当前位置:网站首页>Distributed solution - distributed lock solution - redis based distributed lock implementation
Distributed solution - distributed lock solution - redis based distributed lock implementation
2022-07-05 12:32:00 【vx-Yang_ Gaige】
Distributed lock solutions
Distributed lock can be implemented in three ways :
- Database optimistic lock ;
- be based on Redis Distributed locks for ;
- be based on ZooKeeper Distributed locks for
Database optimistic lock ;
be based on Redis Distributed locks for ;
be based on ZooKeeper Distributed locks for
be based on zookeeper Distributed lock implemented by instantaneous ordered nodes , Its main logic is as follows ( The figure comes from IBM Website ). The general idea is : When each client locks a function , stay zookeeper Under the directory of the specified node corresponding to the function , Generate a unique instantaneous ordered node . The way to determine whether to acquire a lock is simple , Only one of the ordered nodes with the smallest sequence number needs to be judged . When the lock is released , Just delete the instantaneous node . meanwhile , It can avoid the lock cannot be released due to service downtime , And the deadlock problem .
High lock security ,zk Be persistent
边栏推荐
- 嵌入式软件架构设计-消息交互
- 强化学习-学习笔记3 | 策略学习
- A guide to threaded and asynchronous UI development in the "quick start fluent Development Series tutorials"
- Learn the garbage collector of JVM -- a brief introduction to Shenandoah collector
- Video networkState 属性
- 只是巧合?苹果 iOS16 的神秘技术竟然与中国企业 5 年前产品一致!
- GPON technical standard analysis I
- C language structure is initialized as a function parameter
- Pytorch two-layer loop to realize the segmentation of large pictures
- Pytoch implements tf Functions of the gather() function
猜你喜欢

Constructing expression binary tree with prefix expression
NPM install reports an error
Redis clean cache
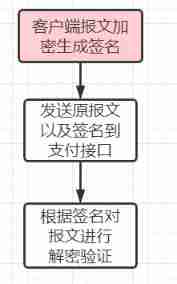
Third party payment interface design
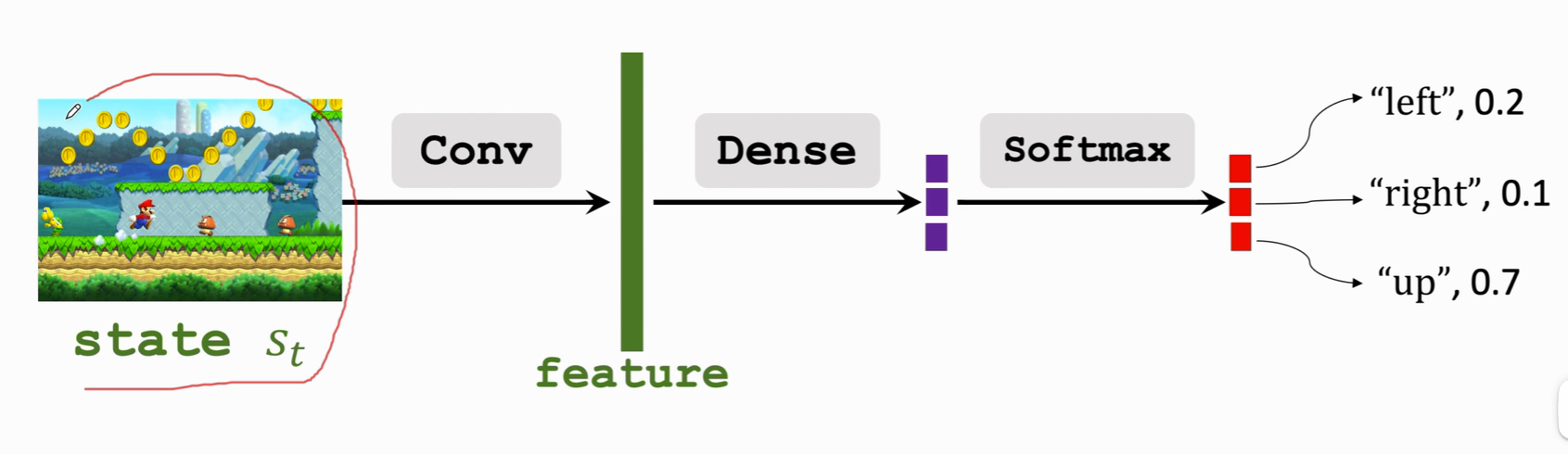
Reinforcement learning - learning notes 3 | strategic learning
Migrate data from Mysql to neo4j database
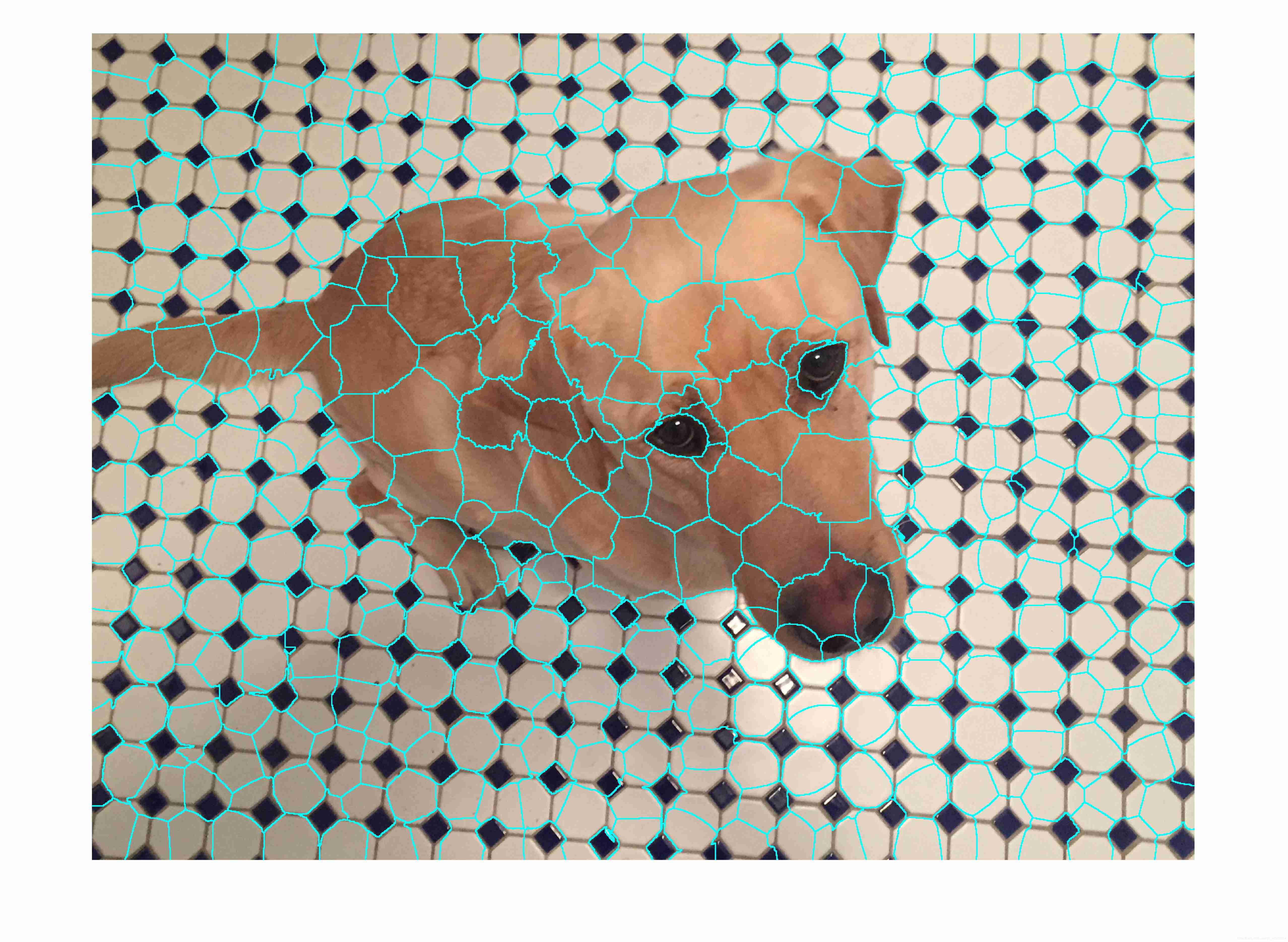
Matlab superpixels function (2D super pixel over segmentation of image)
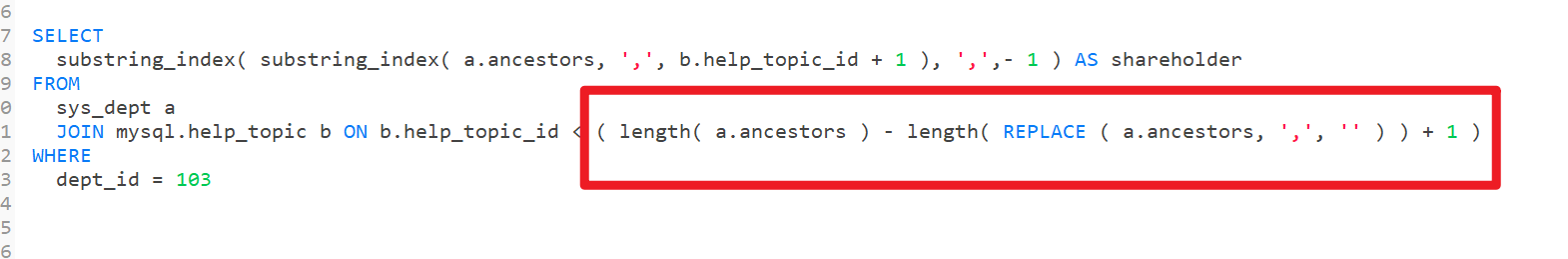
mysql拆分字符串做条件查询
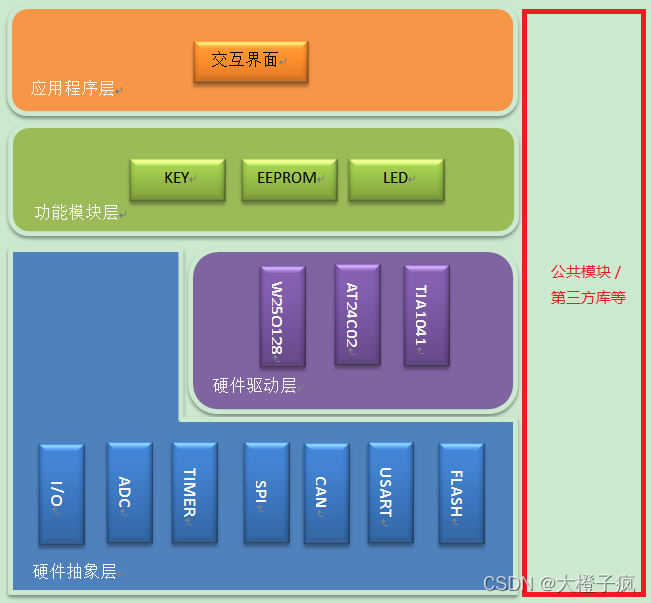
Embedded software architecture design - message interaction
