当前位置:网站首页>[designmode] proxy pattern
[designmode] proxy pattern
2022-07-07 16:36:00 【weixin_ forty-three million two hundred and twenty-four thousan】
Basic introduction
The proxy pattern : Provide a surrogate for an object , To control access to this object . That is, access the target object through the proxy object . The advantage of this is : It can be realized on the basis of the target object , Enhance additional functional operations , That is, extending the functionality of the target object .
The proxied object can be a remote object 、 Create expensive objects or objects that need security control
There are different forms of agency , There are three main types Static proxy 、 The reason is A dynamic proxy (JDK agent 、 The interface agent ) and Cglib The reason is agent ( Objects can be created dynamically in memory , Instead of implementing interfaces , He belongs to the category of dynamic agency ) .
1 The proxy pattern (Proxy)
1.1 The basic introduction of agent mode
The proxy pattern : Provide a surrogate for an object , To control access to this object . That is, access the target object through the proxy object . The advantage of this is : It can be realized on the basis of the target object , Enhance additional functional operations , That is, extending the functionality of the target object .
The proxied object can be a remote object 、 Create expensive objects or objects that need security control
There are different forms of agency , There are three main types Static proxy 、 The reason is A dynamic proxy (JDK agent 、 The interface agent ) and Cglib The reason is agent ( Objects can be created dynamically in memory , Instead of implementing interfaces , He belongs to the category of dynamic agency ) .
Schematic diagram of agent mode
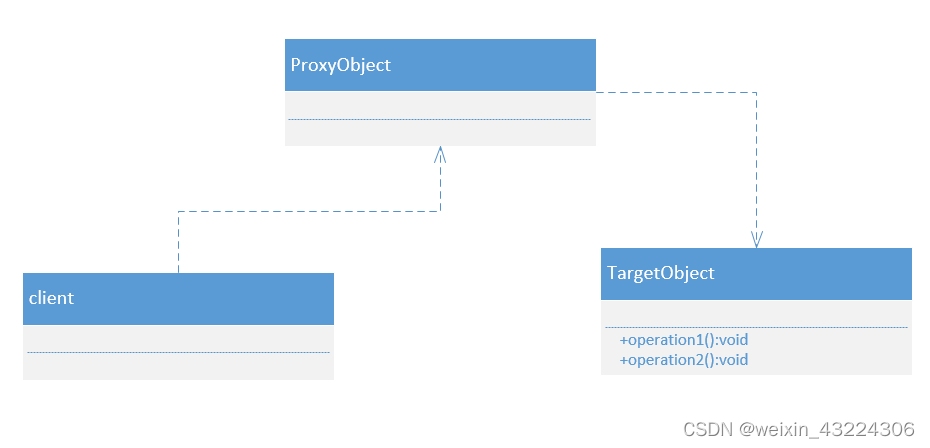
2. Static proxy
2.1 The basic introduction of static code pattern
