当前位置:网站首页>The essence of transaction and the principle of deadlock
The essence of transaction and the principle of deadlock
2020-11-06 21:35:00 【Irving the procedural ape】
Only with MySQL and spring For example ,, This article does not introduce the concepts of transactions and locks .
This paper uses pseudo code to represent method code , Only express the meaning of the method and transaction annotation
〇、 The shape of the transaction
In my heart , Business has always been like this 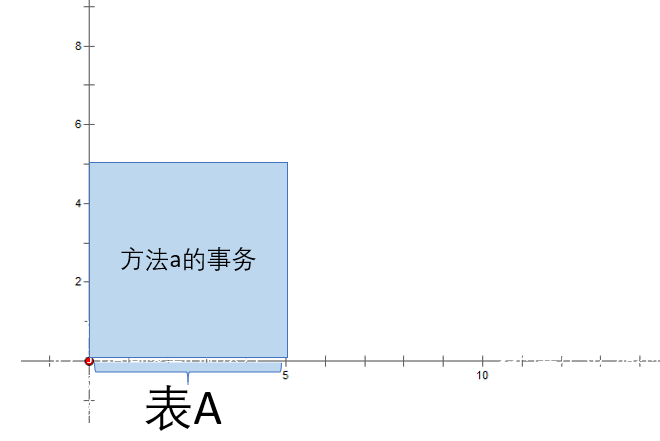
x Axis is a locked resource ,y The axis is the time consumed ,
The transaction box moves down over time ,
When touching x Lock the shaft , Skip over x When the axis is unlocked
The picture above is about the method a The transaction shape of , I named it 【 Transaction box 】, I'm sorry I don't know how to do motion maps , In this paper, we express the best by moving graph .
@Transactional function a(){
Yes A Table modification , It took five seconds }
One 、 A lot of business
When a method calls multiple child methods annotated by a transaction, the situation is 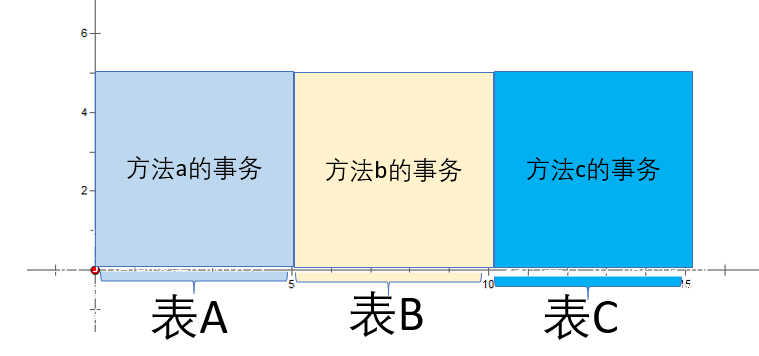
The picture above is about the method abc Invocation time ,a Method 、b Method 、c The transaction shape of the method function abc(){
this.a(){}
this.c(){}}@Transactional function a(){
Yes A Table modification , It took five seconds }@Transactional function b(){
Yes B Table modification , It took five seconds }@Transactional function c(){
Yes C Table modification , It took five seconds }
among abc When the method starts to execute , Execute to a Method , lock a surface , When a Method end b At the beginning of the method ,a Table unlocking ,b Table locking , When b Method end c At the beginning of the method ,b Table unlocking c Table locking .
It is equivalent to that the three transaction blocks in the figure below are united and locked together , Total operation time 15 second 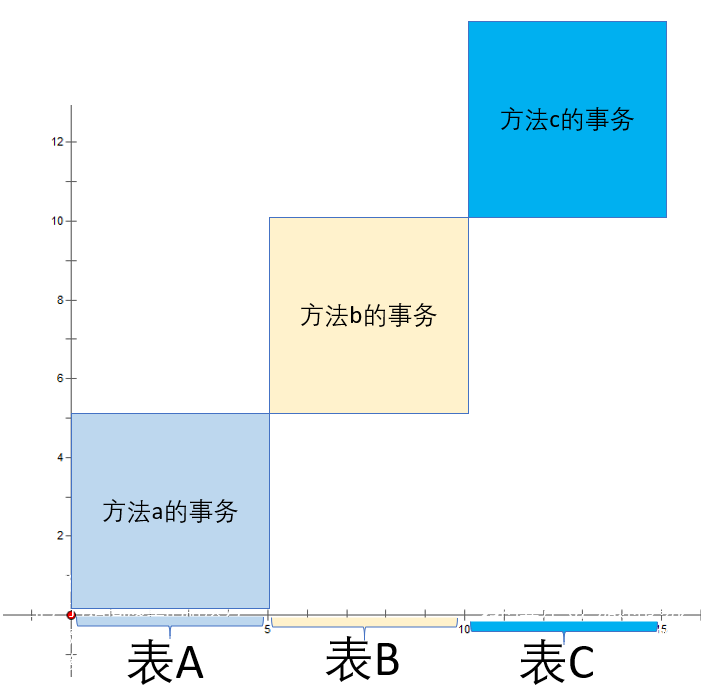
If concurrent requests are made twice abc Method, the transaction box is shown in the figure below 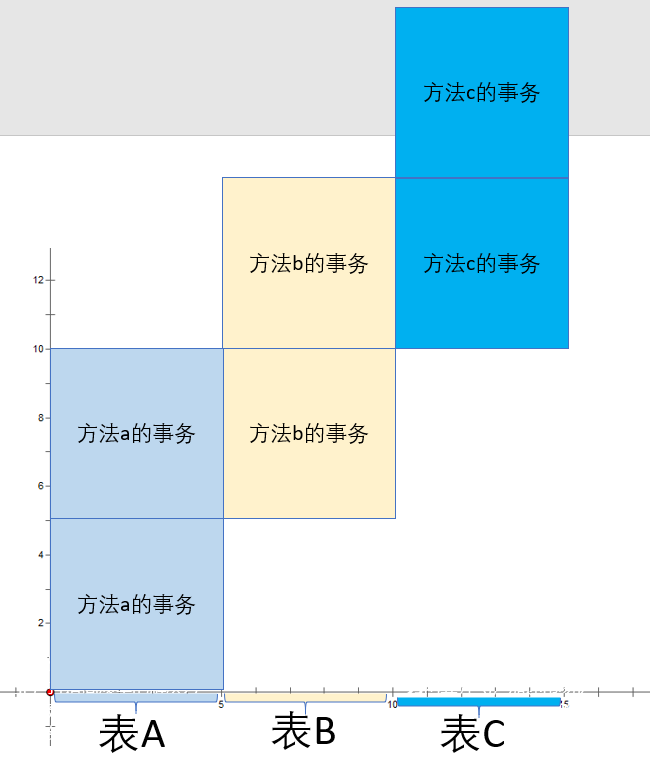
among a The watch will be asked first 1 lock 5 Seconds later to unlock , Be asked again 2 lock 5 second ,
among b The watch will also be requested first 1 lock 5 Seconds later to unlock , Be asked again 2 lock 5 second ,
among c The watch will also be requested first 1 lock 5 Seconds later to unlock , Be asked again 2 lock 5 second ,
The request 1 In the unlock table a And then it locked the watch b Five seconds , At the same time a Be asked again 2 lock 5 second
By analogy , request 2 All asking for 1 After unlocking the corresponding table , Lock the table ,
So the total running time 20 second
Two 、 Large transactions @Transactional function abc(){
this.a(){}
this.b(){}
this.c(){}}
funct.........
版权声明
本文为[Irving the procedural ape]所创,转载请带上原文链接,感谢
边栏推荐
- An article taught you to download cool dog music using Python web crawler
- Call analysis of start method in JNI thread and callback analysis of run method
- Python 100 cases
- Understanding formatting principles
- 2020-08-29:进程线程的区别,除了包含关系之外的一些区别,底层详细信息?
- Diamond standard
- 大数据处理黑科技:揭秘PB级数仓GaussDB(DWS) 并行计算技术
- Using an example to understand the underlying processing mechanism of JS function
- Zero basis to build a web search engine of its own
- To teach you to easily understand the basic usage of Vue codemirror: mainly to achieve code editing, verification prompt, code formatting
猜你喜欢