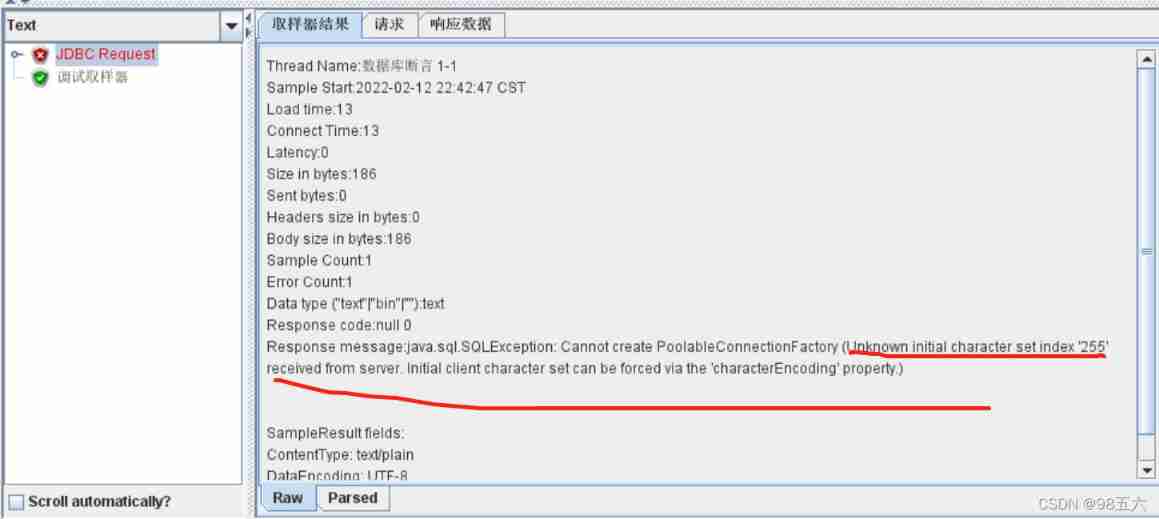
Get data from the database when using JMeter for database assertion
随机推荐
Redis highly available slice cluster
Learn JVM garbage collection 02 - a brief introduction to the reference and recycling method area
A guide to threaded and asynchronous UI development in the "quick start fluent Development Series tutorials"
Redis highly available sentinel mechanism
MySQL log module of InnoDB engine
Pytoch uses torchnet Classerrormeter in meter
Acid transaction theory
[hdu 2096] Xiaoming a+b
图像超分实验:SRCNN/FSRCNN
MySQL installation, Windows version
Average lookup length when hash table lookup fails
Just a coincidence? The mysterious technology of apple ios16 is actually the same as that of Chinese enterprises five years ago!
Implementing Yang Hui triangle with cyclic queue C language
struct MySQL
Swift - enables textview to be highly adaptive
Ecplise development environment configuration and simple web project construction
How to recover the information server and how to recover the server data [easy to understand]
How to design an interface?
byte2String、string2Byte
Get the variable address of structure member in C language