Static agents are used , You need to define an interface or parent class , Proxied object ( That is, the target object ) Implement the same interface or inherit the same parent class with the proxy object
边栏推荐
- JS modularization
- Prometheus API deletes all data of a specified job
- 打造All-in-One应用开发平台,轻流树立无代码行业标杆
- logback.xml配置不同级别日志,设置彩色输出
- 01tire+链式前向星+dfs+贪心练习题.1
- [vulnhub range] thales:1
- Logback日志框架第三方jar包 免费获取
- Cesium (4): the reason why gltf model is very dark after loading
- Deep listening array deep listening watch
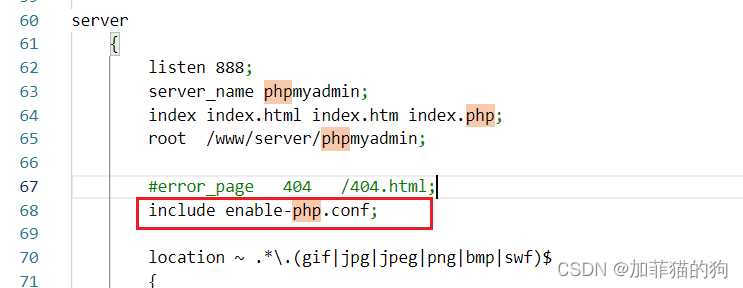
- thinkphp3.2.3中设置路由,优化url
猜你喜欢
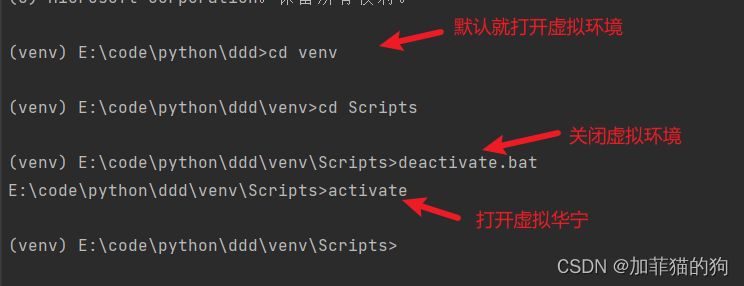
Pycharm terminal enables virtual environment
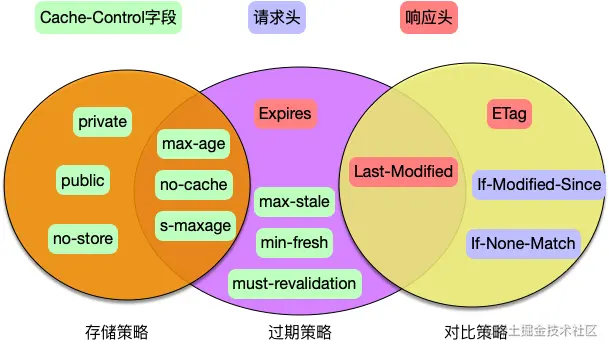
3000 words speak through HTTP cache
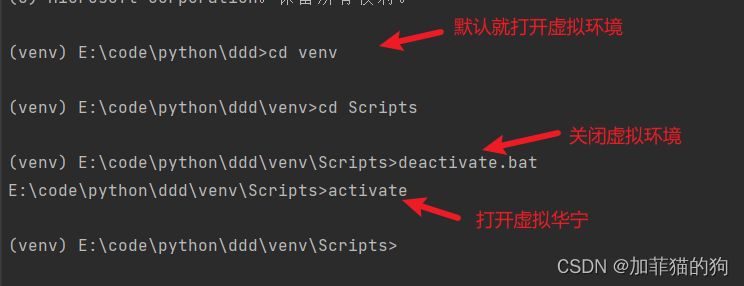
pycharm 终端部启用虚拟环境
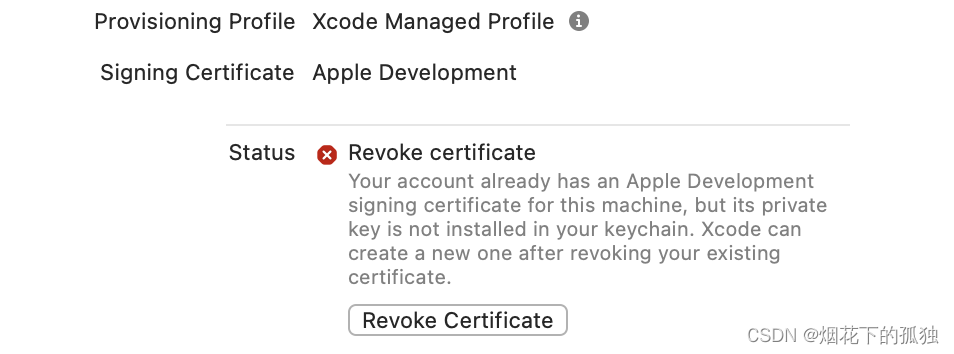
Xcode Revoke certificate
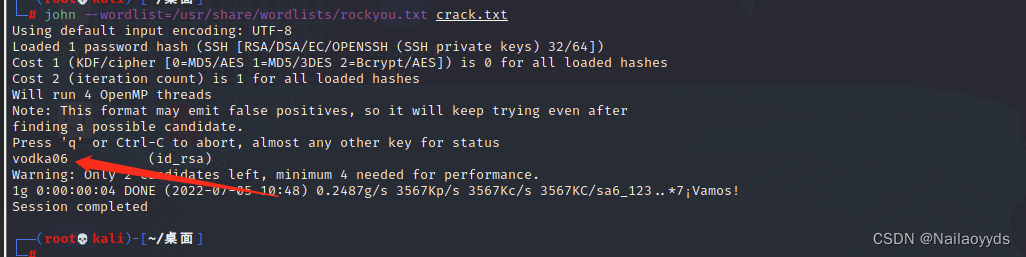
【Vulnhub靶场】THALES:1

Power of leetcode-231-2
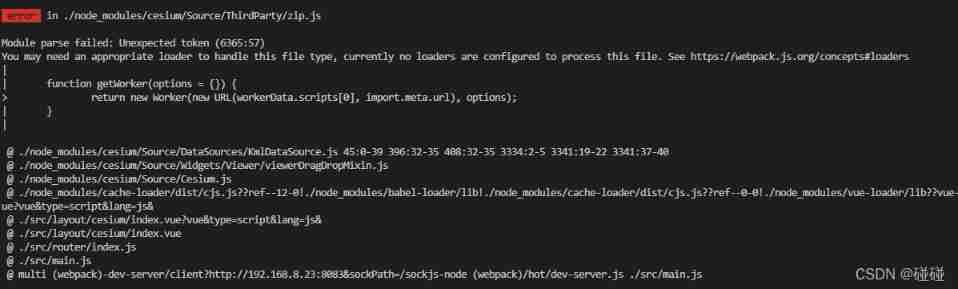
Cesium(3):ThirdParty/zip. js
Record the migration process of a project
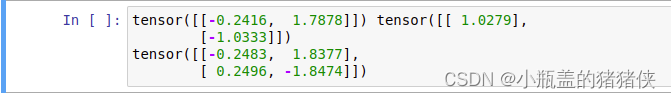
Multiplication in pytorch: mul (), multiply (), matmul (), mm (), MV (), dot ()
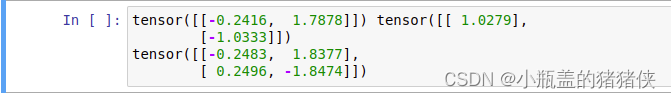
PyTorch 中的乘法:mul()、multiply()、matmul()、mm()、mv()、dot()
随机推荐
Markdown formula editing tutorial
AutoLISP series (1): function function 1
打造All-in-One应用开发平台,轻流树立无代码行业标杆
Common training data set formats for target tracking
【知识小结】PHP使用svn笔记总结
Xcode Revoke certificate
【C 语言】 题集 of Ⅹ
Odoo集成Plausible埋码监控平台
47_Opencv中的轮廓查找 cv::findContours()
Laravel 中config的用法
"The" "PIP" "entry cannot be recognized as the name of a cmdlet, function, script file, or runnable program."
[C language] question set of X
平衡二叉树(AVL)
Tidb cannot start after modifying the configuration file
AutoLISP series (2): function function 2
Deep listening array deep listening watch
PHP中exit,exit(0),exit(1),exit(‘0’),exit(‘1’),die,return的区别
Tragedy caused by deleting the console statement
华东师大团队提出,具有DNA调控电路的卷积神经网络的系统分子实现
iptables只允许指定ip地址访问指定端口