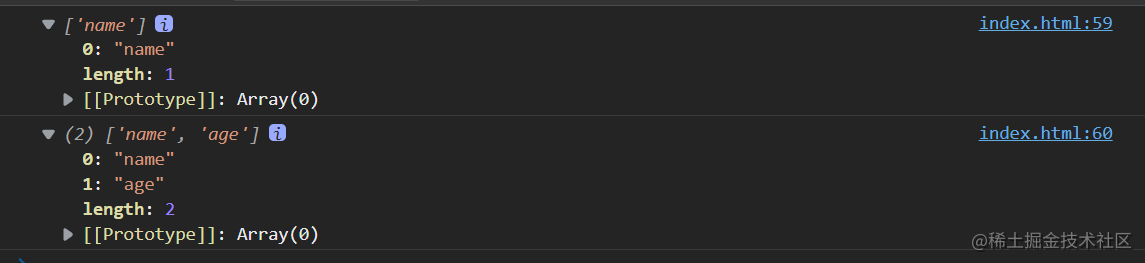
盘点JS判断空对象的几大方法
随机推荐
MPLS experiment
解决 Server returns invalid timezone. Go to ‘Advanced’ tab and set ‘serverTimezone’ property manually
2022危险化学品生产单位安全生产管理人员考题及在线模拟考试
SQL injection -- Audit of PHP source code (take SQL lab 1~15 as an example) (super detailed)
DOM parsing XML error: content is not allowed in Prolog
Realize a simple version of array by yourself from
爱可可AI前沿推介(7.7)
JS to convert array to tree data
sql-lab (54-65)
静态Vxlan 配置
Sign up now | oar hacker marathon phase III midsummer debut, waiting for you to challenge
【玩转 RT-Thread】 RT-Thread Studio —— 按键控制电机正反转、蜂鸣器
SQL Lab (36~40) includes stack injection, MySQL_ real_ escape_ The difference between string and addslashes (continuous update after)
【PyTorch实战】用RNN写诗
"Series after reading" my God! It's so simple to understand throttling and anti shake~
[pytorch practice] write poetry with RNN
IPv6 experiment
2022聚合工艺考试题模拟考试题库及在线模拟考试
What is an esp/msr partition and how to create an esp/msr partition
[Q&A]AttributeError: module ‘signal‘ has no attribute ‘SIGALRM‘