2020-09-03:裸写算法:回形矩阵遍历。
![What grammar is it? ]](/img/3b/00bc81122d330c9d59909994e61027.jpg)
What grammar is it? ]

Behind the record breaking Q2 revenue of Alibaba cloud, the cloud opening mode is reshaping

window系统 本机查找端口号占用方法

An article will take you to understand SVG gradient knowledge

Zero basis to build a web search engine of its own

All the way, I was forced to talk about C code debugging skills and remote debugging

An article will take you to understand CSS3 fillet knowledge

【涂鸦物联网足迹】物联网基础介绍篇

GitHub: the foundation of the front end
随机推荐
Introduction to the development of small game cloud
嘉宾专访|2020 PostgreSQL亚洲大会阿里云数据库专场:曾文旌
Summary of common SQL statements
Can you do it with only six characters?
Try to build my mall from scratch (2): use JWT to protect our information security and perfect swagger configuration
An article will introduce you to CSS3 background knowledge
What grammar is it? ]
Stickinengine architecture 11 message queue
Metersphere developer's Manual
Code generator plug-in and creator preform file analysis
Countdown | 2020 PostgreSQL Asia Conference - agenda arrangement of Chinese sub Forum
【涂鸦物联网足迹】物联网基础介绍篇
mongo 用户权限 登录指令
大数据处理黑科技:揭秘PB级数仓GaussDB(DWS) 并行计算技术
Behind the record breaking Q2 revenue of Alibaba cloud, the cloud opening mode is reshaping
An article will take you to understand CSS alignment
轻量型 GPU 应用首选 京东智联云推出 NVIDIA vGPU 实例
Summary of front-end interview questions (C, s, s) that front-end engineers need to understand (2)
git远程库回退指定版本
Multi robot market share solution